More Than a Fair Share: Network Data Remanence Attacks Against Secret Sharing-Based Schemes
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Algebraic Cryptanalysis.Pdf
EEAlgebraic E Cryptanalysis Gregory V. Bard Algebraic Cryptanalysis Gregory V. Bard Department of Mathematics Fordham University Bronx, NY 10458 USA [email protected] ISBN 978-0-387-88756-2 e-ISBN 978-0-387-88757-9 DOI 10.1007/978-0-387-88757-9 Springer Dordrecht Heidelberg London New York Library of Congress Control Number: 2009929845 © Springer Science+ Business Media, LLC 2009 All rights reserved. This work may not be translated or copied in whole or in part without the written permission of the publisher (Springer Science+Business Media, LLC, 233 Spring Street, New York, NY 10013, USA), except for brief excerpts in connection with reviews or scholarly analysis. Use in connection with any form of information storage and retrieval, electronic adaptation, computer software, or by similar or dissimilar methodology now known or hereafter developed is forbidden. The use in this publication of trade names, trademarks, service marks, and similar terms, even if they are not identified as such, is not to be taken as an expression of opinion as to whether or not they are subject to proprietary rights. Printed on acid-free paper Springer is part of Springer Science+Business Media (www.springer.com) Preface Algebraic Cryptanalysis is the process of breaking codes by solving polynomial systems of equations. In some ways this book began when the author began to ex- plore cryptanalysis as a beginning graduate student, and realized with frustration that no book whatsoever existed on the topic. Since that time, some books have been written about Linear Cryptanalysis or Differential Cryptanalysis (e.g. [211] and [214] cover both), but none on Algebraic Cryptanalysis, which is a rich and growing field. -

The Substitution Cipher Chaining Mode
THE SUBSTITUTION CIPHER CHAINING MODE Mohamed Abo El-Fotouh and Klaus Diepold Institute for Data Processing (LDV), Technische Universitat¨ Munchen¨ (TUM), 80333 Munich, Germany Keywords: Modes of operation, SCC, disk encryption, AES. Abstract: In this paper, we present a new tweakable narrow-block mode of operation, the Substitution Cipher Chaining mode (SCC), that can be efficiently deployed in disk encryption applications. SCC is characterized by its high throughout compared to the current solutions and it can be parallelized. We used this mode to modify Windows Vista’s disk encryption algorithm, to offer some parallelism in its original implementation and to improve its diffusion properties. 1 INTRODUCTION 2001). Bear, Lion and Beast are considered to be slow, as they process the data through multiple passes. And Mercy was broken in (Fluhrer, 2002). The other In todays computing environment, there are many method is to let a block cipher like the Advanced en- threats to the confidentiality of information stored on cryption standard AES (Daemen and Rijmen, 1998) end user devices, such as personal computers, con- (with 16-bytes as a block size) to process the data sumer devices (e.g. PDA), and removable storage me- within a mode of operation. These modes of operation dia like (e.g., USB or external hard drive). A common can be divided into two main classes the narrow-block threat against end user devices is device loss or theft, and wide-block modes. The narrow-block modes op- that can lead to identity theft and other frauds. Some- erate on relatively small portions of data (typically one with physical access to a device has many op- 16-bytes when AES is used), while the wide-block tions for attempting to view or copy the information modes encrypt or decrypt a whole sector (typically stored on that device. -

The QARMA Block Cipher Family
The QARMA Block Cipher Family Almost MDS Matrices Over Rings With Zero Divisors, Nearly Symmetric Even-Mansour Constructions With Non-Involutory Central Rounds, and Search Heuristics for Low-Latency S-Boxes Roberto Avanzi Qualcomm Product Security, Munich, Germany [email protected], [email protected] Abstract. This paper introduces QARMA, a new family of lightweight tweakable block ciphers targeted at applications such as memory encryption, the generation of very short tags for hardware-assisted prevention of software exploitation, and the con- struction of keyed hash functions. QARMA is inspired by reflection ciphers such as PRINCE, to which it adds a tweaking input, and MANTIS. However, QARMA differs from previous reflector constructions in that it is a three-round Even-Mansour scheme instead of a FX-construction, and its middle permutation is non-involutory and keyed. We introduce and analyse a family of Almost MDS matrices defined over a ring with zero divisors that allows us to encode rotations in its operation while maintaining the minimal latency associated to {0, 1}-matrices. The purpose of all these design choices is to harden the cipher against various classes of attacks. We also describe new S-Box search heuristics aimed at minimising the critical path. QARMA exists in 64- and 128-bit block sizes, where block and tweak size are equal, and keys are twice as long as the blocks. We argue that QARMA provides sufficient security margins within the constraints de- termined by the mentioned applications, while still achieving best-in-class latency. Implementation results on a state-of-the art manufacturing process are reported. -

DIVINE MERCY SUNDAY 2 Catholic Times April 23, 2017
CATHOLIC APRIL 23, 2017 SECOND WEEK OF EASTER VOLUME 66:30 DIOCESE OF COLUMBUS A journal of Catholic life in Ohio DIVINE MERCY SUNDAY 2 Catholic Times April 23, 2017 The Editor’s Notebook Honoring Our Blessed Mother’s Fatima Appearances An Issue of Trust By David Garick, Editor A few years ago, I was working for But trust is es- a state government agency, and the sential to our senior staff got together for a daylong souls. The key session of team-building. It took place to trust is faith, at one of those wilderness camp places and that is not that specialize in putting ordinary of- something you go out and get on your fice workers into primitive outdoor own. St. Paul says “Faith is the real- challenges that can be solved only by ization of things hoped for and evi- teamwork. dence of things not seen” (Hebrews One of the first and simplest chal- 11:1). Faith is a gift of the Holy Spirit lenges was to stand with eyes closed and through this gift, this faith, we can and arms folded across one’s chest. trust in the one person who will catch A co-worker was positioned behind us, no matter how hard or how often you and you were to allow yourself we fall. That is Our Lord Jesus Christ. to fall backwards, relying on the co- This week’s Catholic Times looks at worker to catch you. The idea is to devotions that have grown up around develop trust. It sounds simple. But Divine Mercy Sunday. -
Encryption Block Cipher
10/29/2007 Encryption Encryption Block Cipher Dr.Talal Alkharobi 2 Block Cipher A symmetric key cipher which operates on fixed-length groups of bits, termed blocks, with an unvarying transformation. When encrypting, a block cipher take n-bit block of plaintext as input, and output a corresponding n-bit block of ciphertext. The exact transformation is controlled using a secret key. Decryption is similar: the decryption algorithm takes n-bit block of ciphertext together with the secret key, and yields the original n-bit block of plaintext. Mode of operation is used to encrypt messages longer than the block size. 1 Dr.Talal Alkharobi 10/29/2007 Encryption 3 Encryption 4 Decryption 2 Dr.Talal Alkharobi 10/29/2007 Encryption 5 Block Cipher Consists of two algorithms, encryption, E, and decryption, D. Both require two inputs: n-bits block of data and key of size k bits, The output is an n-bit block. Decryption is the inverse function of encryption: D(E(B,K),K) = B For each key K, E is a permutation over the set of input blocks. n Each key K selects one permutation from the possible set of 2 !. 6 Block Cipher The block size, n, is typically 64 or 128 bits, although some ciphers have a variable block size. 64 bits was the most common length until the mid-1990s, when new designs began to switch to 128-bit. Padding scheme is used to allow plaintexts of arbitrary lengths to be encrypted. Typical key sizes (k) include 40, 56, 64, 80, 128, 192 and 256 bits. -
Cryptology: an Historical Introduction DRAFT
Cryptology: An Historical Introduction DRAFT Jim Sauerberg February 5, 2013 2 Copyright 2013 All rights reserved Jim Sauerberg Saint Mary's College Contents List of Figures 8 1 Caesar Ciphers 9 1.1 Saint Cyr Slide . 12 1.2 Running Down the Alphabet . 14 1.3 Frequency Analysis . 15 1.4 Linquist's Method . 20 1.5 Summary . 22 1.6 Topics and Techniques . 22 1.7 Exercises . 23 2 Cryptologic Terms 29 3 The Introduction of Numbers 31 3.1 The Remainder Operator . 33 3.2 Modular Arithmetic . 38 3.3 Decimation Ciphers . 40 3.4 Deciphering Decimation Ciphers . 42 3.5 Multiplication vs. Addition . 44 3.6 Koblitz's Kid-RSA and Public Key Codes . 44 3.7 Summary . 48 3.8 Topics and Techniques . 48 3.9 Exercises . 49 4 The Euclidean Algorithm 55 4.1 Linear Ciphers . 55 4.2 GCD's and the Euclidean Algorithm . 56 4.3 Multiplicative Inverses . 59 4.4 Deciphering Decimation and Linear Ciphers . 63 4.5 Breaking Decimation and Linear Ciphers . 65 4.6 Summary . 67 4.7 Topics and Techniques . 67 4.8 Exercises . 68 3 4 CONTENTS 5 Monoalphabetic Ciphers 71 5.1 Keyword Ciphers . 72 5.2 Keyword Mixed Ciphers . 73 5.3 Keyword Transposed Ciphers . 74 5.4 Interrupted Keyword Ciphers . 75 5.5 Frequency Counts and Exhaustion . 76 5.6 Basic Letter Characteristics . 77 5.7 Aristocrats . 78 5.8 Summary . 80 5.9 Topics and Techniques . 81 5.10 Exercises . 81 6 Decrypting Monoalphabetic Ciphers 89 6.1 Letter Interactions . 90 6.2 Decrypting Monoalphabetic Ciphers . -
Cryptography Lecture 1 Principles and History Course Book, Examination
Cryptography Lecture 1 Principles and history Course book, examination • 12 lectures • 4 lab sessions • Written exam • The first and third labs are online, supervision will be over Zoom • The second and fourth are on campus • Keep an eye out for instructions in lisam “Cryptography” is a Greek word that means “hidden writing” Used to hide message from someone, and sometimes prevent them from creating a new message Key Key Alice Encrypt Decrypt Bob Eve “Cryptography” is a Greek word that means “hidden writing” Used to hide message from someone, and sometimes prevent them from creating a new message Key Key Alice Encrypt Decrypt Bob Eve “Cryptography” is a Greek word that means “hidden writing” Used to hide message from someone, and sometimes prevent them from creating a new message Key Key Alice Sign Verify Bob Eve The message is written using an alphabet in some language • Egyptian hieroglyphs were unreadable until the Rosetta stone was found. This contained the same text in Ancient Egyptian hieroglyphs, in Demotic script, and in ancient Greek. • For example, “Nefer” meaning “good”, “beautiful” could be written or or or in a lot of other ways, like a picture of a horse • Non-standard = Encrypted? Not really. Terminology • The plaintext is the information in its normal form • The ciphertext or cryptogram is the transformed plaintext • The secret parameter for the encryption (known only to the sender and intended recipients) is called the key • The key decides how the transformation is done Kerckhoff’s principle • A cryptosystem should be secure even if everything about the system, except the key, is public knowledge. -

Meeting Mercy
A D E V O T I O N A L B Y H E I D I T A I meeting mercy S T O R I E S O F R E J E C T S & R E B E L S R E D E E M E D B Y M E R C Y Contents Patron Recognition.......................................................................1 Introduction..................................................................................2 Zacchaeus: The Sinner Who Was Seen.......................................4 The Followers Of Little Faith......................................................7 The Poor Widow Of Mighty Faith..............................................9 The Samaritan Woman Quenched By Living Water................11 The Sinful Woman Who Loved Much......................................13 The Family Jesus Loved..............................................................15 Mary: The Woman Who Wasted On Jesus................................17 The Adulterous Woman Shielded By Mercy............................21 The Unfaithful Friends He Loved To The End.......................24 Peter: The Coward Redeemed By Love....................................26 The Criminal Welcomed Into Paradise....................................29 Thomas: The Sceptic Who Touched God's Scars.....................31 Saul: The Good Guy Who Got It All Wrong.............................34 The Bleeding Woman Named A Daughter...............................37 Meet The Author........................................................................42 Become A Patron For Words Of Hope.....................................43 © 2020 Heidi Tai All Rights Reserved. WITH GRATITUDE -
Cryptography in Context
Cryptography in Context Cryptography in Context Gerard Tel iv Contents Contents v Preface ix 1 On the Secure Hash Algorithm family (Wouter Penard and Tim van Werkhoven) 1 1.1 Introduction . 1 1.2 Description of the SHA Algorithms . 4 1.3 Generic Attacks . 8 1.4 Specialized Attacks . 13 1.5 Implications of Attacks . 17 1.6 Conclusion . 17 2 Security and privacy of RFID tags (Jeroen van Wolffelaar) 19 2.1 RFID tags . 19 2.2 Case: Baja Beach Club . 20 2.3 Case: Biometric passports . 22 2.4 Case: OV-chipkaart . 24 2.5 Conclusions . 27 3 Xbox Securtity (Miloslav Valco) 29 3.1 Microsoft's Financial Gambles . 29 3.2 Andrew "bunnie" Huang . 31 3.3 RC4 . 33 3.4 Tiny Encryption Algorithm . 35 3.5 The Visor Hack . 36 3.6 Xbox Linux Project . 36 3.7 Discussion and conclusion . 37 4 Multiple Encryption (Ronald Chu & Mark Jeronimus) 39 4.1 Introduction . 39 4.2 definitions . 40 4.3 Known attacks . 40 4.4 Applications . 45 4.5 Summary and conclusions . 47 v vi Contents 5 Phishing (Marnix Kammer and Barbara Pieters) 49 5.1 Phishing and cryptography . 49 5.2 Forms of phishing . 50 5.3 Changes in human-computer interaction to prevent phishing . 53 5.4 Technical solutions to prevent phishing . 56 5.5 Summary and conclusions . 64 6 Electronic Voting 2.0 (Jeiel Schalkwijk) 67 6.1 The current state of voting machines . 67 6.2 Cryptographic systems . 70 6.3 ThreeBallot . 71 6.4 Moran and Naor's protocol . 72 6.5 Conclusion . -

Simpira V2: a Family of Efficient Permutations Using the AES Round
Simpira v2: A Family of Efficient Permutations Using the AES Round Function Shay Gueron1,2 and Nicky Mouha3,4,5 1 University of Haifa, Israel. 2 Intel Corporation, Israel Development Center, Haifa, Israel. 3 Dept. Electrical Engineering-ESAT/COSIC, KU Leuven, Leuven and iMinds, Ghent, Belgium. 4 Project-team SECRET, Inria, France. 5 National Institute of Standards and Technology, Gaithersburg, MD, USA. [email protected],[email protected] Abstract. This paper introduces Simpira, a family of cryptographic permutations that supports inputs of 128×b bits, whereb is a positive integer. Its design goal is to achieve high throughput on virtually all mod- ern 64-bit processors, that nowadays already have native instructions for AES. To achieve this goal, Simpira uses only one building block: the AES round function. Forb = 1, Simpira corresponds to 12-round AES withfixed round keys, whereas forb≥ 2, Simpira is a Generalized Feis- tel Structure (GFS) with anF -function that consists of two rounds of AES. We claim that there are no structural distinguishers for Simpira with a complexity below 2128, and analyze its security against a variety of attacks in this setting. The throughput of Simpira is close to the theo- retical optimum, namely, the number of AES rounds in the construction. For example, on the Intel Skylake processor, Simpira has throughput below 1 cycle per byte forb≤ 4 andb = 6. For larger permutations, where moving data in memory has a more pronounced effect, Simpira withb = 32 (512 byte inputs) evaluates 732 AES rounds, and performs at 824 cycles (1.61 cycles per byte), which is less than 13% off the theo- retical optimum. -
Adiantum: Length-Preserving Encryption for Entry-Level Processors
Adiantum: length-preserving encryption for entry-level processors Paul Crowley and Eric Biggers Google LLC {paulcrowley,ebiggers}@google.com Abstract. We present HBSH, a simple construction for tweakable length-preserving encryption which supports the fastest options for hashing and stream encryption for processors without AES or other crypto instructions, with a provable quadratic advantage bound. Our composition Adiantum uses NH, Poly1305, XChaCha12, and a single AES invocation. On an ARM Cortex-A7 processor, Adiantum decrypts 4096-byte messages at 10.6 cycles per byte, over five times faster than AES-256-XTS, with a constant-time implementation. We also define HPolyC which is simpler and has excellent key agility at 13.6 cycles per byte. Keywords: super-pseudorandom permutation · variable input length · tweakable encryption · disk encryption 1 Introduction Two aspects of disk encryption make it a challenge for cryptography. First, performance is critical; every extra cycle is a worse user experience, and on a mobile device a reduced battery life. Second, the ciphertext can be no larger than the plaintext: a sector-sized read or write to the filesystem must mean a sector-sized read or write to the underlying device, or performance will again suffer greatly (as well as, in the case of writes to flash memory, the life of the device). Nonce reuse is inevitable as there is nowhere to store a varying nonce, and there is no space for a MAC; thus standard constructions like AES-GCM are not an option and standard notions of semantic security are unachievable. The best that can be done under the circumstances is a “tweakable super-pseudorandom permutation”: an adversary with access to both encryption and decryption functions who can choose tweak and plaintext/ciphertext freely is unable to distinguish it from a family of independent random permutations. -
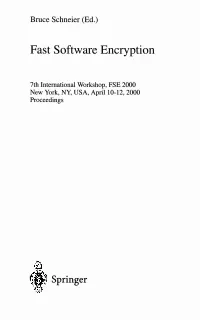
Fast Software Encryption
Bruce Schneier (Ed.) Fast Software Encryption 7th International Workshop, FSE 2000 New York, NY, USA, April 10-12, 2000 Proceedings Springer Table of Contents Specific Stream-Cipher Cryptanalysis Real Time Cryptanalysis of A5/1 on a PC...................................................... 1 Alex Biryukov, Adi Shamir, and David Wagner Statistical Analysis of the Alleged RC4 Keystream Generator...................... 19 Scott R. Fluhrer and David A. McGrew New Ciphers The Software-Oriented Stream Cipher SSC2.................................................... 31 Muxiang Zhang, Christopher Carroll, and Agnes Chan Mercy: A Fast Large Block Cipher for Disk Sector Encryption.................... 49 Paul Crowley AES Cryptanalysis 1 A Statistical Attack on RC6................................................................................ 64 Henri Gilbert, Helena Handschuh, Antoine Joux, and Serge Vaudenay Amplified Boomerang Attacks Against Reduced-Round MARS and Serpent 75 John Kelsey, Tadayoshi Kohno, and Bruce Schneier Correlations in RC6 with a Reduced Number of Rounds.............................. 94 Lars R. Knudsen and Willi Meier Block-Cipher Cryptanalysis 1 On the Interpolation Attacks on Block Ciphers................................................ 109 A.M. Youssef and G. Gong Stochastic Cryptanalysis of Crypton ..................................................................121 Marine Minier and Henri Gilbert Power Analysis Bitslice Ciphers and Power Analysis Attacks ....................................................134 Joan Daemen,