Best of a Decade on Opensource.Com 2010–2019
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Tv Und Video
COMMUNITY-EDITION Frei kopieren und beliebig weiter verteilen ! 01.2013 01.2013 viDeoS SChneiDen unD fernSehen unter linux eo D vi & tv unD viDeo tv Videoschnitt-Praxis S. 22, 28, DVD Linux Mint 14 Mit Openshot und Flowblade selbst gedrehte Clips Maté und Cinnamon für 32- und 64-Bit-PCs durch Effekte und Übergänge aufpeppen rive • g S. 14, DVD Auf dem Prüfstand Die sieben besten Video-Editoren für io • D DV- und HD-Material im direkten Vergleich Linux-Rechner statt Flimmerkiste S. 36, 42, DVD Analog, DVB und Web-TV auf PC und Notebook: Linux-kompatible Hardware finden, optimale Software zum Schauen und Aufnehmen SolusoS 1.2 S. 6 Wieselflinkes Debian mit aktuellen Tools Frischer Wind fürs Tonstudio Bitwig Studio: DAW mit neuen Konzepten, innovativen Tools und flexiblen Plugins S. 68 op & Co. • Bitwig Stu op & Co. t planetarium für den endlich Durchblick Schreibtisch S. 58, DVD im pDf-archiv S. 62, DVD la 12.1 S. 46 Fotorealistischer Blick in den Dokumente ablegen und Allrounder für zu Hause Nachthimmel mit Stellarium wiederfinden mit I-Librarian und das Schulnetz freier adapter für Systemdaten im google Drive S. 74, DVD Blick mit top & Co. Transparenter Zugriff auf den Kritische Zustände erkennen Gratisspeicher mit Grive und blitzschnell reagieren S. 82 Stellarium • Defrag • Stellarium • Defrag 4 196067 008502 01 www.linux-user.de EDITORIAL Zahlenspiele Sehr geehrte Leserinnen und Leser, mussten wir vor einem Monat Macht man sich jedoch die Mühe, haben. So lässt Microsoft jetzt noch darüber spekulieren, wie genauer hinzusehen, dann fällt statt geplanter vier nur noch zwei sich die jüngste Windows-Inkar- schnell auf, dass Windows-CFO Millionen Einheiten seines Sur- nation wohl im Markt machen Reller einige wichtige Details de- face-Tabletts fertigen [2]. -
Performance Counters in Htop 3.0
Slide: [ ] Talk: Perf counters in htop 3.0 Presenter: https://hisham.hm PID USER PRI NI VIRT RES SHR S CPU% MEM% TIME+ Command Performance counters in htop 3.0 Hisham Muhammad @[email protected] https://hisham.hm Slide: [ 2 ] Date: 2018-08-25 Talk: Perf counters in htop 3.0 Presenter: https://hisham.hm PID USER PRI NI VIRT RES SHR S CPU% MEM% TIME+ Command About me original author of htop, a project started in 2004 http://hisham.hm/htop/ lead dev of LuaRocks, package manager for Lua http://luarocks.org/ co-founder of the GoboLinux distribution http://gobolinux.org/ developer at Kong – FLOSS API gateway http://getkong.org/ (we’re hiring!) Slide: [ 3 ] Date: 2018-08-25 Talk: Perf counters in htop 3.0 Presenter: https://hisham.hm PID USER PRI NI VIRT RES SHR S CPU% MEM% TIME+ Command What is htop an interactive process manager intended to be “a better top” by this all I originally meant was: scrolling! (versions of top improved a lot since!) Slide: [ 4 ] Date: 2018-08-25 Talk: Perf counters in htop 3.0 Presenter: https://hisham.hm PID USER PRI NI VIRT RES SHR S CPU% MEM% TIME+ Command Hello, htop! Slide: [ 5 ] Date: 2018-08-25 Talk: Perf counters in htop 3.0 Presenter: https://hisham.hm PID USER PRI NI VIRT RES SHR S CPU% MEM% TIME+ Command htop beyond Linux Linux MacOS FreeBSD OpenBSD DragonFlyBSD Solaris (illumos) Slide: [ 6 ] Date: 2018-08-25 Talk: Perf counters in htop 3.0 Presenter: https://hisham.hm PID USER PRI NI VIRT RES SHR S CPU% MEM% TIME+ Command Then Apple released a broken kernel.. -

Resurrect Your Old PC
Resurrect your old PCs Resurrect your old PC Nostalgic for your old beige boxes? Don’t let them gather dust! Proprietary OSes force users to upgrade hardware much sooner than necessary: Neil Bothwick highlights some great ways to make your pensioned-off PCs earn their keep. ardware performance is constantly improving, and it is only natural to want the best, so we upgrade our H system from time to time and leave the old ones behind, considering them obsolete. But you don’t usually need the latest and greatest, it was only a few years ago that people were running perfectly usable systems on 500MHz CPUs and drooling over the prospect that a 1GHz CPU might actually be available quite soon. I can imagine someone writing a similar article, ten years from now, about what to do with that slow, old 4GHz eight-core system that is now gathering dust. That’s what we aim to do here, show you how you can put that old hardware to good use instead of consigning it to the scrapheap. So what are we talking about when we say older computers? The sort of spec that was popular around the turn of the century. OK, while that may be true, it does make it seem like we are talking about really old hardware. A typical entry-level machine from six or seven years ago would have had something like an 800MHz processor, Pentium 3 or similar, 128MB of RAM and a 20- 30GB hard disk. The test rig used for testing most of the software we will discuss is actually slightly lower spec, it has a 700MHz Celeron processor, because that’s what I found in the pile of computer gear I never throw away in my loft, right next to my faithful old – but non-functioning – Amiga 4000. -
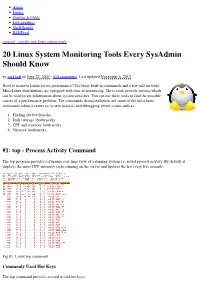
20 Linux System Monitoring Tools Every Sysadmin Should Know by Nixcraft on June 27, 2009 · 315 Comments · Last Updated November 6, 2012
About Forum Howtos & FAQs Low graphics Shell Scripts RSS/Feed nixcraft - insight into linux admin work 20 Linux System Monitoring Tools Every SysAdmin Should Know by nixCraft on June 27, 2009 · 315 comments · Last updated November 6, 2012 Need to monitor Linux server performance? Try these built-in commands and a few add-on tools. Most Linux distributions are equipped with tons of monitoring. These tools provide metrics which can be used to get information about system activities. You can use these tools to find the possible causes of a performance problem. The commands discussed below are some of the most basic commands when it comes to system analysis and debugging server issues such as: 1. Finding out bottlenecks. 2. Disk (storage) bottlenecks. 3. CPU and memory bottlenecks. 4. Network bottlenecks. #1: top - Process Activity Command The top program provides a dynamic real-time view of a running system i.e. actual process activity. By default, it displays the most CPU-intensive tasks running on the server and updates the list every five seconds. Fig.01: Linux top command Commonly Used Hot Keys The top command provides several useful hot keys: Hot Usage Key t Displays summary information off and on. m Displays memory information off and on. Sorts the display by top consumers of various system resources. Useful for quick identification of performance- A hungry tasks on a system. f Enters an interactive configuration screen for top. Helpful for setting up top for a specific task. o Enables you to interactively select the ordering within top. r Issues renice command. -

Developer Survey
Developer Survey Questions requiring a response are in r ed . Questions in which a response is NOT required are in blue. This survey is a critical element of the developers workshop. We are using it to capture nuts and bolts information about codes within the community so that we can assess the landscape before the workshop and use this information to drive the discussions. Please collaborate to provide only one submission per code and submit your response using the online survey: h ttps://ucdavis.co1.qualtrics.com/jfe/form/SV_57wtv4gpuaowTsh Basic Information Code identification 1. What is the name of the code? [small text box] 2. Who are the primary authors/maintainers? [medium text box] 3. URL of webpage for the code (if different than the version control repository) [small text box] 4. URL of version control repository (if public) [small text box] Software 1. Which license(s) do you use? Select all that apply. a. Apache license b. BSD license c. GNU General Public License d. GNU Lesser General Public License e. MIT license f. Mozilla Public License g. Common Development and Distribution License h. Eclipse Public License i. Other. Please specify [small text box] j. No license 2. What programming language(s) is your code currently written in? Select all that apply a. Fortran 77 b. Fortran 90 or later c. C d. C++ e. Go f. Python g. Julia h. Matlab i. Other. Please specify. [small text box] 3. List the primary (high-level) code dependencies (e.g., PETSc, deal.ii, FEniCS) [medium text box] 4. List any additional (low-level) code dependencies (e.g., MPI, NetCDF, HDF5) [medium text box] 5. -

SFLC V Conservancy
Trademark Trial and Appeal Board Electronic Filing System. http://estta.uspto.gov ESTTA Tracking number: ESTTA863914 Filing date: 12/11/2017 IN THE UNITED STATES PATENT AND TRADEMARK OFFICE BEFORE THE TRADEMARK TRIAL AND APPEAL BOARD Proceeding 92066968 Party Defendant Software Freedom Conservancy Correspondence PAMELA S CHESTECK Address CHESTEK LEGAL P O BOX 2492 RALEIGH, NC 27602 UNITED STATES Email: [email protected] Submission Motion for Summary Judgment Yes, the Filer previously made its initial disclosures pursuant to Trademark Rule 2.120(a); OR the motion for summary judgment is based on claim or issue pre- clusion, or lack of jurisdiction. The deadline for pretrial disclosures for the first testimony period as originally set or reset: 07/20/2018 Filer's Name Pamela S Chestek Filer's email [email protected] Signature /Pamela S Chestek/ Date 12/11/2017 Attachments Motion for SJ on affirmative defenses-signed.pdf(756280 bytes ) Kuhn-Declara- tion_summary-judgment_as-submitted_reduced-size-signed.pdf(2181238 bytes ) Sandler-declara- tion_summary-judgment_as-submitted-reduced-size-signed.pdf(1777273 bytes ) Chestek declaration_summary-judgment-signed-with-exhibits.pdf(2003142 bytes ) IN THE UNITED STATES PATENT AND TRADEMARK OFFICE BEFORE THE TRADEMARK TRIAL AND APPEAL BOARD In the Mater of Registraion No. 4212971 Mark: SOFTWARE FREEDOM CONSERVANCY Registraion date: September 25, 2012 Sotware Freedom Law Center Peiioner, v. Cancellaion No. 92066968 Sotware Freedom Conservancy Registrant. RESPONDENT’S MOTION FOR SUMMARY JUDGMENT ON ITS AFFIRMATIVE DEFENSES Introducion The Peiioner, Sotware Freedom Law Center (“SFLC”), is a provider of legal services. It had the idea to create an independent enity that would ofer inancial and administraive services for free and open source sotware projects. -

Leitfaden Für Debian-Betreuer
Leitfaden für DebianBetreuer Osamu Aoki, Helge Kreutzmann, and Mechtilde Stehmann August 27, 2021 Leitfaden für DebianBetreuer by Osamu Aoki, Helge Kreutzmann, and Mechtilde Stehmann Copyright © 20142020 Osamu Aoki Permission is hereby granted, free of charge, to any person obtaining a copy of this software and associated documentation files (the ”Software”), to deal in the Software without restriction, including without limitation the rights to use, copy, modify, merge, publish, distribute, sublicense, and/or sell copies of the Software, and to permit persons to whom the Software is furnished to do so, subject to the following conditions: The above copyright notice and this permission notice shall be included in all copies or substantial portions of the Software. THE SOFTWARE IS PROVIDED ”AS IS”, WITHOUT WARRANTY OF ANY KIND, EXPRESS OR IM PLIED, INCLUDING BUT NOT LIMITED TO THE WARRANTIES OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT. IN NO EVENT SHALL THE AUTHORS OR COPYRIGHT HOLDERS BE LIABLE FOR ANY CLAIM, DAMAGES OR OTHER LIABILITY, WHETHER IN AN ACTION OF CONTRACT, TORT OR OTHERWISE, ARISING FROM, OUT OF OR IN CONNECTION WITH THE SOFTWARE OR THE USE OR OTHER DEALINGS IN THE SOFTWARE. Diese Anleitung wurde mit den nachfolgenden Dokumenten als Referenz erstellt: • »Making a Debian Package (AKA the Debmake Manual)«, Copyright © 1997 Jaldhar Vyas. • »The NewMaintainer’s Debian Packaging Howto«, Copyright © 1997 Will Lowe. • »DebianLeitfaden für Neue Paketbetreuer«, Copyright © 19982002 Josip Rodin, 20052017 Osamu Aoki, 2010 Craig Small und 2010 Raphaël Hertzog. Die neuste Version dieser Anleitung sollte • im Paket debmakedoc und • auf der DebianDokumentationsWebsite verfügbar sein. -

Seamless Interoperability and Data Portability in the Social Web for Facilitating an Open and Heterogeneous Online Social Network Federation
Seamless Interoperability and Data Portability in the Social Web for Facilitating an Open and Heterogeneous Online Social Network Federation vorgelegt von Dipl.-Inform. Sebastian Jürg Göndör geb. in Duisburg von der Fakultät IV – Elektrotechnik und Informatik der Technischen Universität Berlin zur Erlangung des akademischen Grades Doktor der Ingenieurwissenschaften - Dr.-Ing. - genehmigte Dissertation Promotionsausschuss: Vorsitzender: Prof. Dr. Thomas Magedanz Gutachter: Prof. Dr. Axel Küpper Gutachter: Prof. Dr. Ulrik Schroeder Gutachter: Prof. Dr. Maurizio Marchese Tag der wissenschaftlichen Aussprache: 6. Juni 2018 Berlin 2018 iii A Bill of Rights for Users of the Social Web Authored by Joseph Smarr, Marc Canter, Robert Scoble, and Michael Arrington1 September 4, 2007 Preamble: There are already many who support the ideas laid out in this Bill of Rights, but we are actively seeking to grow the roster of those publicly backing the principles and approaches it outlines. That said, this Bill of Rights is not a document “carved in stone” (or written on paper). It is a blog post, and it is intended to spur conversation and debate, which will naturally lead to tweaks of the language. So, let’s get the dialogue going and get as many of the major stakeholders on board as we can! A Bill of Rights for Users of the Social Web We publicly assert that all users of the social web are entitled to certain fundamental rights, specifically: Ownership of their own personal information, including: • their own profile data • the list of people they are connected to • the activity stream of content they create; • Control of whether and how such personal information is shared with others; and • Freedom to grant persistent access to their personal information to trusted external sites. -

Bibliography of Erik Wilde
dretbiblio dretbiblio Erik Wilde's Bibliography References [1] AFIPS Fall Joint Computer Conference, San Francisco, California, December 1968. [2] Seventeenth IEEE Conference on Computer Communication Networks, Washington, D.C., 1978. [3] ACM SIGACT-SIGMOD Symposium on Principles of Database Systems, Los Angeles, Cal- ifornia, March 1982. ACM Press. [4] First Conference on Computer-Supported Cooperative Work, 1986. [5] 1987 ACM Conference on Hypertext, Chapel Hill, North Carolina, November 1987. ACM Press. [6] 18th IEEE International Symposium on Fault-Tolerant Computing, Tokyo, Japan, 1988. IEEE Computer Society Press. [7] Conference on Computer-Supported Cooperative Work, Portland, Oregon, 1988. ACM Press. [8] Conference on Office Information Systems, Palo Alto, California, March 1988. [9] 1989 ACM Conference on Hypertext, Pittsburgh, Pennsylvania, November 1989. ACM Press. [10] UNIX | The Legend Evolves. Summer 1990 UKUUG Conference, Buntingford, UK, 1990. UKUUG. [11] Fourth ACM Symposium on User Interface Software and Technology, Hilton Head, South Carolina, November 1991. [12] GLOBECOM'91 Conference, Phoenix, Arizona, 1991. IEEE Computer Society Press. [13] IEEE INFOCOM '91 Conference on Computer Communications, Bal Harbour, Florida, 1991. IEEE Computer Society Press. [14] IEEE International Conference on Communications, Denver, Colorado, June 1991. [15] International Workshop on CSCW, Berlin, Germany, April 1991. [16] Third ACM Conference on Hypertext, San Antonio, Texas, December 1991. ACM Press. [17] 11th Symposium on Reliable Distributed Systems, Houston, Texas, 1992. IEEE Computer Society Press. [18] 3rd Joint European Networking Conference, Innsbruck, Austria, May 1992. [19] Fourth ACM Conference on Hypertext, Milano, Italy, November 1992. ACM Press. [20] GLOBECOM'92 Conference, Orlando, Florida, December 1992. IEEE Computer Society Press. http://github.com/dret/biblio (August 29, 2018) 1 dretbiblio [21] IEEE INFOCOM '92 Conference on Computer Communications, Florence, Italy, 1992. -

The Next Big OS War Is in Your Dashboard
12/4/12 The Next Big OS War Is in Your Dashboard | Autopia | Wired.com Autopia Planes, Trains, Automobiles and the Future of Transportation Infotainment LTikwe ee1t54 297 25 Sharre 39 The Next Big OS War Is in Your Dashboard By Doug Newcomb 12.03.12 6:30 AM Follow @dougnew comb Photo: Jim Merithew/Wired Competition in automotive technology has long been about who’s got the most horsepower, the best towing capacity or the fastest acceleration. These days, though, it’s all about having the slickest infotainment systems and most-connected cars. The shift in focus from what’s under the hood to what’s behind the dashboard has brought a largely covert war to the auto industry over the operating systems that will control these gadgets. As in the smartphone biz, the battle line is between proprietary and open source software. The outcome will determine what these systems look like, how they work and how distinctive they are as automakers embrace walled gardens or open ecosystems. It would be difficult to overstate the importance of getting this right. The amount of software in the average vehicle has grown exponentially — a typical new car has about 100 million lines of code — with the advent of sophisticated, cloud-connected infotainment systems. Software has become a competitive advantage as vital to General Motors or Toyota as it is to Apple or Google. The trouble is, automotive development cycles are measured in years, while the consumer www.wired.com/autopia/2012/12/automotiv e-os-war/all/ 1/11 The Next Big OS War Is in Your Dashboard | Autopia | Wired.com electronics industry works in months. -

Eclipse IP Management Modernization Sharon Corbett MODERNIZATION
Eclipse IP Management Modernization Sharon Corbett MODERNIZATION ● Eclipse IP - About ● Issue Statement WELCOME ● Objectives/Benefits ● License Compliance ● Self Service ● New Process Overview ● Futures ● Best Practices ● OSCM ● Wrap Up Eclipse Intellectual Property Management > Eclipse IP Policy (Board Approved) ○ Defines mechanism for accepting and licensing the intellectual property developed and leveraged by Eclipse projects > Legal Agreements ○ Formal - ECA, Committer Agreements, Working Group Participation Agreements > Due Diligence Review Process ○ Provenance, License Compatibility, Scanning for Anomalies ○ IP Ticket (CQ) > Commercial Adoption (Confidence/Safe) > High Bar, Rigorous, Well Respected COPYRIGHT (C) 2019, ECLIPSE FOUNDATION, INC. | MADE AVAILABLE UNDER THE ECLIPSE PUBLIC LICENSE 2.0 (EPL-2.0) What’s at Issue? > Eclipse IP Policy and Procedures (2004) > Significant changes over time > Cannot support agile development nor continuous delivery > Impossible to scale to modern day technology (Node.JS, Electron, NPM, etc.) > Burdensome - Lack of Automation COPYRIGHT (C) 2019, ECLIPSE FOUNDATION, INC. | MADE AVAILABLE UNDER THE ECLIPSE PUBLIC LICENSE 2.0 (EPL-2.0) The Time has Arrived ... > Bring Eclipse IP Policy and Process in line with contemporary expectations! COPYRIGHT (C) 2019, ECLIPSE FOUNDATION, INC. | MADE AVAILABLE UNDER THE ECLIPSE PUBLIC LICENSE 2.0 (EPL-2.0) Eclipse IP Governance Approach (Redefined) > Revise the IP Review requirements for third party content > Update IP Policy ○ Change due diligence approach for -

Linux Automotive Security “Safer and More Secure”
Linux Automotive Security “Safer and more secure” Authors Fulup Ar Foll [email protected] José Bollo [email protected] Abstract Cars are expensive pieces of equipment, yet they represent a huge mass market. Adding Internet connectivity to previous elements generates perfect conditions for the growth of a viable business model on attacking “Connected Cars”. It is already well understood that cars will be connected and connected cars will be attacked. While it's still too early to predict with certainty how “Connected Cars” will be impacted by security flaws, making the assumption that a car should be at least as secure as a TV, a set-top-box or a smart phone should make sense to everyone. This white paper focuses on how Linux best practices security mechanisms that could be used today and within the next couple of years to make connected cars safer and more secure. Version 1.0 January 2016 Linux Automotive Security Table of contents 1.Introduction...................................................................................................3 2.Make Sure You Run the Right Code...................................................................4 2.1.Before Booting............................................................................................4 2.2.When Booting.............................................................................................5 2.3.After Booting...............................................................................................5 3.Keeping Secrets Secret...................................................................................6