Xenapp Optimization for W2K8 R2
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Guidelines for Designing Embedded Systems with Windows 10 Iot Enterprise
Guidelines for Designing Embedded Systems with Windows 10 IoT Enterprise Version 2.0 Published July 15, 2016 Guidelines for designing embedded systems 1 CONFIDENTIAL Contents Overview .................................................................................................................................................................................................... 4 Building a task-specific experience ............................................................................................................................................ 4 General Group Policy settings ....................................................................................................................................................... 4 Application control ................................................................................................................................................................................ 5 Application boot options ................................................................................................................................................................. 5 Auto-boot Universal Windows apps ...................................................................................................................................... 5 Auto-boot Classic Windows apps ........................................................................................................................................... 5 Limit application access with AppLocker ............................................................................................................................... -

Copyrighted Material
Index Numerics Address Resolution Protocol (ARP), 1052–1053 admin password, SOHO network, 16-bit Windows applications, 771–776, 985, 1011–1012 900, 902 Administrative Tools window, 1081–1083, 32-bit (x86) architecture, 124, 562, 769 1175–1176 64-bit (x64) architecture, 124, 562, 770–771 administrative tools, Windows, 610 administrator account, 1169–1170 A Administrators group, 1171 ADSL (Asynchronous Digital Subscriber Absolute Software LoJack feature, 206 Line), 1120 AC (alternating current), 40 Advanced Attributes window, NTFS AC adapters, 311–312, 461, 468–469 partitions, 692 Accelerated Graphics Port (AGP), 58 Advanced Computing Environment (ACE) accelerated video cards (graphics initiative, 724 accelerator cards), 388 Advanced Confi guration and Power access points, wireless, 996, 1121 Interface (ACPI) standard, 465 access time, hard drive, 226 Advanced Graphics Port (AGP) card, access tokens, 1146–1147 391–392 Account Operators group, 1172 Advanced Graphics Port (AGP) port, 105 ACE (Advanced Computing Environment) Advanced Host Controller Interface (AHCI), initiative, 724 212–213 ACPI (Advanced Confi guration and Power Advanced Micro Devices (AMD), 141–144 Interface) standard, 465 Advanced Packaging Tool (APT), 572 Action Center, 1191–1192 Advanced Power Management (APM) Active Directory Database, 1145–1146, 1183 standard, 465 active heat sink, 150 Advanced Programmable Interrupt active matrix display, LCD (thin-fi lm Controller (APIC), 374 transistor (TFT) display), 470 Advanced RISC Computing Specifi cation active partition, 267, -

Security Advisory MTIS20-010 - Page 1 of 19 UNDER ANALYSIS: Firewall Enterprise
NEW THREAT OVERVIEW | PREVIOUS THREATS UPDATES | THREAT DETAILS EXECUTIVE SUMMARY March 10, 2020 | MTIS20-010 Since the last McAfee® Labs Security Advisory (February 12), the following noteworthy event has taken place: Patches are available for multiple Microsoft security vulnerabilities NEW THREAT OVERVIEW (MSPT-Mar2020) Microsoft IIS Server improperly handles Malformed Request Headers Privilege Escalation (CVE- 2020-0645) MTIS20-010-A IMPORTANCE: Medium COVERED PRODUCTS: UNDER ANALYSIS: Firewall Enterprise Back to top (MSPT-Mar2020) Microsoft Windows .LNK file Remote Code Execution (CVE-2020-0684) MTIS20-010-B IMPORTANCE: High COVERED PRODUCTS: UNDER ANALYSIS: Firewall Enterprise Back to top (MSPT-Mar2020) Microsoft DirectX improperly handles Objects in Memory Privilege Escalation (CVE-2020-0690) MTIS20-010-C IMPORTANCE: Medium COVERED PRODUCTS: DAT | Web Gateway UNDER ANALYSIS: Firewall Enterprise Back to top (MSPT-Mar2020) Microsoft Visual Studio improperly handles Pipeline Job Tokens Privilege Escalation (CVE-2020- 0758) MTIS20-010-D IMPORTANCE: Medium COVERED PRODUCTS: UNDER ANALYSIS: Firewall Enterprise Back to top (MSPT-Mar2020) Microsoft Defender Handles Certain Objects in Memory Privilege Escalation (CVE-2020-0762) MTIS20-010-E IMPORTANCE: Medium COVERED PRODUCTS: Security Advisory MTIS20-010 - Page 1 of 19 UNDER ANALYSIS: Firewall Enterprise Back to top (MSPT-Mar2020) Microsoft Defender Handles Certain Objects in Memory Privilege Escalation (CVE-2020-0763) MTIS20-010-F IMPORTANCE: Medium COVERED PRODUCTS: UNDER ANALYSIS: Firewall -

9780789756978 Onlineappendi
APPENDIX A Answers to the “Do I Know This Already?” Quizzes and Q&A Questions “Do I Know This Already?” Quizzes Chapter 1 Chapter 3 1. B 1. B 2. D 2. D 3. B 3. C 4. A 4. B 5. D 5. C 6. C 6. A and D 7. B 7. C 8. B and D 8. A 9. B and C 9. C 10. B 10. A and D Chapter 2 Chapter 4 1. D 1. D 2. B 2. C 3. D 3. D 4. B 4. C 5. A 5. D 6. C 6. D 7. A Chapter 5 8. A 9. A 1. C 10. D 2. D 3. B 4 MCSA 70-740 Cert Guide: Installation, Storage, and Compute with Windows Server 2016 4. C Chapter 9 5. A and C 1. B 6. B 2. C 3. B Chapter 6 4. C 1. D 5. A and D 2. A 6. D 3. D 4. A Chapter 10 5. B 1. B 6. A 2. B and D 3. A Chapter 7 4. D 1. B 5. C 2. B 6. A 3. C 4. A Chapter 11 5. D 1. A and D 6. B 2. A 3. A Chapter 8 4. C 1. D 5. A 2. A 6. C 3. B 7. A 4. C 8. C 5. C 6. C Chapter 12 7. A 1. D 8. D 2. B 3. D 4. A 5. C 6. B Appendix A: Answers to the “Do I Know This Already?” Quizzes and Q&A Questions 5 Chapter 13 Chapter 17 1. -
Optimizing Windows 10, Build 2004, for a Virtual Desktop Role
Optimizing Windows 10, Build 2004, for a Virtual Desktop role Written by Robert M. Smith, Program Manager, Azure Global Customer Engineering Date Created: May 12, 2020 Date Updated: July 08, 2020 Date Published: tbd Contributors: Tim Muessig, Senior Premier Field Engineer; Narklis Engler, Principal Program Manager Version 1.2 Document Change History Version Changes 1.0 Adding verbiage for Windows Virtual Desktop, and Windows 10 build 2004 specifically 1.1 Additional updates for 2004 1.2 Final pass, updated group policy, services, tasks, and added info about Storage Sense for disk cleanup. Introduction This article is intended to provide suggestions for configurations for Windows 10, build 2004, for optimal performance in Virtualized Desktop environments, including Virtual Desktop Infrastructure (VDI) and Windows Virtual Desktop (WVD). All settings in this guide are suggested optimization settings only and are in no way requirements. The information in this guide is pertinent to Windows 10, version 2004, operating system (OS) build 19041. The guiding principles to optimize performance of Windows 10 in a virtual desktop environment are to minimize graphic redraws and “effects”, background activities that have no major benefit to the virtual desktop environment, and generally reduce running processes to the bare minimum. A secondary goal is to reduce disk space usage in the base image to the bare minimum. With virtual desktop implementations, the smallest possible base, or “gold” image size, can slightly reduce memory utilization on the host system, as well as a small reduction in overall network operations required to deliver the desktop environment to the consumer. No optimizations should reduce the user experience. -
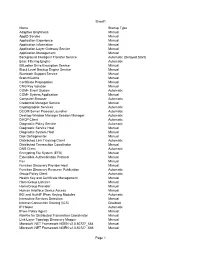
Tweakhound, Windows 7 Beta Default Services
Sheet1 Name Startup Type Adaptive Brightness Manual AppID Service Manual Application Experience Manual Application Information Manual Application Layer Gateway Service Manual Application Management Manual Background Intelligent Transfer Service Automatic (Delayed Start) Base Filtering Engine Automatic BitLocker Drive Encryption Service Manual Block Level Backup Engine Service Manual Bluetooth Support Service Manual BranchCache Manual Certificate Propagation Manual CNG Key Isolation Manual COM+ Event System Automatic COM+ System Application Manual Computer Browser Automatic Credential Manager Service Manual Cryptographic Services Automatic DCOM Server Process Launcher Automatic Desktop Window Manager Session Manager Automatic DHCP Client Automatic Diagnostic Policy Service Automatic Diagnostic Service Host Manual Diagnostic System Host Manual Disk Defragmenter Manual Distributed Link Tracking Client Automatic Distributed Transaction Coordinator Manual DNS Client Automatic Encrypting File System (EFS) Manual Extensible Authentication Protocol Manual Fax Manual Function Discovery Provider Host Manual Function Discovery Resource Publication Automatic Group Policy Client Automatic Health Key and Certificate Management Manual HomeGroup Listener Manual HomeGroup Provider Manual Human Interface Device Access Manual IKE and AuthIP IPsec Keying Modules Automatic Interactive Services Detection Manual Internet Connection Sharing (ICS) Disabled IP Helper Automatic IPsec Policy Agent Manual KtmRm for Distributed Transaction Coordinator Manual Link-Layer -
Windows Internals, Sixth Edition, Part 2
spine = 1.2” Part 2 About the Authors Mark Russinovich is a Technical Fellow in ® the Windows Azure™ group at Microsoft. Windows Internals He is coauthor of Windows Sysinternals SIXTH EDITION Administrator’s Reference, co-creator of the Sysinternals tools available from Microsoft Windows ® The definitive guide—fully updated for Windows 7 TechNet, and coauthor of the Windows Internals and Windows Server 2008 R2 book series. Delve inside Windows architecture and internals—and see how core David A. Solomon is coauthor of the Windows Internals book series and has taught components work behind the scenes. Led by a team of internationally his Windows internals class to thousands of renowned internals experts, this classic guide has been fully updated Windows developers and IT professionals worldwide, SIXTH for Windows 7 and Windows Server® 2008 R2—and now presents its including Microsoft staff. He is a regular speaker 6EDITION coverage in two volumes. at Microsoft conferences, including TechNet As always, you get critical, insider perspectives on how Windows and PDC. operates. And through hands-on experiments, you’ll experience its Alex Ionescu is a chief software architect and internal behavior firsthand—knowledge you can apply to improve consultant expert in low-level system software, application design, debugging, system performance, and support. kernel development, security training, and Internals reverse engineering. He teaches Windows internals courses with David Solomon, and is ® In Part 2, you will: active in the security research community. -

Copyrighted Material
Contents Introduction xxix Part I Introduction to Windows Security Monitoring 1 Chapter 1 Windows Security Logging and Monitoring Policy 3 Security Logging 3 Security Logs 4 System Requirements 5 PII and PHI 5 Availability and Protection 5 Configuration Changes 6 Secure Storage 6 Centralized Collection 6 Backup and Retention 7 Periodic Review 7 Security Monitoring 7 Communications 8 Audit Tool and Technologies 8 Network Intrusion Detection Systems 8 Host-based Intrusion Detection Systems 8 COPYRIGHTEDSystem Reviews MATERIAL 9 Reporting 9 Part II Windows Auditing Subsystem 11 Chapter 2 Auditing Subsystem Architecture 13 Legacy Auditing Settings 13 Advanced Auditing Settings 16 xv ftoc.indd 02:37:46:PM 02/15/2018 Page xv xvi Contents Set Advanced Audit Settings via Local Group Policy 18 Set Advanced Audit Settings via Domain Group Policy 19 Set Advanced Audit Settings in the Local Security Authority (LSA) Policy Database 19 Read Current LSA Policy Database Advanced Audit Policy Settings 20 Advanced Audit Policies Enforcement and Legacy Policies Rollback 20 Switch from Advanced Audit Settings to Legacy Settings 21 Switch from Legacy Audit Settings to Advanced Settings 22 Windows Auditing Group Policy Settings 22 Manage Auditing and Security Log 22 Generate Security Audits 23 Security Auditing Policy Security Descriptor 23 Group Policy: “Audit: Shut Down System Immediately If Unable to Log Security Audits” 24 Group Policy: Protected Event Logging 25 Group Policy: “Audit: Audit the Use of Backup and Restore Privilege” 25 Group Policy: “Audit: -

Dataton Watchout Windows 10 Enterprise Tweaking Guide
DATATON WATCHOUT WINDOWS 10 ENTERPRISE TWEAKING GUIDE INTRODUCTION Support 1 Warranty and service 1 Longevity and 24/7 use 1 New drivers 1 Microsoft EULA when building for reselling 1 Dataton’s WATCHOUT media servers 2 WINDOWS 10 ENTERPRISE TWEAKING GUIDE Install Windows 3 Add and remove Windows features 4 Updates 5 Disable and delete hibernation files 5 Remove Windows components 5 Uninstall OneDrive 6 Group policies 7 Install all drivers 10 Install WATCHOUT 10 Windows settings 11 Services 15 Registry settings 16 Task scheduler 17 © Copyright 2018 DATATON AB. All rights reserved. Dataton, the Dataton logo, WATCHOUT, WATCHPAX, WATCHMAX are trademarks/registered trademarks of DATATON AB. All other company and product names are trademarks or registered trademarks of their respective owners. Use of a term in this guide should not be regarded as affecting the validity of any trademark, or as an endorsement. This guide is provided as advice only and any technical information contained herein regarding features and spec- ifications is subject to change without notice. Dataton assumes no responsibility for any inaccuracies or errors in this guide or the products described. Document number: 3749. Rev 1.3 INTRODUCTION WATCHOUT is the leading multi-display and projection-mapping software with over 17 years of unrivalled performance and reliability under its belt. Award-winning WATCHOUT can be used in a wide range of applications, from smaller fixed installations, to world-record video walls and large, complex live events. In general, building a high performance, top quality and reliable WATCHOUT media server requires a combination of well-developed skills to select the right hardware, tune the BIOS settings and tune the Microsoft Windows® 10 operating system. -

OPUS ERROR REPORTING User Information
OPUS ERROR REPORTING User Information Version 1 1st edition 2008, publication date November 2008 © 2008 BRUKER OPTIK GmbH, Rudolf-Plank-Straße 27, D-76275 Ettlingen, www.brukeroptics.com All rights reserved. No part of this manual may be reproduced or transmitted in any form or by any means including printing, photocopying, microfilm, electronic sys- tems etc. without our prior written permission. Brand names, registered trademarks etc. used in this manual, even if not explicitly marked as such, are not to be consid- ered unprotected by trademarks law. They are the property of their respective own- er. The following publication has been worked out with utmost care. However, Bruker Optik GmbH does not accept any liability for the correctness of the information. Bruker Optik GmbH reserves the right to make changes to the products described in this manual without notice. This manual is the original documentation for the OPUS spectroscopic software. Table of Contents 1 Introduction . 1 1.1 How to report errors? . 1 1.2 Mandatory items to be reported in any case: . 1 1.3 Further items to be reported: . 2 1.4 How to log errors? . 2 1.5 Define Dr Watson as log file standard . 3 1.6 Error messages in Windows . 4 2 Types of errors. 5 2.1 Complete operating system crash . 5 2.2 OPUS crash . 5 2.3 OPUS disappears . 8 2.4 Error message in OPUS . 9 2.5 OPUS interface freezes . 9 3 Error during measurement . 11 3.1 Save and send full report . 11 3.2 Save recent measuring files . -

Debugging in the (Very) Large: Ten Years of Implementation and Experience
Debugging in the (Very) Large: Ten Years of Implementation and Experience Kirk Glerum, Kinshuman Kinshumann, Steve Greenberg, Gabriel Aul, Vince Orgovan, Greg Nichols, David Grant, Gretchen Loihle, and Galen Hunt Microsoft Corporation One Microsoft Way Redmond, WA 98052 examines program state to deduce where algorithms or state ABSTRACT deviated from desired behavior. When tracking particularly Windows Error Reporting (WER) is a distributed system onerous bugs the programmer can resort to restarting and that automates the processing of error reports coming from stepping through execution with the user’s data or an installed base of a billion machines. WER has collected providing the user with a version of the program billions of error reports in ten years of operation. It collects instrumented to provide additional diagnostic information. error data automatically and classifies errors into buckets, Once the bug has been isolated, the programmer fixes the which are used to prioritize developer effort and report code and provides an updated program.1 fixes to users. WER uses a progressive approach to data collection, which minimizes overhead for most reports yet Debugging in the large is harder. When the number of allows developers to collect detailed information when software components in a single system grows to the needed. WER takes advantage of its scale to use error hundreds and the number of deployed systems grows to the statistics as a tool in debugging; this allows developers to millions, strategies that worked in the small, like asking isolate bugs that could not be found at smaller scale. WER programmers to triage individual error reports, fail. -
When Applications Crash Part II - WER a Two Part Guide to How Any ISV Can Find and Fix Crashes That Occur at Customer Sites
TMurgent Technologies 26 Angela Street Canton, MA 02021 USA (+1) 781.492.0403 When Applications Crash Part II - WER A two part guide to how any ISV can find and fix crashes that occur at customer sites. Tim Mangan Founder, TMurgent Technologies April 1, 2006 When Applications Crash Part II Page 2 Copyright 2006 Tmurgent Technologies Introduction Unfortunately it is inevitable. No matter how careful your developers are. No matter how thorough your testing is. It will happen. At a customer site. Before they buy your software. Something crashes in your software. Buffer overrun. Dereferencing a null pointer. Divide by zero. You name it, it can happen – and will at some point. This white paper, and its companion 1, covers the basics of two methods you can use to solve these problems when they happen. Both require some advance planning on your part. The first method, covered in Part I of this paper, is an old tried-and-true method of using DrWtsn32. This second method, covered here in Part II, is newer and usually easier for your customer to deal with. Method 2 – Windows Error Reporting and WinQual. Getting Watson dumps from a customer can be painful. Fortunately, Microsoft has introduced the Windows Error Reporting Service (WER) in Windows XP, Server 2003, and subsequent versions of the OS. WER is not available on Windows 2000 professional or server, so you will need to continue to use Watson dump for those customers. Windows Error Reporting (WER) is that annoying popup dialog that appears when an application crashes that usually says “…has encountered a problem and needs to close”.