SSA-434534: Memory Protection Bypass Vulnerability in SIMATIC S7-1200 and S7-1500 CPU Families
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Joint Spin-Off Report
This report is a non-binding convenience translation of the German-language original report, which is the legally relevant document under German law. Joint Spin-off Report of the Managing Boards of Siemens Aktiengesellschaft, Berlin and Munich, and OSRAM Licht AG, Munich, on the Spin-off of a Majority Participation in OSRAM pursuant to Section 127 sentence 1 German Transformation Act (Umwandlungsgesetz) I. Introduction ................................................................................................................ 11 II. Starting situation – The legal entities involved in the Spin-off and the Siemens Group prior to the Spin-off ....................................................................................... 14 1. Overview of the Siemens Group ................................................................................ 14 2. Siemens AG as the transferring entity...................................................................... 16 a) Registered office and fiscal year .................................................................... 16 b) Capital stock and shares ................................................................................ 16 c) Warrant bonds ................................................................................................ 16 d) Stock-based compensation programs and employee participation programs – authorization to purchase treasury shares .............................. 17 e) Shareholder structure and trading on the stock exchange ......................... 18 f) Managing -

BSH 2010 English.Indd
1 Corporate Social Responsibility Report 2010 BSH IKIAKES SYSKEVES A.B.E CONTENTS 3 1. Introduction Page 4 2. Managing Directors’ Message Page 5 The Company 3. BSH IKIAKES SYSKEVES A.B.E.: The Company Page 6 3.1. History Page 6 3.2. Plants in Athens Page 7 3.3. History of Pitsos Page 7 Corporate Social 4. BSH Ikiakes Syskeves A.B.E” and Corporate Social Responsibility (CSR) Page 8 Responsibility 4.1. The Company’s Philosophy and Sustainability Page 8 4.2 Corporate Governance Page 9 4.3. Code of Business Conduct Page 10 4.4. Mapping our Stakeholders Page 10 4.5. Memberships in Associations and Business Organisations Page 11 Human Resources 5. Acting Responsibly: Our People Page 12 5.1. Policy Page 12 5.2. Equal Opportunities at the Workplace Page 12 5.3. Health & Safety Policy Page 13 5.4. Employee Development and Training Page 14 5.5. Volunteer Work Page 15 5.6. Communicating with our Employees Page 15 The Market 6. Acting Responsibly: the Market Page 16 6.1. Policy Page 16 6.2. Products and Services Page 16 6.3. Supply Chain & Partners & Contribution to Community Page 18 6.4. Customer and Partner Satisfaction Page 18 Environment 7. Acting Responsibly: The Environment and Society Page 20 and Society 7.1. Policy Page 20 7.2. Environmental Management Page 20 7.3. Raw Material Consumption Page 21 7.4. Paper Consumption Page 21 7.5. Energy Consumption Page 21 7.6. Greenhouse Gas Emissions Reduction Page 22 7.7. Water Management and Consumption Page 23 7.8. -

Susan Ascher Olga Brook Christopher
The following planners, managers and reviewers have no financial relationships to disclose: Susan Ascher Olga Brook Christopher Francois Desiree Morgan Andrew Rosenkrantz Aarti Sekhar Jennifer Sheehan Alexis LaCount Ramesh Iyer Bojan Petrovic Lindsay Scott The following planners and managers reported the following financial relationships or relationships to products or devices they or thei spouse/partner have with commercial interests related to the content of this CME activity: First Name Last Name Commercial Interest Explanation/Other Mustafa Bashir No No Yes Research Grants Siemens Healthcare , NGM Biopharmaceuticals, Metacrine Inc, ProSciento Inc, Pinnacle Clinical Research, CymaBay Matthew Davenport No No No Royalties: Wolters Kluwer and uptodate.com Ross Filice No No Yes Stock Options, Ownership/Partnership, Research am an advisor to and have a 0.5% equity stake in BunkerHill Grants, Consultant Health, Inc. I am a co-founder of DexNote, LLC. I have also received an academic GPU grant from Nvidia Corporation. None of these relate directly to any of my roles at SCBT-MR. Avinash Kambadakone Ramesh No No Yes Research Grants Phillips Healthcare, GE Healthcare Jeffrey Maki No No Yes Research Grants Bracco Elizabeth McFarland No No Yes Speakers Bureau Bard Biopsy Systems Eric Tamm No No Yes Research Grants GE Healthcare Scott Reeder No No No Consultant for ArTara Therapeutics, and has ownership interests in Calimetrix, Reveal Pharmaceuticals Cellectar Biosciences, and Elucent Medical. The University of Wisconsin receives research support -

Siemens Healthineers Presentation
Q4 Analyst Call Siemens Healthineers AG Dr. Bernd Montag, CEO | Dr. Jochen Schmitz, CFO Nov 2, 2020 Q4 FY2020 Unrestricted © Siemens Healthineers AG, 2020 l 1 Frei verwendbar Safe Harbour Statement This presentation has been prepared solely for use at this meeting. This material is given in conjunction with an oral presentation and should not be taken out of context. By attending the meeting where this presentation is held or accessing this presentation, you agree to be bound by the following limitations. This presentation has been prepared for information purposes only and the information contained herein (unless otherwise indicated) has been provided by Siemens Healthineers AG. It does not constitute or form part of, and should not be construed as, an offer of, a solicitation of an offer to buy, or an invitation to subscribe for, underwrite or otherwise acquire, any securities of Siemens Healthineers AG or any existing or future member of the Siemens Healthineers Group (the “Group”) or Siemens AG, nor should it or any part of it form the basis of, or be relied on in connection with, any contract to purchase or subscribe for any securities of Siemens Healthineers AG, any member of the Group or Siemens AG or with any other contract or commitment whatsoever. This presentation does not constitute a prospectus in whole or in part, and any decision to invest in securities should be made solely on the basis of the information to be contained in a prospectus and on an independent analysis of the information contained therein. Any assumptions, views or opinions (including statements, projections, forecasts or other forward-looking statements) contained in this presentation represent the assumptions, views or opinions of Siemens Healthineers AG, unless otherwise indicated, as of the date indicated and are subject to change without notice. -

Joint Press Release
Joint Press release Siemens and Atos announce a five-year extension of their strategic partnership Atos to deliver digital, integrated and cybersecurity solutions to support Siemens digital strategic objectives Siemens-Atos Global Alliance will pursue joint go-to-market growth opportunities Munich, Germany - Paris, France – September 23, 2020 – Siemens AG and Atos, a global leader in digital transformation, today announced the extension of their Customer Relationship Agreement within their strategic partnership, started in 2011. The agreement aims to accelerate Siemens’ digital objectives in the areas of services modernization and digitalization, data driven digital, cloud transformation and cybersecurity. It comes in the context of 5-year total €3 billion agreements which were separately signed with Siemens AG, Siemens Energy AG and Siemens Healthineers AG and include existing services as well as new business. As part of the agreement, Atos will also invest in innovation and digital modernization, in order to advance important innovation topics for Siemens. “We are delighted to extend and strengthen our longtime partnership with Atos with this new framework partnership agreement to accelerate our transformation and support our digital strategic objectives”, said Hanna Hennig, Chief Information Officer at Siemens AG. “To support the different requirements of Siemens across all of its businesses, Atos will provide Siemens with best-in-class digital and integrated solutions such as Digital Workplace, Application modernization, full leverage of Atos new hybrid cloud platform, Digital Platforms and end-to-end Integration and Security. Atos will also deploy an innovative, data driven model enabling further leverage of Artificial Intelligence and Machine Learning,” said Eric Grall, Atos Chief Operating Officer. -

Siemens Railcom and Model Driven Architecture Success Story
Success Story: THE IT-ARCHITECTURE PROFESSIONALS Success Story: Siemens RailCom and Model Driven Architecture Siemens builds Product Line with MDA Siemens Transportation mation screens (CIS), closed-circuit TV End Customers Systems (CCTV) surveillance equipment, help- point intercom (HPI) emergency call The main customers of the RailCom Siemens Transportation Systems is a di- stations, supervisory control and data Manager are global and regional mass vision of Siemens AG, the world’s largest acquisition (SCADA), and related facili- transit operators, such as train and sub- manufacturer of electrical and electron- ties. way operators. The organization Siemens ic equipment. Siemens Transportation Transportation Systems Rail Commu- Systems has many years international nication supplies rail communication experience in building large-scale tran- RailCom Manager offers: projects of diverse complexities all over sit systems. the world, including success stories in Berlin, Hanover, the Netherlands, New • Real-time timetable information, con- York, Bangkok, Hong Kong and Malay- tinuously available to passengers RCM – RailCom Manager sia. These projects include passenger in- • Up-to-date information and entertain- formation systems, public address, clock Siemens RailCom Manager communica- ment in stations via electronic media systems, video surveillance, emergency tion management system is a standard call, telephony solutions, communica- • Readily accessible emergency tele- product, which provides access to all tion networks and SCADA – leveraging phones and information terminals information, communication and moni- the full bandwidth of the RailCom Manager toring systems via a single, integrated • Surveillance cameras in stations which functionality. user interface. The product integrates provide active protection of passengers public address (PA), customer infor- and property RCM is a Product Line Solution Siemens RailCom was facing a huge challenge when moving from offering a service towards the development of a standard product. -

Siemens Receives Follow-Up Order for H-Class Gas Turbines in Mexico Erlangen, 2016-Jan-13
Power and Gas Siemens receives follow-up order for H-class gas turbines in Mexico Erlangen, 2016-Jan-13 • Siemens to supply key components for Empalme II combined cycle plant • Six H-class gas turbines ordered by Mexico since spring 2015 • Siemens has received an order to supply two SGT6-8000H gas turbines and two SGen6-2000H generators for the Empalme II combined cycle power plant in Sonora, Mexico. The plant will have an installed electrical capacity of 791 megawatts (MW). The customer is a consortium consisting of the Spanish engineering and construction companies Duro Felguera and Elecnor and the Mexican subsidiary Elecnor Mexico. The operator of the plant will be the state-owned power provider Comisión Federal de Electricidad (CFE). Commercial operation is scheduled for April 2018. Additionally, Siemens will provide technical assistance during construction and commissioning of the plant. Since the spring of 2015, Siemens has received orders for six H-class gas turbines from Mexico. Since the spring of 2015, Siemens has received orders for six model SGT6-8000H gas turbines from Mexico. "CFE is becoming a pioneer in the integration of environmentally-compatible and resource-saving power generation solutions in Latin America. With these steps, Mexico will become an energy hub in the region and a reference for other similar projects", declared José Aparicio, Vice President of the Siemens Power and Gas Division for Latin America. A total of six model SGT6-8000H gas turbines are to be installed in the Empalme I (770 MW), Empalme II (791 MW) and Valle de México II (615 MW) combined cycle power plants. -

Atos and Siemens: a Win-Win Situation with Loadspring
CUSTOMER SUCCESS STORY Atos and Siemens: A Win-Win Situation with LoadSpring Atos is a European multinational IT company headquartered in France, with offices worldwide. They provide global IT support to Siemens. Siemens is a German multinational conglomerate company, with divisions in energy, “LoadSpring’s quick and easy hosting of healthcare, infrastructure, and manufacturing. The two companies are in a P6 has breathed new life into our planning self-described strategic alliance; Siemens recently purchased roughly 15% of group. The boost in performance we’ve Atos stock to reinforce the relationship. seen, combined with the worry-free upkeep of P6, has saved us time, money, CHALLENGES AND SOLUTIONS and frustration.” Jon Davis, Measurable Increase in Performance: Atos initially came to LoadSpring Business Manager for Siemens Gas and Power seeking help supporting Primavera P6 for Siemens. Project managers at Siemens Gas and Power were experiencing sluggish software performance. Once P6 was hosted on LoadSpring Cloud Platform, the PMs saw an immediate improvement in performance. Impressed by these reports, Siemens ran performance testing comparing LoadSpring Cloud Platform hosted P6 to its locally hosted version. LoadSpring’ hosted P6 averaged 10x faster than Siemens’ locally hosted version, based on a series of commonly performed tasks. This performance increase saved over an hour of wait time per user per week. At 17 staff-hour savings each week, the move to LoadSpring Cloud Platform paid for itself. The increase in project efficiency and reduction in frustration added even higher value to that equation. Feeding and Watering of P6: Another barrier to overcome was the day-to-day maintenance, upkeep, and administration of P6. -

Atos-Siemens PLM Software Alliance Partnership Brief
Siemens PLM Software Partnership Brief Atos For manufacturers in need of an end-to-end Proven PLM software execution sustainable product design process or cost excellence efficient application management services, Atos has been helping companies imple- the alliance of Atos and Siemens PLM ment Siemens PLM Software for more than Software brings together industry leading 17 years and can deploy more than 400 product lifecycle management (PLM) highly-experienced consultants who are software and implementation expertise experts in working with Siemens products coupled with extensive manufacturing and technology. The Atos-Siemens alliance expertise. The solutions and services pro- involves joint R&D activities designed to vided by the alliance help companies gain a provide your company with smarter imple- competitive edge by maximizing product mentation practices. portfolio profitability with smarter imple- Manufacturing industry DNA expertise mentations, expert management of com- Manufacturing industry expertise is in the plex manufacturing processes and seamless alliance’s DNA. Atos and Siemens have integration of business processes. helped leading manufacturers globally Business technologists powering PLM improve complex processes (design, devel- The Atos-Siemens PLM Software (Siemens) opment, launch and maintenance) for alliance enables your company to maximize product development. Drawing on 160 your return on your investment in PLM. years of manufacturing heritage and expe- Implementing PLM with the help of this alli- rience, the alliance provides an unequaled ance provides you with the ability to seam- breadth and depth of expertise that lever- lessly integrate business processes across ages both manufacturing and Siemens PLM the enterprise from strategy to execution. Software best practices. PLM can also help you optimize crucial pro- This makes it possible for manufacturers to: cesses, streamline supply chains, cut costs and waste and re-energize product devel- • Develop and evaluate multiple options opment. -

TONY PRENDATT Corporate Nov 11Th PC Format
TONY PRENDATT [email protected] / tonyprendatt.com /201*912*9773 A&R Executive - Producer – Audio Engineer, Editor & Mixer AWARDS 5X Grammy Award recipient, 11x Nominee Lauryn Hill, The Miseducation of Lauryn Hill, Sony Music Entertainment Album of the Year & Best R&B Album Carlos Santana, Supernatural, Arista/Sony-BMG Music Entertainment Album of the Year Mary J. Blige, “All That I Can Say” duet with Lauryn Hill, MCA Records Best R&B Duet The Original Kings of Comedy, Universal Music Group Best Comedy Album Cable Ace Award HBO – Gang Wars: Bangin’ in Little Rock Ampex Golden Reel Award x 2 Shaquille O’Neal – Shaq Fu: ‘Da Return, Jive Records RIAA gold, platinum & multi-platinum certifications 1984-2001 SKILLS Mac OS, iOS & Windows operating systems and maintenance Analog & Digital recording, editing & mix protocols Pro Tools, Adobe Premiere Pro CC, Final Cut Pro, PowerPoint, Excel, Word SSL & Neve analog mix technology, Avid/Euphonics System5 & 5B digital mix technology Dolby Surround 5.1, 7.1 and Atmos 9.1 mix platforms, video production & post edit supervision A&R EXECUTIVE Siemens Corporation / Polygram Worldwide Distribution / Mercury-Polydor Records Vice President A&R Black Music Talent acquisition, development, album and/or single production, song and producer solicitation, marketing-sales- promotion strategies and implementation of same. Budget management (departmental and record production). Hiring and supervision of East and West Coast A&R executives and support staff personnel. Extensive hands on record, remix and mastering work and establishment of continuing studio relationships across the country. Active artist roster of 43 acts encompassing 36 single and album releases per year. -
William Siemens Was a Member of the Founding Generation of the Siemens Company
Sir William Siemens LIFELINES William Siemens was a member of the founding generation of the Siemens company. Born in Germany in , he emigrated to England, where he headed the Siemens offi ce in London, and also worked as an independent engineer and entrepreneur. His work embraced fi elds as diverse as the global telegraph system and innovations in metallurgy; his name is associated with the Siemens-Martin process, which remained the world’s most important steel production process for a century. William Siemens’ achievements earned him esteem as a member of the British scientifi c community, and a great many honors and accolades. The brochure is the eighth volume in the LIFELINES series, which presents portraits of individuals who have shaped the history and development of Siemens in a wide variety of ways. This includes entrepreneurs who have led the company and members of the Managing Board as well as engineers, inventors, and creative thinkers. Sir William Siemens 2 Sir William Siemens April , – November , LIFELINES Gibt es das Bild als Scan? Ist aus Buch fotografiert, dabei verzerrt und unscharf! Sir William Siemens, ca. 1860 Introduction – An engineer with plans of his own Siemens & Halske was founded in the mid-19th century, the era of Germany’s early industrialization. This was a time when German industry endeavored to get industrialization underway at home and catch up to the British model. This was most successful in technologies that were new at the time, like electrical telegraphy. In any event, the innovations in telegraphy produced by the com- pany that Werner von Siemens founded in 1847 were without doubt on the same level as those of the British. -
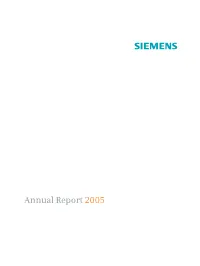
Annual Report 2005 Key Figures
s Annual Report 2005 Key figures in millions of euros 2005 (1) 2004 (1) New orders(2) 83,791 75,789 Sales(2) 75,445 70,237 Income from continuing operations 3,058 3,450 Loss from discontinued operations, net of income taxes (810) (45) Net income 2,248 3,405 Net cash from operating and investing activities(2) (1,489) 3,015 therein: Net cash provided by operating activities 4,217 4,704 Net cash used in investing activities (5,706) (1,689) Supplemental contributions to pension trusts (included in net cash provided by (used in) operating activities) (1,496) (1,255) Net proceeds from the sale of Infineon shares (included in net cash provided by (used in) investing activities) – 1,794 Research and development expenses(2) 5,155 4,650 Shareholders’ equity (September 30) 27,117 26,855 Employees(2) (September 30, in thousands) 461 424 (1) Fiscal year from October 1 to September 30 (2) Continuing operations (excluding the discontinued mobile devices activities) Contents Letter to our Shareholders 6 Managing Board 12 Fit4More Performance and Portfolio 14 Operational Excellence 18 People Excellence 22 Corporate Responsibility 26 Group Presidents 30 Business Areas 32 Megatrends 48 Report of the Supervisory Board 64 Corporate Governance Report 72 Compensation Report 78 Information for shareholders* 88 Management’s discussion and analysis 90 Consolidated Financial Statements 136 Statement of the Managing Board 214 Independent auditors’ report 215 Supervisory Board 220 Managing Board 222 Siemens financial calendar 228 Corporate Structure** * With separate