Teamviewer Security Statement
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Bedienungsanleitung Doro 8050
Doro 8050 Deutsch 1 8 13 2 14 3 9 15 10 4 10 16 5 6 11 7 12 Diese Anleitung dient lediglich als Referenz. Das Gerät, einschließlich, jedoch nicht be- schränkt auf Farbe, Größe und Bildschirmlay- out, sowie das mitgelieferte Zubehör können variieren. Dies ist davon abhängig, welche Software und welches Zubehör in Ihrer Region erhältlich ist bzw. von Ihrem Netzbetreiber an- geboten wird. Bei Ihrem örtlichen Doro-Händ- ler können Sie weiteres Zubehör erhalten. Das mitgelieferte Zubehör bietet die beste Lei- stung für Ihr Telefon. 17 Hinweis! Alle Abbildungen dienen lediglich zu anschaulichen Zwecken und geben das Aussehen des Geräts möglicherweise nicht genau wieder. Übersicht 1. Headset-Anschluss, für Stan- 11. USB Typ C, zum Aufladen des dard-Headsets mit 3,5-mm- Akkus oder zum Anschluss an Telefonbuchse andere Geräte, z. B. einen 2. Ohrstück, für Telefonanrufe Computer mit dem Telefon am Ohr 12. Lautsprecher, für den 3. SIM-/SD-Kartenfach Freisprechmodus 4. Lautstärkeregler 13. Zweites Mikrofon 5. Touchdisplay (berührungs- 14. Rückseitenkamera empfindlicher Bildschirm) 15. Blitzlicht/Taschenlampe 6. Home-Taste 16. Notruftaste, muss vor Ver- 7. Mikrofon wendung eingerichtet wer- den. Weitere Informationen Frontkamera 8. , Selfie-Kamera sind im vollständigen Benut- 9. Näherungssensor, schaltet zerhandbuch zu finden das Touchdisplay aus, wenn 17. Ladestation (optionales das Telefon am Ohr gehalten Zubehör) wird 10. Ein-/Aus-Taste, zum Ein- und Ausschalten des Telefons drücken und gedrückt halten Deutsch Inhalt Einrichtung des Doro 8050 ........................................................................... -

Retirement Strategy Fund 2060 Description Plan 3S DCP & JRA
Retirement Strategy Fund 2060 June 30, 2020 Note: Numbers may not always add up due to rounding. % Invested For Each Plan Description Plan 3s DCP & JRA ACTIVIA PROPERTIES INC REIT 0.0137% 0.0137% AEON REIT INVESTMENT CORP REIT 0.0195% 0.0195% ALEXANDER + BALDWIN INC REIT 0.0118% 0.0118% ALEXANDRIA REAL ESTATE EQUIT REIT USD.01 0.0585% 0.0585% ALLIANCEBERNSTEIN GOVT STIF SSC FUND 64BA AGIS 587 0.0329% 0.0329% ALLIED PROPERTIES REAL ESTAT REIT 0.0219% 0.0219% AMERICAN CAMPUS COMMUNITIES REIT USD.01 0.0277% 0.0277% AMERICAN HOMES 4 RENT A REIT USD.01 0.0396% 0.0396% AMERICOLD REALTY TRUST REIT USD.01 0.0427% 0.0427% ARMADA HOFFLER PROPERTIES IN REIT USD.01 0.0124% 0.0124% AROUNDTOWN SA COMMON STOCK EUR.01 0.0248% 0.0248% ASSURA PLC REIT GBP.1 0.0319% 0.0319% AUSTRALIAN DOLLAR 0.0061% 0.0061% AZRIELI GROUP LTD COMMON STOCK ILS.1 0.0101% 0.0101% BLUEROCK RESIDENTIAL GROWTH REIT USD.01 0.0102% 0.0102% BOSTON PROPERTIES INC REIT USD.01 0.0580% 0.0580% BRAZILIAN REAL 0.0000% 0.0000% BRIXMOR PROPERTY GROUP INC REIT USD.01 0.0418% 0.0418% CA IMMOBILIEN ANLAGEN AG COMMON STOCK 0.0191% 0.0191% CAMDEN PROPERTY TRUST REIT USD.01 0.0394% 0.0394% CANADIAN DOLLAR 0.0005% 0.0005% CAPITALAND COMMERCIAL TRUST REIT 0.0228% 0.0228% CIFI HOLDINGS GROUP CO LTD COMMON STOCK HKD.1 0.0105% 0.0105% CITY DEVELOPMENTS LTD COMMON STOCK 0.0129% 0.0129% CK ASSET HOLDINGS LTD COMMON STOCK HKD1.0 0.0378% 0.0378% COMFORIA RESIDENTIAL REIT IN REIT 0.0328% 0.0328% COUSINS PROPERTIES INC REIT USD1.0 0.0403% 0.0403% CUBESMART REIT USD.01 0.0359% 0.0359% DAIWA OFFICE INVESTMENT -

Annual Financial Statements of Teamviewer Ag Fiscal Year 2020 2 3 15 74 16 61 17 75 51 28 65 29 39 60 60 63 64 40 48
ANNUAL FINANCIAL STATEMENTS OF TEAMVIEWER AG FISCAL YEAR 2020 01_COMBINED MANAGEMENT REPORT 01 Group fundamentals ............................................................................................................... 3 02 Employees .............................................................................................................................. 15 03 Corporate responsibility ...................................................................................................... 16 04 Economic report ................................................................................................................... 17 05 Events after the reporting period ....................................................................................... 28 06 Opportunity and risk report .................................................................................................29 07 Outlook ...................................................................................................................................39 08 Remuneration report ............................................................................................................40 09 Takeover-related disclosures ...............................................................................................48 10 Corporate governance statement ........................................................................................ 51 11 Nonfinancial statement ........................................................................................................60 -

FACTSHEET - AS of 28-Sep-2021 Solactive Mittelstand & Midcap Deutschland Index (TRN)
FACTSHEET - AS OF 28-Sep-2021 Solactive Mittelstand & MidCap Deutschland Index (TRN) DESCRIPTION The Index reflects the net total return performance of 70 medium/smaller capitalisation companies incorporated in Germany. Weights are based on free float market capitalisation and are increased if significant holdings in a company can be attributed to currentmgmtor company founders. HISTORICAL PERFORMANCE 350 300 250 200 150 100 50 Jan-2010 Jan-2012 Jan-2014 Jan-2016 Jan-2018 Jan-2020 Jan-2022 Solactive Mittelstand & MidCap Deutschland Index (TRN) CHARACTERISTICS ISIN / WKN DE000SLA1MN9 / SLA1MN Base Value / Base Date 100 Points / 19.09.2008 Bloomberg / Reuters MTTLSTRN Index / .MTTLSTRN Last Price 342.52 Index Calculator Solactive AG Dividends Included (Performance Index) Index Type Equity Calculation 08:00am to 06:00pm (CET), every 15 seconds Index Currency EUR History Available daily back to 19.09.2008 Index Members 70 FACTSHEET - AS OF 28-Sep-2021 Solactive Mittelstand & MidCap Deutschland Index (TRN) STATISTICS 30D 90D 180D 360D YTD Since Inception Performance -3.69% 3.12% 7.26% 27.72% 12.73% 242.52% Performance (p.a.) - - - - - 9.91% Volatility (p.a.) 13.05% 12.12% 12.48% 13.60% 12.90% 21.43% High 357.49 357.49 357.49 357.49 357.49 357.49 Low 342.52 329.86 315.93 251.01 305.77 52.12 Sharpe Ratio -2.77 1.14 1.27 2.11 1.40 0.49 Max. Drawdown -4.19% -4.19% -4.19% -9.62% -5.56% -47.88% VaR 95 \ 99 -21.5% \ -35.8% -34.5% \ -64.0% CVaR 95 \ 99 -31.5% \ -46.8% -53.5% \ -89.0% COMPOSITION BY CURRENCIES COMPOSITION BY COUNTRIES EUR 100.0% DE -

Preliminary Q4/FY 2020 Results Webcast
TeamViewer – Preliminary Q4 and FY 2020 Results Call and Webcast TeamViewer AG Transcript – Preliminary Q4/FY 2020 Results Webcast 09 February 2021 TeamViewer – Preliminary Q4 and FY 2020 Results Call and Webcast Carsten Keller: Thank you. Good morning ladies and gentlemen, and welcome to our preliminary TeamViewer Q4 and full year 2020 results call. I’m here with Oliver Steil, CEO of TeamViewer, and Stefan Gaiser, our CFO, who will take you through our presentation with some business updates and then details on our Q4 and full year 2020 financials. Following the presentation, we will open the floor for your questions. However, before we start, I would like to remind you of the note on forward-looking statements that you can find on page two of the presentation. Let me now head over to Oliver. Oliver Steil: Thank you, Carsten. Good morning to all of you. Hope you’re all well. Thanks for joining our results call. So it’s a pleasure to discuss Q4 and financial year 2020 outcome, actually very pleased with the year, as you could see from the numbers. I think we were very happy to see that Q4 was a continuing normalization of the business after the corona pandemic effect in the first half of the year. Second half of the year “much more normal” and also very successful in that sense in digitalization projects for enterprises. So very pleased with the numbers. Overall billings came out at €456.7 million, which is slightly higher than our outlook. That’s the organic billings total including the Ubimax acquisition for the last four months was €460.3 million. -

See Through the Eyes of Others
See Through the Eyes of Others TeamViewer Assist AR is a remote support solution that provides easy, fast, and secure augmented reality-powered visual assistance to identify and solve problems from anywhere in the world. Solve problems faster Reduce costs Enable your service technicians and customers Lower travel costs by replacing on-site visits with to get direct support from experts via audio and remote expert help for service technicians and interactive video. customers. Maintain security Increase productivity Benefit from our worldwide infrastructure and Transfer knowledge for technical repairs and industry-leading, end-to-end, secure connections. maintenance or provide approval for inspections from a central location instead of an on-site visit. KEY FUNCTIONALITIES Remote camera sharing Send/Receive Files See your client’s or employee’s problem Send a file to your remote user through Pilot remotely through their smartphone and help with just the click of a button. address it. HD VoIP Optical Character Recognition Speak to the technician or client onsite, Recognize printed characters often found giving them detailed instructions on how to on machines, tools or equipment and send fix the issue them directly through Pilot avoiding errors. Highlighting on 3D objects Session Recording Help the on-site employee or customer fix Record a Pilot session from the expert´s side the issue by drawing and highlighting on the and create a video file ready for use on any screen onto real-world objects.. computer instantly. Freeze Image Real-time Information Sharing Pause the video stream to get a clear still Precisely select the area of your desktop image to highlight and discuss technical de- screen to share on your partner’s smart- tails, as well as work hands-free. -

Euro Stoxx® International Exposure Index
EURO STOXX® INTERNATIONAL EXPOSURE INDEX Components1 Company Supersector Country Weight (%) ASML HLDG Technology Netherlands 6.02 LVMH MOET HENNESSY Consumer Products & Services France 4.99 LINDE Chemicals Germany 3.79 SAP Technology Germany 3.62 SANOFI Health Care France 3.20 IBERDROLA Utilities Spain 3.04 SIEMENS Industrial Goods & Services Germany 2.63 AIR LIQUIDE Chemicals France 2.17 SCHNEIDER ELECTRIC Industrial Goods & Services France 2.10 L'OREAL Consumer Products & Services France 2.05 ANHEUSER-BUSCH INBEV Food, Beverage & Tobacco Belgium 1.99 BASF Chemicals Germany 1.89 ADIDAS Consumer Products & Services Germany 1.76 AIRBUS Industrial Goods & Services France 1.68 DAIMLER Automobiles & Parts Germany 1.65 BAYER Health Care Germany 1.61 PHILIPS Health Care Netherlands 1.51 ADYEN Industrial Goods & Services Netherlands 1.49 ESSILORLUXOTTICA Health Care France 1.40 DEUTSCHE TELEKOM Telecommunications Germany 1.36 INFINEON TECHNOLOGIES Technology Germany 1.35 Kering Retail France 1.35 BCO SANTANDER Banks Spain 1.29 SAFRAN Industrial Goods & Services France 1.26 HERMES INTERNATIONAL Consumer Products & Services France 1.10 PERNOD RICARD Food, Beverage & Tobacco France 1.09 CRH Construction & Materials Ireland 1.09 DEUTSCHE POST Industrial Goods & Services Germany 1.05 BCO BILBAO VIZCAYA ARGENTARIA Banks Spain 1.03 FLUTTER ENTERTAINMENT Travel & Leisure Ireland 1.02 DANONE Food, Beverage & Tobacco France 1.00 MUENCHENER RUECK Insurance Germany 0.99 VOLKSWAGEN PREF Automobiles & Parts Germany 0.82 BMW Automobiles & Parts Germany 0.80 -

Euronext Eurozone 300 Factsheet
EZ300 Factsheet 1/8 Euronext ® Eurozone 300 Objective The Euronext ® Eurozone 300 tracks the performance of a portfolio of 300 stocks in Eurozone, ranked by their free float market capitalization. Constituents are reviewed on a quarterly basis and their weights are reset based on their free float market capitalization at the quarterly rebalances. The index serves as an underlying for structured products, funds and exchange traded funds. Investability Stocks are screened to ensure liquidity to ensure that the index is investable. Transparency The index rules are available on our website. Euronext acts as Supervisor. All our rulebooks can be found on the following webpage: https://live.euronext.com/en/products-indices/index-rules. Statistics Mar-21 Market Capitalization EUR Bil Performance (%) Fundamentals Full 6 850,95 Q1 2021 8,55% P/E Incl. Neg LTM 54,18 Free float 5 085,53 YTD 8,55% P/E Incl. Neg FY1 15,18 2020 -2,72% P/E excl. Neg LTM 59,43 2019 22,32% P/E excl. Neg FY1 23,90 Components (full) EUR Bil 2018 -14,12% Price/Book 4,11 Average 22,86 Price/Sales 4,06 Median 11,32 Annualized (%) Price/Cash Flow 9,05 Largest 286,75 2 Year 7,64% Dividend Yield (%) 2,22 Smallest 1,89 3 Years 4,56% 5 Years 5,89% Risk Component Weights (%) Since Base Date 31-Dec-2005 1,87% Sharpe Ratio 1 Year not calc. Largest 4,27 Volatility 30 Day 11,48 Smallest 0,03 Top ten 23,88 Performance of other versions EZ3NR EZ3GR WLENV Euronext Eurozone 300 NR Euronext Eurozone 300 GR (%) (%) Q1 2021 8,81% Q1 2021 8,89% YTD 8,81% YTD 8,89% 2020 -0,84% 2020 -0,24% 2019 25,51% 2019 26,57% 2018 -12,04% 2018 -11,37% This publication is for information purposes only and is not a recommendation to engage in investment activities. -
Teamviewer Remote Control Window
TeamViewer 13 Manual Remote Control Rev 13.1-201802 TeamViewer GmbH • Jahnstraße 30 D-73037 Göppingen www.teamviewer.com Table of contents 1 About TeamViewer 5 1.1 About the software 5 1.2 About the manual 5 2 Basics 7 2.1 How TeamViewer works 7 2.2 Description of the main TeamViewer window 7 3 Establishing a connection with TeamViewer 12 4 The Remote Control connection mode 13 4.1 Remote Control window options 13 4.2 Remote computer options in the TeamViewer Panel 24 5 The File Transfer connection mode 26 5.1 Options in File Transfer connection mode 26 5.2 Transferring files using drag and drop 29 5.3 File transfer via the Windows context menu 29 6 The VPN connection mode 31 6.1 Sample uses of TeamViewer VPN 31 6.2 Requirements for using TeamViewer VPN 31 6.3 VPN dialog box options 32 TeamViewer 13 Manual – Remote Control www.teamviewer.com Page 2 of 127 7 Other connection options 33 7.1 Establishing a LAN connection using the IP address 33 7.2 Authenticating on the Remote Computer using a Windows user account 34 7.3 Establish a connection via a Windows shortcut 35 7.4 Connections to your own computers without password. 36 8 Computers & Contacts – Managing Contacts 39 8.1 The TeamViewer account 41 8.2 Computers & Contacts options 45 8.3 Service cases 62 8.4 Integrated system health checks 65 9 Multimedia functions 68 9.1 Options within the Session list 68 9.2 Transmitting webcam video to your partner 68 9.3 Talk to your partner via Voice over IP or conference call 69 9.4 Chatting with your partner during a TeamViewer session 71 9.5 Sharing -

Teamviewer AG Transcript – Q4/FY 2020 Results Webcast
TeamViewer – Q4 and FY 2020 Results Call and Webcast TeamViewer AG Transcript – Q4/FY 2020 Results Webcast 09 February 2021 TeamViewer – Q4 and FY 2020 Results Call and Webcast Carsten Keller: Thank you. Good morning ladies and gentlemen, and welcome to our TeamViewer Q4 and full year 2020 results call. I’m here with Oliver Steil, CEO of TeamViewer, and Stefan Gaiser, our CFO, who will take you through our presentation with some business updates and then details on our Q4 and full year 2020 financials. Following the presentation, we will open the floor for your questions. However, before we start, I would like to remind you of the note on forward-looking statements that you can find on page two of the presentation. Let me now head over to Oliver. Oliver Steil: Thank you, Carsten. Good morning to all of you. Hope you’re all well. Thanks for joining our results call. So it’s a pleasure to discuss Q4 and financial year 2020 outcome, actually very pleased with the year, as you could see from the numbers. I think we were very happy to see that Q4 was a continuing normalization of the business after the corona pandemic effect in the first half of the year. Second half of the year “much more normal” and also very successful in that sense in digitalization projects for enterprises. So very pleased with the numbers. Overall billings came out at €456.7 million, which is slightly higher than our outlook. That’s the organic billings total including the Ubimax acquisition for the last four months was €460.3 million. -

1 Bekanntmachung in Bezug Auf Die Folgenden Long Bzw. Short Mini Future Turbo Optionsscheine Der Goldman, Sachs & Co. Wertpa
Bekanntmachung in Bezug auf die folgenden Long bzw. Short Mini Future Turbo Optionsscheine der Goldman, Sachs & Co. Wertpapier GmbH Hinsichtlich der unten genannten Long bzw. Short Mini Future Turbo Optionsscheine ist gemäß der Optionsscheinbedingungen ein Knock-Out Ereignis eingetreten, da die jeweilige Knock-Out Barriere erreicht oder unterschritten (bei Long Optionsscheinen) bzw. erreicht oder überschritten (bei Short Optionsscheinen) wurde. Die betroffenen Optionsscheine werden wie folgt abgerechnet: Datum des Knock-Out WKN Basiswert Optionstyp Knock-Out Barriere Knock-Out Auszahlungsbetrag je Ereignisses Optionsschein in EUR GH7CCL 1 Feinunze Gold, Feinheit mind. 0,995, LBMA Short USD 1.886 7. Juni 2021 3,18 GH7CCT 1 Feinunze Gold, Feinheit mind. 0,995, LBMA Short USD 1.891 7. Juni 2021 3,15 GH7CCW 1 Feinunze Silber, Feinheit mind. 0,999 Short USD 27,7 7. Juni 2021 0,73 GH7CCM 1 Feinunze Silber, Feinheit mind. 0,999 Short USD 27,6 7. Juni 2021 0,69 GH7CE9 1 Feinunze Platin, Feinheit mind. 0,9995 Short USD 1.168,7 7. Juni 2021 0,51 GH6ZZV TeamViewer AG Short EUR 31,14 7. Juni 2021 0,16 GH7CCR 1 Feinunze Gold, Feinheit mind. 0,995, LBMA Short USD 1.882 7. Juni 2021 3,12 GH7CCJ 1 Feinunze Silber, Feinheit mind. 0,999 Short USD 27,8 7. Juni 2021 0,7 GH7CDL 1 Feinunze Silber, Feinheit mind. 0,999 Short USD 27,7 7. Juni 2021 0,67 ICE Brent Crude Oil Future (Generic Front Month GH2U62 Short USD 72,2 7. Juni 2021 1,87 Future) GH7CB9 AIXTRON SE Short EUR 17,06 7. -
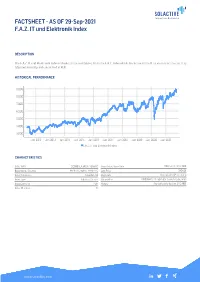
FACTSHEET - AS of 29-Sep-2021 F.A.Z
FACTSHEET - AS OF 29-Sep-2021 F.A.Z. IT und Elektronik Index DESCRIPTION The F.A.Z. IT und Elektronik Index includes those companies from the F.A.Z. Index which are active in the IT or electronics sector. It is adjusted annually and calculated in EUR. HISTORICAL PERFORMANCE 9,000 8,000 7,000 6,000 5,000 4,000 3,000 Jan-2012 Jan-2013 Jan-2014 Jan-2015 Jan-2016 Jan-2017 Jan-2018 Jan-2019 Jan-2020 Jan-2021 F.A.Z. IT und Elektronik Index CHARACTERISTICS ISIN / WKN DE000SLA3AC3 / SLA3AC Base Value / Base Date 100 Points / 31.12.1961 Bloomberg / Reuters FAZIELEC Index / .FAZIELEC Last Price 8484.51 Index Calculator Solactive AG Dividends Not included (Price index) Index Type Industry / Sector Calculation 09:00am to 17:45pm (CET), every 15 seconds Index Currency EUR History Available daily back to 31.12.1961 Index Members 11 FACTSHEET - AS OF 29-Sep-2021 F.A.Z. IT und Elektronik Index STATISTICS 30D 90D 180D 360D YTD Since Inception Performance -3.86% 3.17% 4.42% 9.24% 12.58% 123.08% Performance (p.a.) - - - - - 8.06% Volatility (p.a.) 23.15% 18.59% 18.42% 22.20% 17.82% 20.92% High 8999.43 8999.43 8999.43 8999.43 8999.43 8999.43 Low 8484.51 8078.47 7882.77 6363.28 7490.55 2869.49 Sharpe Ratio -1.62 0.76 0.53 0.44 0.99 0.41 Max. Drawdown -5.72% -5.72% -7.27% -21.00% -7.27% -38.98% VaR 95 \ 99 -31.1% \ -61.2% -33.7% \ -57.4% CVaR 95 \ 99 -59.0% \ -136.1% -51.4% \ -85.4% COMPOSITION BY CURRENCIES COMPOSITION BY COUNTRIES EUR 100.0% DE 100.0% TOP COMPONENTS AS OF 29-Sep-2021 Company Ticker Country Currency Index Weight (%) SAP SE SAP GY Equity DE EUR 38.47% SIEMENS AG SIE GY Equity DE EUR 32.41% INFINEON TECHNOLOGIES AG IFX GY Equity DE EUR 12.23% SIEMENS ENERGY AG ENR GY Equity DE EUR 4.56% CARL ZEISS MEDITEC AG AFX GY Equity DE EUR 3.98% NEMETSCHEK SE NEM GY Equity DE EUR 2.73% BECHTLE AG BC8 GY Equity DE EUR 1.99% TEAMVIEWER AG TMV GY Equity DE EUR 1.38% COMPUGROUP MEDICAL SE & CO KGA COP GY Equity DE EUR 1.01% SOFTWARE AG SOW GY Equity DE EUR 0.79% FACTSHEET - AS OF 29-Sep-2021 F.A.Z.