Frame Relay Analysis and Emulation
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Data Communication and Computer Network Unit 1
Department of Collegiate Education GOVERNMENT FIRST GRADE COLLEGE RAIBAG-591317 Department of Computer Science Lecture Notes SUBJECT : DATA COMMUNICATIONS AND COMPUTER NETWORKS SUBJECT CODE : 17BScCST61 CLASS : BSC VI Sem Paper-1 Subject In charge Smt Bhagirathi Halalli Assistant Professor 2019-20 Data Communication and Computer Network Unit 1 Unit 1: Introduction Content: 1.1. Data communications, 1.2. Networks, 1.3. The internet, 1.4. Protocols and standards, 1.5. Network models – OSI model, 1.6. TCP/IP protocol suite, 1.7. Addressing. 1.1.Data Communications, Data refers to the raw facts that are collected while information refers to processed data that enables us to take decisions. Ex. When result of a particular test is declared it contains data of all students, when you find the marks you have scored you have the information that lets you know whether you have passed or failed. The word data refers to any information which is presented in a form that is agreed and accepted upon by is creators and users. Data Communication Data Communication is a process of exchanging data or information In case of computer networks this exchange is done between two devices over a transmission medium. This process involves a communication system which is made up of hardware and software. The hardware part involves the sender and receiver devices and the intermediate devices through which the data passes. The software part involves certain rules which specify what is to be communicated, how it is to be communicated and when. It is also called as a Protocol. The following sections describe the fundamental characteristics that are important for the effective working of data communication process and are followed by the components that make up a data communications system. -
The OSI Model
Data Encapsulation & OSI & TCP/IP Models Week 2 Lecturer: Lucy White [email protected] Office : 324 1 Network Protocols • A protocol is a formal description of a set of rules and conventions that govern a particular aspect of how devices on a network communicate. Protocols determine the format, timing, sequencing, flow control and error control in data communication. Without protocols, the computer cannot make or rebuild the stream of incoming bits from another computer into the original format. • Protocols control all aspects of data communication, which include the following: - How the physical network is built - How computers connect to the network - How the data is formatted for transmission - The setting up and termination of data transfer sessions - How that data is sent - How to deal with errors 2 Protocol Suites & Industry Standard • Many of the protocols that comprise a protocol suite reference other widely utilized protocols or industry standards • Institute of Electrical and Electronics Engineers (IEEE) or the Internet Engineering Task Force (IETF) • The use of standards in developing and implementing protocols ensures that products from different manufacturers can work together for efficient communications 3 Function of Protocol in Network Communication A standard is a process or protocol that has been endorsed by the networking industry and ratified by a standards organization 4 Protocol Suites TCP/IP Protocol Suite and Communication Function of Protocol in Network Communication 6 Function of Protocol in Network Communication • Technology independent Protocols -Many diverse types of devices can communicate using the same sets of protocols. This is because protocols specify network functionality, not the underlying technology to support this functionality. -

Logical Link Control and Channel Scheduling for Multichannel Underwater Sensor Networks
ICST Transactions on Mobile Communications and Applications Research Article Logical Link Control and Channel Scheduling for Multichannel Underwater Sensor Networks Jun Li ∗, Mylene` Toulgoat, Yifeng Zhou, and Louise Lamont Communications Research Centre Canada, 3701 Carling Avenue, Ottawa, ON. K2H 8S2 Canada Abstract With recent developments in terrestrial wireless networks and advances in acoustic communications, multichannel technologies have been proposed to be used in underwater networks to increase data transmission rate over bandwidth-limited underwater channels. Due to high bit error rates in underwater networks, an efficient error control technique is critical in the logical link control (LLC) sublayer to establish reliable data communications over intrinsically unreliable underwater channels. In this paper, we propose a novel protocol stack architecture featuring cross-layer design of LLC sublayer and more efficient packet- to-channel scheduling for multichannel underwater sensor networks. In the proposed stack architecture, a selective-repeat automatic repeat request (SR-ARQ) based error control protocol is combined with a dynamic channel scheduling policy at the LLC sublayer. The dynamic channel scheduling policy uses the channel state information provided via cross-layer design. It is demonstrated that the proposed protocol stack architecture leads to more efficient transmission of multiple packets over parallel channels. Simulation studies are conducted to evaluate the packet delay performance of the proposed cross-layer protocol stack architecture with two different scheduling policies: the proposed dynamic channel scheduling and a static channel scheduling. Simulation results show that the dynamic channel scheduling used in the cross-layer protocol stack outperforms the static channel scheduling. It is observed that, when the dynamic channel scheduling is used, the number of parallel channels has only an insignificant impact on the average packet delay. -

Data Networks
Second Ed ition Data Networks DIMITRI BERTSEKAS Massachusetts Institute of Technology ROBERT GALLAGER Massachusetts Institute ofTechnology PRENTICE HALL, Englewood Cliffs, New Jersey 07632 2 Node A Node B Time at B --------- Packet 0 Point-to-Point Protocols and Links 2.1 INTRODUCTION This chapter first provides an introduction to the physical communication links that constitute the building blocks of data networks. The major focus of the chapter is then data link control (i.e., the point-to-point protocols needed to control the passage of data over a communication link). Finally, a number of point-to-point protocols at the network, transport, and physical layers are discussed. There are many similarities between the point-to-point protocols at these different layers, and it is desirable to discuss them together before addressing the more complex network-wide protocols for routing, flow control, and multiaccess control. The treatment of physical links in Section 2.2 is a brief introduction to a very large topic. The reason for the brevity is not that the subject lacks importance or inherent interest, but rather, that a thorough understanding requires a background in linear system theory, random processes, and modem communication theory. In this section we pro vide a sufficient overview for those lacking this background and provide a review and perspective for those with more background. 37 38 Point-to-Point Protocols and Links Chap. 2 In dealing with the physical layer in Section 2.2, we discuss both the actual com munication channels used by the network and whatever interface modules are required at the ends of the channels to transmit and receive digital data (see Fig 2.1). -
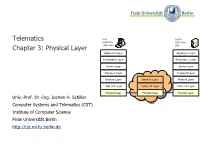
Telematics Chapter 3: Physical Layer
Telematics User Server watching with video Chapter 3: Physical Layer video clip clips Application Layer Application Layer Presentation Layer Presentation Layer Session Layer Session Layer Transport Layer Transport Layer Network Layer Network Layer Network Layer Data Link Layer Data Link Layer Data Link Layer Physical Layer Physical Layer Physical Layer Univ.-Prof. Dr.-Ing. Jochen H. Schiller Computer Systems and Telematics (CST) Institute of Computer Science Freie Universität Berlin http://cst.mi.fu-berlin.de Contents ● Design Issues ● Theoretical Basis for Data Communication ● Analog Data and Digital Signals ● Data Encoding ● Transmission Media ● Guided Transmission Media ● Wireless Transmission (see Mobile Communications) ● The Last Mile Problem ● Multiplexing ● Integrated Services Digital Network (ISDN) ● Digital Subscriber Line (DSL) ● Mobile Telephone System Univ.-Prof. Dr.-Ing. Jochen H. Schiller ▪ cst.mi.fu-berlin.de ▪ Telematics ▪ Chapter 3: Physical Layer 3.2 Design Issues Univ.-Prof. Dr.-Ing. Jochen H. Schiller ▪ cst.mi.fu-berlin.de ▪ Telematics ▪ Chapter 3: Physical Layer 3.3 Design Issues ● Connection parameters ● mechanical OSI Reference Model ● electric and electronic Application Layer ● functional and procedural Presentation Layer ● More detailed ● Physical transmission medium (copper cable, Session Layer optical fiber, radio, ...) ● Pin usage in network connectors Transport Layer ● Representation of raw bits (code, voltage,…) Network Layer ● Data rate ● Control of bit flow: Data Link Layer ● serial or parallel transmission of bits Physical Layer ● synchronous or asynchronous transmission ● simplex, half-duplex, or full-duplex transmission mode Univ.-Prof. Dr.-Ing. Jochen H. Schiller ▪ cst.mi.fu-berlin.de ▪ Telematics ▪ Chapter 3: Physical Layer 3.4 Design Issues Transmitter Receiver Source Transmission System Destination NIC NIC Input Abcdef djasdja dak jd ashda kshd akjsd asdkjhasjd as kdjh askjda Univ.-Prof. -
Radio Communications in the Digital Age
Radio Communications In the Digital Age Volume 1 HF TECHNOLOGY Edition 2 First Edition: September 1996 Second Edition: October 2005 © Harris Corporation 2005 All rights reserved Library of Congress Catalog Card Number: 96-94476 Harris Corporation, RF Communications Division Radio Communications in the Digital Age Volume One: HF Technology, Edition 2 Printed in USA © 10/05 R.O. 10K B1006A All Harris RF Communications products and systems included herein are registered trademarks of the Harris Corporation. TABLE OF CONTENTS INTRODUCTION...............................................................................1 CHAPTER 1 PRINCIPLES OF RADIO COMMUNICATIONS .....................................6 CHAPTER 2 THE IONOSPHERE AND HF RADIO PROPAGATION..........................16 CHAPTER 3 ELEMENTS IN AN HF RADIO ..........................................................24 CHAPTER 4 NOISE AND INTERFERENCE............................................................36 CHAPTER 5 HF MODEMS .................................................................................40 CHAPTER 6 AUTOMATIC LINK ESTABLISHMENT (ALE) TECHNOLOGY...............48 CHAPTER 7 DIGITAL VOICE ..............................................................................55 CHAPTER 8 DATA SYSTEMS .............................................................................59 CHAPTER 9 SECURING COMMUNICATIONS.....................................................71 CHAPTER 10 FUTURE DIRECTIONS .....................................................................77 APPENDIX A STANDARDS -

Android and Wireless Data-Extraction Using Wi-Fi
Android and Wireless data-extraction using Wi-Fi Bert Busstra N-A. Le-Khac, M-Tahar Kechadi School of Computer Science & Informatics School of Computer Science & Informatics University College Dublin University College Dublin Dublin 4, Ireland Dublin 4, Ireland [email protected] {an.lekhac, tahar.kechadi}@ucd.ie Abstract—Today, mobile phones are very popular, fast growing To investigate a mobile device an investigator needs to technology. Mobile phones of the present day are more and more interact with the device directly. The examiner must be like small computers. The so-called "smartphones" contain a sufficiently trained to examine the device. He has to think wealth of information each. This information has been proven to before he acts, because he must know exactly what effects his be very useful in crime investigations, because relevant evidence actions have on the data, and he must be prepared to prove it. If can be found in data retrieved from mobile phones used by criminals. In traditional methods, the data from mobile phones the examiner did change the data, he must be prepared to can be extracted using an USB-cable. However, for some reason explain why it was necessary and what data has changed. For this USB-cable connection cannot be made, the data should be this reason the examiner should document every action taken. extracted in an alternative way. In this paper, we study the In a traditional way, the data from mobile devices can be possibility of extracting data from mobile devices using a Wi-Fi extracted using an USB-cable. -

Sharing a Common Medium: Media Access Protocols
MIT 6.02 DRAFT Lecture Notes Fall 2010 (Last update: October 18, 2010) Comments, questions or bug reports? Please contact [email protected] LECTURE 10 Sharing a Common Medium: Media Access Protocols These are the lecture notes for Lectures 10 and 11 in Fall 2010. In this course so far, we have studied various techniques to develop a point-to-point link between two nodes communicating over a channel. The link includes techniques to: synchronize the receiver with the sender; ensure that there are enough transitions between voltage levels (e.g., using 8b/10b encoding); to cope with inter-symbol interference and noise; and to use channel coding to correct and detect bit errors. There are many communication channels, notably radio (wireless) and certain kinds of wired links (coaxial cables), where multiple nodes can all be connected and hear each other’s transmissions (either perfectly or to varying degrees). The next few lectures ad- dress the fundamental question of how such a common communication channel—also called a shared medium—can be shared between the different nodes. We will study two fundamental ways of sharing a medium: time sharing and frequency sharing. The idea in time sharing is to have the nodes coordinate with each other to divide up the access to the medium one at a time, in some fashion. The idea in frequency sharing is to divide up the frequency range available between the different transmitting nodes in a way that there is little or no interference between concurrently transmitting nodes. This lecture and the next one focus on approaches to time sharing. -

Data Communication
Data Communication: • Exchanging data over some transmission medium. • Four important characteristics: 1) Data delivery safe and accurate to the correct destination 2) Timeliness: On time delivery without “jittering”(variation in arrival time) especially for audio and video data. Major components of DC: Figure 1.1 Five components of data communication 1.3 1) Message: Information to be communicated: text, numbers, pictures, audio, video. 2) Senders: devices that transmits the data messages: computers, telephones, TV stations, cameras, etc. 3) Receivers: devices that receives the data messages: computers, telephones, TV sets, etc. 4) Transmission medium: Physical links that carries the communicated data, TP, coaxial, fibers, radio waves, etc 5) Protocol for DC: Set of rules that govern DC, syntax and semantics. Data are text, Numbers, Images, Audio, and video. Data Flow: Figure 1.2 Data flow (simplex, half-duplex, and full-duplex) 1.4 Data flow between communication devices as follows: a) Simplex (one way only). b) Half Duplex (H/D) (Bidirectional on one links). c) Full Duplex (F/D) (Bidirectional on two links). Networks: Set of nodes connected via physical links for the purpose of: 1) Distributing Processing: dividing a large task over a network of computers. 2) Sharing Data vs. centralization: shared access of data-banks (and other resources) among network of computers. 3) Security and robustness: distributed computers approach is for more security and reliability/dependability. Network Criteria: 1) Performance Response time -- user level inquiry/response speed, function of network size, links' (medium) quality, and relays' hardware and protocols. At a lower level, factors: packets' throughput (number of successful delivered packet per unit time) and delay (source- destination delay encountered by a packet travelling through the network-- typically dynamic, i.e., varying with time) are also used to measure networks performance. -

Medium Access Control Layer
Telematics Chapter 5: Medium Access Control Sublayer User Server watching with video Beispielbildvideo clip clips Application Layer Application Layer Presentation Layer Presentation Layer Session Layer Session Layer Transport Layer Transport Layer Network Layer Network Layer Network Layer Univ.-Prof. Dr.-Ing. Jochen H. Schiller Data Link Layer Data Link Layer Data Link Layer Computer Systems and Telematics (CST) Physical Layer Physical Layer Physical Layer Institute of Computer Science Freie Universität Berlin http://cst.mi.fu-berlin.de Contents ● Design Issues ● Metropolitan Area Networks ● Network Topologies (MAN) ● The Channel Allocation Problem ● Wide Area Networks (WAN) ● Multiple Access Protocols ● Frame Relay (historical) ● Ethernet ● ATM ● IEEE 802.2 – Logical Link Control ● SDH ● Token Bus (historical) ● Network Infrastructure ● Token Ring (historical) ● Virtual LANs ● Fiber Distributed Data Interface ● Structured Cabling Univ.-Prof. Dr.-Ing. Jochen H. Schiller ▪ cst.mi.fu-berlin.de ▪ Telematics ▪ Chapter 5: Medium Access Control Sublayer 5.2 Design Issues Univ.-Prof. Dr.-Ing. Jochen H. Schiller ▪ cst.mi.fu-berlin.de ▪ Telematics ▪ Chapter 5: Medium Access Control Sublayer 5.3 Design Issues ● Two kinds of connections in networks ● Point-to-point connections OSI Reference Model ● Broadcast (Multi-access channel, Application Layer Random access channel) Presentation Layer ● In a network with broadcast Session Layer connections ● Who gets the channel? Transport Layer Network Layer ● Protocols used to determine who gets next access to the channel Data Link Layer ● Medium Access Control (MAC) sublayer Physical Layer Univ.-Prof. Dr.-Ing. Jochen H. Schiller ▪ cst.mi.fu-berlin.de ▪ Telematics ▪ Chapter 5: Medium Access Control Sublayer 5.4 Network Types for the Local Range ● LLC layer: uniform interface and same frame format to upper layers ● MAC layer: defines medium access .. -

Communications Programming Concepts
AIX Version 7.1 Communications Programming Concepts IBM Note Before using this information and the product it supports, read the information in “Notices” on page 323 . This edition applies to AIX Version 7.1 and to all subsequent releases and modifications until otherwise indicated in new editions. © Copyright International Business Machines Corporation 2010, 2014. US Government Users Restricted Rights – Use, duplication or disclosure restricted by GSA ADP Schedule Contract with IBM Corp. Contents About this document............................................................................................vii How to use this document..........................................................................................................................vii Highlighting.................................................................................................................................................vii Case-sensitivity in AIX................................................................................................................................vii ISO 9000.....................................................................................................................................................vii Communication Programming Concepts................................................................. 1 Data Link Control..........................................................................................................................................1 Generic Data Link Control Environment Overview............................................................................... -

DATA COMMUNICATION and NETWORKING Software Department – Fourth Class
DATA COMMUNICATION AND NETWORKING Software Department – Fourth Class Network Models I Dr. Raaid Alubady - Lecture 2 Introduction A network is a combination of hardware and software that sends data from one location to another. The hardware consists of the physical equipment that carries signals from one point of the network to another. The software consists of instruction sets that make possible the services that we expect from a network. Layered Tasks We use the concept of layers in our daily life. As an example, let us consider two friends who communicate through postal mail the process of sending a letter to a friend would be complex if there were no services available from the post office. Figure 1 shows the steps in this task. Figure 1. Tasks involved in sending a letter At the Sender Site Let us first describe, in order, the activities that take place at the sender site. Higher layer. The sender writes the letter, inserts the letter in an envelope, writes the sender and receiver addresses, and drops the letter in a mailbox. Middle layer. The letter is picked up by a letter carrier and delivered to the post office. Lower layer. The letter is sorted at the post office; a carrier transports the letter. At the Receiver Site Lower layer. The carrier transports the letter to the post office. Middle layer. The letter is sorted and delivered to the recipient's mailbox. Higher layer. The receiver picks up the letter, opens the envelope, and reads it. Hierarchy: According to our analysis, there are three different activities at the sender site and another three activities at the receiver site.