Configuring TCP/IP
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Empirical Analysis of the Effects and the Mitigation of Ipv4 Address Exhaustion
TECHNISCHE UNIVERSITÄT BERLIN FAKULTÄT FÜR ELEKTROTECHNIK UND INFORMATIK LEHRSTUHL FÜR INTELLIGENTE NETZE UND MANAGEMENT VERTEILTER SYSTEME Empirical Analysis of the Effects and the Mitigation of IPv4 Address Exhaustion vorgelegt von M.Sc. Philipp Richter geboren in Berlin von der Fakultät IV – Elektrotechnik und Informatik der Technischen Universität Berlin zur Erlangung des akademischen Grades DOKTOR DER NATURWISSENSCHAFTEN -DR. RER. NAT.- genehmigte Dissertation Promotionsausschuss: Vorsitzender: Prof. Dr.-Ing. Sebastian Möller, Technische Universität Berlin Gutachterin: Prof. Anja Feldmann, Ph.D., Technische Universität Berlin Gutachter: Prof. Vern Paxson, Ph.D., University of California, Berkeley Gutachter: Prof. Steve Uhlig, Ph.D., Queen Mary University of London Tag der wissenschaftlichen Aussprache: 2. August 2017 Berlin 2017 Abstract IP addresses are essential resources for communication over the Internet. In IP version 4, an address is represented by 32 bits in the IPv4 header; hence there is a finite pool of roughly 4B addresses available. The Internet now faces a fundamental resource scarcity problem: The exhaustion of the available IPv4 address space. In 2011, the Internet Assigned Numbers Authority (IANA) depleted its pool of available IPv4 addresses. IPv4 scarcity is now reality. In the subsequent years, IPv4 address scarcity has started to put substantial economic pressure on the networks that form the Internet. The pools of available IPv4 addresses are mostly depleted and today network operators have to find new ways to satisfy their ongoing demand for IPv4 addresses. Mitigating IPv4 scarcity is not optional, but mandatory: Networks facing address shortage have to take action in order to be able to accommodate additional subscribers and customers. Thus, if not confronted, IPv4 scarcity has the potential to hinder further growth of the Internet. -

74 Network Addressin
CSC414 Communication Models Computer Network Client/Server Model System - Server Program Fundamentals Addressing - Runs on computer that has files to be shared - Web Server, Mail Server, Warcraft Server Server Client - Client Program Apache Firefox - Computer that needs to access remote files - Web Browser, Mail Client, World of Warcraft Digital Forensics Center Department of Computer Science and Statics THINK BIG WE DO Peer to Peer Model - Single program U R I - makes files on computer available Peer Peer http://www.forensics.cs.uri.edu - accesses remote files LimeWire LimeWire Addressing Data Domain Names http://www.uri.edu:80/courses/cs/index.html Hierarchical system for name creation and registration protocol computer directory file - Created so users would not have to memorize IP addresses address port - Global domain name system provides global scope for user friendly addresses OSI Model Domain Name Application Layer Country Codes Country Domain Type Common .us United States .biz Business File requested by client Presentation Layer Top Level .uk United Kingdom .com Commercial .au Australia .edu US Educational Folder or directory path on server Session Layer Maps to special directory used by Port Domains .cn China .gov US Government application .mil Military Transport Layer .ca Canada Mailbox on the machine the .de Germany .net Network server or peer is checking Top level Network Layer .org Nonprofit Organization IP Address (Logical) domains are .ru Russia What machine has the shared data .info Info Domain approved by .in India Where -
AX1800 Wifi 6 Router Model RAX15
User Manual AX1800 WiFi 6 Router Model RAX15 NETGEAR, Inc. August 2021 350 E. Plumeria Drive 202-12029-02 San Jose, CA 95134, USA AX1800 WiFi 6 Router Support and Community Visit netgear.com/support to get your questions answered and access the latest downloads. You can also check out our NETGEAR Community for helpful advice at community.netgear.com. Regulatory and Legal Si ce produit est vendu au Canada, vous pouvez accéder à ce document en français canadien à https://www.netgear.com/support/download/. (If this product is sold in Canada, you can access this document in Canadian French at https://www.netgear.com/support/download/.) For regulatory compliance information including the EU Declaration of Conformity, visit https://www.netgear.com/about/regulatory/. See the regulatory compliance document before connecting the power supply. For NETGEAR’s Privacy Policy, visit https://www.netgear.com/about/privacy-policy. By using this device, you are agreeing to NETGEAR’s Terms and Conditions at https://www.netgear.com/about/terms-and-conditions. If you do not agree, return the device to your place of purchase within your return period. Trademarks ©NETGEAR, Inc. NETGEAR and the NETGEAR Logo are trademarks of NETGEAR, Inc. Any non-NETGEAR trademarks are used for reference purposes only. 2 Contents Chapter 1 Hardware Setup Unpack your router...............................................................................9 Front panel LEDs and buttons..........................................................10 Rear panel and side panel.................................................................12 -

Unicast Multicast IP Multicast Introduction
Outline 11: ❒ IP Multicast ❒ Multicast routing IP Multicast ❍ Design choices ❍ Distance Vector Multicast Routing Protocol (DVMRP) Last Modified: ❍ Core Based Trees (CBT) ❍ Protocol Independent Multicast (PIM) 4/9/2003 1:15:00 PM ❍ Border Gateway Multicast Protocol (BGMP) ❒ Issues in IP Multicast Deplyment Based on slides by Gordon Chaffee Berkeley Multimedia Research Center URL: http://bmrc.berkeley.edu/people/chaffee 4: Network Layer 4a-1 4: Network Layer 4a-2 What is multicast? Unicast ❒ ❒ 1 to N communication Problem Sender ❍ ❒ Nandwidth-conserving technology that Sending same data to reduces traffic by simultaneously many receivers via unicast is inefficient delivering a single stream of information to R multiple recipients ❒ Example ❒ Examples of Multicast ❍ Popular WWW sites ❍ Network hardware efficiently supports become serious multicast transport bottlenecks • Example: Ethernet allows one packet to be received by many hosts ❍ Many different protocols and service models • Examples: IETF IP Multicast, ATM Multipoint 4: Network Layer 4a-3 4: Network Layer 4a-4 Multicast IP Multicast Introduction ❒ Efficient one to many Sender ❒ Efficient one to many data distribution data distribution ❍ Tree style data distribution ❍ Packets traverse network links only once R ❒ Location independent addressing ❍ IP address per multicast group ❒ Receiver oriented service model ❍ Applications can join and leave multicast groups ❍ Senders do not know who is listening ❍ Similar to television model ❍ Contrasts with telephone network, ATM 4: Network Layer -

Understand Ipv4
LESSON 3.2 98-366 Networking Fundamentals UnderstandUnderstand IPv4IPv4 LESSON 3.2 98-366 Networking Fundamentals Lesson Overview In this lesson, you will learn about: APIPA addressing classful IP addressing and classless IP addressing gateway IPv4 local loopback IP NAT network classes reserved address ranges for local use subnetting static IP LESSON 3.2 98-366 Networking Fundamentals Anticipatory Set 1. Write the address range and broadcast address for the following subnet: Subnet: 192.168.1.128 / 255.255.255.224 Address Range? Subnet Broadcast Address? 2. Check your answer with those provided by the instructor. If it is different, review the method of how you derived the answer with your group and correct your understanding. LESSON 3.2 98-366 Networking Fundamentals IPv4 A connectionless protocol for use on packet-switched Link Layer networks like the Ethernet At the core of standards-based internetworking methods of the Internet Network addressing architecture redesign is underway via classful network design, Classless Inter-Domain Routing, and network address translation (NAT) . Microsoft Windows uses TCP/IP for IP version 4 (a networking protocol suite) to communicate over the Internet with other computers. It interacts with Windows naming services like WINS and security technologies. IPsec helps facilitate the successful and secure transfer of IP packets between computers. An IPv4 address shortage has been developing. LESSON 3.2 98-366 Networking Fundamentals Network Classes Provide a method for interacting with the network All networks have different sizes so IP address space is divided in different classes to meet different requirements. Each class fixes a boundary between the network prefix and the host within the 32-bit address. -

System Administration Guide: IP Services
System Administration Guide: IP Services Sun Microsystems, Inc. 4150 Network Circle Santa Clara, CA 95054 U.S.A. Part No: 816–4554–10 January 2005 Copyright 2005 Sun Microsystems, Inc. 4150 Network Circle, Santa Clara, CA 95054 U.S.A. All rights reserved. This product or document is protected by copyright and distributed under licenses restricting its use, copying, distribution, and decompilation. No part of this product or document may be reproduced in any form by any means without prior written authorization of Sun and its licensors, if any. Third-party software, including font technology, is copyrighted and licensed from Sun suppliers. Parts of the product may be derived from Berkeley BSD systems, licensed from the University of California. UNIX is a registered trademark in the U.S. and other countries, exclusively licensed through X/Open Company, Ltd. Sun, Sun Microsystems, the Sun logo, docs.sun.com, AnswerBook, AnswerBook2, and Solaris are trademarks or registered trademarks of Sun Microsystems, Inc. in the U.S. and other countries. All SPARC trademarks are used under license and are trademarks or registered trademarks of SPARC International, Inc. in the U.S. and other countries. Products bearing SPARC trademarks are based upon an architecture developed by Sun Microsystems, Inc. The OPEN LOOK and Sun™ Graphical User Interface was developed by Sun Microsystems, Inc. for its users and licensees. Sun acknowledges the pioneering efforts of Xerox in researching and developing the concept of visual or graphical user interfaces for the computer industry. Sun holds a non-exclusive license from Xerox to the Xerox Graphical User Interface, which license also covers Sun’s licensees who implement OPEN LOOK GUIs and otherwise comply with Sun’s written license agreements. -

IP Addressing Design Issues and Protocols
IP Addressing Design Issues and Protocols CS2520/TELCOM2321 Wide Area Network Spring Term, 2019 Prof. Taieb Znati Department Computer Science Telecommunication Program Outline Internet Address Structure o Classfull Addresses o Classeless Addresses o Subnetting and Supernetting DHCP and ARP Network Address Translation IP Addressing IP Address Every device connected to the public Internet is assigned a unique IP address. o Typically addresses are assigned to internet service providers within region-based blocks, o IP address can often be used to identify the region or country from which a computer is connecting to the Internet. An IP address can sometimes be used to show the user's general location. IP addresses can be assigned by an ISP statically (Static IP Address) or dynamically (Dynamic IP Address) IP Address IPv4, defined by 4 bytes (32 bits) o IP address represents a network interface o Routers, for example, are typically assigned multiple IP addresses Address spaces o 0.0.0.0 ~ 255.255.255.255 o 232 = 4,294,967,296 hosts Classful IP Address Format Class P r i A 0 NetID HostID m a r y 10 NetID HostID C B l a s s 110 NetID HostID e C s D 1110 Multicast Address E 1111 Experimental Address 8 bits 8 bits 8 bits 8 bits Class A Networks Class B Networks Class C Networks IP Addresses IP Address dotted decimal notation o It divides the 32-bit IP address into 4 byte fields and specifies each byte independently as a decimal number with the fields separated by dots 10 010001 00001010 00100010 00000011 145 145 145 145 145.10.34.3 -

System Administration Guide IP Services
System Administration Guide: IP Services Part No: 816–4554–22 August 2011 Copyright © 1999, 2010, Oracle and/or its affiliates. All rights reserved. License Restrictions Warranty/Consequential Damages Disclaimer This software and related documentation are provided under a license agreement containing restrictions on use and disclosure and are protected by intellectual property laws. Except as expressly permitted in your license agreement or allowed by law, you may not use, copy, reproduce, translate, broadcast, modify, license, transmit, distribute, exhibit, perform, publish or display any part, in any form, or by any means. Reverse engineering, disassembly, or decompilation of this software, unless required by law for interoperability, is prohibited. Warranty Disclaimer The information contained herein is subject to change without notice and is not warranted to be error-free. If you find any errors, please report them to us in writing. Restricted Rights Notice If this is software or related documentation that is delivered to the U.S. Government or anyone licensing it on behalf of the U.S. Government, the following notice is applicable: U.S. GOVERNMENT RIGHTS Programs, software, databases, and related documentation and technical data delivered to U.S. Government customers are "commercial computer software" or "commercial technical data" pursuant to the applicable Federal Acquisition Regulation and agency-specific supplemental regulations. As such, the use, duplication, disclosure, modification, and adaptation shall be subject to the restrictions and license terms set forth in the applicable Government contract,and, to the extent applicable by the terms of the Government contract, the additional rights set forth in FAR 52.227-19, Commercial Computer Software License (December 2007). -
Mac OS X Server Network Services Administration for Version 10.4 Or Later
Mac OS X Server Network Services Administration For Version 10.4 or Later Apple Computer, Inc. © 2005 Apple Computer, Inc. All rights reserved. The owner or authorized user of a valid copy of Mac OS X Server software may reproduce this publication for the purpose of learning to use such software. No part of this publication may be reproduced or transmitted for commercial purposes, such as selling copies of this publication or for providing paid-for support services. Every effort has been made to ensure that the information in this manual is accurate. Apple computer, Inc., is not responsible for printing or clerical errors. Apple 1Infinite Loop Cupertino, CA 95014-2084 408-996-1010 www.apple.com Use of the “keyboard” Apple logo (Option-Shift-K) for commercial purposes without the prior written consent of Apple may constitute trademark infringement and unfair competition in violation of federal and state laws. Apple, the Apple logo, AirPort, AppleScript, AppleShare, AppleTalk, Mac, Mac OS, Macintosh, Power Mac, Power Macintosh, QuickTime, Sherlock, and WebObjects are trademarks of Apple Computer, Inc., registered in the U.S. and other countries. Java and all Java-based trademarks and logos are trademarks or registered trademarks of Sun Microsystems, Inc. in the U.S. and other countries. UNIX is a registered trademark in the United States and other countries, licensed exclusively through X/Open Company, Ltd. Other company and product names mentioned herein are trademarks of their respective companies. Mention of third-party products is for informational purposes only and constitutes neither an endorsement nor a recommendation. Apple assumes no responsibility with regard to the performance or use of these products. -

Understanding Ip Addressing
52-20-31 DATA COMMUNICATIONS MANAGEMENT UNDERSTANDING IP ADDRESSING Gilbert Held INSIDE The IP Addressing Scheme; Dotted Decimal Notation; Basic Workstation Configuration; Reserved Addresses; Subnetting; Multiple Interface Addresses; Address Resolution; ICMP OVERVIEW This article focuses on the mechanism that enables IP datagrams to be delivered to unique or predefined groups of hosts. That mechanism is the addressing method used by the Internet Protocol, commonly referred to as IP addressing. Under the current version of Internet Protocol, IPv4, 32-bit binary numbers are used to identify the source and destination address in each datagram. It was not until RFC 760 that the Internet Protocol as we know it was defined and the next IP-related RFC — RFC 791 that obsoleted RFC 760 — included the concept of IP address classes. Another key IP-related addressing RFC is RFC 950, which introduced the concept of subnetting. Subnetting represents a method for conserving IP network addresses and is described and discussed in detail later in this article. Although one normally associates a host with a distinct IP address, in actuality IP addresses are used by the Internet Protocol to identify dis- tinct device interfaces. That is, each interface on a device has a unique PAYOFF IDEA IP address. This explains how a The Internet Protocol (IP) represents the network router with multiple interfaces can layer of the TCP/IP protocol suite. It was devel- receive communications addressed oped as a mechanism to interconnect packet- to the device on different router switched TCP/IP networks. Since the initial devel- ports connected to LANs and WANs. -
Network+ Guide to Networks, Eight Edition
3/9/2021 Network+ Guide to Networks Objectives (1 of 2) Objectives (2 of 2) Eighth Edition 3.1 Find the MAC address of a computer and explain its function 3.4 Describe domain names and the name resolution process in network communications Chapter 3 3.5 Use command-line tools to troubleshoot problems with 3.2 Configure TCP/IP settings on a computer, including IP address, network addresses Addressing on Networks subnet mask, default gateway, and DNS servers 3.3 Explain the purpose of ports and sockets, and identify the ports of several common, network protocols © 2019 Cengage. All Rights Reserved. May not be copied, scanned, or duplicated, in whole or in part, except for use as permitted in a license distributed with a certain product or service or otherwise on a password-protected website for © 2019 Cengage. All Rights Reserved. May not be copied, scanned, or duplicated, in whole or in part, except for use as permitted in a license © 2019 Cengage. All Rights Reserved. May not be copied, scanned, or duplicated, in whole or in part, except for use as permitted in a license classroom use. 1 distributed with a certain product or service or otherwise on a password-protected website for classroom use. distributed with a certain product or service or otherwise on a password-protected website for classroom use. 1 3/9/2021 Addressing Overview MAC Addresses IP Addresses (1 of 2) • Four addressing methods: • Traditional MAC addresses contain two parts: • Static IP addresses are assigned manually by the network administrator • Data Link layer MAC -
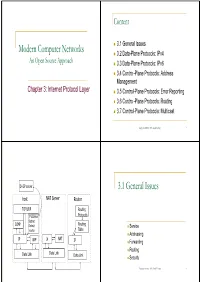
Modern Computer Networks 3.1 General Issues
Content 3.1 General Issues Modern Computer Networks 3.2 Data-Plane Protocols: IPv4 An Open Source Approach 3.3 Data-Plane Protocols: IPv6 34C3.4 Con tro l-Plane Prot ocol s: Add ress Management Chap ter 3It3: Interne t PtProtoco lLl Layer 3.5 Control-Plane Protocols: Error Reporting 3. 6 Control-Plane Protocols: Routing 3.7 Control-Plane Protocols: Multicast Copyright reserved 2001 (Lin & Hwang) 2 DHCP server 3.1 General Issues host NAT Server Router TCP/UDP Routing IP address Protocols Subnet ICMP Routing Default Service router Table Addressing IP ARP IP NAT IP Forwarding Routing Data Link Data Link Data Link Security Copyright reserved 2001 (Lin & Hwang) 4 Service Internetwork An example of an internetwork Provides a host-to-host transmission service Ethernet Fast Ethernet Connects several LANs into an internetwork a network of networks H1 H2 R1 R2 “Internet” GigabitEthernet the global internetwork to which most of networks R3 are connectdted H3 Wireless LAN Copyright reserved 2001 (Lin & Hwang) 5 Copyright reserved 2001 (Lin & Hwang) 6 Internet Service Model Address Connectionless A globally unique address for host Best effort delivery identification packets may be lost Data link layer: a flat address packets are delivered out of order dlitduplicate cop ies o f a pac ktket are dliddelivered Network layer: a hierarchical address packets can be delayed for a long time Next-hop forwarding based on destination address Copyright reserved 2001 (Lin & Hwang) 7 Copyright reserved 2001 (Lin & Hwang) 8 Deliver a packet