Cyrus Mail Server 2 Table of Contents
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
CYRUS: BUILD YOUR TUTORIAL OWN EMAIL SERVER Don’T Trust Google? We’Ll Help You Navigate the Sea of JOHN LANE Acronyms to Build Your Own Mailserver
TUTORIAL MAILSERVER CYRUS: BUILD YOUR TUTORIAL OWN EMAIL SERVER Don’t trust Google? We’ll help you navigate the sea of JOHN LANE acronyms to build your own mailserver. ou can’t beat the convenience and ease of use access their mail by connecting to the server using WHY DO THIS? offered by Gmail. But unfortunately, all that any IMAP-capable email client application. • Take control of your Yfree storage comes at a price: your privacy. You will need a, preferably new, server for this email provision. Spam, intrusive adverts and snooping from unnamed project and you’ll need root access to it. Our examples • Stop outside agencies government agencies are the inevitable downside of use Arch Linux, and we created a new virtual server. from scanning the using someone else’s service for free. So why not Begin by installing Cyrus (build the Arch User content of your emails. build your own email server including anti-spam, Repository package first – see the boxout below-right): • Get webmail without advertising. anti-virus and webmail? $ pacman -U ~build/cyrus-imapd/cyrus-imapd-2.4.17-5-x86_64. You can use your own server to retrieve messages pkg.tar.xz from other mailservers, such as those provided by The default configuration writes data to /var/imap internet service providers, or other services like those and user mailboxes to /var/spool/imap. You can from Google and Yahoo. But you don’t need to rely on change this if you prefer another location; we’ll others if you have your own server. If you have a configure our server to use /srv/mail/cyrus to domain name that you control, and if you can give your illustrate this. -

Oldschool E-Mail Setup Eine Freakshow
Oldschool E-mail Setup Eine Freakshow [email protected] Chemnitzer Linuxtage, 2016 (Screenshot GMX vor >15 Jahren: Waybackmachine zu www.gmx.net) (Screenshot GMX heute) (Screenshot Gmail heute) Lösungen? ● Claws ● Mutt ● Eudora ● Netscape Navigator ● Evolution ● Opera M2 ● GMX ● Outlook ● Gnus ● SquirrelMail ● Hotmail ● The Bat! ● Hushmail ● Thunderbird ● KMail ● … Flußgrafik Email Netz MTA MRA MDA MUA MSA MTA Netz Hipster! ● KISS ● YAGNI ● DRY ● NIH ● Divide And Conquer ● Everything is a file ● No vendor lock-in ● Mißtraue Autoritäten – fördere Dezentralisierung Netz Netz Emails Client, den ich Remote verwenden kann Leicht erweiterbar Emails lokal Filter Offenes Format Adressen Netz Netz Abholen Transportformat? Pull Subject 1 Email = 1 File Keine Spuren X-List-ID Mit Hierarchien am Server Beliebige Einfaches Suchen Header Verlässliches Suchen Verarbeitung mit Unix Tools Client, den ich Remote verwenden kann Leicht erweiterbar Emails lokal Filter Offenes Format Adressen Netz Netz Abholen Transportformat? Pull Subject 1 Email = 1 File Keine Spuren X-List-ID Mit Hierarchien am Server Beliebige Einfaches Suchen Header Verlässliches Suchen Verarbeitung mit Unix Tools mbox Maildir mh Client, den ich Remote verwenden kann Leicht erweiterbar Emails lokal Filter Offenes Format Adressen Netz Netz Abholen Transportformat? Pull Subject 1 Email = 1 File Keine Spuren X-List-ID Mit Hierarchien am Server Beliebige Einfaches Suchen Header Verlässliches Suchen Verarbeitung mit Unix Tools mbox Maildir mh tmp 1439306571.1269_0.elvis ~/Post/Technik/Wikitech new 1448267819.5940_0.spencer ... 1457079728.2000_0.spencer:2, cur 1456839383.9873_0.nepomuk:2,SR 1457166567.23654_0.spencer:2,S ... Client, den ich Remote verwenden kann Leicht erweiterbar Filter Adressen Netz Netz Abholen Pull Subject Maildir Keine Spuren X-List-ID am Server Beliebige Header Client, den ich Remote verwenden kann Leicht erweiterbar Filter Adressen Netz Netz Abholen Pull Subject Maildir Keine Spuren X-List-ID am Server Beliebige Header fetchmail getmail mpop .. -

Resurrect Your Old PC
Resurrect your old PCs Resurrect your old PC Nostalgic for your old beige boxes? Don’t let them gather dust! Proprietary OSes force users to upgrade hardware much sooner than necessary: Neil Bothwick highlights some great ways to make your pensioned-off PCs earn their keep. ardware performance is constantly improving, and it is only natural to want the best, so we upgrade our H system from time to time and leave the old ones behind, considering them obsolete. But you don’t usually need the latest and greatest, it was only a few years ago that people were running perfectly usable systems on 500MHz CPUs and drooling over the prospect that a 1GHz CPU might actually be available quite soon. I can imagine someone writing a similar article, ten years from now, about what to do with that slow, old 4GHz eight-core system that is now gathering dust. That’s what we aim to do here, show you how you can put that old hardware to good use instead of consigning it to the scrapheap. So what are we talking about when we say older computers? The sort of spec that was popular around the turn of the century. OK, while that may be true, it does make it seem like we are talking about really old hardware. A typical entry-level machine from six or seven years ago would have had something like an 800MHz processor, Pentium 3 or similar, 128MB of RAM and a 20- 30GB hard disk. The test rig used for testing most of the software we will discuss is actually slightly lower spec, it has a 700MHz Celeron processor, because that’s what I found in the pile of computer gear I never throw away in my loft, right next to my faithful old – but non-functioning – Amiga 4000. -

Design Document
SPEC OSG Mailserver Subcommittee SPECmail2009 Benchmark Architecture White Paper Revision: v1.0 Date: 22 December 2008 Copyright © 2001-2009 Standard Performance Evaluation Corporation. All Rights Reserved. 1. Introduction 1.1 Overview SPECmail2009 is a software benchmark designed to measure a system's ability to act as an enterprise mail server servicing email requests, based on the Internet standard protocols SMTP and IMAP4. The benchmark concentrates on the workload encountered by corporate mail servers, with an overall user count in the range of 150 to 10,000 (or more) users. It models IMAP business users accessing IMAP servers over fast local area networks (LAN) instead of broadband, WAN or dialup access speeds. Two separate metrics measure e-mail servers with and without secure network connections (SSL). SPECmail2009 has been developed by the Standard Performance Evaluation Corporation (SPEC), a non-profit group of computer vendors, system integrators, universities, research organizations, publishers, and consultants. This paper discusses the benchmark principles and architecture, and the rationale behind the key design decisions. It also outlines the workload used in the benchmark, and the general steps needed to run a benchmark. However those aspects are covered in more detail in other documents. 1.2 Organization of this Paper Chapter 2 discusses the basic goals and non-goals of the benchmark. Chapter 3 introduces the two performance metrics for SPECmail2009 – IMAP sessions per hour - and how it relates to the transaction mix imposed on the system under test.. Chapter 4 explains the benchmark workload - how it was derived, how it translates into configuration parameters for the benchmark tool and size calculations for planning a benchmark, and how it relates to the benchmark metric. -

Toward an Automated Vulnerability Comparison of Open Source IMAP Servers Chaos Golubitsky – Carnegie Mellon University
Toward an Automated Vulnerability Comparison of Open Source IMAP Servers Chaos Golubitsky – Carnegie Mellon University ABSTRACT The attack surface concept provides a means of discussing the susceptibility of software to as-yet-unknown attacks. A system’s attack surface encompasses the methods the system makes available to an attacker, and the system resources which can be used to further an attack. A measurement of the size of the attack surface could be used to compare the security of multiple systems which perform the same function. The Internet Message Access Protocol (IMAP) has been in existence for over a decade. Relative to HTTP or SMTP, IMAP is a niche protocol, but IMAP servers are widely deployed nonetheless. There are three popular open source UNIX IMAP servers – UW-IMAP, Cyrus, and Courier-IMAP – and there has not been a formal security comparison between them. In this paper, I use attack surfaces to compare the relative security risks posed by these three products. I undertake this evaluation in service of two complementary goals: to provide an honest examination of the security postures and risks of the three servers, and to advance the study of attack surfaces by performing an automated attack surface measurement using a methodology based on counting entry and exit points in the code. Introduction Contributions and Roadmap System administrators frequently confront the The paper makes two major contributions. First, problem of selecting a software package to perform a I undertake an in-depth discussion of the relative secu- desired function. Many considerations affect this deci- rity postures of the three major open source IMAP sion, including functionality, ease of installation, soft- servers in use today. -

Release Notes for Debian 7.0 (Wheezy), Kfreebsd 64-Bits PC
Release Notes for Debian 7.0 (wheezy), kFreeBSD 64-bits PC The Debian Documentation Project (http://www.debian.org/doc/) November 20, 2018 Release Notes for Debian 7.0 (wheezy), kFreeBSD 64-bits PC This document is free software; you can redistribute it and/or modify it under the terms of the GNU General Public License, version 2, as published by the Free Software Foundation. This program is distributed in the hope that it will be useful, but WITHOUT ANY WARRANTY; without even the implied warranty of MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the GNU General Public License for more details. You should have received a copy of the GNU General Public License along with this program; if not, write to the Free Software Foundation, Inc., 51 Franklin Street, Fifth Floor, Boston, MA 02110-1301 USA. The license text can also be found at http://www.gnu.org/licenses/gpl-2.0.html and /usr/ share/common-licenses/GPL-2 on Debian. ii Contents 1 Introduction 1 1.1 Reporting bugs on this document . 1 1.2 Contributing upgrade reports . 1 1.3 Sources for this document . 2 2 What’s new in Debian 7.0 3 2.1 Supported architectures . 3 2.2 What’s new for kFreeBSD? . 4 2.3 What’s new in the distribution? . 4 2.3.1 CDs, DVDs and BDs . 5 2.3.2 Multiarch . 5 2.3.3 Dependency booting . 5 2.3.4 systemd . 5 2.3.5 Multimedia . 5 2.3.6 Hardened security . 6 2.3.7 AppArmor . -

Symantec White Paper
QUARTERLY REPORT: SYMANTEC ENTERPRISE SECURITY SYMANTEC REPORT: QUARTERLY Symantec Intelligence Quarterly July - September, 2009 Published October 2009 Technical Brief: Symantec Enterprise Security Symantec Intelligence Quarterly July - September, 2009 Contents Introduction . 1 Highlights . 2 Metrics. 2 Meeting the Challenge of Sophisticated Attacks . 8 Timeline of a zero-day event . 8 How secure are security protocols?. 11 Why attackers use packers. 14 Protection and Mitigation . 16 Appendix A—Best Practices . 18 Appendix B—Methodologies. 20 Credits . 24 Symantec Intelligence Quarterly July - September, 2009 Introduction Symantec has established some of the most comprehensive sources of Internet threat data in the world through the Symantec™ Global Intelligence Network. More than 240,000 sensors in over 200 countries monitor attack activity through a combination of Symantec products and services such as Symantec DeepSight™ Threat Management System, Symantec™ Managed Security Services and Norton™ consumer products, as well as additional third-party data sources. Symantec also gathers malicious code intelligence from more than 130 million client, server, and gateway systems that have deployed its antivirus products. Additionally, the Symantec distributed honeypot network collects data from around the globe, capturing previously unseen threats and attacks and providing valuable insight into attacker methods. Spam data is captured through the Symantec probe network, a system of more than 2.5 million decoy email accounts, Symantec MessageLabs™ Intelligence, and other Symantec technologies in more than 86 countries from around the globe. Over 8 billion email messages, as well as over 1 billion Web requests, are scanned per day across 16 data centers. Symantec also gathers phishing information through an extensive antifraud community of enterprises, security vendors, and more than 50 million consumers. -

Ispmail Tutorial for Debian Lenny
6.10.2015 ISPmail tutorial for Debian Lenny ISPmail tutorial for Debian Lenny Add new comment 223533 reads This tutorial is for the former stable version "Debian Lenny". If you are using "Debian Squeeze" then please follow the new tutorial. A spanish translation of this tutorial is also available courtesy of José Ramón Magán Iglesias. What this tutorial is about You surely know the internet service providers that allow you to rent a domain and use it to receive emails. If you have a computer running Debian which is connected to the internet permanently you can do that yourself. You do not even need to have a fixed IP address thanks to dynamic DNS services like dyndns.org. All you need is this document, a cup of tea and a little time. When you are done your server will be able to... receive and store emails for your users from other mail servers let your users retrieve the email through IMAP and POP3 even with SSL to encrypt to connection receive and forward ("relay") email for your users if they are authenticated offer a webmail interface to read emails in a web browser detect most spam emails and filter them out or tag them License/Copyright This tutorial book is copyrighted 2009 Christoph Haas (email@christophhaas.de). It can be used freely under the terms of the GNU General Public License. Don't forget to refer to this URL when using it. Thank you. Changelog 17.6.09: Lenny tutorial gets published. 19.6.09: The page on SPF checks is temporarily offline. -

School and Email Systems
Email system survey: Top 50 US Colleges US Note Email system Server queried Greeting News School ranking 1 Harvard University Mail2World imap.college.harvard.edu OK Mail2World IMAP4 Server 2.5 ready Sun Java SMS imap.princeton.edu OK [CAPABILITY IMAP4 IMAP4rev1 ACL QUOTA LITERAL+ NAMESPACE UIDPLUS CHILDREN BINARY LANGUAGE XSENDER X-NETSCAPE XSERVERINFO Princeton University 1 AUTH=PLAIN] Messaging Multiplexor (Sun Java(tm) System Messaging Server 6.2-5.05 (built Feb 16 2006)) Unknown mail.yale.edu OK [CAPABILITY IMAP4REV1 LOGIN-REFERRALS AUTH=PLAIN AUTH=LOGIN] pantheon-po14.its.yale.edu IMAP4rev1 2002.336 at Mon, 26 Jul 2010 14:10:23 Yale University 3 -0400 (EDT) Dovecot imap-server.its.caltech.edu OK Dovecot ready. Cyrus mail.alumni.caltech.edu OK posteaux1.caltech.edu Cyrus IMAP4 v2.2.12-Invoca-RPM-2.2.12-10.el4_8.4 server ready 4 California Institute of Technology Dovecot imap.gps.caltech.edu OK dovecot ready. Dovecot theory.caltech.edu OK dovecot ready. 4 Massachusetts Institute of Technology Unable to find a server to query (username.mail.mit.edu)Unknown 4 Stanford University Zimbra zm01.stanford.edu OK zm01.stanford.edu Zimbra IMAP4rev1 server ready Zimbra mailbox.zimbra.upenn.edu OK mailbox.zimbra.upenn.edu Zimbra IMAP4rev1 service ready 4 University of Pennsylvania Exchange 2010 webmail.wharton.upenn.edu OK The Microsoft Exchange IMAP4 service is ready. Dovecot imap.nevis.columbia.edu OK [CAPABILITY IMAP4rev1 LITERAL+ SASL-IR LOGIN-REFERRALS ID ENABLE AUTH=PLAIN] Dovecot ready. Lotus Domino equinox.law.columbia.edu OK Domino IMAP4 -
The Bioinformatics Lab SS11 Mail / DNS Antonia Stank 20.06.2011
The bioinformatics lab SS11 Mail / DNS Antonia Stank 20.06.2011 1 Introduction The Domain Name System (DNS) is a one of the most important systems in the network. It is a hierarchical naming system which is built on a distributed database for computers, services or any resource connected to the Internet. The DNS can also be used in a private or local network. The main service of a DNS is that it serves as a kind of “phone book” for the internet or local network by translating user-friendly hostnames into specific IP addresses. For example it is much easier to remember the internet address: www.google.de than the corresponding IP address 209.85.148.99. So it can translate names to numbers and vice versa and helps therefore to connect on a specific IP address without knowing the number. An e-mail-server or just mail server is a server which can handle the mail traffic. It is necessary for sending, receiving, forwarding and saving mails. An Internet Message Access Protocol (IMAP) server is a server that provides the usage of the most prevalent IMAP protocol. There is also another common protocol which is the so called Post Office Protocol (POP). The advantage of the IMAP is that it allows an e-mail client access to a remote mail server. The e-mail clients using IMAP leave the mails on the server until they are explicitly deleted by the user. This and some other advantages make it possible to allow multiple clients to have access to the same mailbox. -
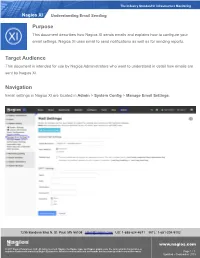
Understanding Email Sending in Nagios XI
The Industry Standard In Infrastructure Monitoring Nagios XI Understanding Email Sending Purpose This document describes how Nagios XI sends emails and explains how to configure your email settings. Nagios XI uses email to send notifications as well as for sending reports. Target Audience This document is intended for use by Nagios Administrators who want to understand in detail how emails are sent by Nagios XI. Navigation Email settings in Nagios XI are located in Admin > System Config > Manage Email Settings. 1295 Bandana Blvd N, St. Paul, MN 55108 [email protected] US: 1-888-624-4671 INTL: 1-651-204-9102 www.nagios.com © 2017 Nagios Enterprises, LLC. All rights reserved. Nagios, the Nagios logo, and Nagios graphics are the servicemarks, trademarks, or registered trademarks owned by Nagios Enterprises. All other servicemarks and trademarks are the property of their respective owner. Page 1 / 7 Updated – September, 2018 The Industry Standard In Infrastructure Monitoring Nagios XI Understanding Email Sending Web Browser Behavior There are some behaviors of your web browser which you need to be aware of. A lot of different web browsers will auto-complete / auto-populate fields on a web page when it loads. This usually only occurs when it sees a common field that does not have a value, it may have a saved value for that "named field" and hence it will populate that field with that saved value. If you open the Manage Email Settings page in Nagios XI you might notice that the username and password fields are already populated. You know that you didn't put a value in here, especially when this is the first time you've visited this page on a fresh install of Nagios XI. -

Efficient Spam Filtering System Based on Smart Cooperative Subjective and Objective Methods*
Int. J. Communications, Network and System Sciences, 2013, 6, 88-99 http://dx.doi.org/10.4236/ijcns.2013.62011 Published Online February 2013 (http://www.scirp.org/journal/ijcns) Efficient Spam Filtering System Based on Smart * Cooperative Subjective and Objective Methods Samir A. Elsagheer Mohamed1,2 1College of Computer, Qassim University, Qassim, KSA 2Electrical Engineering Department, Faculty of Engineering, Aswan University, Aswan, Egypt Email: [email protected], [email protected] Received September 17, 2012; revised January 16, 2013; accepted January 25, 2013 ABSTRACT Most of the spam filtering techniques are based on objective methods such as the content filtering and DNS/reverse DNS checks. Recently, some cooperative subjective spam filtering techniques are proposed. Objective methods suffer from the false positive and false negative classification. Objective methods based on the content filtering are time con- suming and resource demanding. They are inaccurate and require continuous update to cope with newly invented spammer’s tricks. On the other side, the existing subjective proposals have some drawbacks like the attacks from mali- cious users that make them unreliable and the privacy. In this paper, we propose an efficient spam filtering system that is based on a smart cooperative subjective technique for content filtering in addition to the fastest and the most reliable non-content-based objective methods. The system combines several applications. The first is a web-based system that we have developed based on the proposed technique. A server application having extra features suitable for the enter- prises and closed work groups is a second part of the system. Another part is a set of standard web services that allow any existing email server or email client to interact with the system.