Jailbreaking, Rooting and Unlocking Phones
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Isam: an Iphone Stealth Airborne Malware
iSAM: An iPhone Stealth Airborne Malware Dimitrios Damopoulos, Georgios Kambourakis, and Stefanos Gritzalis Info-Sec-Lab Laboratory of Information and Communications Systems Security, University of the Aegean, Samos, Greece {ddamop,gkamb,sgritz}@aegean.gr http://www.icsd.aegean.gr/info-sec-lab Abstract. Modern and powerful mobile devices comprise an attractive target for any potential intruder or malicious code. The usual goal of an attack is to acquire users’ sensitive data or compromise the device so as to use it as a stepping stone (or bot) to unleash a number of attacks to other targets. In this paper, we focus on the popular iPhone device. We create a new stealth and airborne malware namely iSAM able to wirelessly infect and self-propagate to iPhone devices. iSAM incorporates six different malware mechanisms, and is able to connect back to the iSAM bot master server to update its programming logic or to obey commands and unleash a synchronized attack. Our analysis unveils the internal mechanics of iSAM and discusses the way all iSAM components contribute towards achieving its goals. Although iSAM has been specifically designed for iPhone it can be easily modified to attack any iOS-based device. Keywords: Malware, iPhone, iOS, Jailbreak, Stealth, Airborne, Rootkit. 1 Introduction Mobile devices have evolved and experienced an immense popularity over the last few years. These devices have penetrated the market due to the variety of data services they offer, such as texting, emailing, browsing the Internet, documents editing, listening to music, watching videos and playing games in addition to the traditional voice services. As a result, analysts are expecting a mobile device population of 5 billion by 2015 [1]. -

Ten Steps to Smartphone Security
Ten Steps to Smartphone Security Smartphones continue to grow in popularity and are now as powerful and functional as many computers. It is important to protect your smartphone just like you protect your computer as mobile cybersecurity threats are growing. These mobile security tips can help you reduce the risk of exposure to mobile security threats: 1. Set PINs and passwords. To prevent unauthorized access to your phone, set a password or Personal Identification Number (PIN) on your phone’s home screen as a first line of defense in case your phone is lost or stolen. When possible, use a different password for each of your important log-ins (email, banking, personal sites, etc.). You should configure your phone to automatically lock after five minutes or less when your phone is idle, as well as use the SIM password capability available on most smartphones. 2. Do not modify your smartphone’s security settings. Do not alter security settings for convenience. Tampering with your phone’s factory settings, jailbreaking, or rooting your phone undermines the built-in security features offered by your wireless service and smartphone, while making it more susceptible to an attack. 3. Backup and secure your data. You should backup all of the data stored on your phone – such as your contacts, documents, and photos. These files can be stored on your computer, on a removal storage card, or in the cloud. This will allow you to conveniently restore the information to your phone should it be lost, stolen, or otherwise erased. 4. Only install apps from trusted sources. -

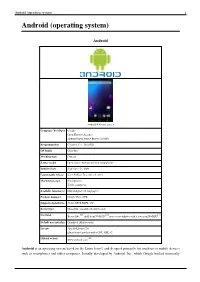
Android (Operating System) 1 Android (Operating System)
Android (operating system) 1 Android (operating system) Android Home screen displayed by Samsung Nexus S with Google running Android 2.3 "Gingerbread" Company / developer Google Inc., Open Handset Alliance [1] Programmed in C (core), C++ (some third-party libraries), Java (UI) Working state Current [2] Source model Free and open source software (3.0 is currently in closed development) Initial release 21 October 2008 Latest stable release Tablets: [3] 3.0.1 (Honeycomb) Phones: [3] 2.3.3 (Gingerbread) / 24 February 2011 [4] Supported platforms ARM, MIPS, Power, x86 Kernel type Monolithic, modified Linux kernel Default user interface Graphical [5] License Apache 2.0, Linux kernel patches are under GPL v2 Official website [www.android.com www.android.com] Android is a software stack for mobile devices that includes an operating system, middleware and key applications.[6] [7] Google Inc. purchased the initial developer of the software, Android Inc., in 2005.[8] Android's mobile operating system is based on a modified version of the Linux kernel. Google and other members of the Open Handset Alliance collaborated on Android's development and release.[9] [10] The Android Open Source Project (AOSP) is tasked with the maintenance and further development of Android.[11] The Android operating system is the world's best-selling Smartphone platform.[12] [13] Android has a large community of developers writing applications ("apps") that extend the functionality of the devices. There are currently over 150,000 apps available for Android.[14] [15] Android Market is the online app store run by Google, though apps can also be downloaded from third-party sites. -
Sophos Mobile Security
Sophos Mobile Security Protect your Android devices against malware and other threats The market dominance of Android devices and the inherent openness of Android led to the proliferation of malware and Potentially Unwanted Applications (PUA). SophosLabs detected over a million new pieces of malware in 2014 alone, and the growth rate is accelerating. Malware can lead to data loss, reputation loss, additional costs, and reduced performance. Highlights Protection and performance The Sophos Mobile Security antivirus app protects your Android devices without compromising Ì Privacy Advisor warns performance or battery life. The app uses up-to-the-minute intelligence from SophosLabs and the Sophos of potential privacy core antivirus engine. This means your apps are automatically scanned for malware as you install them. breaches Sophos Mobile Security’s consistent performance has earned recognition from independent testing agencies including AV-Test. Ì Security Advisor gives tips to improve device Malware protection security Our Sophos Mobile Security antivirus app protects your Android devices with proactive identification of malware. Your apps are automatically scanned for malware as you install them. Sophos includes protection Ì Loss and Theft for PUAs and low-reputation apps—new apps that have no known history and may pose a threat. PUAs Protection include adware, rootkits, diallers, and any association the app may have to previous malicious behaviour such as a certificate that has been compromised. Ì App Protection with additional passwords for Web protection sensitive apps Surf securely on the internet from your Android device. Sophos Mobile Security checks all websites against a Ì Spam Filter SophosLabs database for known malicious sites and prevents users from accessing them. -

Total Defense Mobile Security
USER'S GUIDE Total Defense Mobile Security Total Defense Mobile Security User's Guide Publication date 2015.04.09 Copyright© 2015 Total Defense Mobile Security Legal Notice All rights reserved. No part of this book may be reproduced or transmitted in any form or by any means, electronic or mechanical, including photocopying, recording, or by any information storage and retrieval system, without written permission from an authorized representative of Total Defense. The inclusion of brief quotations in reviews may be possible only with the mention of the quoted source. The content can not be modified in any way. Warning and Disclaimer. This product and its documentation are protected by copyright. The information in this document is provided on an “as is” basis, without warranty. Although every precaution has been taken in the preparation of this document, the authors will not have any liability to any person or entity with respect to any loss or damage caused or alleged to be caused directly or indirectly by the information contained in this work. This book contains links to third-party Websites that are not under the control of Total Defense, therefore Total Defense is not responsible for the content of any linked site. If you access a third-party website listed in this document, you will do so at your own risk. Total Defense provides these links only as a convenience, and the inclusion of the link does not imply that Total Defense endorses or accepts any responsibility for the content of the third-party site. Trademarks. Trademark names may appear in this book. -
Android (Operating System) 1 Android (Operating System)
Android (operating system) 1 Android (operating system) Android Android 4.4 home screen Company / developer Google Open Handset Alliance Android Open Source Project (AOSP) Programmed in C (core), C++, Java (UI) OS family Unix-like Working state Current Source model Open source with proprietary components Initial release September 23, 2008 Latest stable release 4.4.2 KitKat / December 9, 2013 Marketing target Smartphones Tablet computers Available language(s) Multi-lingual (46 languages) Package manager Google Play, APK Supported platforms 32-bit ARM, MIPS, x86 Kernel type Monolithic (modified Linux kernel) [1] [2] [3] Userland Bionic libc, shell from NetBSD, native core utilities with a few from NetBSD Default user interface Graphical (Multi-touch) License Apache License 2.0 Linux kernel patches under GNU GPL v2 [4] Official website www.android.com Android is an operating system based on the Linux kernel, and designed primarily for touchscreen mobile devices such as smartphones and tablet computers. Initially developed by Android, Inc., which Google backed financially Android (operating system) 2 and later bought in 2005, Android was unveiled in 2007 along with the founding of the Open Handset Alliance: a consortium of hardware, software, and telecommunication companies devoted to advancing open standards for mobile devices. The first publicly available smartphone running Android, the HTC Dream, was released on October 22, 2008. The user interface of Android is based on direct manipulation, using touch inputs that loosely correspond to real-world actions, like swiping, tapping, pinching and reverse pinching to manipulate on-screen objects. Internal hardware such as accelerometers, gyroscopes and proximity sensors are used by some applications to respond to additional user actions, for example adjusting the screen from portrait to landscape depending on how the device is oriented. -

2019 China Military Power Report
OFFICE OF THE SECRETARY OF DEFENSE Annual Report to Congress: Military and Security Developments Involving the People’s Republic of China ANNUAL REPORT TO CONGRESS Military and Security Developments Involving the People’s Republic of China 2019 Office of the Secretary of Defense Preparation of this report cost the Department of Defense a total of approximately $181,000 in Fiscal Years 2018-2019. This includes $12,000 in expenses and $169,000 in DoD labor. Generated on 2019May02 RefID: E-1F4B924 OFFICE OF THE SECRETARY OF DEFENSE Annual Report to Congress: Military and Security Developments Involving the People’s Republic of China OFFICE OF THE SECRETARY OF DEFENSE Annual Report to Congress: Military and Security Developments Involving the People’s Republic of China Annual Report to Congress: Military and Security Developments Involving the People’s Republic of China 2019 A Report to Congress Pursuant to the National Defense Authorization Act for Fiscal Year 2000, as Amended Section 1260, “Annual Report on Military and Security Developments Involving the People’s Republic of China,” of the National Defense Authorization Act for Fiscal Year 2019, Public Law 115-232, which amends the National Defense Authorization Act for Fiscal Year 2000, Section 1202, Public Law 106-65, provides that the Secretary of Defense shall submit a report “in both classified and unclassified form, on military and security developments involving the People’s Republic of China. The report shall address the current and probable future course of military-technological development of the People’s Liberation Army and the tenets and probable development of Chinese security strategy and military strategy, and of the military organizations and operational concepts supporting such development over the next 20 years. -

Ah! Universal Android Rooting Is Back
AH! UNIVERSAL ANDROID ROOTING IS BACK Wen `Memeda` Xu @K33nTeam ABOUT ME Wen Xu a.k.a Memeda @antlr7 • Security research intern at KeenTeam • Android Roo6ng • Soware exploita6on • Senior student at Shanghai Jiao Tong University • Member of LoCCS • Vice-captain of CTF team 0ops • Rank 2rd in the world on CTFTIME AGENDA • Present Situa6on of Android Roo6ng • Awesome Bug (CVE-2015-3636) • Fuzzing • Analysis • Awesome Exploita6on Techniques • Object Re-filling in kernel UAF • Kernel Code Execu@on • Targe@ng 64bit Devices • Future PART I Present Situation PRESENT SITUATION Root for what? • Goal • uid=0(root) gid=0(root) groups=0(root) • Kernel arbitrary read/write • Cleaning • SELinux • … PRESENT SITUATION • SoC (Driver) • Missing argument sani6Za6on (ioctl/mmap) • Qualcomm camera drivers bug CVE-2014-4321, CVE-2014-4324 CVE-2014-0975, CVE-2014-0976 • TOCTTOU • Direct dereference in user space CVE-2014-8299 • Chip by chip A BIG DEAL • Universal root soluon • Universally applied bug • Confronng Linux kernel • Universally applied exploita6on techniques • One exploit for hundreds of thousands of devices • Adaptability (Hardcode) • User-friendly (Stability) • COMING BACK AGAIN! PART II Bug Hunting FUZZING Open source kernel syscall fuzzer • Trinity • hps://github.com/kernelslacker/trinity • Scalability • Ported to ARM Linux FUZZING Let’s take a look at our log when we wake up ;) • Crical paging fault at 0x200200?!! SK: PING SOCKET OBJECT IN KERNEL user_sock_fd = socket(AF_INET, SOCK_DGRAM, IPPROTO_ICMP); 2 3 1 LIST_POISON2 == 0X200200 ping_unhash -
Beginners Guide to Developing for a Jailbroken Ios Plaxorm
Beginners Guide to Developing for a Jailbroken iOS Plaorm Priya Rajagopal Twier: @rajagp Blog: hp://www.priyaontech.com CocoaHeads, Jan 2012 Jailbreaking is Legal (..at least in the US) Priya Rajagopal, CocoaHeads,2012 Why develop for a jailbroken plaorm? • Develop run-Ume patches (.dylibs) that can be automacally loaded and shared across apps – Link with third part dylibs (eg- BTStack) • Hook into “system” apps and control plaorm behavior – Eg. Mobile Safari, Springboard • UUlize features not exposed through SDK’s public APIs to build something really cool Priya Rajagopal, CocoaHeads,2012 3 Why develop for a jailbroken plaorm? • More control over the plaorm – Terminal window, ssh, scp, rm etc. It’s a unix system. • Don’t need an Apple developer’s license – Self signed apps, pseudo signed apps • You don’t even need a Mac – You can even develop on the phone (Cool!) • Opons : – Distribute through Cydia – Internal Enterprise apps – Personal use. If you can’t find it, you can build it! Priya Rajagopal, CocoaHeads,2012 4 Tethered vs. Untethered Jailbreak • Tethered – You need to tether your device to your PC to reboot it. Quite inconvenient • Untethered – You don’t need to tether your device to your PC to reboot it. • ParUal Untethered – Tethered but you can reboot untethered to enable minimal funcUonality Priya Rajagopal, CocoaHeads,2012 5 Jailbreak Sogware (If its not free, it’s a scam) • RedSn0w (Mac /Windows) • Jailbreakme.com (Web) • PwnageTool (Mac) • GreenPois0n (Mac/Windows) Priya Rajagopal, CocoaHeads,2012 6 Status of iOS Jailbreak -
Mobile Security Companion to the CIS Critical Security Controls (Version 6)
Mobile Security Companion to the CIS Critical Security Controls (Version 6) 1 Mobile Security Companion to the CIS Critical Security Controls (Version 6) Introduction ................................................................................................................................................................................................................................................................. 3 Description ................................................................................................................................................................................................................................................................... 5 CIS Critical Security Controls (Version 6): Mobile Security .................................................................................................................................................................... 5 2 Introduction Mobile devices are starting to replace laptops for regular business use. Organizations are building or porting their applications to mobile platforms, so users are increasingly accessing the same data with mobile as with their laptops. Also, organizations have increasingly implemented Bring Your Own Device (BYOD) policies to manage this trend. However, many organizations have been struggling with the increase of personal mobile devices, and don’t fully understand the security risks they may bring. There are concerns that their compact size makes them easy to lose, that they run newer operating systems that don’t -

Jailbreak D'ios
Jailbreak d'iOS Débridage d'iOS Un outil similaire à Blackra1n, Limera1n, est par la suite développé et publié lors de la sortie de la version 4.1 Pour les articles homonymes, voir Jailbreak. d'iOS, malgré un problème présent dans la première ver- sion de cet outil. Le jailbreak d'iOS, également appelé débridage Des outils comme redsn0w, Pwnage Tool et Sn0wbreeze d'iOS, déverrouillage ou déplombage est un proces- ainsi que GreenPois0n, Absinthe (pour l'iPhone 4S et sus permettant aux appareils tournant sous le système l'iPad 2) permettent de jailbreaker les versions plus ré- d'exploitation mobile d'Apple iOS (tels que l'iPad, centes du terminal. l'iPhone, l'iPod touch, et plus récemment, l'Apple TV) d'obtenir un accès complet pour déverrouiller toutes les Depuis le 6 janvier 2013, il est possible de jailbreaker fonctionnalités du système d'exploitation, éliminant ain- les terminaux sous l'iOS 6, et ce jusqu'à la version 6.1.2, si les restrictions posées par Apple. Une fois iOS débri- par le biais d'un outil connu sous le nom d'Evasi0n. Cette dé, ses utilisateurs sont en mesure de télécharger d'autres méthode s’applique pour tous les terminaux supportant applications, des extensions ainsi que des thèmes qui ne IOS 6 mise à part l'Apple TV. Les versions 6.1.2 jus- sont pas proposés sur la boutique d'application officielle qu’à 6.1.6 ont été libéré en janvier 2014 grâce au logiciel d'Apple, l'App Store, via des installeurs comme Cydia. -
Satisfy That Android Sweet Tooth
IBM Security Thought Leadership White Paper Satisfy that Android sweet tooth Do Android’s dessert-named updates improve device and data security enough to work for the enterprise? Satisfy that Android sweet tooth Android is ready for the enterprise. Is your continues to grow. The wide variety of Android devices enterprise ready for Android? available means that they are often a good fit for corporate- owned device programs. For example, many field-based employees need rugged Android devices built to stand up to Introduction dust, shock, vibration, rain, humidity, solar radiation, altitude, Android has long ruled the consumer market. Now, the latest and temperature extremes. Others want Android devices with security advancements from Google and device manufacturers, data capture features ideal for inventory control and warehouse and support for Android by leading EMM solution providers, operations. are expanding its presence in the enterprise. To help ensure security and compliance with industry standards and This growth comes with some unintended consequences, as government regulations, enterprises need a way to protect well as important considerations for IT. Companies are and manage the wide range of available devices, versions, and allowing employees to use their own preferred or industry- idiosyncrasies of the world’s most popular mobile operating specific devices, but IT must address the very real concerns of system. protecting corporate data and providing standardized management. It’s not a one-solution-fits-all situation. IT needs to examine its device and application landscape and decide what security and The most popular mobile platform in the world also has a management capabilities are essential in a customized volatile security record;2 however, Android’s recent, sweetly- enterprise mobility strategy.