Public-Key Cryptography RSA Attacks Against RSA
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Public-Key Cryptography
Public Key Cryptography EJ Jung Basic Public Key Cryptography public key public key ? private key Alice Bob Given: Everybody knows Bob’s public key - How is this achieved in practice? Only Bob knows the corresponding private key Goals: 1. Alice wants to send a secret message to Bob 2. Bob wants to authenticate himself Requirements for Public-Key Crypto ! Key generation: computationally easy to generate a pair (public key PK, private key SK) • Computationally infeasible to determine private key PK given only public key PK ! Encryption: given plaintext M and public key PK, easy to compute ciphertext C=EPK(M) ! Decryption: given ciphertext C=EPK(M) and private key SK, easy to compute plaintext M • Infeasible to compute M from C without SK • Decrypt(SK,Encrypt(PK,M))=M Requirements for Public-Key Cryptography 1. Computationally easy for a party B to generate a pair (public key KUb, private key KRb) 2. Easy for sender to generate ciphertext: C = EKUb (M ) 3. Easy for the receiver to decrypt ciphertect using private key: M = DKRb (C) = DKRb[EKUb (M )] Henric Johnson 4 Requirements for Public-Key Cryptography 4. Computationally infeasible to determine private key (KRb) knowing public key (KUb) 5. Computationally infeasible to recover message M, knowing KUb and ciphertext C 6. Either of the two keys can be used for encryption, with the other used for decryption: M = DKRb[EKUb (M )] = DKUb[EKRb (M )] Henric Johnson 5 Public-Key Cryptographic Algorithms ! RSA and Diffie-Hellman ! RSA - Ron Rives, Adi Shamir and Len Adleman at MIT, in 1977. • RSA -

Integral Cryptanalysis on Full MISTY1⋆
Integral Cryptanalysis on Full MISTY1? Yosuke Todo NTT Secure Platform Laboratories, Tokyo, Japan [email protected] Abstract. MISTY1 is a block cipher designed by Matsui in 1997. It was well evaluated and standardized by projects, such as CRYPTREC, ISO/IEC, and NESSIE. In this paper, we propose a key recovery attack on the full MISTY1, i.e., we show that 8-round MISTY1 with 5 FL layers does not have 128-bit security. Many attacks against MISTY1 have been proposed, but there is no attack against the full MISTY1. Therefore, our attack is the first cryptanalysis against the full MISTY1. We construct a new integral characteristic by using the propagation characteristic of the division property, which was proposed in 2015. We first improve the division property by optimizing a public S-box and then construct a 6-round integral characteristic on MISTY1. Finally, we recover the secret key of the full MISTY1 with 263:58 chosen plaintexts and 2121 time complexity. Moreover, if we can use 263:994 chosen plaintexts, the time complexity for our attack is reduced to 2107:9. Note that our cryptanalysis is a theoretical attack. Therefore, the practical use of MISTY1 will not be affected by our attack. Keywords: MISTY1, Integral attack, Division property 1 Introduction MISTY [Mat97] is a block cipher designed by Matsui in 1997 and is based on the theory of provable security [Nyb94,NK95] against differential attack [BS90] and linear attack [Mat93]. MISTY has a recursive structure, and the component function has a unique structure, the so-called MISTY structure [Mat96]. -

LNCS 7215, Pp
ACoreCalculusforProvenance Umut A. Acar1,AmalAhmed2,JamesCheney3,andRolyPerera1 1 Max Planck Institute for Software Systems umut,rolyp @mpi-sws.org { 2 Indiana} University [email protected] 3 University of Edinburgh [email protected] Abstract. Provenance is an increasing concern due to the revolution in sharing and processing scientific data on the Web and in other computer systems. It is proposed that many computer systems will need to become provenance-aware in order to provide satisfactory accountability, reproducibility,andtrustforscien- tific or other high-value data. To date, there is not a consensus concerning ap- propriate formal models or security properties for provenance. In previous work, we introduced a formal framework for provenance security and proposed formal definitions of properties called disclosure and obfuscation. This paper develops a core calculus for provenance in programming languages. Whereas previous models of provenance have focused on special-purpose languages such as workflows and database queries, we consider a higher-order, functional language with sums, products, and recursive types and functions. We explore the ramifications of using traces based on operational derivations for the purpose of comparing other forms of provenance. We design a rich class of prove- nance views over traces. Finally, we prove relationships among provenance views and develop some solutions to the disclosure and obfuscation problems. 1Introduction Provenance, or meta-information about the origin, history, or derivation of an object, is now recognized as a central challenge in establishing trust and providing security in computer systems, particularly on the Web. Essentially, provenance management in- volves instrumenting a system with detailed monitoring or logging of auditable records that help explain how results depend on inputs or other (sometimes untrustworthy) sources. -

Public Key Cryptography And
PublicPublic KeyKey CryptographyCryptography andand RSARSA Raj Jain Washington University in Saint Louis Saint Louis, MO 63130 [email protected] Audio/Video recordings of this lecture are available at: http://www.cse.wustl.edu/~jain/cse571-11/ Washington University in St. Louis CSE571S ©2011 Raj Jain 9-1 OverviewOverview 1. Public Key Encryption 2. Symmetric vs. Public-Key 3. RSA Public Key Encryption 4. RSA Key Construction 5. Optimizing Private Key Operations 6. RSA Security These slides are based partly on Lawrie Brown’s slides supplied with William Stallings’s book “Cryptography and Network Security: Principles and Practice,” 5th Ed, 2011. Washington University in St. Louis CSE571S ©2011 Raj Jain 9-2 PublicPublic KeyKey EncryptionEncryption Invented in 1975 by Diffie and Hellman at Stanford Encrypted_Message = Encrypt(Key1, Message) Message = Decrypt(Key2, Encrypted_Message) Key1 Key2 Text Ciphertext Text Keys are interchangeable: Key2 Key1 Text Ciphertext Text One key is made public while the other is kept private Sender knows only public key of the receiver Asymmetric Washington University in St. Louis CSE571S ©2011 Raj Jain 9-3 PublicPublic KeyKey EncryptionEncryption ExampleExample Rivest, Shamir, and Adleman at MIT RSA: Encrypted_Message = m3 mod 187 Message = Encrypted_Message107 mod 187 Key1 = <3,187>, Key2 = <107,187> Message = 5 Encrypted Message = 53 = 125 Message = 125107 mod 187 = 5 = 125(64+32+8+2+1) mod 187 = {(12564 mod 187)(12532 mod 187)... (1252 mod 187)(125 mod 187)} mod 187 Washington University in -

New Security Proofs for the 3GPP Confidentiality and Integrity
An extended abstract of this paper appears in Fast Software Encryption, FSE 2004, Lecture Notes in Computer Science, W. Meier and B. Roy editors, Springer-Verlag, 2004. This is the full version. New Security Proofs for the 3GPP Confidentiality and Integrity Algorithms Tetsu Iwata¤ Tadayoshi Kohnoy January 26, 2004 Abstract This paper analyses the 3GPP confidentiality and integrity schemes adopted by Universal Mobile Telecommunication System, an emerging standard for third generation wireless commu- nications. The schemes, known as f8 and f9, are based on the block cipher KASUMI. Although previous works claim security proofs for f8 and f90, where f90 is a generalized versions of f9, it was recently shown that these proofs are incorrect. Moreover, Iwata and Kurosawa (2003) showed that it is impossible to prove f8 and f90 secure under the standard PRP assumption on the underlying block cipher. We address this issue here, showing that it is possible to prove f80 and f90 secure if we make the assumption that the underlying block cipher is a secure PRP-RKA against a certain class of related-key attacks; here f80 is a generalized version of f8. Our results clarify the assumptions necessary in order for f8 and f9 to be secure and, since no related-key attacks are known against the full eight rounds of KASUMI, lead us to believe that the confidentiality and integrity mechanisms used in real 3GPP applications are secure. Keywords: Modes of operation, PRP-RKA, f8, f9, KASUMI, security proofs. ¤Dept. of Computer and Information Sciences, Ibaraki University, 4–12–1 Nakanarusawa, Hitachi, Ibaraki 316- 8511, Japan. -

Universit`A Di Pisa Post Quantum Cryptography
Universit`adi Pisa Facolt`a di Scienze Matematiche, Fisiche e Naturali Corso di Laurea Magistrale in Fisica Anno Accademico 2013/2014 Elaborato Finale Post Quantum Cryptography Candidato: Relatori: Antonio Vaira Prof. Oliver Morsch Ing. Cristiano Borrelli Alla mia mamma Abstract I started my experience with cryptography within the Airbus environment working on this master thesis. I have been asked to provide a framework, or in other words, a big picture about present-day alternatives to the most used public key crypto-system, the RSA, that are supposed to be quantum resistant. The final application of my work eventually resulted in recommendations on how to handle the quantum threat in the near future. This was quite a complex task to accomplish because it involves a huge variety of topics but by physical background was really helpful in facing it. Not because of specific and previous knowledge but for the mathematical toolsacquired during the studies and especially for that attitude that belongs to out category that make us, physicist problem solver in a large variety of fields. Indeed I also tried to go a bit further with my studies. I took one of the most promising algorithm on my opinion, but not well known yet so unfeasible for a recommendation and therefore an implementation in the close future, and I tried to figure out how to enhance it from both a security and an operational point of view (how to increase the correctness ratio of the decryption and the speed of the cryptographic operations). It followed a period of time in which I improved my skills with few computing languages and in the end I decided to implement a toy model at a high level using an interface that already implements all the mathematical and algebraical structures used to build the model. -

Sabermetrics: the Past, the Present, and the Future
Sabermetrics: The Past, the Present, and the Future Jim Albert February 12, 2010 Abstract This article provides an overview of sabermetrics, the science of learn- ing about baseball through objective evidence. Statistics and baseball have always had a strong kinship, as many famous players are known by their famous statistical accomplishments such as Joe Dimaggio’s 56-game hitting streak and Ted Williams’ .406 batting average in the 1941 baseball season. We give an overview of how one measures performance in batting, pitching, and fielding. In baseball, the traditional measures are batting av- erage, slugging percentage, and on-base percentage, but modern measures such as OPS (on-base percentage plus slugging percentage) are better in predicting the number of runs a team will score in a game. Pitching is a harder aspect of performance to measure, since traditional measures such as winning percentage and earned run average are confounded by the abilities of the pitcher teammates. Modern measures of pitching such as DIPS (defense independent pitching statistics) are helpful in isolating the contributions of a pitcher that do not involve his teammates. It is also challenging to measure the quality of a player’s fielding ability, since the standard measure of fielding, the fielding percentage, is not helpful in understanding the range of a player in moving towards a batted ball. New measures of fielding have been developed that are useful in measuring a player’s fielding range. Major League Baseball is measuring the game in new ways, and sabermetrics is using this new data to find better mea- sures of player performance. -

Ch 13 Digital Signature
1 CH 13 DIGITAL SIGNATURE Cryptography and Network Security HanJung Mason Yun 2 Index 13.1 Digital Signatures 13.2 Elgamal Digital Signature Scheme 13.3 Schnorr Digital Signature Scheme 13.4 NIST Digital Signature Algorithm 13.6 RSA-PSS Digital Signature Algorithm 3 13.1 Digital Signature - Properties • It must verify the author and the date and time of the signature. • It must authenticate the contents at the time of the signature. • It must be verifiable by third parties, to resolve disputes. • The digital signature function includes authentication. 4 5 6 Attacks and Forgeries • Key-Only attack • Known message attack • Generic chosen message attack • Directed chosen message attack • Adaptive chosen message attack 7 Attacks and Forgeries • Total break • Universal forgery • Selective forgery • Existential forgery 8 Digital Signature Requirements • It must be a bit pattern that depends on the message. • It must use some information unique to the sender to prevent both forgery and denial. • It must be relatively easy to produce the digital signature. • It must be relatively easy to recognize and verify the digital signature. • It must be computationally infeasible to forge a digital signature, either by constructing a new message for an existing digital signature or by constructing a fraudulent digital signature for a given message. • It must be practical to retain a copy of the digital signature in storage. 9 Direct Digital Signature • Digital signature scheme that involves only the communication parties. • It must authenticate the contents at the time of the signature. • It must be verifiable by third parties, to resolve disputes. • Thus, the digital signature function includes the authentication function. -
A Comparitive Study of Asymmetric Key Cryptography
Vol-5 Issue-3 2019 IJARIIE-ISSN(O)-2395-4396 A COMPARITIVE STUDY OF ASYMMETRIC KEY CRYPTOGRAPHY Dr. Prashant P. Pittalia Associate Professor, Department of Computer Science, Gujarat, India ABSTRACT Cryptography is use to secure the computer networks. Cryptography converts the plain text into cipher text such a way that it is impossible for intruders to read and understand the content. Asymmetric key cryptography is based on the public key and private key concepts to support the confidentiality and authentication services in computer networks. This paper describes how confidentiality and authentication service provides by asymmetric key algorithms. In this paper the discussion and comparison of a asymmetric key algorithms like RSA, Diffie-Hellman, ElGamal and ECC. Keyword: - RSA, Authentication, Public key, Private Key, Confidentiality 1. INTRODUCTION Today in global village the internet security is the challenging aspect and cryptography is used for it. Cryptography is the mathematical techniques of information security. It supports confidentiality, privacy, and data integrity and entity authentication. Cryptography systems classified into two main categories symmetric-key cryptography that use a symmetric key used by both sender and recipient and a public-key cryptography that use two keys, a public key known to everyone in the network and a private key that is used by only the recipient of the messages. Symmetric algorithms use the same secret key for both encryption of plaintext and decryption of cipher text. The keys may be same or there may be an easy transformation to go between the two keys. The key is shared between the two parties (sender and receiver) who want to communicate. -
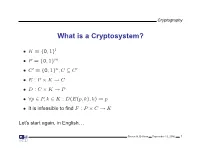
What Is a Cryptosystem?
Cryptography What is a Cryptosystem? • K = {0, 1}l • P = {0, 1}m • C′ = {0, 1}n,C ⊆ C′ • E : P × K → C • D : C × K → P • ∀p ∈ P, k ∈ K : D(E(p, k), k) = p • It is infeasible to find F : P × C → K Let’s start again, in English. Steven M. Bellovin September 13, 2006 1 Cryptography What is a Cryptosystem? A cryptosystem is pair of algorithms that take a key and convert plaintext to ciphertext and back. Plaintext is what you want to protect; ciphertext should appear to be random gibberish. The design and analysis of today’s cryptographic algorithms is highly mathematical. Do not try to design your own algorithms. Steven M. Bellovin September 13, 2006 2 Cryptography A Tiny Bit of History • Encryption goes back thousands of years • Classical ciphers encrypted letters (and perhaps digits), and yielded all sorts of bizarre outputs. • The advent of military telegraphy led to ciphers that produced only letters. Steven M. Bellovin September 13, 2006 3 Cryptography Codes vs. Ciphers • Ciphers operate syntactically, on letters or groups of letters: A → D, B → E, etc. • Codes operate semantically, on words, phrases, or sentences, per this 1910 codebook Steven M. Bellovin September 13, 2006 4 Cryptography A 1910 Commercial Codebook Steven M. Bellovin September 13, 2006 5 Cryptography Commercial Telegraph Codes • Most were aimed at economy • Secrecy from casual snoopers was a useful side-effect, but not the primary motivation • That said, a few such codes were intended for secrecy; I have some in my collection, including one intended for union use Steven M. -

CS 255: Intro to Cryptography 1 Introduction 2 End-To-End
Programming Assignment 2 Winter 2021 CS 255: Intro to Cryptography Prof. Dan Boneh Due Monday, March 1st, 11:59pm 1 Introduction In this assignment, you are tasked with implementing a secure and efficient end-to-end encrypted chat client using the Double Ratchet Algorithm, a popular session setup protocol that powers real- world chat systems such as Signal and WhatsApp. As an additional challenge, assume you live in a country with government surveillance. Thereby, all messages sent are required to include the session key encrypted with a fixed public key issued by the government. In your implementation, you will make use of various cryptographic primitives we have discussed in class—notably, key exchange, public key encryption, digital signatures, and authenticated encryption. Because it is ill-advised to implement your own primitives in cryptography, you should use an established library: in this case, the Stanford Javascript Crypto Library (SJCL). We will provide starter code that contains a basic template, which you will be able to fill in to satisfy the functionality and security properties described below. 2 End-to-end Encrypted Chat Client 2.1 Implementation Details Your chat client will use the Double Ratchet Algorithm to provide end-to-end encrypted commu- nications with other clients. To evaluate your messaging client, we will check that two or more instances of your implementation it can communicate with each other properly. We feel that it is best to understand the Double Ratchet Algorithm straight from the source, so we ask that you read Sections 1, 2, and 3 of Signal’s published specification here: https://signal. -

A Covert Encryption Method for Applications in Electronic Data Interchange
Technological University Dublin ARROW@TU Dublin Articles School of Electrical and Electronic Engineering 2009-01-01 A Covert Encryption Method for Applications in Electronic Data Interchange Jonathan Blackledge Technological University Dublin, [email protected] Dmitry Dubovitskiy Oxford Recognition Limited, [email protected] Follow this and additional works at: https://arrow.tudublin.ie/engscheleart2 Part of the Digital Communications and Networking Commons, Numerical Analysis and Computation Commons, and the Software Engineering Commons Recommended Citation Blackledge, J., Dubovitskiy, D.: A Covert Encryption Method for Applications in Electronic Data Interchange. ISAST Journal on Electronics and Signal Processing, vol: 4, issue: 1, pages: 107 -128, 2009. doi:10.21427/D7RS67 This Article is brought to you for free and open access by the School of Electrical and Electronic Engineering at ARROW@TU Dublin. It has been accepted for inclusion in Articles by an authorized administrator of ARROW@TU Dublin. For more information, please contact [email protected], [email protected]. This work is licensed under a Creative Commons Attribution-Noncommercial-Share Alike 4.0 License A Covert Encryption Method for Applications in Electronic Data Interchange Jonathan M Blackledge, Fellow, IET, Fellow, BCS and Dmitry A Dubovitskiy, Member IET Abstract— A principal weakness of all encryption systems is to make sure that the ciphertext is relatively strong (but not that the output data can be ‘seen’ to be encrypted. In other too strong!) and that the information extracted is of good words, encrypted data provides a ‘flag’ on the potential value quality in terms of providing the attacker with ‘intelligence’ of the information that has been encrypted.