Autofac Documentation Release 6.0.0
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Ioc Containers in Spring
301AA - Advanced Programming Lecturer: Andrea Corradini [email protected] http://pages.di.unipi.it/corradini/ AP-2018-11: Frameworks and Inversion of Control Frameworks and Inversion of Control • Recap: JavaBeans as Components • Frameworks, Component Frameworks and their features • Frameworks vs IDEs • Inversion of Control and Containers • Frameworks vs Libraries • Decoupling Components • Dependency Injection • IoC Containers in Spring 2 Components: a recap A software component is a unit of composition with contractually specified interfaces and explicit context dependencies only. A software component can be deployed independently and is subject to composition by third party. Clemens Szyperski, ECOOP 1996 • Examples: Java Beans, CLR Assemblies • Contractually specified interfaces: events, methods and properties • Explicit context dependencies: serializable, constructor with no argument • Subject to composition: connection to other beans – Using connection oriented programming (event source and listeners/delegates) 3 Towards Component Frameworks • Software Framework: A collection of common code providing generic functionality that can be selectively overridden or specialized by user code providing specific functionality • Application Framework: A software framework used to implement the standard structure of an application for a specific development environment. • Examples: – GUI Frameworks – Web Frameworks – Concurrency Frameworks 4 Examples of Frameworks Web Application Frameworks GUI Toolkits 5 Examples: General Software Frameworks – .NET – Windows platform. Provides language interoperability – Android SDK – Supports development of apps in Java (but does not use a JVM!) – Cocoa – Apple’s native OO API for macOS. Includes C standard library and the Objective-C runtime. – Eclipse – Cross-platform, easily extensible IDE with plugins 6 Examples: GUI Frameworks • Frameworks for Application with GUI – MFC - Microsoft Foundation Class Library. -

Design Pattern Interview Questions
DDEESSIIGGNN PPAATTTTEERRNN -- IINNTTEERRVVIIEEWW QQUUEESSTTIIOONNSS http://www.tutorialspoint.com/design_pattern/design_pattern_interview_questions.htm Copyright © tutorialspoint.com Dear readers, these Design Pattern Interview Questions have been designed specially to get you acquainted with the nature of questions you may encounter during your interview for the subject of Design Pattern. As per my experience good interviewers hardly plan to ask any particular question during your interview, normally questions start with some basic concept of the subject and later they continue based on further discussion and what you answer: What are Design Patterns? Design patterns represent the best practices used by experienced object-oriented software developers. Design patterns are solutions to general problems that software developers faced during software development. These solutions were obtained by trial and error by numerous software developers over quite a substantial period of time. What is Gang of Four GOF? In 1994, four authors Erich Gamma, Richard Helm, Ralph Johnson and John Vlissides published a book titled Design Patterns - Elements of Reusable Object-Oriented Software which initiated the concept of Design Pattern in Software development. These authors are collectively known as Gang of Four GOF. Name types of Design Patterns? Design patterns can be classified in three categories: Creational, Structural and Behavioral patterns. Creational Patterns - These design patterns provide a way to create objects while hiding the creation logic, rather than instantiating objects directly using new opreator. This gives program more flexibility in deciding which objects need to be created for a given use case. Structural Patterns - These design patterns concern class and object composition. Concept of inheritance is used to compose interfaces and define ways to compose objects to obtain new functionalities. -

Logview Studio Linux Preparation with Mono
LogView Studio Linux Preparation with Mono 2014 by Dominik Schmidt [email protected] © 2014 Dominik Schmidt / Holger Hemmecke I LogView Studio Table of Contents Part I Linux Prepare 1 1 SSH Co..n..n..e..c..t. ........................................................................................................................ 1 2 Raspbe..r.r.y.. .P..i. ......................................................................................................................... 4 System Prepar..a..t.i.o...n.. ............................................................................................................................................... 5 Mono .......................................................................................................................................................... 6 Install Mono......................................................................................................................................................... 7 Compile Mon..o.. .f.r..o..m.. .T..A...R....................................................................................................................................... 8 Compile Mon..o.. .f.r..o..m.. .G...I.T........................................................................................................................................ 9 Testing ......................................................................................................................................................... 10 3 Cubie.t.r.u..c..k.. ......................................................................................................................... -
Dependency Injection with Unity
D EPEN DEPENDENCY INJECTION WITH UNITY Over the years software systems have evolutionarily become more and more patterns & practices D ENCY complex. One of the techniques for dealing with this inherent complexity Proven practices for predictable results of software systems is dependency injection – a design pattern that I allows the removal of hard-coded dependencies and makes it possible to Save time and reduce risk on your NJECT assemble a service by changing dependencies easily, whether at run-time software development projects by or compile-time. It promotes code reuse and loosely-coupled design which incorporating patterns & practices, I leads to more easily maintainable and flexible code. Microsoft’s applied engineering ON guidance that includes both production The guide you are holding in your hands is a primer on using dependency quality source code and documentation. W I injection with Unity – a lightweight extensible dependency injection TH DEPENDENCY INJECTION container built by the Microsoft patterns & practices team. It covers The guidance is designed to help U software development teams: various styles of dependency injection and also additional capabilities N I of Unity container, such as object lifetime management, interception, Make critical design and technology TY and registration by convention. It also discusses the advanced topics of selection decisions by highlighting WITH UNITY enhancing Unity with your custom extensions. the appropriate solution architectures, technologies, and Microsoft products The guide contains plenty of trade-off discussions and tips and tricks for for common scenarios managing your application cross-cutting concerns and making the most out of both dependency injection and Unity. These are accompanied by a Understand the most important Dominic Betts real world example that will help you master the techniques. -

Designpatternsphp Documentation Release 1.0
DesignPatternsPHP Documentation Release 1.0 Dominik Liebler and contributors Jul 18, 2021 Contents 1 Patterns 3 1.1 Creational................................................3 1.1.1 Abstract Factory........................................3 1.1.2 Builder.............................................8 1.1.3 Factory Method......................................... 13 1.1.4 Pool............................................... 18 1.1.5 Prototype............................................ 21 1.1.6 Simple Factory......................................... 24 1.1.7 Singleton............................................ 26 1.1.8 Static Factory.......................................... 28 1.2 Structural................................................. 30 1.2.1 Adapter / Wrapper....................................... 31 1.2.2 Bridge.............................................. 35 1.2.3 Composite............................................ 39 1.2.4 Data Mapper.......................................... 42 1.2.5 Decorator............................................ 46 1.2.6 Dependency Injection...................................... 50 1.2.7 Facade.............................................. 53 1.2.8 Fluent Interface......................................... 56 1.2.9 Flyweight............................................ 59 1.2.10 Proxy.............................................. 62 1.2.11 Registry............................................. 66 1.3 Behavioral................................................ 69 1.3.1 Chain Of Responsibilities................................... -
JAVA CONCURRENCY ONLINE TRAINING – Java2aspire
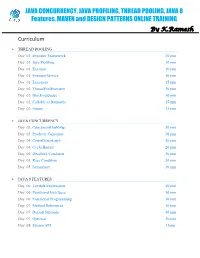
JAVA CONCURRENCY, JAVA PROFILING, THREAD POOLING, JAVA 8 Features, MAVEN and DESIGN PATTERNS ONLINE TRAINING By K.Ramesh Curriculum THREAD POOLING Day 01: Executor Framework 20 min Day 01: Java Profiling 10 min Day 01: Executor 10 min Day 01: ExecutorService 10 min Day 01: Executors 15 min Day 02: ThreadPoolExecutor 20 min Day 02: BlockingQueue 10 min Day 02: Callable vs Runnable 15 min Day 02: Future 15 min JAVA CONCURRENCY Day 03: ConcurrentHashMap 30 min Day 03: Producer Consumer 30 min Day 04: CountDownLatch 20 min Day 04: CyclicBarrier 20 min Day 04: Deadlock Condition 20 min Day 05: Race Condition 30 min Day 05: Semaphore 30 min JAVA 8 FEATURES Day 06: Lambda Expressions 40 min Day 06: Functional Interfaces 10 min Day 06: Functional Programming 10 min Day 07: Method References 10 min Day 07: Default Methods 40 min Day 07: Optional 10 min Day 08: Stream API 1 hour MAVEN Day 09: Project Object Model (POM) 20 min Day 09: Project Description 10 min Day 09: Public Repository 10 min Day 09: Dependency Management 10 min Day 09: Build Configuration 10 min Day 10: Installation 15 min Day 10: Dependency Scope 15 min Day 10: Proprietary Dependencies 15 min Day 10: Project Inheritance 15 min Day 11: Maven life cycle 20 min Day 11: Maven Directory Structure 20 min Day 11: Archetypes 20 min Day 12: Applications 1 hour DESIGN PATTERNS Day 13: Factory Pattern 20 min Day 13: Abstract Factory Pattern 10 min Day 13: Single Pattern 20 min Day 13: Prototype Pattern 10 min Day 14: Composite Pattern 10 min Day 14: Facade Pattern 15 min Day 14: DAO -

Semantic Description of Services and Service Factories for Ambient Intelligence Rémi Emonet
Semantic Description of Services and Service Factories for Ambient Intelligence Rémi Emonet To cite this version: Rémi Emonet. Semantic Description of Services and Service Factories for Ambient Intelligence. Soft- ware Engineering [cs.SE]. Institut National Polytechnique de Grenoble - INPG, 2009. English. tel- 00450479 HAL Id: tel-00450479 https://tel.archives-ouvertes.fr/tel-00450479 Submitted on 26 Jan 2010 HAL is a multi-disciplinary open access L’archive ouverte pluridisciplinaire HAL, est archive for the deposit and dissemination of sci- destinée au dépôt et à la diffusion de documents entific research documents, whether they are pub- scientifiques de niveau recherche, publiés ou non, lished or not. The documents may come from émanant des établissements d’enseignement et de teaching and research institutions in France or recherche français ou étrangers, des laboratoires abroad, or from public or private research centers. publics ou privés. GRENOBLE INP n◦ attribu´epar la biblioth`eque THESE` pour obtenir le grade de ❉♦❝❡✉ ❉✉ ●♦✉♣❡ ●❡♥♦❜❧❡ ■◆ Sp´ecialit´e: Informatique pr´epar´eeau Laboratoire d’Informatique de Grenoble dans le cadre de l’Ecole´ Doctorale Math´ematiques, Sciences et Technologies de l’Information, Informatique pr´esent´eeet soutenue publiquement par R´emi ❊♠♦♥❡ le 23 septembre 2009 ❉❡❝✐♣✐♦♥ ❙♠❛♥✐✉❡ ❞❡ ❙❡✈✐❝❡ ❡ ❞✬❯✐♥❡ à ❙❡✈✐❝❡ ♣♦✉ ❧✬■♥❡❧❧✐❣❡♥❝❡ ❆♠❜✐❛♥❡ ❙❡♠❛♥✐❝ ❉❡❝✐♣✐♦♥ ♦❢ ❙❡✈✐❝❡ ❛♥❞ ❙❡✈✐❝❡ ❋❛❝♦✐❡ ❢♦ ❆♠❜✐❡♥ ■♥❡❧❧✐❣❡♥❝❡ Directeur de th`ese : James L. ❈♦✇❧❡② Co-directeur de th`ese : Dominique ❱❛✉❢❡②❞❛③ JURY Pr. Marie-Christine Rousset Pr´esident Pr. James L. Crowley Directeur de th`ese Dr. Dominique Vaufreydaz Co-directeur de th`ese Pr. Gregory D. Abowd Rapporteur Pr. David Simplot-Ryl Rapporteur Pr. Michel Riveill Examinateur 2 R´esum´e Ce manuscrit ´etudie l’ad´equation des approches `aservices, ainsi que leur am´elioration, pour l’int´egration dynamique et la r´eutilisation logicielle dans le cadre de l’informatique ambiante. -

ENERGY EFFICIENCY in RESIDENTIAL BUILDINGS in MOZAMBIQUE Measurements and Simulations
Report TABK-1027 BZ info: TABK-1027 GABRIEL AUZIANE Rygg: 13,22 = 187 sidor Setup (bxh): 369,22 x 252 Upplaga: 120 Mellanblad: grå and Simulations ENERGY EFFICIENCY IN RESIDENTIAL BUI DINGS MOZAMBIQUE - Measurements Färgsidor: ingen begränsn. ENERGY EFFICIENCY IN RESIDENTIAL BUILDINGS IN MOZAMBIQUE Measurements and Simulations GABRIEL AUZIANE Building Doctoral Thesis Science DEPARTMENT OF CONSTRUCTION SCIENCES DIVISION OF BUILDING SCIENCE ISRN LUTVDG/TABK--15/1027--SE (1-176) | ISSN 1103-4467 ISBN 978-91-7623-159-3 (print) | ISBN 978-91-7623-160-9 (pdf) DOCTORAL THESIS ENERGY EFFICIENCY IN RESIDENTIAL BUILDINGS IN MOZAMBIQUE Measurements and Simulations GABRIEL AUZIANE Copyright © Gabriel Auziane 2015. Printed by Media-Tryck LU, Lund, Sweden, April 2015 (Pl). For information, address: Division of Building Science, LTH, Lund University, Box 118, SE-221 00 Lund, Sweden. Homepage: http://www.bkl.lth.se Acknowledgements I am deeply thankful to my main supervisors, Professor Bertil Fredlund and Associate Professor Susanne Heyden, my co-supervisors Dr. Kurt Källblad, Dr. Daniel Baloi, and the former Head of the Department of Construction Sciences, Professor Göran Sandberg and Professor Anne Landin for offering me the possibility of working in this project and also for support, encouragement, inspiration and patience over the years, without their help and advice this thesis work would never have been successful. Furthermore, I would like to thank the Head of the Division of Structural Mechanics, Professor Erik Serrano and Professors Jesper Arfvidsson and Petter Wallentén, for their supervision of the work and great help in the overall process of this research. I thank Asdi/SAREC for this research receiving financial support through Lund University and Eduardo Mondlane University under the coordination of Prof. -
Sun Certified Enterprise Architect for Java EE Study Guide / Mark Cade, Humphrey Sheil
Many of the designations used by manufacturers and sellers to distinguish their products are claimed as trademarks. Where those designations appear in this book, and the publisher was aware of a trademark claim, the designations have been printed with initial capital letters or in all capitals. Sun Microsystems, Inc. has intellectual property rights relating to implementations of the technology described in this publication. In particular, and without limitation, these intellectual property rights may include one or more U.S. patents, foreign patents, or pending applications. Sun, Sun Microsystems, the Sun logo, J2ME, J2EE, Java Card, and all Sun and Java based trademarks and logos are trademarks or registered trademarks of Sun Microsystems, Inc., in the United States and other countries. UNIX is a registered trademark in the United States and other countries, exclusively licensed through X/Open Company, Ltd. This publication is provided “as is” without warranty of any kind, either express or implied, including, but not limited to, the implied warranties of merchantability, fitness for a particular purpose, or non-infringement. This publication could include technical inaccuracies or typographical errors. Changes are periodically added to the information herein; these changes will be incorporated in new editions of the publication. Sun Microsystems, Inc. may make improvements and/or changes in the product(s) and/or the program(s) described in this publication at any time. The authors and publisher have taken care in the preparation of this book, but make no expressed or implied warranty of any kind and assume no responsibility for errors or omissions. No liability is assumed for incidental or consequential damages in connection with or arising out of the use of the information or programs contained herein. -

KEMPER PROFILER Addendum 8.6 Legal Notice
KEMPER PROFILER Addendum 8.6 Legal Notice This manual, as well as the software and hardware described in it, is furnished under license and may be used or copied only in accordance with the terms of such license. The content of this manual is furnished for informational use only, is subject to change without notice and should not be construed as a commitment by Kemper GmbH. Kemper GmbH assumes no responsibility or liability for any errors or inaccuracies that may appear in this book. Except as permitted by such license, no part of this publication may be reproduced, stored in a retrieval system, or transmitted in any form or by any means, electronic, mechanical, recording, by smoke signals or otherwise without the prior written permission of Kemper GmbH. KEMPER™, PROFILER™, PROFILE™, PROFILING™, PROFILER PowerHead™, PROFILER PowerRack™, PROFILER Stage™, PROFILER Remote™, KEMPER Kone™, KEMPER Kabinet™, KEMPER Power Kabinet™, KEMPER Rig Exchange™, KEMPER Rig Manager™, PURE CABINET™, and CabDriver™ are trademarks of Kemper GmbH. All features and specifications are subject to change without notice. (Rev. September 2021). © Copyright 2021 Kemper GmbH. All rights reserved. www.kemper-amps.com Table of Contents What is new? 1 What is new in version 8.6? 2 Double Tracker 2 Acoustic Simulator Enhancements 3 Auto Swell Sensitivity 3 PROFILER Stage Wi-Fi Enhancement 4 What is new in version 8.5? 5 Important Hints for Users of KEMPER Power Kabinet 5 KEMPER Rig Manager for iOS®* 6 Wi-Fi with PROFILER Stage 9 What is new in version 8.2? 11 Power Amp -

Practical Migration to Linux on System Z
Front cover Practical Migration to Linux on System z Overview and migration methodology Migration analysis Hands-on migration case study Lydia Parziale Joseph Apuzzo Saulo Augusto M Martins da Silva Louis Henderson Manoj Srinivasan Pattabhiraman Richard Sewell ibm.com/redbooks International Technical Support Organization Practical Migration to Linux on System z October 2009 SG24-7727-00 Note: Before using this information and the product it supports, read the information in “Notices” on page xi. First Edition (October 2009) This edition applies to z/VM Version 5.3 and Version 5.4, Novell SUSE Linux Enterprise Server Version 10 and Version 11, and Red Hat Enterprise Linux Version 5.3. © Copyright International Business Machines Corporation 2009. All rights reserved. Note to U.S. Government Users Restricted Rights -- Use, duplication or disclosure restricted by GSA ADP Schedule Contract with IBM Corp. Contents Notices . xi Trademarks . xii Preface . xv The team who wrote this book . xv Become a published author . xviii Comments welcome. xviii Part 1. Overview and migration methodology . 1 Chapter 1. Migration considerations . 3 1.1 Reason to migrate systems. 4 1.1.1 How green is your data center . 4 1.1.2 The IBM Big Green server consolidation . 7 1.2 Benefits of migrating to Linux on System z . 7 1.3 Reasons to select Linux on System z . 9 1.3.1 System z strengths . 10 1.3.2 Value of Linux on System z. 12 1.3.3 Choosing workloads to migrate to IBM System z . 13 1.4 z/VM virtualization for Linux on IBM System z . -

J2EE Architecture and Patterns in Enterprise Systems
J2EE Architecture and Patterns in Enterprise Systems Zhiguo Guo University of Tampere Department of Computer and Information Science Master’s Thesis May 2004 i University of Tampere Department of Computer and Information Science Zhiguo Guo: J2EE Architecture and Patterns in Enterprise Systems Master’s Thesis, 60 pages May 2004 The purpose of this thesis is to illustrate an enterprise project named HUVA, in which Java Platform 2, Enterprise Edition (J2EE) architecture and patterns are applied. This study took a constructive research approach: It starts from the application domain including the initial plan and business model, then moves to the system architecture covering the architecturally significant requirements and the system structure compliant with J2EE architecture, finally ends at the application design elaborated by applying the J2EE patterns at a high level. As a result the architectural and application design satisfied the project needs and requirements; and the HUVA software has been implemented in practice according to the design. Keywords: J2EE, architecture, pattern, enterprise system. ii Acknowledgements I would like to thank Professor Roope Raisamo and Professor Isto Aho from the University of Tampere for being my encouraging, patient and responsible supervisors during the master’s thesis project. I would like to thank Mr. Mika Miettinen from Solteq Oyj and Mr. Timo Westkämper for supporting the technical aspects of this thesis. Finally, I would like to use this opportunity to express huge thanks to my dear wife, Chongliang Tang for always being the invaluable person behind my success. Tampere - Finland, June 1st, 2004 Zhiguo Guo iii Contents 1. Introduction.............................................................................................................1 2. Application domain ...............................................................................................3 2.1.