Opensmtpd: We Deliver
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
CYRUS: BUILD YOUR TUTORIAL OWN EMAIL SERVER Don’T Trust Google? We’Ll Help You Navigate the Sea of JOHN LANE Acronyms to Build Your Own Mailserver
TUTORIAL MAILSERVER CYRUS: BUILD YOUR TUTORIAL OWN EMAIL SERVER Don’t trust Google? We’ll help you navigate the sea of JOHN LANE acronyms to build your own mailserver. ou can’t beat the convenience and ease of use access their mail by connecting to the server using WHY DO THIS? offered by Gmail. But unfortunately, all that any IMAP-capable email client application. • Take control of your Yfree storage comes at a price: your privacy. You will need a, preferably new, server for this email provision. Spam, intrusive adverts and snooping from unnamed project and you’ll need root access to it. Our examples • Stop outside agencies government agencies are the inevitable downside of use Arch Linux, and we created a new virtual server. from scanning the using someone else’s service for free. So why not Begin by installing Cyrus (build the Arch User content of your emails. build your own email server including anti-spam, Repository package first – see the boxout below-right): • Get webmail without advertising. anti-virus and webmail? $ pacman -U ~build/cyrus-imapd/cyrus-imapd-2.4.17-5-x86_64. You can use your own server to retrieve messages pkg.tar.xz from other mailservers, such as those provided by The default configuration writes data to /var/imap internet service providers, or other services like those and user mailboxes to /var/spool/imap. You can from Google and Yahoo. But you don’t need to rely on change this if you prefer another location; we’ll others if you have your own server. If you have a configure our server to use /srv/mail/cyrus to domain name that you control, and if you can give your illustrate this. -
Cyrus Mail Server 2 Table of Contents
Univention Corporate Server Cyrus mail server 2 Table of Contents 1. Introduction ........................................................................................................................ 4 2. Installation ......................................................................................................................... 5 3. Management of the mail server data ....................................................................................... 6 3.1. Management of mail domains ..................................................................................... 6 3.2. Assignment of e-mail addresses to users ........................................................................ 6 3.3. Management of mailing lists ....................................................................................... 7 3.4. Management of mail groups ........................................................................................ 7 3.5. Management of shared IMAP folders ........................................................................... 8 3.6. Mail quota ............................................................................................................... 9 4. Spam detection and filtering ................................................................................................ 10 5. Identification of viruses and malware .................................................................................... 11 6. Identification of Spam sources with DNS-based Blackhole Lists (DNSBL) ................................... -

Setting up a Dial in PPP Server for Use with NX1500 Series Nexion Data Modems
Setting up a Dial In PPP Server for use with NX1500 series Nexion Data modems. A Linux server can provide many network services and all of these can be accessed by users via a dial up connection. Such services might include Email, Instant Messaging, BBS File Sharing and Internet access. This document applies to Red Hat Linux 7.3 and details only PPP Dial In setup. It requires Mgetty and PPPd to be installed – PPPd is installed by default. Mgetty. Installation To see if Mgetty is installed, run GnoRPM and click Find. Select Match Label from the list and enter mgetty. Click find. No result means Mgetty is not installed. Close the find window. To install, insert the Red Hat CD, mount it by right clicking the desktop and choosing Disks, CD-ROM. Click the Install button in GnoRPM, find Mgetty in the list and install by following the prompts etc. Unmount the drive the same way it was mounted. Mgetty must be run against each port to be monitored for dial in. To run Mgetty on COM 1, the command would be /sbin/mgetty –D ttyS0 where –D forces data mode (deny fax) and ttyS0 = COM 1. (ttyS1 is equivalent to COM 2). Most commonly the Mgetty command is added to /etc/inittab so it is automatically executed at startup and is also re-executed each time the process is terminated (modem hang up). For a modem on COM 1, add the following line to /etc/inittab: S0:2345:respawn:/sbin/mgetty –D ttyS0 The starting ‘S0’ is an arbitrary reference and can be any unique set of characters. -

Thanos Tsouanas --- C.V
Curriculum Vitæ Thanos Tsouanas 02/05/2017 I Personal details hello photo full name: Athanasios (Thanos) Tsouanas date of birth: 22/02/1983 place of birth: Athens, Greece nationality: Hellenic office address: IMD, Universidade Federal do Rio Grande do Norte Av. Cap. Mor Gouveia, S/N CEP: 59063-400, Natal{RN, Brasil phone number: (+55) (84) 9 8106-9789 (mobile, Telegram, WhatsApp) email address: [email protected] personal website: http://www.tsouanas.org/ GitHub: http://github.com/tsouanas Spoken languages Greek (native); English (proficient); Brazilian Portuguese (fluent). I Studies & academic positions 2016 { Associate professor (permanent position) in Instituto Metr´opole Digital of Universidade Federal do Rio Grande do Norte (UFRN), Brazil. 2015 Postdoctoral researcher in the Mathematics Department of Universidade Federal do Rio Grande do Norte (UFRN), Brazil. 2014 PhD from Ecole´ Normale Superieure´ de Lyon, under the supervision of Olivier Laurent, in the field of theoretical computer science. I was employed by CNRS under the Marie Curie fellowship \MALOA", and had a 1-month secondment split between the University of Oxford (in the team of Luke Ong) and Ecole´ Polytechnique (in the team of Dale Miller). Thesis title: On the Semantics of Disjunctive Logic Programs1 2010 Master of Science degree from MPLA (graduate program in Logic, Algorithms and Computation of the University of Athens and of the Technical University of Athens),2 mathematical logic specialty, grade 8.23/10. 2007 Bachelor's degree from the Department of Mathematics of the University of Athens, specialty of pure mathematics, grade \excellent" (8.51/10). Seminars and schools • Logoi school on Linear Logic and Geometry of Interaction. -

Toward an Automated Vulnerability Comparison of Open Source IMAP Servers Chaos Golubitsky – Carnegie Mellon University
Toward an Automated Vulnerability Comparison of Open Source IMAP Servers Chaos Golubitsky – Carnegie Mellon University ABSTRACT The attack surface concept provides a means of discussing the susceptibility of software to as-yet-unknown attacks. A system’s attack surface encompasses the methods the system makes available to an attacker, and the system resources which can be used to further an attack. A measurement of the size of the attack surface could be used to compare the security of multiple systems which perform the same function. The Internet Message Access Protocol (IMAP) has been in existence for over a decade. Relative to HTTP or SMTP, IMAP is a niche protocol, but IMAP servers are widely deployed nonetheless. There are three popular open source UNIX IMAP servers – UW-IMAP, Cyrus, and Courier-IMAP – and there has not been a formal security comparison between them. In this paper, I use attack surfaces to compare the relative security risks posed by these three products. I undertake this evaluation in service of two complementary goals: to provide an honest examination of the security postures and risks of the three servers, and to advance the study of attack surfaces by performing an automated attack surface measurement using a methodology based on counting entry and exit points in the code. Introduction Contributions and Roadmap System administrators frequently confront the The paper makes two major contributions. First, problem of selecting a software package to perform a I undertake an in-depth discussion of the relative secu- desired function. Many considerations affect this deci- rity postures of the three major open source IMAP sion, including functionality, ease of installation, soft- servers in use today. -

BSD UNIX Toolbox 1000+ Commands for Freebsd, Openbsd
76034ffirs.qxd:Toolbox 4/2/08 12:50 PM Page iii BSD UNIX® TOOLBOX 1000+ Commands for FreeBSD®, OpenBSD, and NetBSD®Power Users Christopher Negus François Caen 76034ffirs.qxd:Toolbox 4/2/08 12:50 PM Page ii 76034ffirs.qxd:Toolbox 4/2/08 12:50 PM Page i BSD UNIX® TOOLBOX 76034ffirs.qxd:Toolbox 4/2/08 12:50 PM Page ii 76034ffirs.qxd:Toolbox 4/2/08 12:50 PM Page iii BSD UNIX® TOOLBOX 1000+ Commands for FreeBSD®, OpenBSD, and NetBSD®Power Users Christopher Negus François Caen 76034ffirs.qxd:Toolbox 4/2/08 12:50 PM Page iv BSD UNIX® Toolbox: 1000+ Commands for FreeBSD®, OpenBSD, and NetBSD® Power Users Published by Wiley Publishing, Inc. 10475 Crosspoint Boulevard Indianapolis, IN 46256 www.wiley.com Copyright © 2008 by Wiley Publishing, Inc., Indianapolis, Indiana Published simultaneously in Canada ISBN: 978-0-470-37603-4 Manufactured in the United States of America 10 9 8 7 6 5 4 3 2 1 Library of Congress Cataloging-in-Publication Data is available from the publisher. No part of this publication may be reproduced, stored in a retrieval system or transmitted in any form or by any means, electronic, mechanical, photocopying, recording, scanning or otherwise, except as permitted under Sections 107 or 108 of the 1976 United States Copyright Act, without either the prior written permission of the Publisher, or authorization through payment of the appropriate per-copy fee to the Copyright Clearance Center, 222 Rosewood Drive, Danvers, MA 01923, (978) 750-8400, fax (978) 646-8600. Requests to the Publisher for permis- sion should be addressed to the Legal Department, Wiley Publishing, Inc., 10475 Crosspoint Blvd., Indianapolis, IN 46256, (317) 572-3447, fax (317) 572-4355, or online at http://www.wiley.com/go/permissions. -
H2418.1 EMC-Computer Generated Solutions E-Mail Management and E-Discovery Solution Overview
Solution Overview EMC-Computer Generated Solutions E-mail Management and E-discovery Solution The Big Picture • Saves time, money, and space on • Helps reduce help desk calls and e-mail servers because the application lessens IT time spent manually runs on a different server (no code is archiving e-mail loaded on the e-mail server) • Delivers a secure corporate e-mail sys- • Remote calls to e-mail servers allow tem that protects valuable intellectual Unlimited Mailbox to run 24 hours per property, as well as complying with day, seven days a week without any government regulatory standards impact on e-mail server performance regarding e-mail storage and retention • Supports all known e-mail platforms, • Delivers immediate time to value including Microsoft Exchange, Lotus by enabling businesses to conduct Domino, Novell GroupWise, SunOne, legal discovery in-house, minimizing and UNIX Sendmail the need for expensive outside e-discovery fees • Provides complete compatibility with double-byte character support •Lowers the total cost of ownership by reducing operational and adminis- • Reduces disk and tape storage trative costs with self-managing and required to back up mail servers and self-healing content-addressed improves the performance of the storage (CAS) backup and recovery of e-mails • Provides long-term data retention • Reduces e-mail server farm as older capabilities, so content cannot be messages are moved to stable, overwritten or changed and is kept for less-expensive media a definable period of time, ensuring •Reduces licensing fees for operating its authenticity and meeting regulatory and backup systems, maintenance requirements costs, and support communications costs A unique, flexible solution that reduces costs and provides faster, less-expensive, lower-risk e-discovery The number and size of e-mails received at any given company, any given day, is becoming increasingly difficult and costly to manage. -
Groupwise Internet Agent
GroupWise Internet Agent April 7, 2000 Novell Confidential Manual Rev 99a24 8 February 00 Legal Notices Novell, Inc. makes no representations or warranties with respect to the contents or use of this documentation, and specifically disclaims any express or implied warranties of merchantability or fitness for any particular purpose. Further, Novell, Inc. reserves the right to revise this publication and to make changes to its content, at any time, without obligation to notify any person or entity of such revisions or changes. Further, Novell, Inc. makes no representations or warranties with respect to any software, and specifically disclaims any express or implied warranties of merchantability or fitness for any particular purpose. Further, Novell, Inc. reserves the right to make changes to any and all parts of Novell software, at any time, without any obligation to notify any person or entity of such changes. This product may require export authorization from the U.S. Department of Commerce prior to exporting from the U.S. or Canada. Copyright © 1993-1999 Novell, Inc. All rights reserved. No part of this publication may be reproduced, photocopied, stored on a retrieval system, or transmitted without the express written consent of the publisher. U.S. Patent Nos. 4,555,775; 4,580,218; 5,412,772; 5,701,459; 5,717,912; 5,760,772; 5,870,739; 5,873,079; 5,884,304; 5,903,755; 5,913,209; 5,924,096; 5,946,467; D393,457 and U.S. Patents Pending. Novell, Inc. 122 East 1700 South Provo, UT 84606 U.S.A. www.novell.com GroupWise Internet Agent February 2000 104-001304-001 Online Documentation: To access the online documentation for this and other Novell products, and to get updates, see www.novell.com/documentation. -

Install Sendmail Mail Server on Debian GNU / Linux
Walking in Light with Christ - Faith, Computing, Diary Articles & tips and tricks on GNU/Linux, FreeBSD, Windows, mobile phone articles, religious related texts http://www.pc-freak.net/blog Install Sendmail mail server on Debian GNU / Linux Author : admin Installing sendmail on Debian Linux is something not so common these days. As sendmail has been overshadowed by his competitors Exim and Postfix. By default Debian Linux comes with Exim (light) installed as Exim is tiny and perfectly suitable for dealing with small and mid-sized SMTP needs. The reason why sendmail has been moved out by its competitors over the last 15 years is sendmail configuration is one big hell and besides that sendmail has been well known for its many security remote exploit holes - making it a famous target for crackers. Well anyways in some cases sendmail is necessary to install especially if you have a client which wants to have it set up. In this short article I will show how very basic sendmail installation on Debian host is done. blackstar:~# apt-get install sendmail-bin sensible-mda Reading package lists... Done Building dependency tree Reading state information... Done The following extra packages will be installed: sendmail-base sendmail-cf sensible-mda Suggested packages: sendmail-doc logcheck resolvconf sasl2-bin The following packages will be REMOVED: exim4 exim4-base exim4-config exim4-daemon-light sa-exim task-mail-server The following NEW packages will be installed: sendmail-base sendmail-bin sendmail-cf 0 upgraded, 3 newly installed, 6 to remove and 26 not upgraded. Need to get 1,626 kB of archives. -
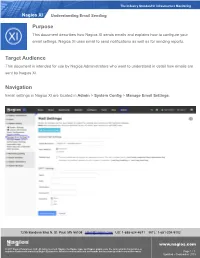
Understanding Email Sending in Nagios XI
The Industry Standard In Infrastructure Monitoring Nagios XI Understanding Email Sending Purpose This document describes how Nagios XI sends emails and explains how to configure your email settings. Nagios XI uses email to send notifications as well as for sending reports. Target Audience This document is intended for use by Nagios Administrators who want to understand in detail how emails are sent by Nagios XI. Navigation Email settings in Nagios XI are located in Admin > System Config > Manage Email Settings. 1295 Bandana Blvd N, St. Paul, MN 55108 [email protected] US: 1-888-624-4671 INTL: 1-651-204-9102 www.nagios.com © 2017 Nagios Enterprises, LLC. All rights reserved. Nagios, the Nagios logo, and Nagios graphics are the servicemarks, trademarks, or registered trademarks owned by Nagios Enterprises. All other servicemarks and trademarks are the property of their respective owner. Page 1 / 7 Updated – September, 2018 The Industry Standard In Infrastructure Monitoring Nagios XI Understanding Email Sending Web Browser Behavior There are some behaviors of your web browser which you need to be aware of. A lot of different web browsers will auto-complete / auto-populate fields on a web page when it loads. This usually only occurs when it sees a common field that does not have a value, it may have a saved value for that "named field" and hence it will populate that field with that saved value. If you open the Manage Email Settings page in Nagios XI you might notice that the username and password fields are already populated. You know that you didn't put a value in here, especially when this is the first time you've visited this page on a fresh install of Nagios XI. -

Postfix−Cyrus−Web−Cyradm−HOWTO
Postfix−Cyrus−Web−cyradm−HOWTO Luc de Louw luc at delouw.ch Revision History Revision 1.2.0 2002−10−16 Revised by: ldl The first release of the 1.2 version. Revision 1.1.7 2002−10−15 Revised by: ldl Added Michael Muenz' hints for SMTP AUTH, corrected ca−cert related mistake, improved SGML code (more metadata), updated the software mentioned in the document. Revision 1.1.6 2002−06−14 Revised by: ldl Added sasl_mech_list: PLAIN to imapd.conf, added web−cyradm Mailinglist, added more to web−cyradm Revision 1.1.5 2002−06−11 Revised by: ldl Added new SQL query to initialize web−cyradm to have full data integrity in the MySQL Database, mysql−mydestination.cf reported to be operational as expected. Revision 1.1.4 2002−05−15 Revised by: ldl Added description what is needed in /etc/services Another fix for pam_mysql compile, updated software versions. Revision 1.1.3 2002−05−08 Revised by: ldl Added more description for web−cyradm, fix for wrong path of the saslauthdb−socket, Fix for wrong place of com_err.h, protection of the TLS/SSL private key. Revision 1.1.2 2002−04−29 Revised by: ldl Added description for Redhat users how to install the init scripts. Revision 1.1.1 2002−04−29 Revised by: ldl Fixed bug in configuring cyrus−IMAP (disabled unused kerberos authentication) Revision 1.1.0 2002−04−28 Revised by: ldl Initial support for building cyrus from source, dropped binary installation for Cyrus, because configuration has changed with Release 2.1.x Revision 1.0.2 2002−04−25 Revised by: ldl Added basic description for sieve and correct sender handling, minor fixes to db related stuff, Added mysql−lookup for »mydestination« , fixed bug for building postfix with mysql support. -

Clé USB Bootable Openbsd Clé USB Bootable Openbsd
2018/05/25 10:12 1/11 Clé USB bootable OpenBSD Clé USB bootable OpenBSD Je vais indiquer ici comment créer une clé USB bootable avec OpenBSD. Intérêt ? Quel est l'intérêt de la chose ? Et bien il est multiple : Avoir un UNIX sous la main, c'est le bien Avoir un système de secours sur clé USB, c'est le pied Booter sur un système super-sécurisé, ça le fé ! C'est fun C'est la frime Les différents usages : obtenir un dmesg super détaillé pour identifier du matériel récupérer un système endommagé Avoir un anti-virus non compromis installer OpenBSD sur une nouvelle machine (oui, en plus d'être bootable, l'installation est possible !) faire de la maintenance Bref, ça le fait bien. Installation C'est l'enfance de l'art : booter sur un CD OpenBSD (i386 pour une plus grande compatibilité, mais ça marche pareil avec un amd64…), une clé USB déjà préparée, une disquette, en réseau… et lancez l'installation ! Repérez bien le device qui correspond à votre clé USB (sd0 ou sd1 probablement) et installez le système dessus. Le plus simple ? Une seule partition 'a', pas de swap, créer un utilisateur autre que root, n'installez pas compXX.tgz, ni gameXX.tgz (pour gagner quelques Mo…). Et surtout, utilisez les DUID pour identifier les disques au montage ! Exemple <mavie> J'ai reçu une clé USB Duracell de 4Go avec le programme de fidélité Orange Davantage Internet. Cool. Je m'en va installer le bousin là-dessus. Bon, le formatage prend des plombes, l'installation complète met deux heures pour aboutir, le Chez moi..