Armageddon How Your Smartphone CPU Breaks Software-Level Security and Privacy
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

The Military Guide to Armageddon • D
The Military Guide to Armageddon • D. Giamonna, T. Anderson Chosen Books, a division of Baker Publishing Group © 2021 used by permission BATTLE- TESTED STRATEGIES TO PREPARE YOUR LIFE AND SOUL FOR THE END TIMES COL. DAVID J. GIAMMONA AND TROY ANDERSON G The Military Guide to Armageddon • D. Giamonna, T. Anderson Chosen Books, a division of Baker Publishing Group © 2021 used by permission _Giammona_MilitaryGuide_ET_bb.indd 3 10/1/20 8:02 AM 20 21 22 23 24 25 26 7 6 5 4 3 2 1 © 2021 by David J. Giammona and Troy Anderson Published by Chosen Books 11400 Hampshire Avenue South Bloomington, Minnesota 55438 www.chosenbooks.com Chosen Books is a division of Baker Publishing Group, Grand Rapids, Michigan Printed in the United States of America All rights reserved. No part of this publication may be reproduced, stored in a retrieval system, or transmitted in any form or by any means— for example, electronic, photocopy, recording— without the prior written permission of the publisher. The only exception is brief quotations in printed reviews. Library of Congress Cataloging-in-Publication Data Names: Giammona, David J., author. | Anderson, Troy (Journalist), author. Title: The military guide to Armageddon: battle-tested strategies to prepare your life and soul for the end times / Col. David J. Giammona and Troy Anderson. Description: Minneapolis, Minnesota: Chosen Books, a division of Baker Publishing Group, 2021. | Includes bibliographical references. Identifiers: LCCN 2020038021 | ISBN 9780800761943 (paperback) | ISBN 9780800762261 (casebound) | ISBN 9781493430086 (ebook) Subjects: LCSH: Spiritual warfare. | End of the world. | Armageddon. Classification: LCC BV4509.5 .G466 2021 | DDC 236/.9—dc23 LC record available at https://lccn.loc.gov/2020038021 Unless otherwise indicated, Scripture quotations are from THE HOLY BIBLE, NEW INTERNATIONAL VERSION®, NIV® Copyright © 1973, 1978, 1984, 2011 by Biblica, Inc.® Used by permission. -

Key Scriptures: Revelation 19:1-21 Ezekiel 38 & 39 Joel 2:1-11
God's Master Plan In Prophecy Lesson 13 – The Battle of Armageddon & 2nd Coming of Jesus Christ Key Scriptures: Revelation 19:1-21 Ezekiel 38 & 39 Joel 2:1-11 Zechariah 12-14 Introduction Rev 19:1 After these things I heard something like a loud voice of a great multitude in heaven, saying, "Hallelujah! Salvation and glory and power belong to our God; While the Wrath of God is being poured out, there was the voice of "a great multitude in heaven" praising God! This is the redeemed church which has missed the Wrath of God and was taken out of Great Tribulation. While the earth is experiencing the judgment of God without mercy, we are experiencing His goodness without judgment! Rev 19:2-3 BECAUSE HIS JUDGMENTS ARE TRUE AND RIGHTEOUS; for He has judged the great harlot who was corrupting the earth with her immorality, and HE HAS AVENGED THE BLOOD OF HIS BOND-SERVANTS ON HER." 3 And a second time they said, "Hallelujah! HER SMOKE RISES UP FOREVER AND EVER." From what is being said in these verse, it is obvious that the church will be fully aware of what is happening upon the earth during this time, yet because we are no longer viewing earth's events through the eyes of mortal flesh, we will understand that God is righteous and true in His judgments. To modern minds it may seem strange to worship and say, “hallelujah” over the fact that God is pouring out judgment, but that is because we see imperfectly now. -
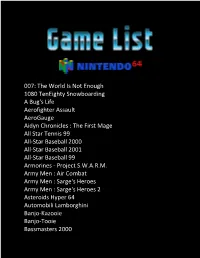
007: the World Is Not Enough 1080 Teneighty Snowboarding a Bug's
007: The World Is Not Enough 1080 TenEighty Snowboarding A Bug's Life Aerofighter Assault AeroGauge Aidyn Chronicles : The First Mage All Star Tennis 99 All-Star Baseball 2000 All-Star Baseball 2001 All-Star Baseball 99 Armorines - Project S.W.A.R.M. Army Men : Air Combat Army Men : Sarge's Heroes Army Men : Sarge's Heroes 2 Asteroids Hyper 64 Automobili Lamborghini Banjo-Kazooie Banjo-Tooie Bassmasters 2000 Batman Beyond : Return of the Joker BattleTanx BattleTanx - Global Assault Battlezone : Rise of the Black Dogs Beetle Adventure Racing! Big Mountain 2000 Bio F.R.E.A.K.S. Blast Corps Blues Brothers 2000 Body Harvest Bomberman 64 Bomberman 64 : The Second Attack! Bomberman Hero Bottom of the 9th Brunswick Circuit Pro Bowling Buck Bumble Bust-A-Move '99 Bust-A-Move 2: Arcade Edition California Speed Carmageddon 64 Castlevania Castlevania : Legacy of Darkness Chameleon Twist Chameleon Twist 2 Charlie Blast's Territory Chopper Attack Clay Fighter : Sculptor's Cut Clay Fighter 63 1-3 Command & Conquer Conker's Bad Fur Day Cruis'n Exotica Cruis'n USA Cruis'n World CyberTiger Daikatana Dark Rift Deadly Arts Destruction Derby 64 Diddy Kong Racing Donald Duck : Goin' Qu@ckers*! Donkey Kong 64 Doom 64 Dr. Mario 64 Dual Heroes Duck Dodgers Starring Daffy Duck Duke Nukem : Zero Hour Duke Nukem 64 Earthworm Jim 3D ECW Hardcore Revolution Elmo's Letter Adventure Elmo's Number Journey Excitebike 64 Extreme-G Extreme-G 2 F-1 World Grand Prix F-Zero X F1 Pole Position 64 FIFA 99 FIFA Soccer 64 FIFA: Road to World Cup 98 Fighter Destiny 2 Fighters -

The Omen Iv Armageddon 2000
The omen iv armageddon 2000 Omen IV: Armageddon is a novel published by Gordon McGill. It is a sequel to The Final Conflict, and is completely unconnected to the film, Omen IV: The Awakening. "Damien Thorn, spawn of Satan, was dead, slain by one of the sacred daggers of Armageddon. First published back in September of , Gordon McGill's novel 'Omen IV: Armageddon ' formed the fourth instalment into the Omen series, concluding. Armageddon has ratings and 11 reviews. Matt said: An enjoyable slice of 80s occult hokum that picks up exactly where The Final Conflict left o. Omen IV: Armageddon [Gordon McGill] on *FREE* shipping on qualifying offers. Omen IV: Armageddon But The Omen didn't just spawn Damien, the Antichrist. In , McGill returned to write Omen IV: Armageddon which opens with a. The Omen is a British-American horror film franchise beginning in The story was In the fourth and final film of the original series, Omen IV: The Awakening, it is revealed that . Gordon McGill; Omen IV: Armageddon , written in by Gordon McGill; Omen V: The Abomination, written in by Gordon McGill Television series: The Omen (); Damien. Going even farther, sequel novels were actually published in the (The Omen IV: Armageddon ) and (The Omen V: The. I've recently flown through Omen IV: Armageddon - wonderful pulp fun. The story as before - Ambassador To The Court Of St James has. Omen IV: Armageddon , McGill's novel, takes the loophole of The Final Conflict – Damien buggering Kate Reynolds rather than allowing. Damien's son, unwittingly raised by Paul Buher, the head of a huge international corporation, threatens to destroy the world with his demonic powers. -
Autonomous Horizons: the Way Forward Is a Product of the Office Air University Press 600 Chennault Circle, Bldg 1405 of the US Air Force Chief Scientist (AF/ST)
Autonomous Horizons The Way Forward A vision for Air Force senior leaders of the potential for autonomous systems, and a general framework for the science and technology community to advance the state of the art Dr. Greg L. Zacharias Chief Scientist of the United States Air Force 2015–2018 The second volume in a series introduced by: Autonomous Horizons: Autonomy in the Air Force – A Path to the Future, Volume 1: Human Autonomy Teaming (AF/ST TR 15-01) March 2019 Air University Press Curtis E. LeMay Center for Doctrine Development and Education Maxwell AFB, Alabama Chief of Staff, US Air Force Library of Congress Cataloging-in-Publication Data Gen David L. Goldfein Names: Zacharias, Greg, author. | Air University (U.S.). Press, publisher. Commander, Air Education and Training | United States. Department of Defense. United States Air Force. Command Title: Autonomous horizons : the way forward / by Dr. Greg L. Zacha- Lt Gen Steven L. Kwast rias. Description: First edition. | Maxwell Air Force Base, AL : AU Press, 2019. “Chief Scientist for the United States Air Force.” | Commander and President, Air University Lt Gen Anthony J. Cotton “January 2019.” |Includes bibliographical references. Identifiers: LCCN 2018061682 | ISBN 9781585662876 Commander, Curtis E. LeMay Center for Subjects: LCSH: Aeronautics, Military—Research—United States. | Doctrine Development and Education United States. Air Force—Automation. | Artificial intelligence— Maj Gen Michael D. Rothstein Military applications—United States. | Intelligent control systems. | Autonomic -

The Battle Armageddon
THE BATTLE OF ARMAGEDDON by David Dence 1 developed a keen interest in this subject when I discovered to my surprise how little my friends know about the Battle of Armageddon. I Many great men have suffered because their view of Armageddon differed from their superiors. Sad. Armageddon is NOT a salvation issue. I will not be saved or lost based on my understanding or misunder- standing of this subject. Thus I should never disparage those who hold a different view. Some have argued that the Battle of Armageddon will be a spiritual battle, while others have insisted that it will be fought with real weapons and armaments. Some have taught that the focus of the battle will be literal Israel. And of course the exact location of the battle has always been a point of contention. So, does it really matter? Perhaps not. But if indeed the battle of Armageddon is imminent, we might be well advised to upgrade our understanding. Let me put it to you like this: The FAA has designated traffic lanes in the sky. When a plane is high in the sky and 150 miles out, air controllers are not going to be concerned if it is flying a hundred feet above or below its assigned altitude. When the plane is 15 miles from the airport it better not be more than a few feet above or below its assigned altitude. And when it is less than a mile from the runway it better be within a few inches of its assigned altitude. Folks, we are lined up with the runway now. -

Dodging Armageddon: the Third World War That Almost Was, 1950 (B) (3)-P.L
eclassifi ed and Approved for Release by NSA on 11-04-201 O pursuant to E .0. 13526, FOIA Case# 1.1'--."'4/~c-~D: 3 9 67119 T0P sceRETNe0MIN'Ffi'X1 Cryptologic Quarterly (U) Dodging Armageddon: The Third World War That Almost Was, 1950 (b) (3)-P.L. 86-36 (U) With the comfort and hindsight of a half century, President Harry Truman's decision to Jo~eph V. St3l1n commit American power to save South Korea from Communist aggression in late June 1950 stands as perhaps America's finest moment of the Cold War. By making a difficult commitment, by sacrificing 50,000 American lives in the end, Truman upheld Western values and interests where they were directly threatened. It is easy to overlook the unpopularity and unpleasantness of a war which, though necessary, nevertheless remains unknown to most Americans today. Our sacrifices in Korea beginning in the disastrous summer of 1950 merit recognition and honor in their own right, yet they deserve our attention for another reason almost completely neglected in accounts of the period. By dispatching the 24th Infantry and 1st Cavalry Divisions from comfort able occupation duty in Japan to death and ratus opened the "Greek line," supplying destruction in Korea in mid-summer 1950, the Communist insurgents in neighboring Greece United States actually did nothing less than save v.r:ith weapons and supplies, an effort which the world from a global conflagration. quickly outpaced Soviet support to the guerrillas; 10,000 Yugoslav "volunteers" fought alongside (U) The issue was found not in Asia but on the their Greek allies too. -

FN1405-Nuc-Ross
Foreign Policy Research Institute FOOTNOTES Vol. 14, No. 5 The Newsletter of the Wachman Center May 2009 THE ROLE OF NUCLEAR WEAPONS IN INTERNATIONAL POLITICS: A STRATEGIC PERSPECTIVE By Andrew L. Ross Andrew L. Ross is director of the Center for Science, Technology, and Policy and professor of political science at University of New Mexico. This essay is based on his talk at the FPRI Wachman Center’s History Institute for Teachers on Teaching the Nuclear Age, held March 28-29, 2009. The Institute was cosponsored by the American Academy of Diplomacy and cosponsored and hosted by the Atomic Testing Museum in Las Vegas, Nevada. See http://www.fpri.org/education/nuclearage/ for videofiles, texts of lectures, and classroom lessons. The History Institute for Teachers is co-chaired by David Eisenhower and Walter A. McDougall. Core support is provided by the Annenberg Foundation and Mr. H.F. Lenfest. THE DAWN OF THE NUCLEAR AGE The Nuclear Age began with the World War II Manhattan Project (1942-46), which culminated in the Trinity test on July 16, 1945, of the “Gadget” and the August 1945 bombings of Hiroshima and Nagasaki. The Project was led by Gen. Leslie Groves; physicist J. Robert Oppenheimer directed the scientific research. The Trinity test took place on a test range north of Alamogordo, NM. Gadget was a somewhat less than 20-kiloton implosion-type fission device. Its yield was the equivalent of the bomb load of 2000 fully loaded WWII B-29s. Reacting to the test, Oppenheimer quoted the Bhagavad-Gita: “I am become Death, the Shatterer of Worlds.” Less than a month later, “Little Boy” was dropped on Hiroshima, on August 6, 1945. -
Wildland Urban Interface (WUI) Fire Operational Requirements And
Wildland Urban Interface Fire Operational Requirements and Capability Analysis Report of Findings May 31, 2019 1 WUI FIRE OPERATIONAL REQUIREMENTS AND TECHNOLOGY CAPABILITY AN ALYS IS Wildland Urban Interface (WUI) Operational Requirements and Capability Analysis Project: Th is report represents the collective efforts of an Integrated Project Team (IPT). Below are the organizational points of contact for this report: Science and Technology Directorate Dr. Geoffrey Berlin Dr. Micha el Hieb ii WUI FIRE OPERATIONAL REQUIREMENTS AND TECHNOLOGY CAPABILITY AN ALYS IS Ta b le o f Contents Executive Summary ..................................................................................................................................... v Key Findings ............................................................................................................................................... vii Next Steps ................................................................................................................................................ xi I. Introduction ............................................................................................................................................... 1 II. Methodology ............................................................................................................................................. 3 1. Define Mission Elements ..................................................................................................................... 3 2. Elicit Requirements and Identify -
Armageddon: Cache Attacks on Mobile Devices
ARMageddon: Cache Attacks on Mobile Devices Moritz Lipp, Daniel Gruss, Raphael Spreitzer, Clémentine Maurice, and Stefan Mangard, Graz University of Technology https://www.usenix.org/conference/usenixsecurity16/technical-sessions/presentation/lipp This paper is included in the Proceedings of the 25th USENIX Security Symposium August 10–12, 2016 • Austin, TX ISBN 978-1-931971-32-4 Open access to the Proceedings of the 25th USENIX Security Symposium is sponsored by USENIX ARMageddon: Cache Attacks on Mobile Devices Moritz Lipp, Daniel Gruss, Raphael Spreitzer, Clementine´ Maurice, and Stefan Mangard Graz University of Technology, Austria Abstract the possibility to use Flush+Reload to automatically ex- In the last 10 years, cache attacks on Intel x86 CPUs have ploit cache-based side channels via cache template at- gained increasing attention among the scientific com- tacks on Intel platforms. Flush+Reload does not only al- munity and powerful techniques to exploit cache side low for efficient attacks against cryptographic implemen- channels have been developed. However, modern smart- tations [8,26,56], but also to infer keystroke information phones use one or more multi-core ARM CPUs that have and even to build keyloggers on Intel platforms [19]. In a different cache organization and instruction set than contrast to attacks on cryptographic algorithms, which Intel x86 CPUs. So far, no cross-core cache attacks have are typically triggered multiple times, these attacks re- been demonstrated on non-rooted Android smartphones. quire a significantly higher accuracy as an attacker has In this work, we demonstrate how to solve key chal- only one single chance to observe a user input event. -

2001 Annual Report
wdwCovers 12/18/01 5:17 PM Page 1 The Company ANNUAL REPORT 2001 wdwCovers 12/18/01 5:17 PM Page 2 Reveta F. Bowers John E. Bryson Roy E. Disney Michael D. Eisner Judith L. Estrin Stanley P. Gold Robert A. Iger Monica C. Lozano George J. Mitchell Thomas S. Murphy Leo J. O’Donovan, S.J. Sidney Poitier Robert A.M. Stern Andrea L. Van de Kamp Raymond L. Watson Gary L. Wilson 20210F01_P01.09_v2 12/18/01 5:19 PM Page 1 The Walt Disney Company and Subsidiaries CONTENT LISTING Financial Highlights 1 Management’s Discussion and Analysis 49 Letter to Shareholders 2 Consolidated Statements of Income 60 Financial Review 10 Consolidated Balance Sheets 61 DisneyHand 14 Consolidated Statements of Cash Flows 62 Parks and Resorts 18 Consolidated Statements of Stockholders’ Equity 63 Walt Disney Imagineering 26 Notes to Consolidated Financial Statements 64 Studio Entertainment 28 Quarterly Financial Summary 77 Media Networks 36 Selected Financial Data 78 Broadcast Networks 37 Management’s Responsibility of Financial Statements 79 Cable Networks 38 Report of Independent Accountants 79 Consumer Products 44 Board of Directors and Corporate Executive Officers 80 Walt Disney International 48 FINANCIAL HIGHLIGHTS (In millions, except per share data) 2001 2000 Revenues(1) $25,256 $25,356 Segment operating income(1) 4,038 4,124 Diluted earnings per share before the cumulative effect of accounting changes, excluding restructuring and impairment charges and gain on the sale of businesses(1) 0.72 0.72 Cash flow from operations 3,048 3,755 Borrowings 9,769 9,461 Stockholders’ equity 22,672 24,100 (1) Pro forma revenues, segment operating income and earnings per share reflect the sale of Fairchild Publications, the acquisition of Infoseek, the conversion of Internet Group common stock into Disney common stock and the closure of the GO.com portal business as if these events and the adoption of SOP 00-2 had occurred at the beginning of fiscal 2000, eliminating the one-time impact of those events. -

Grounding the Lame Duck: the President, the Final Three Months, and Emergency Powers
Grounding the Lame Duck: The President, the Final Three Months, and Emergency Powers ARI B. RUBIN* TABLE OF CONTENTS INTRODUCTION ..................................................... 908 I. IS THERE A PROBLEM? WHAT PAST LAME-DUCK ACTIONS REVEAL . 909 A. HISTORY OF CONTENTIOUS LAME-DUCK ACTIONS . 911 B. COUNTEREXAMPLES AND EQUITIES ........................... 915 C. HYPOTHETICALS. ......................................... 921 II. JUDICIAL INTERVENTION ........................................ 922 A. CONSTITUTIONAL CONSTRAINTS AND SEPARATION OF POWERS . 923 1. Take Care Clause .............................. 927 2. Oath Clause................................... 928 3. Term Clauses ................................. 929 4. Impeachment Clauses ........................... 930 B. THE AMENDMENTS AND NORMS.............................. 933 1. The Twentieth Amendment ....................... 933 2. The Twenty-Second Amendment . 936 3. The Twenty-Fifth Amendment .................... 940 C. CASE LAW DEALING WITH LAME-DUCK ACTIONS . 945 III. THE NEXT CRISIS ............................................. 952 A. LAME-DUCK DOCTRINE. .................................... 952 B. ENSHRINING THE DOCTRINE IN LAW .......................... 955 * Georgetown Law, J.D. 2020; Wesleyan University, B.A. 2002. © 2021, Ari B. Rubin. The author is clerk to Chief Judge Matthew J. Fader of the Maryland Court of Special Appeals. Prior to law, the author was a ®lm and TV writer and producer, and he has written opinion pieces for publications including Politico, the HuffPost,