Twenty Years of Attacks on the RSA Cryptosystem Dan Boneh
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Public Key Cryptography And
PublicPublic KeyKey CryptographyCryptography andand RSARSA Raj Jain Washington University in Saint Louis Saint Louis, MO 63130 [email protected] Audio/Video recordings of this lecture are available at: http://www.cse.wustl.edu/~jain/cse571-11/ Washington University in St. Louis CSE571S ©2011 Raj Jain 9-1 OverviewOverview 1. Public Key Encryption 2. Symmetric vs. Public-Key 3. RSA Public Key Encryption 4. RSA Key Construction 5. Optimizing Private Key Operations 6. RSA Security These slides are based partly on Lawrie Brown’s slides supplied with William Stallings’s book “Cryptography and Network Security: Principles and Practice,” 5th Ed, 2011. Washington University in St. Louis CSE571S ©2011 Raj Jain 9-2 PublicPublic KeyKey EncryptionEncryption Invented in 1975 by Diffie and Hellman at Stanford Encrypted_Message = Encrypt(Key1, Message) Message = Decrypt(Key2, Encrypted_Message) Key1 Key2 Text Ciphertext Text Keys are interchangeable: Key2 Key1 Text Ciphertext Text One key is made public while the other is kept private Sender knows only public key of the receiver Asymmetric Washington University in St. Louis CSE571S ©2011 Raj Jain 9-3 PublicPublic KeyKey EncryptionEncryption ExampleExample Rivest, Shamir, and Adleman at MIT RSA: Encrypted_Message = m3 mod 187 Message = Encrypted_Message107 mod 187 Key1 = <3,187>, Key2 = <107,187> Message = 5 Encrypted Message = 53 = 125 Message = 125107 mod 187 = 5 = 125(64+32+8+2+1) mod 187 = {(12564 mod 187)(12532 mod 187)... (1252 mod 187)(125 mod 187)} mod 187 Washington University in -

Ch 13 Digital Signature
1 CH 13 DIGITAL SIGNATURE Cryptography and Network Security HanJung Mason Yun 2 Index 13.1 Digital Signatures 13.2 Elgamal Digital Signature Scheme 13.3 Schnorr Digital Signature Scheme 13.4 NIST Digital Signature Algorithm 13.6 RSA-PSS Digital Signature Algorithm 3 13.1 Digital Signature - Properties • It must verify the author and the date and time of the signature. • It must authenticate the contents at the time of the signature. • It must be verifiable by third parties, to resolve disputes. • The digital signature function includes authentication. 4 5 6 Attacks and Forgeries • Key-Only attack • Known message attack • Generic chosen message attack • Directed chosen message attack • Adaptive chosen message attack 7 Attacks and Forgeries • Total break • Universal forgery • Selective forgery • Existential forgery 8 Digital Signature Requirements • It must be a bit pattern that depends on the message. • It must use some information unique to the sender to prevent both forgery and denial. • It must be relatively easy to produce the digital signature. • It must be relatively easy to recognize and verify the digital signature. • It must be computationally infeasible to forge a digital signature, either by constructing a new message for an existing digital signature or by constructing a fraudulent digital signature for a given message. • It must be practical to retain a copy of the digital signature in storage. 9 Direct Digital Signature • Digital signature scheme that involves only the communication parties. • It must authenticate the contents at the time of the signature. • It must be verifiable by third parties, to resolve disputes. • Thus, the digital signature function includes the authentication function. -
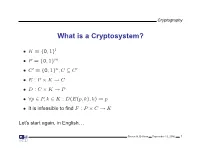
What Is a Cryptosystem?
Cryptography What is a Cryptosystem? • K = {0, 1}l • P = {0, 1}m • C′ = {0, 1}n,C ⊆ C′ • E : P × K → C • D : C × K → P • ∀p ∈ P, k ∈ K : D(E(p, k), k) = p • It is infeasible to find F : P × C → K Let’s start again, in English. Steven M. Bellovin September 13, 2006 1 Cryptography What is a Cryptosystem? A cryptosystem is pair of algorithms that take a key and convert plaintext to ciphertext and back. Plaintext is what you want to protect; ciphertext should appear to be random gibberish. The design and analysis of today’s cryptographic algorithms is highly mathematical. Do not try to design your own algorithms. Steven M. Bellovin September 13, 2006 2 Cryptography A Tiny Bit of History • Encryption goes back thousands of years • Classical ciphers encrypted letters (and perhaps digits), and yielded all sorts of bizarre outputs. • The advent of military telegraphy led to ciphers that produced only letters. Steven M. Bellovin September 13, 2006 3 Cryptography Codes vs. Ciphers • Ciphers operate syntactically, on letters or groups of letters: A → D, B → E, etc. • Codes operate semantically, on words, phrases, or sentences, per this 1910 codebook Steven M. Bellovin September 13, 2006 4 Cryptography A 1910 Commercial Codebook Steven M. Bellovin September 13, 2006 5 Cryptography Commercial Telegraph Codes • Most were aimed at economy • Secrecy from casual snoopers was a useful side-effect, but not the primary motivation • That said, a few such codes were intended for secrecy; I have some in my collection, including one intended for union use Steven M. -

A Covert Encryption Method for Applications in Electronic Data Interchange
Technological University Dublin ARROW@TU Dublin Articles School of Electrical and Electronic Engineering 2009-01-01 A Covert Encryption Method for Applications in Electronic Data Interchange Jonathan Blackledge Technological University Dublin, [email protected] Dmitry Dubovitskiy Oxford Recognition Limited, [email protected] Follow this and additional works at: https://arrow.tudublin.ie/engscheleart2 Part of the Digital Communications and Networking Commons, Numerical Analysis and Computation Commons, and the Software Engineering Commons Recommended Citation Blackledge, J., Dubovitskiy, D.: A Covert Encryption Method for Applications in Electronic Data Interchange. ISAST Journal on Electronics and Signal Processing, vol: 4, issue: 1, pages: 107 -128, 2009. doi:10.21427/D7RS67 This Article is brought to you for free and open access by the School of Electrical and Electronic Engineering at ARROW@TU Dublin. It has been accepted for inclusion in Articles by an authorized administrator of ARROW@TU Dublin. For more information, please contact [email protected], [email protected]. This work is licensed under a Creative Commons Attribution-Noncommercial-Share Alike 4.0 License A Covert Encryption Method for Applications in Electronic Data Interchange Jonathan M Blackledge, Fellow, IET, Fellow, BCS and Dmitry A Dubovitskiy, Member IET Abstract— A principal weakness of all encryption systems is to make sure that the ciphertext is relatively strong (but not that the output data can be ‘seen’ to be encrypted. In other too strong!) and that the information extracted is of good words, encrypted data provides a ‘flag’ on the potential value quality in terms of providing the attacker with ‘intelligence’ of the information that has been encrypted. -

Implementation and Performance Evaluation of XTR Over Wireless Network
Implementation and Performance Evaluation of XTR over Wireless Network By Basem Shihada [email protected] Dept. of Computer Science 200 University Avenue West Waterloo, Ontario, Canada (519) 888-4567 ext. 6238 CS 887 Final Project 19th of April 2002 Implementation and Performance Evaluation of XTR over Wireless Network 1. Abstract Wireless systems require reliable data transmission, large bandwidth and maximum data security. Most current implementations of wireless security algorithms perform lots of operations on the wireless device. This result in a large number of computation overhead, thus reducing the device performance. Furthermore, many current implementations do not provide a fast level of security measures such as client authentication, authorization, data validation and data encryption. XTR is an abbreviation of Efficient and Compact Subgroup Trace Representation (ECSTR). Developed by Arjen Lenstra & Eric Verheul and considered a new public key cryptographic security system that merges high level of security GF(p6) with less number of computation GF(p2). The claim here is that XTR has less communication requirements, and significant computation advantages, which indicate that XTR is suitable for the small computing devices such as, wireless devices, wireless internet, and general wireless applications. The hoping result is a more flexible and powerful secure wireless network that can be easily used for application deployment. This project presents an implementation and performance evaluation to XTR public key cryptographic system over wireless network. The goal of this project is to develop an efficient and portable secure wireless network, which perform a variety of wireless applications in a secure manner. The project literately surveys XTR mathematical and theoretical background as well as system implementation and deployment over wireless network. -

A New Cryptosystem for Ciphers Using Transposition Techniques
Published by : International Journal of Engineering Research & Technology (IJERT) http://www.ijert.org ISSN: 2278-0181 Vol. 8 Issue 04, April-2019 A New Cryptosystem for Ciphers using Transposition Techniques U. Thirupalu Dr. E. Kesavulu Reddy FCSRC (USA) Research Scholar Assistant Professor, Dept. of Computer Science Dept. of Computer Science S V U CM&CS – Tirupati S V U CM&CS - Tirupati India – 517502 India – 517502 Abstract:- Data Encryption techniques is used to avoid the performs the decryption. Cryptographic algorithms are unauthorized access original content of a data in broadly classified as Symmetric key cryptography and communication between two parties, but the data can be Asymmetric key cryptography. recovered only through using a key known as decryption process. The objective of the encryption is to secure or save data from unauthorized access in term of inspecting or A. Symmetric Cryptography adapting the data. Encryption can be implemented occurs by In the symmetric key encryption, same key is used for both using some substitute technique, shifting technique, or encryption and decryption process. Symmetric algorithms mathematical operations. By adapting these techniques we more advantageous with low consuming with more can generate a different form of that data which can be computing power and it works with high speed in encrypt difficult to understand by any person. The original data is them. The symmetric key encryption takes place in two referred to as the plaintext and the encrypted data as the modes either as the block ciphers or as the stream ciphers. cipher text. Several symmetric key base algorithms have been The block cipher mode provides, whole data is divided into developed in the past year. -

Key Improvements to XTR
To appear in Advances in Cryptology|Asiacrypt 2000, Lecture Notes in Computer Science 1976, Springer-Verlag 2000, 220-223. Key improvements to XTR Arjen K. Lenstra1, Eric R. Verheul2 1 Citibank, N.A., Technical University Eindhoven, 1 North Gate Road, Mendham, NJ 07945-3104, U.S.A., [email protected] 2 PricewaterhouseCoopers, GRMS Crypto Group, Goudsbloemstraat 14, 5644 KE Eindhoven, The Netherlands, Eric.Verheul@[nl.pwcglobal.com, pobox.com] Abstract. This paper describes improved methods for XTR key rep- resentation and parameter generation (cf. [4]). If the ¯eld characteristic is properly chosen, the size of the XTR public key for signature appli- cations can be reduced by a factor of three at the cost of a small one time computation for the recipient of the key. Furthermore, the para- meter set-up for an XTR system can be simpli¯ed because the trace of a proper subgroup generator can, with very high probability, be com- puted directly, thus avoiding the probabilistic approach from [4]. These non-trivial extensions further enhance the practical potential of XTR. 1 Introduction In [1] it was shown that conjugates of elements of a subgroup of GF(p6)¤ of order 2 dividing Á6(p) = p ¡ p + 1 can be represented using 2 log2(p) bits, as opposed to the 6 log2(p) bits that would be required for their traditional representation. In [4] an improved version of the method from [1] was introduced that achieves the same communication advantage at a much lower computational cost. The resulting representation method is referred to as XTR, which stands for E±cient and Compact Subgroup Trace Representation. -

Efficient Encryption on Limited Devices
Rochester Institute of Technology RIT Scholar Works Theses 2006 Efficient encryption on limited devices Roderic Campbell Follow this and additional works at: https://scholarworks.rit.edu/theses Recommended Citation Campbell, Roderic, "Efficient encryption on limited devices" (2006). Thesis. Rochester Institute of Technology. Accessed from This Master's Project is brought to you for free and open access by RIT Scholar Works. It has been accepted for inclusion in Theses by an authorized administrator of RIT Scholar Works. For more information, please contact [email protected]. Masters Project Proposal: Efficient Encryption on Limited Devices Roderic Campbell Department of Computer Science Rochester Institute of Technology Rochester, NY, USA [email protected] June 24, 2004 ________________________________________ Chair: Prof. Alan Kaminsky Date ________________________________________ Reader: Prof. Hans-Peter Bischof Date ________________________________________ Observer: Prof. Leonid Reznik Date 1 1 Summary As the capstone of my Master’s education, I intend to perform a comparison of Elliptic Curve Cryptography(ECC) and The XTR Public Key System to the well known RSA encryption algorithm. The purpose of such a project is to provide a further understanding of such types of encryption, as well as present an analysis and recommendation for the appropriate technique for given circumstances. This comparison will be done by developing a series of tests on which to run identical tasks using each of the previously mentioned algorithms. Metrics such as running time, maximum and average memory usage will be measured as applicable. There are four main goals of Crypto-systems: Confidentiality, Data Integrity, Authentication and Non-repudiation[5]. This implementation deals only with confidentiality of symmetric key exchange. -

Caesar's Cipher Is a Monoalphabetic
Mathematical summer in Paris - Cryptography Exercise 1 (Caesar’s cipher ?) Caesar’s cipher is a monoalphabetic encryption method where all letters in the alphabet are shifted by a certain constant d. For example, with d = 3, we obtain A ! D; B ! E;:::; Y ! B; Z ! C: 1. Translate the encryption function f in algebraic terms. What is the decryption function g? 2. What is the key in Caesar’s cipher? How many keys are possible? 3. Decrypt the ciphertext LIPPSASVPH. Exercise 2 (Affine encryption ?) We now want to study a more general kind of encryption method, called affine encryption. We represent each letter in the latin alphabet by its position in the alphabet, starting with 0, i.e. A ! 0; B ! 1; C ! 2;:::; Z ! 25; and we consider the map f : x ! ax + b mod 26; where a and b are fixed integers between 0 and 25. We want to use the map f to encrypt each letter in the plaintext. 1. What happens if we choose a = 1? We now choose a = 10 and b = 3. def 2. Let 0 ≤ y ≤ 25 such that y = f(x) = 10x + 3 mod 26. Prove that there exists k 2 Z such that y = 10x + 26k + 3. 3. Prove that y is always odd. 4. What can we say about this encryption method? We now choose a = 9 and b = 4. 5. Find an integer u 2 Z such that 9u = 1 mod 26. 6. Explain why the equation y = 9x + 4 mod 26, with 0 ≤ y ≤ 25, always has a solution. -

The Mathemathics of Secrets.Pdf
THE MATHEMATICS OF SECRETS THE MATHEMATICS OF SECRETS CRYPTOGRAPHY FROM CAESAR CIPHERS TO DIGITAL ENCRYPTION JOSHUA HOLDEN PRINCETON UNIVERSITY PRESS PRINCETON AND OXFORD Copyright c 2017 by Princeton University Press Published by Princeton University Press, 41 William Street, Princeton, New Jersey 08540 In the United Kingdom: Princeton University Press, 6 Oxford Street, Woodstock, Oxfordshire OX20 1TR press.princeton.edu Jacket image courtesy of Shutterstock; design by Lorraine Betz Doneker All Rights Reserved Library of Congress Cataloging-in-Publication Data Names: Holden, Joshua, 1970– author. Title: The mathematics of secrets : cryptography from Caesar ciphers to digital encryption / Joshua Holden. Description: Princeton : Princeton University Press, [2017] | Includes bibliographical references and index. Identifiers: LCCN 2016014840 | ISBN 9780691141756 (hardcover : alk. paper) Subjects: LCSH: Cryptography—Mathematics. | Ciphers. | Computer security. Classification: LCC Z103 .H664 2017 | DDC 005.8/2—dc23 LC record available at https://lccn.loc.gov/2016014840 British Library Cataloging-in-Publication Data is available This book has been composed in Linux Libertine Printed on acid-free paper. ∞ Printed in the United States of America 13579108642 To Lana and Richard for their love and support CONTENTS Preface xi Acknowledgments xiii Introduction to Ciphers and Substitution 1 1.1 Alice and Bob and Carl and Julius: Terminology and Caesar Cipher 1 1.2 The Key to the Matter: Generalizing the Caesar Cipher 4 1.3 Multiplicative Ciphers 6 -

A Secure Variant of the Hill Cipher
† A Secure Variant of the Hill Cipher Mohsen Toorani ‡ Abolfazl Falahati Abstract the corresponding key of each block but it has several security problems [7]. The Hill cipher is a classical symmetric encryption In this paper, a secure cryptosystem is introduced that algorithm that succumbs to the know-plaintext attack. overcomes all the security drawbacks of the Hill cipher. Although its vulnerability to cryptanalysis has rendered it The proposed scheme includes an encryption algorithm unusable in practice, it still serves an important that is a variant of the Affine Hill cipher for which a pedagogical role in cryptology and linear algebra. In this secure cryptographic protocol is introduced. The paper, a variant of the Hill cipher is introduced that encryption core of the proposed scheme has the same makes the Hill cipher secure while it retains the structure of the Affine Hill cipher but its internal efficiency. The proposed scheme includes a ciphering manipulations are different from the previously proposed core for which a cryptographic protocol is introduced. cryptosystems. The rest of this paper is organized as follows. Section 2 briefly introduces the Hill cipher. Our 1. Introduction proposed scheme is introduced and its computational costs are evaluated in Section 3, and Section 4 concludes The Hill cipher was invented by L.S. Hill in 1929 [1]. It is the paper. a famous polygram and a classical symmetric cipher based on matrix transformation but it succumbs to the 2. The Hill Cipher known-plaintext attack [2]. Although its vulnerability to cryptanalysis has rendered it unusable in practice, it still In the Hill cipher, the ciphertext is obtained from the serves an important pedagogical role in both cryptology plaintext by means of a linear transformation. -

Research Notices
AMERICAN MATHEMATICAL SOCIETY Research in Collegiate Mathematics Education. V Annie Selden, Tennessee Technological University, Cookeville, Ed Dubinsky, Kent State University, OH, Guershon Hare I, University of California San Diego, La jolla, and Fernando Hitt, C/NVESTAV, Mexico, Editors This volume presents state-of-the-art research on understanding, teaching, and learning mathematics at the post-secondary level. The articles are peer-reviewed for two major features: (I) advancing our understanding of collegiate mathematics education, and (2) readability by a wide audience of practicing mathematicians interested in issues affecting their students. This is not a collection of scholarly arcana, but a compilation of useful and informative research regarding how students think about and learn mathematics. This series is published in cooperation with the Mathematical Association of America. CBMS Issues in Mathematics Education, Volume 12; 2003; 206 pages; Softcover; ISBN 0-8218-3302-2; List $49;AII individuals $39; Order code CBMATH/12N044 MATHEMATICS EDUCATION Also of interest .. RESEARCH: AGul<lelbrthe Mathematics Education Research: Hothomatldan- A Guide for the Research Mathematician --lllll'tj.M...,.a.,-- Curtis McKnight, Andy Magid, and -- Teri J. Murphy, University of Oklahoma, Norman, and Michelynn McKnight, Norman, OK 2000; I 06 pages; Softcover; ISBN 0-8218-20 16-8; List $20;AII AMS members $16; Order code MERN044 Teaching Mathematics in Colleges and Universities: Case Studies for Today's Classroom Graduate Student Edition Faculty