Analysis of SSH Executables
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
A Story of an Embedded Linux Botnet
A Moose Once Bit My Honeypot A Story of an Embedded Linux Botnet by Olivier Bilodeau (@obilodeau) $ apropos Embedded Linux Malware Moose DNA (description) Moose Herding (the Operation) What’s New? Take Aways $ whoami Malware Researcher at ESET Infosec lecturer at ETS University in Montreal Previously infosec developer, network admin, linux system admin Co-founder Montrehack (hands-on security workshops) Founder NorthSec Hacker Jeopardy Embedded Linux Malware What marketing likes to call "Internet of Things Malware" Malware Running On An Embedded Linux System Like consumer routers DVR Smart TVs IP Camera monitoring systems … Caracteristics of Embedded Linux Systems Small amount of memory Small amount of flash Non x86 architectures: ARM, MIPS Wide-variety of libc implementations / versions Same ABI-compatible Linux kernel (2.4 < x < 4.3) Support ELF binaries Rarely an integrated UI Networked Why Threats On These Systems Matters? Hard to detect Hard to remediate Hard to fix Low hanging fruit for bad guys It’s Real Several cases disclosed in the last two years A lot of same-old background noise (DDoSer) Things are only getting worse Wait, is IoT malware really about things? NNoo.. NNoott yyeett.. So what kind of malware can we find on such insecure devices? Linux/Aidra Linux/Bassobo ChinaZ family (XOR.DDoS, …) Linux/Dofloo Linux/DNSAmp (Mr Black, BillGates) Linux/Gafgyt (LizardStresser) Linux/Hydra Linux/Tsunami … LLeessssoonn LLeeaarrnneedd ##00 Statically-linked stripped binaries Static/stripped ELF primer No imports (library calls) present -

Survivor: a Fine-Grained Intrusion Response and Recovery Approach for Commodity Operating Systems
Survivor: A Fine-Grained Intrusion Response and Recovery Approach for Commodity Operating Systems Ronny Chevalier David Plaquin HP Labs HP Labs CentraleSupélec, Inria, CNRS, IRISA [email protected] [email protected] Chris Dalton Guillaume Hiet HP Labs CentraleSupélec, Inria, CNRS, IRISA [email protected] [email protected] ABSTRACT 1 INTRODUCTION Despite the deployment of preventive security mechanisms to pro- Despite progress in preventive security mechanisms such as cryp- tect the assets and computing platforms of users, intrusions even- tography, secure coding practices, or network security, given time, tually occur. We propose a novel intrusion survivability approach an intrusion will eventually occur. Such a case may happen due to to withstand ongoing intrusions. Our approach relies on an orches- technical reasons (e.g., a misconfiguration, a system not updated, tration of fine-grained recovery and per-service responses (e.g., or an unknown vulnerability) and economic reasons [39] (e.g., do privileges removal). Such an approach may put the system into a the benefits of an intrusion for criminals outweigh their costs?). degraded mode. This degraded mode prevents attackers to reinfect To limit the damage done by security incidents, intrusion re- the system or to achieve their goals if they managed to reinfect covery systems help administrators restore a compromised system it. It maintains the availability of core functions while waiting for into a sane state. Common limitations are that they do not preserve patches to be deployed. We devised a cost-sensitive response se- availability [23, 27, 34] (e.g., they force a system shutdown) or that lection process to ensure that while the service is in a degraded they neither stop intrusions from reoccurring nor withstand re- mode, its core functions are still operating. -

Sureview® Memory Integrity Advanced Linux Memory Analysis Delivers Unparalleled Visibility and Verification
SureView® Memory Integrity Advanced Linux Memory Analysis Delivers Unparalleled Visibility and Verification Promoting trustworthy and repeatable analysis of volatile system state Benefits Increased Usage of Linux in Forensics Field Guide for Linux Global Enterprises Systems2,” the apparent goal n Enables visibility into the state n Scans thousands of The use of Linux is everywhere of these attackers is to steal all systems with hundreds of of systems software while in the world. Linux is used in types of information. Perhaps of gigabytes of memory executing in memory our stock exchange transactions, greatest concern are the synchro- on Linux systems n Provides a configurable social media, network storage nized, targeted attacks against n Delivers malware detection using scanning engine for automated devices, smartphones, DVR’s, Linux systems. For several years, scans of remote systems an integrity verification approach online purchasing web sites, organized groups of attackers to verify that all systems software throughout an enterprise running is known and unmodified and in the majority of global (a.k.a. threat actors) have been n Incorporates an easy-to- Internet traffic. The Linux infiltrating Linux systems and to quickly identify threats use GUI to quickly assess Foundation’s 2013 Enterprise have been communicating with n Allows the integration and interpret results End User Report indicates that command and control (C2) of memory forensics into n Delivers output in a structured 80% of respondents planned servers and exfiltrating data enterprise security information data format (JSON) to to increase their numbers of from compromised Linux sys- and event management facilitate analytics systems (SIEMS) supporting Linux servers over the next five tems. -

Malware Trends
NCCIC National Cybersecurity and Communications Integration Center Malware Trends Industrial Control Systems Emergency Response Team (ICS-CERT) Advanced Analytical Laboratory (AAL) October 2016 This product is provided subject only to the Notification Section as indicated here:http://www.us-cert.gov/privacy/ SUMMARY This white paper will explore the changes in malware throughout the past several years, with a focus on what the security industry is most likely to see today, how asset owners can harden existing networks against these attacks, and the expected direction of developments and targets in the com- ing years. ii CONTENTS SUMMARY .................................................................................................................................................ii ACRONYMS .............................................................................................................................................. iv 1.INTRODUCTION .................................................................................................................................... 1 1.1 State of the Battlefield ..................................................................................................................... 1 2.ATTACKER TACTIC CHANGES ........................................................................................................... 2 2.1 Malware as a Service ...................................................................................................................... 2 2.2 Destructive Malware ...................................................................................................................... -

Russian GRU 85Th Gtsss Deploys Previously Undisclosed Drovorub Malware
National Security Agency Federal Bureau of Investigation Cybersecurity Advisory Russian GRU 85th GTsSS Deploys Previously Undisclosed Drovorub Malware August 2020 Rev 1.0 U/OO/160679-20 PP-20-0714 Russian GRU 85th GTsSS Deploys Previously Undisclosed Drovorub Malware Notices and history Disclaimer of Warranties and Endorsement The information and opinions contained in this document are provided "as is" and without any warranties or guarantees. Reference herein to any specific commercial products, process, or service by trade name, trademark, manufacturer, or otherwise, does not necessarily constitute or imply its endorsement, recommendation, or favoring by the United States Government. This guidance shall not be used for advertising or product endorsement purposes. Sources and Methods NSA and FBI use a variety of sources, methods, and partnerships to acquire information about foreign cyber threats. This advisory contains the information NSA and FBI have concluded can be publicly released, consistent with the protection of sources and methods and the public interest. Publication Information Purpose This advisory was developed as a joint effort between NSA and FBI in support of each agency’s respective missions. The release of this advisory furthers NSA’s cybersecurity missions, including its responsibilities to identify and disseminate threats to National Security Systems, Department of Defense information systems, and the Defense Industrial Base, and to develop and issue cybersecurity specifications and mitigations. This information may be shared broadly to reach all appropriate stakeholders. Contact Information Client Requirements / General Cybersecurity Inquiries: Cybersecurity Requirements Center, 410-854-4200, [email protected] Media Inquiries / Press Desk: Media Relations, 443-634-0721, [email protected] Trademark Recognition Linux® is a registered trademark of Linus Torvalds. -
Linux Security Review 2015
Linux Security Review 2015 www.av-comparatives.org AV-Comparatives Linux Security Review Language: English May 2015 Last revision: 26 th May 2015 www.av-comparatives.org -1- Linux Security Review 2015 www.av-comparatives.org Contents Introduction ....................................................................................................................... 3 Reviewed products ............................................................................................................... 4 Malware for Linux systems ..................................................................................................... 5 Linux security advice ............................................................................................................ 6 Items covered in the review .................................................................................................. 7 Avast File Server Security ...................................................................................................... 8 AVG Free Edition for Linux.................................................................................................... 11 Bitdefender Antivirus Scanner for Unices ................................................................................ 13 Clam Antivirus for Linux ....................................................................................................... 17 Comodo Antivirus for Linux .................................................................................................. 20 Dr.Web Anti-virus for -
Unix/Mac/Linux OS Malware 10/15/2020
Unix/Mac/Linux OS Malware 10/15/2020 Report #: 202010151030 Agenda • Executive Summary • Origin of Modern Operating Systems • Overview of Operating Systems o Desktop o Servers o Super Computers o Mobile o Attack Surface and CVEs • Malware Case Studies o Drovorub o Hidden Wasp o Operation Windigo o MAC Malware Slides Key: • Defending Against Malware The picture can't be displayed. Non-Technical: Managerial, strategic and high- • Summary level (general audience) The picture can't be displayed. Technical: Tactical / IOCs; requiring in-depth knowledge (system admins, IRT) TLP: WHITE, ID# 202010151030 2 Executive Summary • Unix and Unix-like systems drive most of today's computer systems. • Vulnerabilities and malware • Threat mitigation o Comprehensive security policies o Access control o Regular updates and backups o Training employees o Improving posture and maturity TLP: WHITE, ID# 202010151030 3 Modern Operating Systems "Determining the operating system on which the server runs is the most important part of hacking. Mostly, hacking is breaking into the target's system to steal data or any such purpose. Hence, the security of the system becomes the thing of prime importance." Source: Parikh, K. (2020, August) The Hackers Library Functions of Operating Systems Timeline of the Origins of Operating Systems TLP: WHITE, ID# 202010151030 4 Overview of Operating Systems (Non-Mobile) Unix Chrome OS •Derived from Original AT&T Unix •Free and open-source •Command-line input •Graphical user interface •Very popular among scientific, •Based on Linux -
What Is Linux?
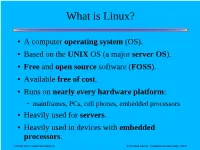
What is Linux? ● A computer operating system (OS). ● Based on the UNIX OS (a major server OS). ● Free and open source software (FOSS). ● Available free of cost. ● Runs on nearly every hardware platform: – mainframes, PCs, cell phones, embedded processors ● Heavily used for servers. ● Heavily used in devices with embedded processors. CS Day 2013: Linux Introduction © Norman Carver Computer Science Dept. SIUC Linux?? ● “But I have never heard of Linux, so it must not be very commonly used.” ● “Nobody uses Linux.” ● “Everyone runs Windows.” ● “Linux is too hard for anyone but computer scientists to use.” ● “There's no malware for Linux because Linux is so unimportant.” CS Day 2013: Linux Introduction © Norman Carver Computer Science Dept. SIUC Have You Used Linux? ● Desktop OS? – many distributions: Ubuntu, Red Hat, etc. CS Day 2013: Linux Introduction © Norman Carver Computer Science Dept. SIUC Have You Used Linux? ● Desktop OS? – many distributions: Ubuntu, Red Hat, etc. CS Day 2013: Linux Introduction © Norman Carver Computer Science Dept. SIUC Have You Used Linux? ● Cell phones or tablets or netbooks? – Android and Chrome OS are Linux based CS Day 2013: Linux Introduction © Norman Carver Computer Science Dept. SIUC Have You Used Linux? ● Routers? – many routers and other network devices run Linux – projects like DD-WRT are based on Linux CS Day 2013: Linux Introduction © Norman Carver Computer Science Dept. SIUC Have You Used Linux? ● NAS (Network Attached Storage) devices? – most run Linux CS Day 2013: Linux Introduction © Norman Carver Computer Science Dept. SIUC Have You Used Linux? ● Multimedia devices? – many run Linux CS Day 2013: Linux Introduction © Norman Carver Computer Science Dept. -
Leveraging Advanced Linux Debugging Techniques for Malware Hunting
Beyond Whitelisting: Fileless Attacks Against Linux Shlomi Boutnaru ./whomai • Currently: − CTO & Co-Founder, Rezilion • Previous: − Chief Technologist Cybersecurity, PayPal − CTO & Co-Founder, CyActive − Acquired by PayPal (2015) Fileless Malware - Definition “… a variant of computer related malicious software that exists exclusively as a computer memory-based artifact i.e. in RAM. It does not write any part of its activity to the computer's hard drive meaning that it's very resistant to existing Anti-computer forensic strategies that incorporate file-based whitelisting, signature detection, hardware verification, pattern-analysis, time-stamping, etc., and leaves very little by way of evidence that could be used by digital forensic investigators to identify illegitimate activity. As malware of this type is designed to work in-memory, its longevity on the system exists only until the system is rebooted…” https://en.wikipedia.org/wiki/Fileless_malware In the News… https://www.techradar.com/news/why-fileless-malware-is-the-biggest-new-threat-to-your-business https://securelist.com/fileless-attacks-against-enterprise-networks/77403/ https://threatpost.com/threatlist-ransomware-attacks-down-fileless-malware-up-in-2018/136962/ And More… Statistics https://www.barkly.com/ponemon-2018-endpoint-security-statistics-trends “…77% of attacks that successfully compromised organizations in 2017 utilized fileless techniques…” https://blog.barkly.com/2018-cybersecurity-statistics A third of all attacks are projected to utilize fileless techniques in 2018. -

MMALE„A Methodology for Malware Analysis in Linux Environments
Computers, Materials & Continua Tech Science Press DOI:10.32604/cmc.2021.014596 Article MMALE—A Methodology for Malware Analysis in Linux Environments José Javier de Vicente Mohino1, Javier Bermejo Higuera1, Juan Ramón Bermejo Higuera1, Juan Antonio Sicilia Montalvo1,*, Manuel Sánchez Rubio1 and José Javier Martínez Herraiz2 1Escuela Superior de Ingeniería y Tecnología, Universidad Internacional de La Rioja, Logroño, 26006, La Rioja, Spain 2Departamento de Ciencias de la Computación de la Escuela Politécnica Superior, Universidad de Alcalá de Henares, Alcalá de Henares, Madrid, Spain *Corresponding Author: Juan Antonio Sicilia Montalvo. Email: [email protected] Received: 01 October 2020; Accepted: 28 November 2020 Abstract: In a computer environment, an operating system is prone to malware, and even the Linux operating system is not an exception. In recent years, malware has evolved, and attackers have become more qualified compared to a few years ago. Furthermore, Linux-based systems have become more attractive to cybercriminals because of the increasing use of the Linux operating system in web servers and Internet of Things (IoT) devices. Windows is the most employed OS, so most of the research efforts have been focused on its malware protection rather than on other operating systems. As a result, hundreds of research articles, documents, and methodologies dedicated to malware analysis have been reported. However, there has not been much literature concerning Linux security and protection from malware. To address all these new challenges, it is necessary to develop a methodology that can standardize the required steps to perform the malware analysis in depth. A systematic analysis process makes the difference between good and ordinary malware analyses. -
Geek Guide > Childhood's
GEEK GUIDE Childhood’s End Table of Contents The Conventional Wisdom ...................................................6 A Worthy Target in Its Own Right .........................................8 Facing the New Reality .........................................................9 Arming Yourself with a Few Basic Countermeasures ......11 How Attacks Happen and How to Avoid Them .................13 Don’t Presume Linux Is Not a Target and Do Nothing ����������������������������������������������������13 Recognize That Files on Any Platform Can Be Encrypted and Locked for Ransomware ���������������������������������������������������������������������������������������������������������������13 Unpatched Software, Including SSH and Common Services Like Apache and FTP, Create Vulnerabilities ����������������������������������������������������������������������������������������14 Unpatched Services atop Other Services Are Entry Points for Malware, Regardless of OS Platform ����������������������������������������������������������������������������������������������14 Linux Systems Can Be “Resistant Carries” That Pass Viruses and Malware to Vulnerable Systems �����������������������������������������������������������������������������������������������������14 Remote, Non-Native Scans Can Leave Linux Filesystems Open and Vulnerable ����������15 Unencrypted Remote Shares Can Leave Network Traffic Vulnerable ����������������������������15 Don’t Let the Scale of Your Operation Keep You from Monitoring Everything���������������16 Create Policies -

Decade of the Rats Threat Report
Decade of the Cross-Platform APT Espionage Attacks Targeting Linux, Windows and Android Table of Contents Executive Summary ................................................................................................3 Lancer – An Installation Script ..................................................................................20 PWNLNX5 – The Controller .......................................................................................22 Key Findings ...........................................................................................................5 Another Linux Oddity — CASPER Mirai Variant .........................................................23 Strategic Intelligence Assessments: ........................................................................... 5 Tactical Intelligence Assessments: ............................................................................ 6 Cellular Division ...................................................................................................24 PWNDROID4 ..............................................................................................................24 Why the Targeting of Linux Systems Matters ..........................................................7 An Interesting Find .....................................................................................................26 The Linux Advantage ..............................................................................................8 CASPER Goes Mobile – PWNDROID5 .......................................................................27