Hardening Network Devices
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

List of TCP and UDP Port Numbers - Wikipedia, the Free Encyclopedia 6/12/11 3:20 PM
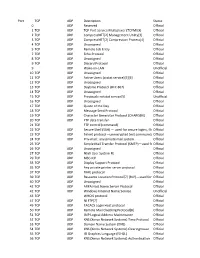
List of TCP and UDP port numbers - Wikipedia, the free encyclopedia 6/12/11 3:20 PM List of TCP and UDP port numbers From Wikipedia, the free encyclopedia (Redirected from TCP and UDP port numbers) This is a list of Internet socket port numbers used by protocols of the Transport Layer of the Internet Protocol Suite for the establishment of host-to-host communications. Originally, these port numbers were used by the Transmission Control Protocol (TCP) and the User Datagram Protocol (UDP), but are used also for the Stream Control Transmission Protocol (SCTP), and the Datagram Congestion Control Protocol (DCCP). SCTP and DCCP services usually use a port number that matches the service of the corresponding TCP or UDP implementation if they exist. The Internet Assigned Numbers Authority (IANA) is responsible for maintaining the official assignments of port numbers for specific uses.[1] However, many unofficial uses of both well-known and registered port numbers occur in practice. Contents 1 Table legend 2 Well-known ports: 0–1023 3 Registered ports: 1024–49151 4 Dynamic, private or ephemeral ports: 49152–65535 5 See also 6 References 7 External links Table legend Color coding of table entries Official Port/application combination is registered with IANA Unofficial Port/application combination is not registered with IANA Conflict Port is in use for multiple applications (may be official or unofficial) Well-known ports: 0–1023 The port numbers in the range from 0 to 1023 are the well-known ports. They are used by system processes that provide widely-used types of network services. -
Automotive Ethernet: the Definitive Guide
Automotive Ethernet: The Definitive Guide Charles M. Kozierok Colt Correa Robert B. Boatright Jeffrey Quesnelle Illustrated by Charles M. Kozierok, Betsy Timmer, Matt Holden, Colt Correa & Kyle Irving Cover by Betsy Timmer Designed by Matt Holden Automotive Ethernet: The Definitive Guide. Copyright © 2014 Intrepid Control Systems. All rights reserved. No part of this work may be reproduced or transmitted in any form or by any means, electronic or mechanical, including photocopying, recording, or by any information storage or retrieval system, without the prior written permission of the copyright owner and publisher. Printed in the USA. ISBN-10: 0-9905388-0-X ISBN-13: 978-0-9905388-0-6 For information on distribution or bulk sales, contact Intrepid Control Systems at (586) 731-7950. You can purchase the paperback or electronic version of this book at www.intrepidcs.com or on Amazon. We’d love to hear your feedback about this book—email us at [email protected]. Product and company names mentioned in this book may be the trademarks of their respective owners. Rather than use a trademark symbol with every occurence of a trademarked name, we are using the names only in an editorial fashion and to the benefit of the trademark owner, with no intention of infringement of the trademark. The information in this book is distributed on an “As Is” basis, without warranty. While every precaution has been taken in the preparation of this book, neither the authors nor Intrepid Control Systems shall have any liability to any person or entity with respect to any loss or damage caused or alleged to be caused directly or indirectly by the information contained in this book. -

Edition with Romkey, April 16, 1986 (PDF)
PC/IP User's Guide MASSACHUSETTS INSTITUTE OF TECHNOLOGY Laboratory For Computer Science Network programs based on the DoD Internet Protocol for the mM Personal Computer PC/~ release or March, 1986; document updated Aprill4, 1986 by: Jerome H. Saltzer John L. Romkey .• Copyright 1984, 1985, 1986 by the Massachusetts Institute or Technology Permission to use, copy, modlt'y, and distribute these programs and their documentation ror any purpose and without ree ls hereby granted, provided that this copyright and permission notice appear on all copies and supporting documentation, the name or M.I.T. not be used in advertising or publlclty pertalnlng to dlstrlbutlon or the programs without written prior permission, and notice be glven in supporting documentation that copying and distribution ls by permlsslon or M.I.T. M.I.T. makes no representations about the suitablllty or this software for any purpose. It is provided "as ls" without express or Implied warranty. - ii - CREDITS The PC/IP packages are bullt on the work of many people in the TCP/IP community, both at M.I.T. and elsewhere. Following are some of the people who directly helped in the creation of the packages. Network environment-John L. Romkey Terminal emulator and customizer-David A. Bridgham Inltlal TFTP-Kari D. Wright Inltlal telnet-Louls J. Konopelskl Teinet model-David D. Clark Tasking package-Larry W. Allen Development system-Christopher J. Terman Development environment-Wayne C. Gramlich Administrative Assistant-Muriel Webber October 3, 1985. This document is in cover .mss - iii- - iv Table of Contents 1. Overview of PC/IP network programs 1 1.1. -

List of TCP and UDP Port Numbers from Wikipedia, the Free Encyclopedia
List of TCP and UDP port numbers From Wikipedia, the free encyclopedia This is a list of Internet socket port numbers used by protocols of the transport layer of the Internet Protocol Suite for the establishment of host-to-host connectivity. Originally, port numbers were used by the Network Control Program (NCP) in the ARPANET for which two ports were required for half- duplex transmission. Later, the Transmission Control Protocol (TCP) and the User Datagram Protocol (UDP) needed only one port for full- duplex, bidirectional traffic. The even-numbered ports were not used, and this resulted in some even numbers in the well-known port number /etc/services, a service name range being unassigned. The Stream Control Transmission Protocol database file on Unix-like operating (SCTP) and the Datagram Congestion Control Protocol (DCCP) also systems.[1][2][3][4] use port numbers. They usually use port numbers that match the services of the corresponding TCP or UDP implementation, if they exist. The Internet Assigned Numbers Authority (IANA) is responsible for maintaining the official assignments of port numbers for specific uses.[5] However, many unofficial uses of both well-known and registered port numbers occur in practice. Contents 1 Table legend 2 Well-known ports 3 Registered ports 4 Dynamic, private or ephemeral ports 5 See also 6 References 7 External links Table legend Official: Port is registered with IANA for the application.[5] Unofficial: Port is not registered with IANA for the application. Multiple use: Multiple applications are known to use this port. Well-known ports The port numbers in the range from 0 to 1023 are the well-known ports or system ports.[6] They are used by system processes that provide widely used types of network services. -

TCP/IP Explained
TCP/IP Explained PHILIP MILLER DIGITAL PRESS Boston Oxford Johannesburg Melbourne New Delhi Singapore Table of Contents Preface xvii Chapter 1 - Introduction 1 1.1 What is TCP/IP? 1 1.1.1 A Brief History of TCP/IP 2 1.1.2 The Internet Protocol Suite 3 1.2 The Internet 5 1.2.1 The Growth of the Internet 6 1.3 Summary 9 Chapter 2 - Standardization 11 2.1 The Internet Architecture Board 11 2.1.1 The Internet Engineering Task Force 12 2.1.2 The Internet Research Task Force 13 2.2 Internet Protocol Standards 13 2.2.1 Protocol States 14 2.2.2 Protocol Status 16 2.2.3 The Request For Comments (RFC) 16 2.3 Internet Protocol Architecture 17 2.3.1 The Open Systems Interconnection (OSI) Model 18 2.3.2 The OSI Model and LANs 20 2.3.3 The Internet Protocol Suite Model 23 2.4 A Comparison of Major Architectures 25 2.5 Summary 26 Chapter 3 - An Overview of Network Technologies and Relay Systems 27 3.1 Ethernet and IEEE 802.3 27 3.1.1 802.3 Specifications 27 3.1.2 Ethernet/802.3 Frame Structure 30 3.1.3 Ethernet/802.3 Operation 32 3.2 Token Ring 33 3.2.1 802.5 Specifications 34 3.2.2 802.5 Frame Structure 36 3.2.3 802.5 Operation 38 3.3 Fibre Distributed Data Interface (FDDI) 39 3.3.1 FDDI Specifications 41 3.3.2 FDDI Frame Structure 42 3.3.3 FDDI Operation 43 3.4 Relay Systems 43 3.4.1 Repeaters 44 3.4.2 Bridges 45 3.5 WAN Links 50 3.6 Summary 51 Chapter 4 - Internet Addressing 53 4.1 The Need for an Addressing Scheme 53 4.2 Internet Addressing 54 4.2.1 Dotted Decimal Notation 55 4.2.2 Identifying IP Addresses and Rules 56 4.2.3 Choosing the Right Addressing -
Network Working Group J. Postel Request for Comments: 840 ISI April 1983
Network Working Group J. Postel Request for Comments: 840 ISI April 1983 Official Protocols This RFC identifies the documents specifying the official protocols used in the Internet. Annotations identify any revisions or changes planned. To first order, the official protocols are those in the Internet Protocol Transition Workbook (IPTW) dated March 1982. There are several protocols in use that are not in the IPTW. A few of the protocols in the IPTW have been revised these are noted here. In particular, the mail protocols have been revised and issued as a volume titled "Internet Mail Protocols" dated November 1982. There is a volume of protocol related information called the Internet Protocol Implementers Guide (IPIG) dated August 1982. A few of the protocols (in particular the Telnet Options) have not been revised for many years, these are found in the old ARPANET Protocol Handbook (APH) dated January 1978. This document is organized as a sketchy outline. The entries are protocols (e.g., Transmission Control Protocol). In each entry there are notes on status, specification, comments, other references, dependencies, and contact. The status is one of: required, recommended, elective, or experimental. The specification identifies the protocol defining documents. The comments describe any differences from the specification or problems with the protocol. The other references identify documents that comment on or expand on the protocol. The dependencies indicate what other protocols are called upon by this protocol. The contact indicates a person -
ECHO Through EXEC
ECHO through EXEC • ECHO, page 3 • EDONKEY-STATIC, page 4 • EDONKEY, page 5 • EGP, page 6 • EIGRP, page 7 • ELCSD, page 8 • EMBL-NDT, page 9 • EMCON, page 10 • EMFIS-CNTL, page 11 • EMFIS-DATA, page 12 • ENCAP, page 13 • ENCRYPTED-BITTORRENT, page 14 • ENCRYPTED-EMULE, page 15 • ENTOMB, page 16 • ENTRUST-AAAS, page 17 • ENTRUST-AAMS, page 18 • ENTRUST-ASH, page 19 • ENTRUST-KMSH, page 20 • ENTRUST-SPS, page 21 • EPMAP, page 22 • ERPC, page 23 • ESCP-IP, page 24 • ESIGNAL, page 25 • ESPN-BROWSING, page 26 NBAR2 Protocol Pack 7.0.0 1 ECHO through EXEC • ESPN-VIDEO, page 27 • ESRO-EMSDP, page 28 • ESRO-GEN, page 29 • ETHERIP, page 30 • EUDORA-SET, page 31 • EXCHANGE, page 32 • EXEC, page 33 NBAR2 Protocol Pack 7.0.0 2 ECHO through EXEC ECHO ECHO Name/CLI Keyword echo Full Name Echo Protocol Description Echo is a protocol that is used for debugging and measurement. It works by sending back all the data that was received from the source. The protocol works on TCP and UDP, typically on port 7. Reference http://www.faqs.org/rfcs/rfc862.html Global ID L4:7 ID 101 Known Mappings UDP Port 7 TCP Port 7 IP Protocol - IP Version IPv4 Support Yes IPv6 Support Yes Application Group other Category net-admin Sub Category network-management P2P Technology No Encrypted No Tunnel No Underlying Protocols - NBAR2 Protocol Pack 7.0.0 3 ECHO through EXEC EDONKEY-STATIC EDONKEY-STATIC Name/CLI Keyword edonkey-static Full Name eDonkey Description eDonkey is peer-to-peer file sharing adopted to share large files. -

Port Ranges Traffic Analysis
Simon Owens Port Ranges • Ports 0 to 1023 are Well-Known Ports. • Ports 1024 to 49151 are Registered Ports (often registered by a software developer to designate a particular port for their application) • Ports 49152 to 65535 are Public Ports. Traffic Analysis - Wireshark Configure Name Resolution 1. Make a new profile 2. Make a “hosts” file with format “ip hostname” 3. Place that “hosts” file in the ~/.config/wireshark/configprofilename/ folder 4. open pcap file, select your configuration profile, and ensure “view>>name resolution>>resolve network/transport address names” is checked Configure Ports 1. Go to “Edit>>preferences>>columns” and add src and dst ports to the display Figuring out what multi-cast goes too 1. Fill out “hosts” and “services” file if you can 2. Click on various multi-cast products – generally the parameters will identify what the application is with a version or the company that made it. Query for Common Ports • tcp.dstport >= 0 and tcp.dstport <= 10000 || tftp || dns Saving off filters to make capture smaller 1. Apply a filter 2. Click “File>> Export Specified Packets” then save them to a file Search for Strings • Edit >> find packet Extracting files • file >> export objects Find Hashes • net-creds.py file.pcap Changing Parameters in the Packets Simon Owens • Port Scan Netdiscover -r <ip-range> make sure you know everything on network IP=insert mkdir $IP Masscan: • masscan -p0-65535 $IP --banners -oG $IP/masscan_$IP.grep Nmap: • Nmap -sV -T4 $IP -oN $IP/normalNmap.txt • nmap -v -sS -T4 -A --script=vuln --host-timeout 336h -p 0-65535 $IP -oA $IP/TCPscan_$IP • nmap -v -sU -T4 -A --script=vuln --host-timeout 336h -p 0-65535 $IP -oA $IP/UDPscan_$IP General Services: • 9/tcp - Discard o Discard Protocol - https://www.exploit-db.com/exploits/19555 The Discard Protocol is a service in the Internet Protocol Suite defined in RFC 863. -

SWMME-3000 Series Modular Industrial Ethernet Switch (EN)
SWMME-3000 Series Modular Industrial Ethernet Switch Performance Features ● Modular industrial switches with 3 slot modules of flexible configuration and high performance, and all modules support on-line upgrade ● Supporting Ethernet ring and multiple self-healing rings with the fail-over time in every node less than 5ms and the network self-healing time less than 50ms (typical value) ● Supporting IEC62439-2 based MRP ● Supporting IEC62439-3 based PRP, and HSR ● Any two ports can establish a self-healing ring and support multiple independent self-healing rings CXR SWMME series - the modular ● With function of data packet dropout protection and quick recover from network failure. industrial Ethernet switches provide multi-slots and ● Multi-Protocol L3 routing meets the requirement of many integrated forms including gigabit network, private network. content switching, PRP/HSR module. And all the ● Support various multicast protocols and strong safety protection mechanism modules support on-line upgrade. All modules in ● Provide bandwidth service with different levels in SWMME series are equipped with unified optical Ethernet service by speed limiting and traffic modules and software, forming a system that can shaping in QoS of layer 2 ● adapt to future develop-ment. With the unified Support function of the static and dynamic allocation as well as limitation of CPU and real-time monitor operation, the equipment can make better use of the key operating parameters, including CPU themselves. series adopt ardware-based utilization rate, RAM, supply voltage and mainboard SWMME h voltage. algorithm that ensures the fail-over time in every ● SWMME series have a full set of professional net- node less than 5ms and the network self-healing work management and monitoring and alarm system. -

VPN Ipsec Tunnels with Cisco ASA/Asav VTI on Oracle Cloud Infrastructure
Deploying VPN IPSec Tunnels with Cisco ASA/ASAv VTI on Oracle Cloud Infrastructure O R A C L E SOLUTION GUIDE | M A R C H 2 0 1 8 | VERSION 1.1 Table of Contents Overview 4 Scope and Assumptions 4 VPN IPSec Tunnel Concepts 5 CPE Configuration 5 General Requirements for Connecting to the Oracle Cloud Infrastructure DRG via IPSec 6 Establish the IKE Security Association Using Pre-Shared Keys 6 Establish the IPSec Security Association 6 Use AES 256-Bit Encryption 6 Use the SHA-1 or SHA-256 Hashing Function 6 Use Diffie-Hellman with Perfect Forward Secrecy 7 IPSec Dead Peer Detection 7 Bind Tunnel to Logical Interface (Route-Based VPN) 7 Fragment IP Packets Before Encryption 8 Recommendations for TCP Maximum Segment Size and DF Flags 8 Data Lifetime Rekey Interval 9 VPN IPSec Tunnels on Oracle Cloud Infrastructure 9 Key Components of VPN IPSec Tunnels on OCI 10 Access Requirements for VPN IPSec Tunnels Configuration 13 Configure the VPN IPSec 14 Step 1: Create a VCN 15 Step 2: Create the DRG 16 Step 3: Attach the DRG to the VCN 17 Step 4: Modify the Default Route Table for the VCN 17 Step 6: Edit the Default Security List for the Subnet 18 2 | DEPLOYING VPN IPSEC TUNNELS WITH CISCO ASA/ASAV VTI ON ORACLE CLOUD INFRASTRUCTURE Step 7: Create a Subnet 19 Step 8: Create a CPE Object 21 Step 9: Create an IPSec Tunnel Between the DRG and CPE 22 Step 10: Verify the IPSec Tunnels 23 Summary 24 Configure the ASA/ASAv On-Premises Device 25 Step 1: Note All the Values Used in the ASA/ASAv Configuration 25 Step 2: Configure the IKE and IPSec Policy and IPSec Profile 26 Step 3: Set Up Some IPSec and Tunnel Friendly Parameters 27 Step 4: Configure the Tunnel Group 28 Step 5: Configure the VTI 28 Step 6: Configure the Static Routes 29 Step 7: Verify That the Tunnels Are Up on Oracle Cloud Infrastructure 31 Sample ASA/ASAv Configuration File from this Document 31 Conclusion 33 3 | DEPLOYING VPN IPSEC TUNNELS WITH CISCO ASA/ASAV VTI ON ORACLE CLOUD INFRASTRUCTURE Overview This guide provides step-by-step instructions for configuring VPN IPSec tunnels on Oracle Cloud Infrastructure. -
Official 2 TCP UDP Compr
Port TCP UDP Description Status 0 UDP Reserved Official 1 TCP UDP TCP Port Service Multiplexer (TCPMUX) Official 2 TCP UDP CompressNET[2] Management Utility[3] Official 3 TCP UDP CompressNET[2] Compression Process[4] Official 4 TCP UDP Unassigned Official 5 TCP UDP Remote Job Entry Official 7 TCP UDP Echo Protocol Official 8 TCP UDP Unassigned Official 9 TCP UDP Discard Protocol Official 9 UDP Wake-on-LAN Unofficial 10 TCP UDP Unassigned Official 11 TCP UDP Active Users (systat service)[5][6] Official 12 TCP UDP Unassigned Official 13 TCP UDP Daytime Protocol (RFC 867) Official 14 TCP UDP Unassigned Official 15 TCP UDP Previously netstat service[5] Unofficial 16 TCP UDP Unassigned Official 17 TCP UDP Quote of the Day Official 18 TCP UDP Message Send Protocol Official 19 TCP UDP Character Generator Protocol (CHARGEN) Official 20 TCP UDP FTP data transfer Official 21 TCP FTP control (command) Official 22 TCP UDP Secure Shell (SSH) — used for secure logins, file Officialtransfers (scp, sftp) and port forwarding 23 TCP UDP Telnet protocol—unencrypted text communicationsOfficial 24 TCP UDP Priv-mail : any private mail system. Official 25 TCP Simple Mail Transfer Protocol (SMTP)—used forOfficial e-mail routing between mail servers 26 TCP UDP Unassigned Official 27 TCP UDP NSW User System FE Official 29 TCP UDP MSG ICP Official 33 TCP UDP Display Support Protocol Official 35 TCP UDP Any private printer server protocol Official 37 TCP UDP TIME protocol Official 39 TCP UDP Resource Location Protocol*7+ (RLP)—used for determiningOfficial the location -
The Definitive Guide to HTML5 Websocket // Example Websocket Server
For your convenience Apress has placed some of the front matter material after the index. Please use the Bookmarks and Contents at a Glance links to access them. Contents at a Glance Foreword ���������������������������������������������������������������������������������������� xiii About the Authors ���������������������������������������������������������������������������� xv About the Technical Reviewer ������������������������������������������������������� xvii Acknowledgments �������������������������������������������������������������������������� xix ■ Chapter 1: Introduction to HTML5 WebSocket �������������������������������� 1 ■ Chapter 2: The WebSocket API ����������������������������������������������������� 13 ■ Chapter 3: The WebSocket Protocol ��������������������������������������������� 33 ■ Chapter 4: Building Instant Messaging and Chat over WebSocket with XMPP ��������������������������������������������������������� 61 ■ Chapter 5: Using Messaging over WebSocket with STOMP ���������� 85 ■ Chapter 6: VNC with the Remote Framebuffer Protocol ������������� 109 ■ Chapter 7: WebSocket Security �������������������������������������������������� 129 ■ Chapter 8: Deployment Considerations �������������������������������������� 149 ■ Appendix A: Inspecting WebSocket Traffic ��������������������������������� 163 ■ Appendix B: WebSocket Resources �������������������������������������������� 177 Index ���������������������������������������������������������������������������������������������� 183 v CHAPTER 1 Introduction