Securing the Border Gateway Protocol by Stephen T
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Understanding the Impact of Network Infrastructure Changes Using Large-Scale Measurement Platforms
Understanding the Impact of Network Infrastructure Changes using Large-Scale Measurement Platforms Vaibhav Bajpai Understanding the Impact of Network Infrastructure Changes using Large-Scale Measurement Platforms by Vaibhav Bajpai A thesis submitted in partial fulfillment of the requirements for the degree of Doctor of Philosophy in Computer Science Dissertation Committee: Prof. Dr. Jürgen Schönwälder Jacobs University Bremen, Germany Dr. Kinga Lipskoch Jacobs University Bremen, Germany Prof. Dr. Filip De Turck University of Ghent, Belgium Date of Defense: May 30, 2016 DECLARATION I, hereby declare that I have written this PhD thesis independently, unless where clearly stated otherwise. I have used only the sources, the data and the support that I have clearly mentioned. This PhD thesis has not been submitted for conferral of degree elsewhere. I confirm that no rights of third parties will be infringed by the publication of this thesis. Bremen, Germany, May 30, 2016 Vaibhav Bajpai This thesis is dedicated to my mom for her love, endless support and encouragement ACKNOWLEDGMENTS I would like to express my gratitude to my supervisor Jürgen Schönwälder for providing me constant feedback and support throughout the entire duration of my doctoral research. I would also like to thank my thesis committee consisting of Jürgen Schönwälder, Kinga Lipskoch and Filip De Turck for guiding and supporting my doctoral research. I am grateful to my co-authors: Steffie Jacob Eravuchira, Saba Ahsan, Radek Krejˇcí,Jörg Ott and Jürgen Schönwälder with whom I learned to be a productive collaborator. Special thanks to: Sam Crawford, Philip Eardley, Trevor Burbridge, Arthur Berger, Daniel Karrenberg, Robert Kisteleki, Al Morton, Frank Bulk, Dan Wing and Andrew Yourtchenko for providing valuable and constructive feedback for improving my manuscripts. -

The Internet Development Process Stockholm October 2010
The Internet development Process Stockholm October 2010 Pål Spilling What I would talk about? • The main Norwegian contributions • Competitions between alternatives • Did Norway benefit from its participation? • Some observations and reflections • Conclusion A historical timeline 1981/82 TCP/IP accepted standard for US 1993 Web browser Mosaic Defence became available 1980 TCP/IP fully 2000 developed 1975 Start of the Internet Project; 1974 Preliminary specificaons of TCP 1977 First 3 – network Demonstration Mid 1973 ARPANET covers US, Hawaii, FFI Kjeller, and UCL London 1950 1955 ‐1960, End 1968 Ideas of resource Start of the ARPANET sharing networks project Norway and UK on ARPANET 1973 London o SATNET o Kjeller Norwegian Contributions • SATNET development – Simulations – Performance measurements • Internet performance measurements • Packet speech experiments over the Internet • Improved PRNET protocol architecture Competitions between alternatives • X.25 (ITU) • ISO standards (committee work) • DECNET (proprietary) • IBM (proprietary) • TCP/IP demonstrated its usefullness i 1977 accepted as a standard for US defence Norwegian benefits • Enabled me to create a small Norwegian internet • Got access to UNIX, with TCP/IP and user services integrated • Gave research scientists early exposure to internet and its services • Early curriculum in computer communications; Oslo University Observations and reflections • Norwegian Arpanet Committee; dissolved itself due to lack of interest • IP address space too small for todays use • TCP split in -

Check Detailed Interview In
Interviewee: Shigeki Goto Interviewer: Fan Yuanyuan Date: April 13th, 2018 Location: Cyberlabs, Beijing Transcriber: Hong Wei 1:34 FYY: Ok, so let's begin. But today is thirteenth of April, 2018.We’re in office of cyber labs in Beijing and we feel so honored to be able to interview doctor Shigeki Goto here? Am pronouncing it right? (Yes). I’ll briefly introduce the history of Internet project to you. The project is launched in …… It's launched in 2007 to celebrate the first fifty years of the Internet by recording and preserving the personal narratives of global Internet pioneers, uh, their extraordinary contributions to the Internet development. And by 2018, we should have interviewed 500 Internet pioneers, as we planned, and by now is interviewed more than 170 pioneers around the world and about 80 are from overseas of China, and let’s start from the very beginning of you like, uh, your name, where and when were you born and what did your parents do, when you were young? SG: I was born in Utsunomiya city that is near Nikko, Tochigi Prefecture in Japan. Both of my parents basically were school teachers and my father spent most of his life at the unified school district. He was a school teacher. He worked for the administrative structure of the school system. It covers from elementary school, middle school, and high school if they are public. FYY: So that's a big school covered all three… SG: Yes. All the regional public schools are under control of the unified school district. -
BALG: Bypassing Application Layer Gateways Using Multi-Staged Encrypted Shellcodes
Sebastian Roschke, Feng Cheng, Christoph Meinel: "BALG: Bypassing Application Layer Gateways Using Multi-Staged Encrypted Shellcodes" in Proceedings of the 12th IFIP/IEEE International Symposium on Integrated Network Management (IM 2011), IEEE Press, Dublin, Ireland, pp. 399-406, 5, 2011. ISBN: 978-1-4244-9219-0. BALG: Bypassing Application Layer Gateways Using Multi-Staged Encrypted Shellcodes Sebastian Roschke Feng Cheng Christoph Meinel Hasso Plattner Institute (HPI) Hasso Plattner Institute (HPI) Hasso Plattner Institute (HPI) University of Potsdam University of Potsdam University of Potsdam 14482, Potsdam, Germany 14482, Potsdam, Germany 14482, Potsdam, Germany Email: [email protected] Email: [email protected] Email: [email protected] Abstract—Modern attacks are using sophisticated and inno- easily penetrated by simple tunneling. IDS needs to handle vative techniques. The utilization of cryptography, self-modified efficient evasion techniques. ALGs provide more restrictions code, and integrated attack frameworks provide more possibili- for network access by combining filtering on the application ties to circumvent most existing perimeter security approaches, such as firewalls and IDS. Even Application Layer Gateways layer and IDS techniques, such as deep packet inspection. (ALG) which enforce the most restrictive network access can be Most of ALG implementations provide filtering due to ap- exploited by using advanced attack techniques. In this paper, plication layer protocol compliance and even allow to block we propose a new attack for circumventing ALGs. By using certain commands within a specific protocol. Although ALGs polymorphic and encrypted shellcode, multiple shellcode stages, enforce a very restrictive access policy, it is still possible to protocol compliant and encrypted shell tunneling, and reverse channel discovery techniques, we are able to effectively bypass circumvent such devices by using modern attack techniques. -
VPN 3000 Series Concentrator Reference Volume II: Administration and Monitoring Release 3.6 August 2002
VPN 3000 Series Concentrator Reference Volume II: Administration and Monitoring Release 3.6 August 2002 Corporate Headquarters Cisco Systems, Inc. 170 West Tasman Drive San Jose, CA 95134-1706 USA http://www.cisco.com Tel: 408 526-4000 800 553-NETS (6387) Fax: 408 526-4100 Customer Order Number: DOC-7814742= Text Part Number: 78-14742-01 THE SPECIFICATIONS AND INFORMATION REGARDING THE PRODUCTS IN THIS MANUAL ARE SUBJECT TO CHANGE WITHOUT NOTICE. ALL STATEMENTS, INFORMATION, AND RECOMMENDATIONS IN THIS MANUAL ARE BELIEVED TO BE ACCURATE BUT ARE PRESENTED WITHOUT WARRANTY OF ANY KIND, EXPRESS OR IMPLIED. USERS MUST TAKE FULL RESPONSIBILITY FOR THEIR APPLICATION OF ANY PRODUCTS. THE SOFTWARE LICENSE AND LIMITED WARRANTY FOR THE ACCOMPANYING PRODUCT ARE SET FORTH IN THE INFORMATION PACKET THAT SHIPPED WITH THE PRODUCT AND ARE INCORPORATED HEREIN BY THIS REFERENCE. IF YOU ARE UNABLE TO LOCATE THE SOFTWARE LICENSE OR LIMITED WARRANTY, CONTACT YOUR CISCO REPRESENTATIVE FOR A COPY. The Cisco implementation of TCP header compression is an adaptation of a program developed by the University of California, Berkeley (UCB) as part of UCB’s public domain version of the UNIX operating system. All rights reserved. Copyright © 1981, Regents of the University of California. NOTWITHSTANDING ANY OTHER WARRANTY HEREIN, ALL DOCUMENT FILES AND SOFTWARE OF THESE SUPPLIERS ARE PROVIDED “AS IS” WITH ALL FAULTS. CISCO AND THE ABOVE-NAMED SUPPLIERS DISCLAIM ALL WARRANTIES, EXPRESSED OR IMPLIED, INCLUDING, WITHOUT LIMITATION, THOSE OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT OR ARISING FROM A COURSE OF DEALING, USAGE, OR TRADE PRACTICE. IN NO EVENT SHALL CISCO OR ITS SUPPLIERS BE LIABLE FOR ANY INDIRECT, SPECIAL, CONSEQUENTIAL, OR INCIDENTAL DAMAGES, INCLUDING, WITHOUT LIMITATION, LOST PROFITS OR LOSS OR DAMAGE TO DATA ARISING OUT OF THE USE OR INABILITY TO USE THIS MANUAL, EVEN IF CISCO OR ITS SUPPLIERS HAVE BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES. -
Configuring SSH and Telnet
Configuring SSH and Telnet This chapter describes how to configure Secure Shell Protocol (SSH) and Telnet on Cisco NX-OS devices. This chapter includes the following sections: • About SSH and Telnet, on page 1 • Licensing Requirements for SSH and Telnet, on page 3 • Prerequisites for SSH and Telnet, on page 3 • Guidelines and Limitations for SSH and Telnet, on page 3 • Default Settings for SSH and Telnet, on page 4 • Configuring SSH , on page 4 • Configuring Telnet, on page 15 • Verifying the SSH and Telnet Configuration, on page 17 • Configuration Example for SSH, on page 18 • Configuration Example for SSH Passwordless File Copy, on page 19 • Additional References for SSH and Telnet, on page 21 About SSH and Telnet This section includes information about SSH and Telnet. SSH Server You can use the SSH server to enable an SSH client to make a secure, encrypted connection to a Cisco NX-OS device. SSH uses strong encryption for authentication. The SSH server in the Cisco NX-OS software can interoperate with publicly and commercially available SSH clients. The user authentication mechanisms supported for SSH are RADIUS, TACACS+, LDAP, and the use of locally stored usernames and passwords. SSH Client The SSH client feature is an application that runs over the SSH protocol to provide device authentication and encryption. The SSH client enables a Cisco NX-OS device to make a secure, encrypted connection to another Cisco NX-OS device or to any other device that runs the SSH server. This connection provides an outbound Configuring SSH and Telnet 1 Configuring SSH and Telnet SSH Server Keys connection that is encrypted. -
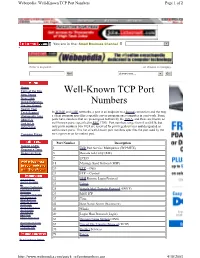
Well-Known TCP Port Numbers Page 1 of 2
Webopedia: Well-Known TCP Port Numbers Page 1 of 2 You are in the: Small Business Channel Jump to Website Enter a keyword... ...or choose a category. Go! choose one... Go! Home Term of the Day Well-Known TCP Port New Terms New Links Quick Reference Numbers Did You Know? Search Tool Tech Support In TCP/IP and UDP networks, a port is an endpoint to a logical connection and the way Webopedia Jobs a client program specifies a specific server program on a computer in a network. Some About Us ports have numbers that are preassigned to them by the IANA, and these are known as Link to Us well-known ports (specified in RFC 1700). Port numbers range from 0 to 65536, but Advertising only ports numbers 0 to 1024 are reserved for privileged services and designated as well-known ports. This list of well-known port numbers specifies the port used by the Compare Prices server process as its contact port. Port Number Description Submit a URL 1 TCP Port Service Multiplexer (TCPMUX) Request a Term Report an Error 5 Remote Job Entry (RJE) 7 ECHO 18 Message Send Protocol (MSP) 20 FTP -- Data 21 FTP -- Control Internet News 22 SSH Remote Login Protocol Internet Investing IT 23 Telnet Windows Technology Linux/Open Source 25 Simple Mail Transfer Protocol (SMTP) Developer Interactive Marketing 29 MSG ICP xSP Resources Small Business 37 Time Wireless Internet Downloads 42 Host Name Server (Nameserv) Internet Resources Internet Lists 43 WhoIs International EarthWeb 49 Login Host Protocol (Login) Career Resources 53 Domain Name System (DNS) Search internet.com Advertising -

Secured Connectivity Why It Matters and How to Protect Your Organization
Secured Connectivity Why it Matters and How to Protect Your Organization While every attempt has been made to ensure the accuracy and completeness of the information in this document, some typographical or technical errors may exist. Hummingbird Connectivity – a division of Open Text cannot accept responsibility for customers’ losses resulting from the use of this document. The information contained in this document is subject to change without notice. This document contains proprietary information that is protected by copyright. This document, in whole or in part, may not be photocopied, reproduced, or translated into another language without prior written consent from Hummingbird Connectivity. This edition published September 2008 www.hummingbird.com 2 Contents The Security Challenge 4 Security in Organizations 5 Driving Security 6 Structural Factors 6 External Factors 6 Connectivity — A Definition 7 Security Risks in a Connectivity World 8 Weak Authentication 8 Easy Protocol Decoding 8 Data Authenticity and Integrity Tampering 8 Solutions for Secured Connectivity 9 SSL 9 Kerberos 10 Secure Shell 11 ® Connectivity SecureTerm 12 ™ Connectivity Secure Shell 14 Connectivity Secure Server 16 Secure Replacement for Telnet and FTP 16 High Performance and Scalability 16 Glossary of Terms 18 www.hummingbird.com 3 The Security Challenge Security is the hot topic today. Although, companies have been slow to recognize the importance of security things have changed during the last decade. Security is a top priority and there are no indications that this will end any time soon. The costs of security (or lack thereof) have now been clearly identified, and the picture does not look very good. -

Adding Enhanced Services to the Internet: Lessons from History
Adding Enhanced Services to the Internet: Lessons from History kc claffy and David D. Clark [email protected] and [email protected] September 7, 2015 Contents 1 Introduction 3 2 Related technical concepts 4 2.1 What does “enhanced services” mean? . 4 2.2 Using enhanced services to mitigate congestion . 5 2.3 Quality of Service (QoS) vs. Quality of Experience (QoE) . 6 2.4 Limiting the use of enhanced services via regulation . 7 3 Early history of enhanced services: technology and operations (1980s) 7 3.1 Early 1980s: Initial specification of Type-of-Service in the Internet Protocol suite . 7 3.2 Mid 1980s: Reactive use of service differentation to mitigate NSFNET congestion . 10 3.3 Late 1980s: TCP protocol algorithmic support for dampening congestion . 10 4 Formalizing support for enhanced services across ISPs (1990s) 11 4.1 Proposed short-term solution: formalize use of IP Precedence field . 11 4.2 Proposed long-term solution: standardizing support for enhanced services . 12 4.3 Standardization of enhanced service in the IETF . 13 4.4 Revealing moments: the greater obstacle is economics not technology . 15 5 Non-technical barriers to enhanced services on the Internet (2000s) 15 5.1Early2000s:afuneralwakeforQoS............................ 15 5.2 Mid 2000s: Working with industry to gain insight . 16 5.3 Late 2000s: QoS becomes a public policy issue . 17 6 Evolving interconnection structure and implications for enhanced services (2010s) 20 6.1 Expansion of network interconnection scale and scope . 20 6.2 Emergence of private IP-based platforms to support enhanced services . 22 6.3 Advancing our empirical understanding of performance impairments . -

Features of the Internet History the Norwegian Contribution to the Development PAAL SPILLING and YNGVAR LUNDH
Features of the Internet history The Norwegian contribution to the development PAAL SPILLING AND YNGVAR LUNDH This article provides a short historical and personal view on the development of packet-switching, computer communications and Internet technology, from its inception around 1969 until the full- fledged Internet became operational in 1983. In the early 1990s, the internet backbone at that time, the National Science Foundation network – NSFNET, was opened up for commercial purposes. At that time there were already several operators providing commercial services outside the internet. This presentation is based on the authors’ participation during parts of the development and on literature Paal Spilling is studies. This provides a setting in which the Norwegian participation and contribution may be better professor at the understood. Department of informatics, Univ. of Oslo and University 1 Introduction Defense (DOD). It is uncertain when DoD really Graduate Center The concept of computer networking started in the standardized on the entire protocol suite built around at Kjeller early 1960s at the Massachusetts Institute of Technol- TCP/IP, since for several years they also followed the ogy (MIT) with the vision of an “On-line community ISO standards track. of people”. Computers should facilitate communica- tions between people and be a support for human The development of the Internet, as we know it today, decision processes. In 1961 an MIT PhD thesis by went through three phases. The first one was the Leonard Kleinrock introduced some of the earliest research and development phase, sponsored and theoretical results on queuing networks. Around the supervised by ARPA. Research groups that actively same time a series of Rand Corporation papers, contributed to the development process and many mainly authored by Paul Baran, sketched a hypotheti- who explored its potential for resource sharing were cal system for communication while under attack that permitted to connect to and use the network. -

NBAR2 Standard Protocol Pack 1.0
NBAR2 Standard Protocol Pack 1.0 Americas Headquarters Cisco Systems, Inc. 170 West Tasman Drive San Jose, CA 95134-1706 USA http://www.cisco.com Tel: 408 526-4000 800 553-NETS (6387) Fax: 408 527-0883 © 2013 Cisco Systems, Inc. All rights reserved. CONTENTS CHAPTER 1 Release Notes for NBAR2 Standard Protocol Pack 1.0 1 CHAPTER 2 BGP 3 BITTORRENT 6 CITRIX 7 DHCP 8 DIRECTCONNECT 9 DNS 10 EDONKEY 11 EGP 12 EIGRP 13 EXCHANGE 14 FASTTRACK 15 FINGER 16 FTP 17 GNUTELLA 18 GOPHER 19 GRE 20 H323 21 HTTP 22 ICMP 23 IMAP 24 IPINIP 25 IPV6-ICMP 26 IRC 27 KAZAA2 28 KERBEROS 29 L2TP 30 NBAR2 Standard Protocol Pack 1.0 iii Contents LDAP 31 MGCP 32 NETBIOS 33 NETSHOW 34 NFS 35 NNTP 36 NOTES 37 NTP 38 OSPF 39 POP3 40 PPTP 41 PRINTER 42 RIP 43 RTCP 44 RTP 45 RTSP 46 SAP 47 SECURE-FTP 48 SECURE-HTTP 49 SECURE-IMAP 50 SECURE-IRC 51 SECURE-LDAP 52 SECURE-NNTP 53 SECURE-POP3 54 SECURE-TELNET 55 SIP 56 SKINNY 57 SKYPE 58 SMTP 59 SNMP 60 SOCKS 61 SQLNET 62 SQLSERVER 63 SSH 64 STREAMWORK 65 NBAR2 Standard Protocol Pack 1.0 iv Contents SUNRPC 66 SYSLOG 67 TELNET 68 TFTP 69 VDOLIVE 70 WINMX 71 NBAR2 Standard Protocol Pack 1.0 v Contents NBAR2 Standard Protocol Pack 1.0 vi CHAPTER 1 Release Notes for NBAR2 Standard Protocol Pack 1.0 NBAR2 Standard Protocol Pack Overview The Network Based Application Recognition (NBAR2) Standard Protocol Pack 1.0 is provided as the base protocol pack with an unlicensed Cisco image on a device. -

Smith 1 CINE-GT 1807 Fall 2019 Madeline Smith December 13
Smith 1 CINE-GT 1807 Fall 2019 Madeline Smith December 13, 2019 Assignment 2: Final Research Paper The History of Web Archiving and the Evolution of Archive-It’s Brozzler Since the beginning of the Internet and the World Wide Web in 1991, an unimaginable amount of data and content has been created, shared, posted, and stored on the World Wide Web. When the World Wide Web began, there was no system in place to archive and preserve the Web content, as no one could imagine how massive the infrastructure would become. It was not until the 1990s that users began to recognize the gravity of archiving and preserving all the incredibly diverse born-digital data and content on the Web. Web crawlers are a key component in accomplishing the mission to archive Web content before it is lost for good. While there have been advancements in web archiving over the years, considering the speed at which digital technology and the varied uses of the Internet are changing, there is still work to be done. One of the more recent web crawling technologies is Archive-It’s Brozzler. This report aims to frame Brozzler within the larger landscape of web archiving and web crawler technology. The report will attempt to answer whether Brozzler as a web archiving tool is effective for capturing dynamic websites and the rapidly evolving content of the modern web. The end of this report will be an examination of my own experience attempting to use Brozzler. In order to understand web archiving and web crawling, a few terms used in describing the evolution of the Internet and the World Wide Web need to be defined.