Cryptanalysis of the SIGABA Cipher
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Implementation and Didactical Visualization of the Chacha Cipher Family in Cryptool 2
Implementation and Didactical Visualization of the ChaCha Cipher Family in CrypTool 2 Bachelor’s Thesis Ramdip Gill Supervisor Priv.-Doz. Dr. Wolfgang Merkle Second Supervisor Prof. Dr. Frederik Armknecht Heidelberg, December 11, 2020 Faculty of Mathematics and Computer Science Heidelberg University ABSTRACT This thesis is about the implementation of the ChaCha plug-in in CrypTool 2. The thesis introduces the ChaCha cipher family, explains what the plug-in is capa- ble of, and gives insight into the development process of the plug-in. ChaCha is used in the Transport Layer Security protocol (TLS) since 2014 and so very relevant for applied modern cryptography. Because of the importance of ChaCha its internal design should be made more accessible to the broader public. This is the actual goal of the plug-in. The goal is achieved by focusing on an in-depth but easy to understand visualiza- tion of the encryption process. CrypTool 2 is the most popular e-learning platform in the field of cryptology, used in schools, universities, and companies. Incorporat- ing this plug-in into CrypTool 2 helps to reach a broad audience. iii ZUSAMMENFASSUNG Diese Bachelorarbeit befasst sich mit der Implementierung des ChaCha Plugins für CrypTool 2. Die Arbeit stellt die Familie der ChaCha-Chiffren vor; erklärt, wozu das Plugin in der Lage ist; und gibt Einblick in den Entwicklungsprozess des Plugins. ChaCha wird seit 2014 im Transport Layer Security-Protokoll (TLS) verwendet und ist daher für die angewandte moderne Kryptographie sehr relevant. Aufgrund der Bedeutung von ChaCha sollte sein internes Design der breiten Öffentlichkeit zu- gänglicher gemacht werden. -

COS433/Math 473: Cryptography Mark Zhandry Princeton University Spring 2017 Cryptography Is Everywhere a Long & Rich History
COS433/Math 473: Cryptography Mark Zhandry Princeton University Spring 2017 Cryptography Is Everywhere A Long & Rich History Examples: • ~50 B.C. – Caesar Cipher • 1587 – Babington Plot • WWI – Zimmermann Telegram • WWII – Enigma • 1976/77 – Public Key Cryptography • 1990’s – Widespread adoption on the Internet Increasingly Important COS 433 Practice Theory Inherent to the study of crypto • Working knowledge of fundamentals is crucial • Cannot discern security by experimentation • Proofs, reductions, probability are necessary COS 433 What you should expect to learn: • Foundations and principles of modern cryptography • Core building blocks • Applications Bonus: • Debunking some Hollywood crypto • Better understanding of crypto news COS 433 What you will not learn: • Hacking • Crypto implementations • How to design secure systems • Viruses, worms, buffer overflows, etc Administrivia Course Information Instructor: Mark Zhandry (mzhandry@p) TA: Fermi Ma (fermima1@g) Lectures: MW 1:30-2:50pm Webpage: cs.princeton.edu/~mzhandry/2017-Spring-COS433/ Office Hours: please fill out Doodle poll Piazza piaZZa.com/princeton/spring2017/cos433mat473_s2017 Main channel of communication • Course announcements • Discuss homework problems with other students • Find study groups • Ask content questions to instructors, other students Prerequisites • Ability to read and write mathematical proofs • Familiarity with algorithms, analyZing running time, proving correctness, O notation • Basic probability (random variables, expectation) Helpful: • Familiarity with NP-Completeness, reductions • Basic number theory (modular arithmetic, etc) Reading No required text Computer Science/Mathematics Chapman & Hall/CRC If you want a text to follow along with: Second CRYPTOGRAPHY AND NETWORK SECURITY Cryptography is ubiquitous and plays a key role in ensuring data secrecy and Edition integrity as well as in securing computer systems more broadly. -

IMPLEMENTASI ALGORITMA CAESAR, CIPHER DISK, DAN SCYTALE PADA APLIKASI ENKRIPSI DAN DEKRIPSI PESAN SINGKAT, Lumasms
Prosiding Seminar Ilmiah Nasional Komputer dan Sistem Intelijen (KOMMIT 2014) Vol. 8 Oktober 2014 Universitas Gunadarma – Depok – 14 – 15 Oktober 2014 ISSN : 2302-3740 IMPLEMENTASI ALGORITMA CAESAR, CIPHER DISK, DAN SCYTALE PADA APLIKASI ENKRIPSI DAN DEKRIPSI PESAN SINGKAT, LumaSMS Yusuf Triyuswoyo ST. 1 Ferina Ferdianti ST. 2 Donny Ajie Baskoro ST. 3 Lia Ambarwati ST. 4 Septiawan ST. 5 1,2,3,4,5Jurusan Manajemen Sistem Informasi, Universitas Gunadarma [email protected] Abstrak Short Message Service (SMS) merupakan salah satu cara berkomunikasi yang banyak digunakan oleh pengguna telepon seluler. Namun banyaknya pengguna telepon seluler yang menggunakan layanan SMS, tidak diimbangi dengan faktor keamanan yang ada pada layanan tersebut. Banyak pengguna telepon seluler yang belum menyadari bahwa SMS tidak menjamin integritas dan keamanan pesan yang disampaikan. Ada beberapa risiko yang dapat mengancam keamanan pesan pada layanan SMS, diantaranya: SMS spoofing, SMS snooping, dan SMS interception. Untuk mengurangi risiko tersebut, maka dibutuhkan sebuah sistem keamanan pada layanan SMS yang mampu menjaga integritas dan keamanan isi pesan. Dimana tujuannya ialah untuk menutupi celah pada tingkat keamanan SMS. Salah satu penanggulangannya ialah dengan menerapkan algoritma kriptografi, yaitu kombinasi atas algoritma Cipher Disk, Caesar, dan Scytale pada pesan yang akan dikirim. Tujuan dari penulisan ini adalah membangun aplikasi LumaSMS, dengan menggunakan kombinasi ketiga algoritma kriptografi tersebut. Dengan adanya aplikasi ini diharapkan mampu mengurangi masalah keamanan dan integritas SMS. Kata Kunci: caesar, cipher disk, kriptografi, scytale, SMS. PENDAHULUAN dibutuhkan dikarenakan SMS mudah digunakan dan biaya yang dikeluarkan Telepon seluler merupakan salah untuk mengirim SMS relatif murah. satu hasil dari perkembangan teknologi Namun banyaknya pengguna komunikasi. -
Cryptology with Jcryptool V1.0
www.cryptool.org Cryptology with JCrypTool (JCT) A Practical Introduction to Cryptography and Cryptanalysis Prof Bernhard Esslinger and the CrypTool team Nov 24th, 2020 JCrypTool 1.0 Cryptology with JCrypTool Agenda Introduction to the e-learning software JCrypTool 2 Applications within JCT – a selection 22 How to participate 87 JCrypTool 1.0 Page 2 / 92 Introduction to the software JCrypTool (JCT) Overview JCrypTool – A cryptographic e-learning platform Page 4 What is cryptology? Page 5 The Default Perspective of JCT Page 6 Typical usage of JCT in the Default Perspective Page 7 The Algorithm Perspective of JCT Page 9 The Crypto Explorer Page 10 Algorithms in the Crypto Explorer view Page 11 The Analysis tools Page 13 Visuals & Games Page 14 General operation instructions Page 15 User settings Page 20 Command line parameters Page 21 JCrypTool 1.0 Page 3 / 92 JCrypTool – A cryptographic e-learning platform The project Overview . JCrypTool – abbreviated as JCT – is a free e-learning software for classical and modern cryptology. JCT is platform independent, i.e. it is executable on Windows, MacOS and Linux. It has a modern pure-plugin architecture. JCT is developed within the open-source project CrypTool (www.cryptool.org). The CrypTool project aims to explain and visualize cryptography and cryptanalysis in an easy and understandable way while still being correct from a scientific point of view. The target audience of JCT are mainly: ‐ Pupils and students ‐ Teachers and lecturers/professors ‐ Employees in awareness campaigns ‐ People interested in cryptology. As JCT is open-source software, everyone is capable of implementing his own plugins. -

Visualization of the Avalanche Effect in CT2
University of Mannheim Faculty for Business Informatics & Business Mathematics Theoretical Computer Science and IT Security Group Bachelor's Thesis Visualization of the Avalanche Effect in CT2 as part of the degree program Bachelor of Science Wirtschaftsinformatik submitted by Camilo Echeverri [email protected] on October 31, 2016 (2nd revised public version, Apr 18, 2017) Supervisors: Prof. Dr. Frederik Armknecht Prof. Bernhard Esslinger Visualization of the Avalanche Effect in CT2 Abstract Cryptographic algorithms must fulfill certain properties concerning their security. This thesis aims at providing insights into the importance of the avalanche effect property by introducing a new plugin for the cryptography and cryptanalysis platform CrypTool 2. The thesis addresses some of the desired properties, discusses the implementation of the plugin for modern and classic ciphers, guides the reader on how to use it, applies the proposed tool in order to test the avalanche effect of different cryptographic ciphers and hash functions, and interprets the results obtained. 2 Contents Abstract .......................................... 2 Contents .......................................... 3 List of Abbreviations .................................. 5 List of Figures ...................................... 6 List of Tables ....................................... 7 1 Introduction ..................................... 8 1.1 CrypTool 2 . 8 1.2 Outline of the Thesis . 9 2 Properties of Secure Block Ciphers ....................... 10 2.1 Avalanche Effect . 10 2.2 Completeness . 10 3 Related Work ..................................... 11 4 Plugin Design and Implementation ....................... 12 4.1 General Description of the Plugin . 12 4.2 Prepared Methods . 14 4.2.1 AES and DES . 14 4.3 Unprepared Methods . 20 4.3.1 Classic Ciphers, Modern Ciphers, and Hash Functions . 20 4.4 Architecture of the Code . 22 4.5 Limitations and Future Work . -

CEH: Certified Ethical Hacker Course Content
CEH: Certified Ethical Hacker Course ID #: 1275-100-ZZ-W Hours: 35 Course Content Course Description: The Certified Ethical Hacker (CEH) program is the core of the most desired information security training system any information security professional will ever want to be in. The CEH, is the first part of a 3 part EC-Council Information Security Track which helps you master hacking technologies. You will become a hacker, but an ethical one! As the security mindset in any organization must not be limited to the silos of a certain vendor, technologies or pieces of equipment. This course was designed to provide you with the tools and techniques used by hackers and information security professionals alike to break into an organization. As we put it, “To beat a hacker, you need to think like a hacker”. This course will immerse you into the Hacker Mindset so that you will be able to defend against future attacks. It puts you in the driver’s seat of a hands-on environment with a systematic ethical hacking process. Here, you will be exposed to an entirely different way of achieving optimal information security posture in their organization; by hacking it! You will scan, test, hack and secure your own systems. You will be thought the Five Phases of Ethical Hacking and thought how you can approach your target and succeed at breaking in every time! The ve phases include Reconnaissance, Gaining Access, Enumeration, Maintaining Access, and covering your tracks. The tools and techniques in each of these five phases are provided in detail in an encyclopedic approach to help you identify when an attack has been used against your own targets. -

The Mathemathics of Secrets.Pdf
THE MATHEMATICS OF SECRETS THE MATHEMATICS OF SECRETS CRYPTOGRAPHY FROM CAESAR CIPHERS TO DIGITAL ENCRYPTION JOSHUA HOLDEN PRINCETON UNIVERSITY PRESS PRINCETON AND OXFORD Copyright c 2017 by Princeton University Press Published by Princeton University Press, 41 William Street, Princeton, New Jersey 08540 In the United Kingdom: Princeton University Press, 6 Oxford Street, Woodstock, Oxfordshire OX20 1TR press.princeton.edu Jacket image courtesy of Shutterstock; design by Lorraine Betz Doneker All Rights Reserved Library of Congress Cataloging-in-Publication Data Names: Holden, Joshua, 1970– author. Title: The mathematics of secrets : cryptography from Caesar ciphers to digital encryption / Joshua Holden. Description: Princeton : Princeton University Press, [2017] | Includes bibliographical references and index. Identifiers: LCCN 2016014840 | ISBN 9780691141756 (hardcover : alk. paper) Subjects: LCSH: Cryptography—Mathematics. | Ciphers. | Computer security. Classification: LCC Z103 .H664 2017 | DDC 005.8/2—dc23 LC record available at https://lccn.loc.gov/2016014840 British Library Cataloging-in-Publication Data is available This book has been composed in Linux Libertine Printed on acid-free paper. ∞ Printed in the United States of America 13579108642 To Lana and Richard for their love and support CONTENTS Preface xi Acknowledgments xiii Introduction to Ciphers and Substitution 1 1.1 Alice and Bob and Carl and Julius: Terminology and Caesar Cipher 1 1.2 The Key to the Matter: Generalizing the Caesar Cipher 4 1.3 Multiplicative Ciphers 6 -

Polish Mathematicians Finding Patterns in Enigma Messages
Fall 2006 Chris Christensen MAT/CSC 483 Machine Ciphers Polyalphabetic ciphers are good ways to destroy the usefulness of frequency analysis. Implementation can be a problem, however. The key to a polyalphabetic cipher specifies the order of the ciphers that will be used during encryption. Ideally there would be as many ciphers as there are letters in the plaintext message and the ordering of the ciphers would be random – an one-time pad. More commonly, some rotation among a small number of ciphers is prescribed. But, rotating among a small number of ciphers leads to a period, which a cryptanalyst can exploit. Rotating among a “large” number of ciphers might work, but that is hard to do by hand – there is a high probability of encryption errors. Maybe, a machine. During World War II, all the Allied and Axis countries used machine ciphers. The United States had SIGABA, Britain had TypeX, Japan had “Purple,” and Germany (and Italy) had Enigma. SIGABA http://en.wikipedia.org/wiki/SIGABA 1 A TypeX machine at Bletchley Park. 2 From the 1920s until the 1970s, cryptology was dominated by machine ciphers. What the machine ciphers typically did was provide a mechanical way to rotate among a large number of ciphers. The rotation was not random, but the large number of ciphers that were available could prevent depth from occurring within messages and (if the machines were used properly) among messages. We will examine Enigma, which was broken by Polish mathematicians in the 1930s and by the British during World War II. The Japanese Purple machine, which was used to transmit diplomatic messages, was broken by William Friedman’s cryptanalysts. -
Cipher Disk A
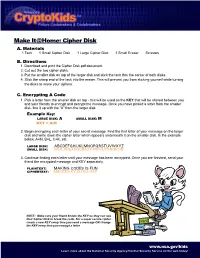
Make It@Home: Cipher Disk A. Materials 1 Tack 1 Small Cipher Disk 1 Large Cipher Disk 1 Small Eraser Scissors B. Directions 1. Download and print the Cipher Disk.pdf document. 2. Cut out the two cipher disks. 3. Put the smaller disk on top of the larger disk and stick the tack thru the center of both disks. 4. Stick the sharp end of the tack into the eraser. This will prevent you from sticking yourself while turning the disks to make your ciphers. C. Encrypting A Code 1. Pick a letter from the smaller disk on top - this will be used as the KEY that will be shared between you and your friends to encrypt and decrypt the message. Once you have picked a letter from the smaller disk, line it up with the “A” from the larger disk. Example Key: LARGE DISK: A SMALL DISK: M KEY = A:M 2. Begin encrypting each letter of your secret message. Find the first letter of your message on the larger disk and write down the cipher letter which appears underneath it on the smaller disk. In the example below, A=M, B=L, C=K, etc. LARGE DISK: ABCDEFGHIJKLMNOPQRSTUVWXYZ SMALL DISK: MLKJIHGFEDCBAZYXWVUTSRQPON 3. Continue finding each letter until your message has been encrypted. Once you are finished, send your friend the encrypted message and KEY seperately. PLAINTEXT: MAKING CODES IS FUN CIPHERTEXT: AMCEZG KYJIU EU HSZ NOTE: Make sure your friend knows the KEY so they can use their Cipher Disk to break the code. For a super secure cipher, create a new KEY every time you send a message OR change the KEY every time you encrypt a letter. -

Can You Keep a Secret?
Codes and Ciphers 20 Can You Keep a Secret? Codes and ciphers have been around just about as long as there has been written language. The ability to communicate in secret – as well as the ability to peer into the secret communications of others – has been central to a surprising number of major world events throughout history, often with nations as well as lives hanging in the balance. A word first about the difference between a code and a cipher: • A code is a secret language used to disguise the meaning of a message. The simplest form is a “jargon code,” where a particular phrase corresponds to a previously defined message. “The milkman comes in the morning,” for example, could mean “the invasion begins at dawn.” • A cipher conceals what is referred to as a “plaintext” message by substituting (a “substitu- tion cipher”) and/or scrambling (a “transposition cipher”) the letters. As we shall see later, a simple substitution cipher may encrypt the message “Call me tomorrow morning” as “FDO OPH WRP RUU RZP RUQ LQJ.” For our purposes, we will use such general terms as “code,” Cryptography, sometimes called “cryptology,” is “code breaker,” “encryp- tion” and “decryption” to from the Greek, meaning “hidden writing,” and its refer both to codes and ci- use has been documented for over 2,000 years. phers, rather than repeatedly drawing the distinction between the two. Hidden Writing Cryptography, sometimes called “cryptology,” is from the Greek, meaning “hidden writing” and its use has been documented for over 2,000 years. From the beginning, codes have always been of greatest use in matters of war and diplomacy. -

The Battle Over Pearl Harbor: the Controversy Surrounding the Japanese Attack, 1941-1994
W&M ScholarWorks Dissertations, Theses, and Masters Projects Theses, Dissertations, & Master Projects 1995 The Battle Over Pearl Harbor: The Controversy Surrounding the Japanese Attack, 1941-1994 Robert Seifert Hamblet College of William & Mary - Arts & Sciences Follow this and additional works at: https://scholarworks.wm.edu/etd Part of the United States History Commons Recommended Citation Hamblet, Robert Seifert, "The Battle Over Pearl Harbor: The Controversy Surrounding the Japanese Attack, 1941-1994" (1995). Dissertations, Theses, and Masters Projects. Paper 1539625993. https://dx.doi.org/doi:10.21220/s2-5zq1-1y76 This Thesis is brought to you for free and open access by the Theses, Dissertations, & Master Projects at W&M ScholarWorks. It has been accepted for inclusion in Dissertations, Theses, and Masters Projects by an authorized administrator of W&M ScholarWorks. For more information, please contact [email protected]. THE BATTLE OVER PEARL HARBOR The Controversy Surrounding the Japanese Attack, 1941-1994 A Thesis Presented to The Faculty of the Department of History The College of William and Mary in Virginia In Partial Fulfillment Of the Requirements for the Degree of Master of Arts by Robert S. Hamblet 1995 APPROVAL SHEET This thesis is submitted in partial fulfillment of the requirements for the degree of Master of Arts '-{H JxijsJr 1. Author Approved, November 1995 d(P — -> Edward P. CrapoII Edward E. Pratt TABLE OF CONTENTS Page ACKNOWLEDGEMENTS......................................................................iv ABSTRACT..............................................................................................v -

Vigenere Cryptography
Fall 2006 Chris Christensen MAT/CSC 483 Cryptography of the Vigenère Cipher Cryptanalysis is based upon finding the ghosts of patterns of the plaintext. We have seen that an important technique of doing this is frequency analysis. So, cryptographers try to develop ciphers that are not easily attacked by frequency analysis. There are two basic ways to do this: use more than one ciphertext alphabet or encrypt more than one letter in a block. First, we will consider using more than one cipher text alphabet. Simple substitution ciphers, Caesar ciphers, multiplicative ciphers, and affine ciphers are all examples of monoalphabetic ciphers – only one ciphertext alphabet is used. Even if the original word lengths are concealed and the substitution alphabet is random, it is possible to find a solution by using frequency data, repetition patterns and information about the way letters combine with one another. What makes the solution possible is the fact that a given plain language letter is always represented by the same cipher letter. As a consequence, all the properties of plain language such as frequencies and combinations are carried over into the cipher and may be utilized for solution. In effect we could say that all such properties are invariant except that the names of the letters have been changed. It would seem then that one way to obtain greater security would be to use more than one alphabet in enciphering a message. The general system could be one that uses a number of different alphabets for encipherment, with an understanding between correspondents of the order in which the alphabets are to be used.