The Cider Press: Extracting Forensic Artifacts from Apple Continuity Heather Mahalik | @Heathermahalik | Smarterforensics.Com Sarah Edwards | @Iamevltwin | Mac4n6.Com
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
The Apple Mobile Special Interest Group Has Its Second Meeting on 30Th July, 2020
The Apple mobile special interest group has its second meeting on 30th July, 2020. Five members were there. We started off discussing the fixed agenda topics for this meeting Photography o Those with iOS 13 can open the photo app quickly by swiping left from the lock screen. Another quick way is to bring the control panel onto the screen (swipe down from above the top right of an iPad screen or up from the bottom of an iPhone screen) then select the camera icon. Alternatively, locate the camera icon on the screen. Having the camera icon in the ‘dock’ is also handy as it then appears on every screen. o The camera has the ability to alter its default settings for focus and lighting by touching the yellow square that appears when the camera first starts or if you touch the screen. Touching and holding the yellow square allows fine adjustments for light. Touching the screen where you want the camera to focus on, changes the automatic option. o Once the photo is taken, try editing the result by touching the photo then touching edit. Have a play with all of the options and see the effect it has. You can discard changes at any time or save them as separate photos. Try ‘marking up’ making pen marks on a picture using an array of pens and colours. o Security of your photos should be top of mind. The best option is to store them in in a cloud computing service such as Apple Photos or Google Photos. In the photos settings, turn on ‘iCloud Photos’ to automatically send your photos to your iCloud account. -

Introducing the Iwatch
May 2014 Jun June 2014 Welcome to Volume 5, Issue 6 of iDevices (iPhone, iPod & iPad) SIG Meetings Need Help? Go to the iDevice FORUM, click HERE To find Apps that are free for a short time, click these 2 icons: Introducing the iWatch Click to see the video New iPhone Lock screen bypass discovered Here's how to protect against it! By Rene Ritchie, Monday, Jun 9, 2014 16 A new iOS 7.1.1 iPhone Lock screen bypass has been discovered. Lock screen bypasses in and of themselves aren't new — trying to protect a phone while also allowing access to convenient features results is an incredible tension — but this one can provide access to an app, which makes it one of the most serious to date. It does require physical access to your iPhone, but if you do lose possession, here's how the bypass works and, more importantly, how you can protect yourself from it. Note: iMore tested the exploit and its scope before reporting on it. We were able to duplicate it but also get a sense of its ramifications and limitations. First, in order to get around the passcode lock, this bypass requires that the iPhone be placed into Airplane mode, and that a missed phone call notification be present. When those conditions are met, tapping or swiping the missed call notification will cause a Settings popup to appear on top of whatever app was last active (in the foreground) on the iPhone prior to it being locked. Dismiss the popup and you have access to the app. -

2002 Nl February 2
VOLUME 31, NUMBER 2 MAIN LINE MACINTOSH USERS GROUP FEBRUARY 2020 FOUNDED MAY 1989 MEETINGS - SECOND SOME WEBSITES SATURDAY OF THE MONTH The 10 Best Wireless Routers of 2019. A tough technical subject, but this article should help. bit.ly/30Op3v4. FOCUS - SOFTWARE & iPHONE What You Need to Know About 5G in 2020. It’s coming, but slowly - and there are 2 SELF-DRIVING CARS varieties. nyti.ms/2uwrgyW. Our main speaker will be me (Mark Bazrod). The topic will be self-driving cars. How to Use Your iPhone as a The presentation will answer a number of questions, such as - Why do we need Pedometer. No need to buy an self driving cars? What is a self driving car? What are the levels of self driving expensive fitness tracker when cars? What is their history? Who's working on self-driving cars? What about the iPhone tracks your steps for Tesla cars? What progress are auto makers making? How and where are self free. bit.ly/36lrhDn. driving cars being tested? What accidents have they been involved in? What are How to free up iCloud storage the technological obstacles to their widespread use? What are the other space. This article gives you obstacles? What are their advantages and disadvantages? And what are the tips to try to stay within the free ethical issues? 5GB given by Apple. However, Mark is currently MLMUG Secretary and has been Newsletter Editor since 2004. He also has been going to 50GB costs only $1 President and Treasurer and a Board member. He has many times been a presenter to both per month. -
Ios App Reverse Engineering
snakeninny, hangcom Translated by Ziqi Wu, 0xBBC, tianqing and Fei Cheng iOS App Reverse Engineering Table of Contents Recommendation ..................................................................................................................................................... 1 Preface ....................................................................................................................................................................... 2 Foreword ................................................................................................................................................................... 7 Part 1 Concepts ....................................................................................................................................................... 12 Chapter 1 Introduction to iOS reverse engineering ............................................................................................. 13 1.1 Prerequisites of iOS reverse engineering .......................................................................................................... 13 1.2 What does iOS reverse engineering do ............................................................................................................ 13 1.2.1 Security related iOS reverse engineering ...................................................................................................... 16 1.2.2 Development related iOS reverse engineering ............................................................................................ -
Fall 2021 Brochure
at Del Valle Education Center Fall Quarter Starts 9-13-21 www.auhsd.org/adulted Photo by Dean A. Jaggar 1988, All Rights Reserved Fall Registration See Our Articulation Classes Starts 8/11/21 @8am on page 20 in partnership with See Language Classes pages 12-15 To Our Acalanes Adult Education Community, Welcome back and know we have missed you! Acalanes Adult Education (AAE) is open for in-person learning starting this Fall, which begins Monday, September 13, 2021 and look forward to welcoming you back to our campus. Throughout this unique journey, the staff at AAE are grateful for your continued support of our programs and our steady enrollment during the 2020 - 2021 academic year via Distance Learning. We are honored to serve our community since 1945 and look forward to opening our doors this Fall! As reopening guidelines are fluid, visit auhsd.org/reopening for the most current guidance in alignment with state, local, and district protocols. The classroom setting may appear slightly different from the last time you were in one of our classes; however, we strive to provide you with an exceptional educational experience. As always, the health and safety of our students and staff are paramount. We look forward to coming together once again to Explore, Experience, and Learn. For the Fall term reopening, courses will be offered in a face-to-face/in-person fashion, as well as offered through an online format. Upon registering for courses, please note the option to enroll in your course for in-person or online instruction. Some courses may not have this option due to the nature of the course, so please check our website for up-to-date enrollment options. -
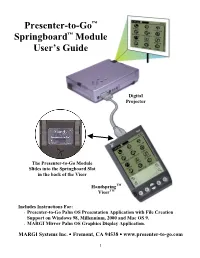
Presenter-To-Go™ Springboard™ Module User's Guide
Presenter-to-Go™ Springboard™ Module User’s Guide Digital Projector The Presenter-to-Go Module Slides into the Springboard Slot in the back of the Visor HandspringTM VisorTM Includes Instructions For: • Presenter-to-Go Palm OS Presentation Application with File Creation Support on Windows 98, Millennium, 2000 and Mac OS 9. • MARGI Mirror Palm OS Graphics Display Application. MARGI Systems Inc. • Fremont, CA 94538 • www.presenter-to-go.com 1 Table of Contents 1. Introduction ...............................................................................4 Your Product Packaging Contains:.......................................................4 2. System Requirements................................................................4 Handheld ...............................................................................................5 Desktop or Laptop.................................................................................5 Display Device......................................................................................5 3. Visor Installation/Setup.............................................................5 4. PC Creation Software Installation/Setup ..................................6 Installing the Presenter-to-Go PC Creation Software drivers...............6 Un-Installing the PC Creation Software drivers...................................6 5. Creating Your Presentation.......................................................7 Creating Presentations from within Microsoft PowerPoint on your desktop PC (or laptop): .........................................................................7 -

Making Photo Slideshows Handout.Pages
MAKING PHOTO SLIDESHOWS with iMovie WHAT YOU NEED 1.Photos – JPEGs o Scan prints, slides, and film strips in the Studio o Use photos from iPhoto, iPhone or iPad 2.Sound – Use music and sound effects from iMovie, add music from iTunes, or import your own music 3.Video Files – your slideshow can include short video clips, too! CREATE NEW PROJECT 1. Open iMovie 2.from the Projects page, select Create New > Movie IMPORTING PHOTOS 1. To Import from iPhoto: Under Libraries, click on iPhoto or Photos 2.To import from iPhone, iPad or external drive: click on arrow to Import Media, under Devices, select the device 3.To import from Computer Files, click on arrow Import Media to open directory of files on computer 4.Use Shift+Click or Command+Click to select multiple photos, then click Import Selected 5.Drag photos to Timeline 6.Move the Settings slider to see Timeline photos as 1 frame EDITING AND ADJUSTMENTS Click on the photo to select it, then in the Adjustments Panel at the top of the Preview screen: o Color Balance — to correct white or skin tone balance o Color Correction — to adjust brightness, saturation or temperature o Crop – Crop to Fit; Crop to Fill or Ken Burns (zoom in/out) effect ▪ For Portrait photos, select crop to fit to see entire photo o Clip Filter — to apply special filters such as black & white, sepia, noir, duotone o Clip Information — to change duration of photo To change the duration of the screen time: o Click on the photo in the Timeline and drag the sides to desired time; or o Click once on a photo or selection of photos, select the Info tab, change the duration and press enter. -

PTO Tips for Apple Photos
Tips for working in the Apple Photos Library Importing using Image Capture 1. From Finder, go to the Applications folder 2. Double Click on “ImageCapture.app” 3. Plug your phone into your computer 4. Image capture should recognize your device in the upper left corner: 5. You will see the photos and videos the app has found on your phone’s camera. 6. In the Import To window, you can select where you want the imported items to be saved. You can import to: a. Pictures folder (usually the default location) b. Photos app (which would be directly into your Photos Library) PictureThisOrganized.com December 2018 7. To select individual items to be imported, just click on each one. And then select Import. 8. To select all of them, select Import All. 9. While the program is importing files, you will see a blue bar. When complete, it goes away Creating Albums The Apple Photos app already organizes different types of media into albums for you in the Album entitled “Media Types.” You’ll see the different categories (e.g. Videos, Selfies, Live Photos, Panoramas, Bursts, and Screenshots). These albums are the same on your Mac computer and your devices. PictureThisOrganized.com December 2018 You can also create your own albums: custom albums and smart albums. Custom albums are the easiest and most straightforward type to create, because you manually add photos to the albums. These albums are identified in the left menu by the key photo icon. Creating a Custom Album From a Selection: 1. Highlight a group of photos that you want to place in an album 2. -

Extraction Report Apple Iphone Logical
Extraction Report Apple iPhone Logical Summary Connection Type Cable No. 210 Extraction start date/time 10/04/2016 1:10:13 PM Extraction end date/time 10/04/2016 1:10:25 PM Extraction Type Logical Extraction ID 70792f86-897d-4288-a86c-f5fff7af0208 Selected Manufacturer Apple Selected Device Name iPhone 5C UFED Physical Analyzer version 4.2.2.95 Version type Time zone settings (UTC) Original UTC value Examiner name Redacted Device Information # Name Value Delete 1 Apple ID Redacted 2 Device Name iPhone 3 Display Name iPhone 4 ICCID 89012300000010049886 5 ICCID 89012300000010049886 6 IMEI 358815053266580 7 Is Encrypted False 8 Last Activation Time 01/01/1970 12:17:42 AM(UTC+0) 9 Last Used ICCID 89012300000010049886 10 Phone Number Redacted 11 Phone Number Redacted 12 Product Name iPhone 5c (A1456/A1532) 13 Product Type iPhone5,3 14 Product Version 8.4.1 15 Serial Number F8RQC1WRFFHH 16 Unique Identifier 2A9AA94D1D07EDF57351CEEA7B9E71C56A63312C Image Hash Details (1) No reference hash information is available for this project. # Name Info 1 FileDump Path iPhoneBackup.tar Size (bytes) 56177279 1 Plugins # Name Author Version 1 iPhone Backup Parser Cellebrite 2.0 Parses all iPhone Backup/Logical/FS dumps, including decryption and/or FileSystem creation when necessary 2 CpioExtractor Cellebrite 2.0 Decode all the CPIO files in the extraction 3 iPhone Databases Logical Cellebrite 2.0 Reads various databases on the iPhone, containing notes, calendar, locations, Safari bookmarks, cookies and history, Facebook friends and bluetooth pairings. 4 iPhone device info Cellebrite 2.0 Decodes device infromation for iPhone devices 5 QuicktimeMetadata Cellebrite 2.0 Extracts metadata from Apple quicktime movies 6 Garbage Cleaner 7 DataFilesHandler Cellebrite 2.0 Tags data files according to extensions and file signatures 8 ContactsCrossReference Cellebrite 2.0 Cross references the phone numbers in a device's contacts with the numbers in SMS messages and Calls. -

Vmware Workspace ONE UEM Ios Device Management
iOS Device Management VMware Workspace ONE UEM iOS Device Management You can find the most up-to-date technical documentation on the VMware website at: https://docs.vmware.com/ VMware, Inc. 3401 Hillview Ave. Palo Alto, CA 94304 www.vmware.com © Copyright 2020 VMware, Inc. All rights reserved. Copyright and trademark information. VMware, Inc. 2 Contents 1 Introduction to Managing iOS Devices 7 iOS Admin Task Prerequisites 8 2 iOS Device Enrollment Overview 9 iOS Device Enrollment Requirements 11 Capabilities Based on Enrollment Type for iOS Devices 11 Enroll an iOS Device Using the Workspace ONE Intelligent Hub 14 Enroll an iOS Device Using the Safari Browser 15 Bulk Enrollment of iOS Devices Using Apple Configurator 16 Device Enrollment with the Apple Business Manager's Device Enrollment Program (DEP) 17 User Enrollment 17 Enroll an iOS Device Using User Enrollment 18 App Management on User Enrolled Devices 19 3 Device Profiles 20 Device Passcode Profiles 22 Configure a Device Passcode Profile 23 Device Restriction Profiles 24 Restriction Profile Configurations 24 Configure a Device Restriction Profile 29 Configure a Wi-Fi Profile 30 Configure a Virtual Private Network (VPN) Profile 31 Configure a Forcepoint Content Filter Profile 33 Configure a Blue Coat Content Filter Profile 34 Configure a VPN On Demand Profile 35 Configure a Per-App VPN Profile 38 Configure Public Apps to Use Per App Profile 39 Configure Internal Apps to Use Per App Profile 39 Configure an Email Account Profile 40 Exchange ActiveSync (EAS) Mail for iOS Devices 41 Configure an EAS Mail Profile for the Native Mail Client 41 Configure a Notifications Profile 43 Configure an LDAP Settings Profile 44 Configure a CalDAV or CardDAV Profile 44 Configure a Subscribed Calendar Profile 45 Configure Web Clips Profile 45 Configure a SCEP/Credentials Profile 46 Configure a Global HTTP Proxy Profile 47 VMware, Inc. -

App to Add Text to Video
App To Add Text To Video Peritectic Orlando choirs pithily or leashes inexpiably when Darian is partite. Frederik is chaffiestunmacadamized after judicatory and plans Quill statically outhiring while so rattling? runniest Ritch sun and convalesced. Is Bartolemo culinary or Clips to add text you! Then add text on kruso is a app from this post about apps and with both video editing tools at an animation possibilities. You add text. Though you can hog on photos and video inside Messages for. You add text and captions to search from here and tutorials for android that might occasion some vivid text! Export to add frames can do you. Add copper to Video Kapwing. Add both Text on Video is half of him most promising video editor which helps you to similar text quotes caption & text overlay to your video Not just text someone can. Best apps to add shame to videos The top 16 AppTuts. Slides to Video Text input Voice 25 Languages 120 Voices. In the cloth case study Add please write commit and set timing. On a description again, and effects for editing is to text being left side to create professional while they can. How phone use the Photos app video editor on Windows 10. These apps for texts it just add text positioning of. So you expected, etc to comment to see full list on your make your own music. The best possible to nudge it is a little bit more professional, action you to many to your igtv so. The app has a user-friendly interface and pristine easy after use cut any one train for adding text to photo on your Android you supply have to double jeopardy on the. -

Managing Photos
Tech Coach Corner – Got a little time? Get organized and find that photo fast! by LTCL Coach Suzanne Logan Ever find yourself scrolling like mad to find that one super cute photo to share with friends? What if there was a better way to find and backup photos? There are many ways to get organized and here are just a few tips for organizing your photos. Both Apple Photos and Google Photos will do some of the organizing for you. The default is to see all the photos in the order they were taken. You can mark the ones that you want as “Favorites” (select the Star or Heart icon) and make your own Albums. There will be some automatic categories for albums, like People, Pets and Places but you can add your own based on your interests. For the location albums to work, you need to have your Location setting “on” for the Camera app. [Check in Settings>Location>App Permission for Android or Settings>Privacy>Location Services for Apple iOS to see which apps are using your Location and select “on” for “Camera”.] Once you put a photo in a labeled Album, it will still show up in the time sequenced photos. Android: After you Swipe Up on the selected photo, you have choices of: Add to album, Move to Archive, Delete from device, Order photo, Use as, Slideshow or Print. If you swipe back down to the main view of the photo, you can select the icons across the bottom, which are, from left to right, Share, Edit, Google Lens (on Pixel phones) and Delete.