Interlude: Process API
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Parallel Programming in Unix, Many Programs Run in at the Same Time
parallelism parallel programming! to perform a number of tasks simultaneously! these can be calculations, or data transfer or…! In Unix, many programs run in at the same time handling various tasks! we like multitasking…! we don’t like waiting… "1 simplest way: FORK() Each process has a process ID called PID.! After a fork() call, ! there will be a second process with another PID which we call the child. ! The first process, will also continue to exist and to execute commands, we call it the mother. "2 fork() example #include <stdio.h> // printf, stderr, fprintf! ! #include <sys/types.h> // pid_t ! } // end of child! #include <unistd.h> // _exit, fork! else ! #include <stdlib.h> // exit ! { ! #include <errno.h> // errno! ! ! /* If fork() returns a positive number, we int main(void)! are in the parent process! {! * (the fork return value is the PID of the pid_t pid;! newly created child process)! pid = fork();! */! ! int i;! if (pid == -1) {! for (i = 0; i < 10; i++)! fprintf(stderr, "can't fork, error %d\n", {! errno);! printf("parent: %d\n", i);! exit(EXIT_FAILURE);! sleep(1);! }! }! ! exit(0);! if (pid == 0) {! }// end of parent! /* Child process:! ! * If fork() returns 0, it is the child return 0;! process.! } */! int j;! for (j = 0; j < 15; j++) {! printf("child: %d\n", j);! sleep(1);! }! _exit(0); /* Note that we do not use exit() */! !3 why not to fork fork() system call is the easiest way of branching out to do 2 tasks concurrently. BUT" it creates a separate address space such that the child process has an exact copy of all the memory segments of the parent process. -

A Microkernel API for Fine-Grained Decomposition
A Microkernel API for Fine-Grained Decomposition Sebastian Reichelt Jan Stoess Frank Bellosa System Architecture Group, University of Karlsruhe, Germany freichelt,stoess,[email protected] ABSTRACT from the microkernel APIs in existence. The need, for in- Microkernel-based operating systems typically require spe- stance, to explicitly pass messages between servers, or the cial attention to issues that otherwise arise only in dis- need to set up threads and address spaces in every server for tributed systems. The resulting extra code degrades per- parallelism or protection require OS developers to adopt the formance and increases development effort, severely limiting mindset of a distributed-system programmer rather than to decomposition granularity. take advantage of their knowledge on traditional OS design. We present a new microkernel design that enables OS devel- Distributed-system paradigms, though well-understood and opers to decompose systems into very fine-grained servers. suited for physically (and, thus, coarsely) partitioned sys- We avoid the typical obstacles by defining servers as light- tems, present obstacles to the fine-grained decomposition weight, passive objects. We replace complex IPC mecha- required to exploit the benefits of microkernels: First, a nisms by a simple function-call approach, and our passive, lot of development effort must be spent into matching the module-like server model obviates the need to create threads OS structure to the architecture of the selected microkernel, in every server. Server code is compiled into small self- which also hinders porting existing code from monolithic sys- contained files, which can be loaded into the same address tems. Second, the more servers exist | a desired property space (for speed) or different address spaces (for safety). -

Freebsd-And-Git.Pdf
FreeBSD and Git Ed Maste - FreeBSD Vendor Summit 2018 Purpose ● History and Context - ensure we’re starting from the same reference ● Identify next steps for more effective use / integration with Git / GitHub ● Understand what needs to be resolved for any future decision on Git as the primary repository Version control history ● CVS ○ 1993-2012 ● Subversion ○ src/ May 31 2008, r179447 ○ doc/www May 19, 2012 r38821 ○ ports July 14, 2012 r300894 ● Perforce ○ 2001-2018 ● Hg Mirror ● Git Mirror ○ 2011- Subversion Repositories svnsync repo svn Subversion & Git Repositories today svn2git git push svnsync git svn repo svn git github Repositories Today fork repo / Freebsd Downstream svn github github Repositories Today fork repo / Freebsd Downstream svn github github “Git is not a Version Control System” phk@ missive, reproduced at https://blog.feld.me/posts/2018/01/git-is-not-revision-control/ Subversion vs. Git: Myths and Facts https://svnvsgit.com/ “Git has a number of advantages in the popularity race, none of which are really to do with the technology” https://chapmanworld.com/2018/08/25/why-im-now-using-both-git-and-subversion-for-one-project/ 10 things I hate about Git https://stevebennett.me/2012/02/24/10-things-i-hate-about-git Git popularity Nobody uses Subversion anymore False. A myth. Despite all the marketing buzz related to Git, such notable open source projects as FreeBSD and LLVM continue to use Subversion as the main version control system. About 47% of other open source projects use Subversion too (while only 38% are on Git). (2016) https://svnvsgit.com/ Git popularity (2018) Git UI/UX Yes, it’s a mess. -

Technical Evaluation and Legal Opinion of Warden: a Network Forensics Tool, Version 1.0 Author(S): Rod Yazdan, Newton Mccollum, Jennifer Ockerman, Ph.D
NCJRS O FFICE OF JU STI CE PR OG RAM Se ~ N ATIONAL C RIMINAL JUSTICE REFERENCE SERVICE QJA BJS N/J OJJF OVC SMART '~ ..) The author(s) shown below used Federal funding provided by the U.S. Department of Justice to prepare the following resource: Document Title: Technical Evaluation and Legal Opinion of Warden: A Network Forensics Tool, Version 1.0 Author(s): Rod Yazdan, Newton McCollum, Jennifer Ockerman, Ph.D. Document Number: 252944 Date Received: May 2019 Award Number: 2013-MU-CX-K111 This resource has not been published by the U.S. Department of Justice. This resource is being made publically available through the Office of Justice Programs’ National Criminal Justice Reference Service. Opinions or points of view expressed are those of the author(s) and do not necessarily reflect the official position or policies of the U.S. Department of Justice. nl JOHNS HOPKINS ..APPLIED PHYSICS LABORATORY 11100 Johns Hopkins Road • Laurel, Maryland 20723-6099 AOS-18-1223 NIJ RT&E Center Project 15WA October 2018 TECHNICAL EVALUATION AND LEGAL OPINION OF WARDEN: A NETWORK FORENSICS TOOL Version 1.0 Rod Yazdan Newton McCollum Jennifer Ockerman, PhD Prepared for: r I I Nation~/ Institute Nl.I of Justice STRENGTHEN SCIENCE. ADVANCE JUSTICE. Prepared by: The Johns Hopkins University Applied Physics Laboratory 11100 Johns Hopkins Rd. Laurel, MD 20723-6099 Task No.: FGSGJ Contract No.: 2013-MU-CX-K111/115912 This project was supported by Award No. 2013-MU-CX-K111, awarded by the National Institute of Justice, Office of Justice Programs, U.S. Department of Justice. -
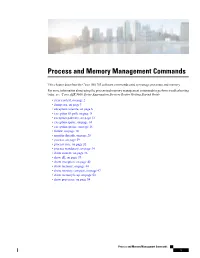
Process and Memory Management Commands
Process and Memory Management Commands This chapter describes the Cisco IOS XR software commands used to manage processes and memory. For more information about using the process and memory management commands to perform troubleshooting tasks, see Cisco ASR 9000 Series Aggregation Services Router Getting Started Guide. • clear context, on page 2 • dumpcore, on page 3 • exception coresize, on page 6 • exception filepath, on page 8 • exception pakmem, on page 12 • exception sparse, on page 14 • exception sprsize, on page 16 • follow, on page 18 • monitor threads, on page 25 • process, on page 29 • process core, on page 32 • process mandatory, on page 34 • show context, on page 36 • show dll, on page 39 • show exception, on page 42 • show memory, on page 44 • show memory compare, on page 47 • show memory heap, on page 50 • show processes, on page 54 Process and Memory Management Commands 1 Process and Memory Management Commands clear context clear context To clear core dump context information, use the clear context command in the appropriate mode. clear context location {node-id | all} Syntax Description location{node-id | all} (Optional) Clears core dump context information for a specified node. The node-id argument is expressed in the rack/slot/module notation. Use the all keyword to indicate all nodes. Command Default No default behavior or values Command Modes Administration EXEC EXEC mode Command History Release Modification Release 3.7.2 This command was introduced. Release 3.9.0 No modification. Usage Guidelines To use this command, you must be in a user group associated with a task group that includes appropriate task IDs. -

Openvms Record Management Services Reference Manual
OpenVMS Record Management Services Reference Manual Order Number: AA-PV6RD-TK April 2001 This reference manual contains general information intended for use in any OpenVMS programming language, as well as specific information on writing programs that use OpenVMS Record Management Services (OpenVMS RMS). Revision/Update Information: This manual supersedes the OpenVMS Record Management Services Reference Manual, OpenVMS Alpha Version 7.2 and OpenVMS VAX Version 7.2 Software Version: OpenVMS Alpha Version 7.3 OpenVMS VAX Version 7.3 Compaq Computer Corporation Houston, Texas © 2001 Compaq Computer Corporation Compaq, AlphaServer, VAX, VMS, the Compaq logo Registered in U.S. Patent and Trademark Office. Alpha, PATHWORKS, DECnet, DEC, and OpenVMS are trademarks of Compaq Information Technologies Group, L.P. in the United States and other countries. UNIX and X/Open are trademarks of The Open Group in the United States and other countries. All other product names mentioned herein may be the trademarks of their respective companies. Confidential computer software. Valid license from Compaq required for possession, use, or copying. Consistent with FAR 12.211 and 12.212, Commercial Computer Software, Computer Software Documentation, and Technical Data for Commercial Items are licensed to the U.S. Government under vendor’s standard commercial license. Compaq shall not be liable for technical or editorial errors or omissions contained herein. The information in this document is provided "as is" without warranty of any kind and is subject to change without notice. The warranties for Compaq products are set forth in the express limited warranty statements accompanying such products. Nothing herein should be construed as constituting an additional warranty. -

Hang Analysis: Fighting Responsiveness Bugs
Hang Analysis: Fighting Responsiveness Bugs Xi Wang† Zhenyu Guo‡ Xuezheng Liu‡ Zhilei Xu† Haoxiang Lin‡ Xiaoge Wang† Zheng Zhang‡ †Tsinghua University ‡Microsoft Research Asia Abstract return to life. However, during the long wait, the user can neither Soft hang is an action that was expected to respond instantly but in- cancel the operation nor close the application. The user may have stead drives an application into a coma. While the application usu- to kill the application or even reboot the computer. ally responds eventually, users cannot issue other requests while The problem of “not responding” is widespread. In our expe- waiting. Such hang problems are widespread in productivity tools rience, hang has occurred in everyday productivity tools, such as such as desktop applications; similar issues arise in server programs office suites, web browsers and source control clients. The actions as well. Hang problems arise because the software contains block- that trigger the hang issues are often the ones that users expect to re- ing or time-consuming operations in graphical user interface (GUI) turn instantly, such as opening a file or connecting to a printer. As and other time-critical call paths that should not. shown in Figure 1(a), TortoiseSVN repository browser becomes unresponsive when a user clicks to expand a directory node of a This paper proposes HANGWIZ to find hang bugs in source code, which are difficult to eliminate before release by testing, remote source repository. The causes of “not responding” bugs may be complicated. An as they often depend on a user’s environment. HANGWIZ finds hang bugs by finding hang points: an invocation that is expected erroneous program that becomes unresponsive may contain dead- to complete quickly, such as a GUI action, but calls a blocking locks (Engler and Ashcraft 2003; Williams et al. -
Process Management
Princeton University Computer Science 217: Introduction to Programming Systems Process Management 1 Goals of this Lecture Help you learn about: • Creating new processes • Waiting for processes to terminate • Executing new programs • Shell structure Why? • Creating new processes and executing new programs are fundamental tasks of many utilities and end-user applications • Assignment 7… 2 System-Level Functions As noted in the Exceptions and Processes lecture… Linux system-level functions for process management Function Description exit() Terminate the process fork() Create a child process wait() Wait for child process termination execvp() Execute a program in current process getpid() Return the process id of the current process 3 Agenda Creating new processes Waiting for processes to terminate Executing new programs Shell structure 4 Why Create New Processes? Why create a new process? • Scenario 1: Program wants to run an additional instance of itself • E.g., web server receives request; creates additional instance of itself to handle the request; original instance continues listening for requests • Scenario 2: Program wants to run a different program • E.g., shell receives a command; creates an additional instance of itself; additional instance overwrites itself with requested program to handle command; original instance continues listening for commands How to create a new process? • A “parent” process forks a “child” process • (Optionally) child process overwrites itself with a new program, after performing appropriate setup 5 fork System-Level -
Beginning Portable Shell Scripting from Novice to Professional
Beginning Portable Shell Scripting From Novice to Professional Peter Seebach 10436fmfinal 1 10/23/08 10:40:24 PM Beginning Portable Shell Scripting: From Novice to Professional Copyright © 2008 by Peter Seebach All rights reserved. No part of this work may be reproduced or transmitted in any form or by any means, electronic or mechanical, including photocopying, recording, or by any information storage or retrieval system, without the prior written permission of the copyright owner and the publisher. ISBN-13 (pbk): 978-1-4302-1043-6 ISBN-10 (pbk): 1-4302-1043-5 ISBN-13 (electronic): 978-1-4302-1044-3 ISBN-10 (electronic): 1-4302-1044-3 Printed and bound in the United States of America 9 8 7 6 5 4 3 2 1 Trademarked names may appear in this book. Rather than use a trademark symbol with every occurrence of a trademarked name, we use the names only in an editorial fashion and to the benefit of the trademark owner, with no intention of infringement of the trademark. Lead Editor: Frank Pohlmann Technical Reviewer: Gary V. Vaughan Editorial Board: Clay Andres, Steve Anglin, Ewan Buckingham, Tony Campbell, Gary Cornell, Jonathan Gennick, Michelle Lowman, Matthew Moodie, Jeffrey Pepper, Frank Pohlmann, Ben Renow-Clarke, Dominic Shakeshaft, Matt Wade, Tom Welsh Project Manager: Richard Dal Porto Copy Editor: Kim Benbow Associate Production Director: Kari Brooks-Copony Production Editor: Katie Stence Compositor: Linda Weidemann, Wolf Creek Press Proofreader: Dan Shaw Indexer: Broccoli Information Management Cover Designer: Kurt Krames Manufacturing Director: Tom Debolski Distributed to the book trade worldwide by Springer-Verlag New York, Inc., 233 Spring Street, 6th Floor, New York, NY 10013. -

Getting Started With... Berkeley Software for UNIX† on the VAX‡ (The Third Berkeley Software Distribution)
Getting started with... Berkeley Software for UNIX† on the VAX‡ (The third Berkeley Software Distribution) A package of software for UNIX developed at the Computer Science Division of the University of California at Berkeley is installed on our system. This package includes a new version of the operating sys- tem kernel which supports a virtual memory, demand-paged environment. While the kernel change should be transparent to most programs, there are some things you should know if you plan to run large programs to optimize their performance in a virtual memory environment. There are also a number of other new pro- grams which are now installed on our machine; the more important of these are described below. Documentation The new software is described in two new volumes of documentation. The first is a new version of volume 1 of the UNIX programmers manual which has integrated manual pages for the distributed software and incorporates changes to the system made while introducing the virtual memory facility. The second volume of documentation is numbered volume 2c, of which this paper is a section. This volume contains papers about programs which are in the distribution package. Where are the programs? Most new programs from Berkeley reside in the directory /usr/ucb. A major exception is the C shell, csh, which lives in /bin. We will later describe how you can arrange for the programs in the distribution to be part of your normal working environment. Making use of the Virtual Memory With a virtual memory system, it is no longer necessary for running programs to be fully resident in memory. -

Unix/Linux Command Reference
Unix/Linux Command Reference .com File Commands System Info ls – directory listing date – show the current date and time ls -al – formatted listing with hidden files cal – show this month's calendar cd dir - change directory to dir uptime – show current uptime cd – change to home w – display who is online pwd – show current directory whoami – who you are logged in as mkdir dir – create a directory dir finger user – display information about user rm file – delete file uname -a – show kernel information rm -r dir – delete directory dir cat /proc/cpuinfo – cpu information rm -f file – force remove file cat /proc/meminfo – memory information rm -rf dir – force remove directory dir * man command – show the manual for command cp file1 file2 – copy file1 to file2 df – show disk usage cp -r dir1 dir2 – copy dir1 to dir2; create dir2 if it du – show directory space usage doesn't exist free – show memory and swap usage mv file1 file2 – rename or move file1 to file2 whereis app – show possible locations of app if file2 is an existing directory, moves file1 into which app – show which app will be run by default directory file2 ln -s file link – create symbolic link link to file Compression touch file – create or update file tar cf file.tar files – create a tar named cat > file – places standard input into file file.tar containing files more file – output the contents of file tar xf file.tar – extract the files from file.tar head file – output the first 10 lines of file tar czf file.tar.gz files – create a tar with tail file – output the last 10 lines -

SOAP / REST and IBM I
1/11/18 SOPA / REST and IBM i Tim Rowe- [email protected] Business Architect Application Development © 2017 International Business Machines Corporation Using a REST API with Watson https://ibm-i-watson-test.mybluemix.net/ 2 © 2017 International Business Machines Corporation 1 1/11/18 ™ What is an API - Agenda •What is an API •What is a Web Service •SOAP vs REST – What is SOAP – What is REST – Benefits – Drawbacks 3 © 2017 International Business Machines Corporation ™ Connections Devices There Here Applications 4 © 2017 International Business Machines Corporation 2 1/11/18 ™ 5 © 2017 International Business Machines Corporation ™ 6 © 2017 International Business Machines Corporation 3 1/11/18 ™ 7 © 2017 International Business Machines Corporation ™ 8 © 2017 International Business Machines Corporation 4 1/11/18 ™ API Definition Application Programming Interface 9 © 2017 International Business Machines Corporation ™ API Definition 10 © 2017 International Business Machines Corporation 5 1/11/18 ™ APIs - Simple Simple way to connect endpoints. Send a request and receive a response. 11 © 2017 International Business Machines Corporation ™ Example Kitchen 12 © 2017 International Business Machines Corporation 6 1/11/18 ™ 13 © 2017 International Business Machines Corporation ™ Not just a buzz-word, but rather the evolution of services- oriented IT. Allows users, businesses & partners the ability to interact in new and different ways resulting in the growth (in some cases the revolution) of business. 14 © 2017 International Business Machines Corporation