Windows for Reverse Engineers
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Lab Report: 7.1.6 Configure Windows Defender
Lab Report: 7.1.6 Configure Windows Defender Your Performance Your Score: 0 of 6 (0%) Pass Status: Not Passed Elapsed Time: 12 seconds Required Score: 100% Task Summary Perform a full scan once per week Hide Details Perform the scan on Saturday Perform the scan at midnight (12:00 am) Perform a full system scan Check for updates before scanning Configure default actions to take Hide Details Remove severe alert items Remove high alert items Remove medium alert items Allow low alert items Apply recommended actions to items detected during a scan Configure advanced options Hide Details Scan email Scan removable drives Display items from all users of this computer Perform a quick scan Explanation In this lab, your task is to configure Windows Defender as follows: Automatic scanning setting: Frequency: Saturday Approximate time: 12:00 am Type: Full scan (A quick scan checks the areas of the computer that spyware is likely to affect, and a full scan checks all files and programs on the computer) Check for updated definitions before scanning: Enabled Default actions settings: Severe alert items: Remove High alert items: Remove Medium alert items: Remove Low alert items: Allow Apply recommended actions: Enabled Advanced settings: Scan email: Enabled Scan removable drives: Enabled Administrator settings: Display items from all users of this computer: Enabled Complete this lab as follows: 1. Right-click Start > Control Panel. 2. In the top right corner under View by, select Small icons from the drop-down list. 3. Select Windows Defender. 4. Select Tools. 5. Under Settings, select Options. 6. Make sure Automatically scan my computer (recommended) is selected to allow Windows Defender to scan the computer automatically. -
Exploring the X64
Exploring the x64 Junichi Murakami Executive Officer, Director of Research Fourteenforty Research Institute, Inc. Who am I? • Junichi Murakami – @Fourteenforty Research Institute, Inc. – Both Windows and Linux kernel development – Reversing malware and P2P software, etc. – Speaker at: • Black Hat 2008 US and Japan, AVAR 2009, RSA Conference(2009-) – Instructor at Security & Programming Camp(2006-) 2 Environment • Windows 7 x64 Edition • Visual Studio 2008 • Windbg • IDA Pro Advanced – STD doesn’t support x64, an offering is needed! 4 Agenda • Windows x64 • ABI(Application Binary Interface) • API Hooking • Code Injection 5 Windows x64 • Native x64 and WoW64 • Virtual Address Space – 2^64 = 16 Exa Byte ( Exa: 10^18) – but, limited to 16TB by Microsoft • File/Registry reflection • New 64-bit APIs – IsWow64Process, GetNativeSystemInfo, etc. 6 ABI • Binary Format • Register • Calling Convention • Exception Handling • Systemcall(x64, WoW64) 11 Binary Format(Cont.) • Some fields were extended to 64-bits – IMAGE_NT_HEADERS.IMAGE_OPTIONAL_HEADER • ImageBase • SizeOfStackReserve • SizeOfStackCommit • SizeOfHeapReserve • SizeOfHeapCommit 13 Calling Convention • first 4 parameters are passed by RCX, RDX, R8, R9 – 5th and later are passed on the stack • caller allocates register home space on the stack • RAX is used for return values • leaf / non-leaf function – leaf function: never use stack – PE32+ contains non-leaf function’s information in its EXCEPTION DIRECTORY • Register’s volatility – volatile: RAX, RCX, RDX, R8-R11 15 Exception Handling • -

Through the Looking Glass: Webcam Interception and Protection in Kernel
VIRUS BULLETIN www.virusbulletin.com Covering the global threat landscape THROUGH THE LOOKING GLASS: and WIA (Windows Image Acquisition), which provides a WEBCAM INTERCEPTION AND still image acquisition API. PROTECTION IN KERNEL MODE ATTACK VECTORS Ronen Slavin & Michael Maltsev Reason Software, USA Let’s pretend for a moment that we’re the bad guys. We have gained control of a victim’s computer and we can run any code on it. We would like to use his camera to get a photo or a video to use for our nefarious purposes. What are our INTRODUCTION options? When we talk about digital privacy, the computer’s webcam The simplest option is just to use one of the user-mode APIs is one of the most relevant components. We all have a tiny mentioned previously. By default, Windows allows every fear that someone might be looking through our computer’s app to access the computer’s camera, with the exception of camera, spying on us and watching our every move [1]. And Store apps on Windows 10. The downside for the attackers is while some of us think this scenario is restricted to the realm that camera access will turn on the indicator LED, giving the of movies, the reality is that malware authors and threat victim an indication that somebody is watching him. actors don’t shy away from incorporating such capabilities A sneakier method is to spy on the victim when he turns on into their malware arsenals [2]. the camera himself. Patrick Wardle described a technique Camera manufacturers protect their customers by incorporating like this for Mac [8], but there’s no reason the principle into their devices an indicator LED that illuminates when can’t be applied to Windows, albeit with a slightly different the camera is in use. -

Operating System Boot from Fully Encrypted Device
Masaryk University Faculty of Informatics Operating system boot from fully encrypted device Bachelor’s Thesis Daniel Chromik Brno, Fall 2016 Replace this page with a copy of the official signed thesis assignment and the copy of the Statement of an Author. Declaration Hereby I declare that this paper is my original authorial work, which I have worked out by my own. All sources, references and literature used or excerpted during elaboration of this work are properly cited and listed in complete reference to the due source. Daniel Chromik Advisor: ing. Milan Brož i Acknowledgement I would like to thank my advisor, Ing. Milan Brož, for his guidance and his patience of a saint. Another round of thanks I would like to send towards my family and friends for their support. ii Abstract The goal of this work is description of existing solutions for boot- ing Linux and Windows from fully encrypted devices with Secure Boot. Before that, though, early boot process and bootloaders are de- scribed. A simple Linux distribution is then set up to boot from a fully encrypted device. And lastly, existing Windows encryption solutions are described. iii Keywords boot process, Linux, Windows, disk encryption, GRUB 2, LUKS iv Contents 1 Introduction ............................1 1.1 Thesis goals ..........................1 1.2 Thesis structure ........................2 2 Boot Process Description ....................3 2.1 Early Boot Process ......................3 2.2 Firmware interfaces ......................4 2.2.1 BIOS – Basic Input/Output System . .4 2.2.2 UEFI – Unified Extended Firmware Interface .5 2.3 Partitioning tables ......................5 2.3.1 MBR – Master Boot Record . -
Mitigating Service Account Credential Theft on Windows
Mitigating Service Account Credential Theft on Windows Reducing the risk of automated authentication against untrusted endpoints Version 1.0.0 Last Updated: 2014-09-16 Mitigating Service Account Credential Theft on Windows Disclaimer This document is for informational purposes only. The authors make no warranties, express, implied, or statutory as to the information in the document. This document is provided "as-is". Information and views expressed in this document, including URLs and other Internet website references, may change without notice. You bear the risk of using it. This document is provided under the Creative Commons Attribution 4.0 International (CC BY 4.0) license. The names of actual companies and products mentioned herein may be the trademarks of their respective owners. Authors HD Moore Joe Bialek Ashwath Murthy Rapid7 Microsoft Palo Alto Networks Contents Executive Summary ................................................................................................................................................................ 1 Introduction ............................................................................................................................................................................ 2 Attacks .................................................................................................................................................................................... 2 Kerberos ............................................................................................................................................................................. -
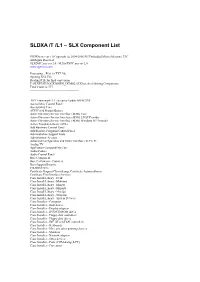
SLDXA /T /L1 – SLX Component List
SLDXA /T /L1 – SLX Component List SLDXA.exe ver 1.0 Copyright (c) 2004-2006 SJJ Embedded Micro Solutions, LLC All Rights Reserved SLXDiffC.exe ver 2.0 / SLXtoTXTC.exe ver 2.0 www.sjjmicro.com Processing... File1 to TXT file. Opening XSL File Reading RTF for final conversion F:\SLXTEST\LOCKDOWN_DEMO2.SLX has the following Components Total Count is: 577 -------------------------------------------------- .NET Framework 1.1 - Security Update KB887998 Accessibility Control Panel Accessibility Core ACPI Fixed Feature Button Active Directory Service Interface (ADSI) Core Active Directory Service Interface (ADSI) LDAP Provider Active Directory Service Interface (ADSI) Windows NT Provider Active Template Library (ATL) Add Hardware Control Panel Add/Remove Programs Control Panel Administration Support Tools Administrator Account Advanced Configuration and Power Interface (ACPI) PC Analog TV Application Compatibility Core Audio Codecs Audio Control Panel Base Component Base Performance Counters Base Support Binaries CD-ROM Drive Certificate Request Client & Certificate Autoenrollment Certificate User Interface Services Class Install Library - Desk Class Install Library - Mdminst Class Install Library - Mmsys Class Install Library - Msports Class Install Library - Netcfgx Class Install Library - Storprop Class Install Library - System Devices Class Installer - Computer Class Installer - Disk drives Class Installer - Display adapters Class Installer - DVD/CD-ROM drives Class Installer - Floppy disk controllers Class Installer - Floppy disk drives -

Login with Amazon Developer Guide for Websites
Login with Amazon Developer Guide for Websites Login with Amazon: Developer Guide for Websites Copyright © 2017 Amazon Services, LLC or its affiliates. All rights reserved. Amazon and the Amazon logo are trademarks of Amazon.com, Inc. or its affiliates. All other trademarks not owned by Amazon are the property of their respective owners Contents Welcome .................................................................................................................................................. 2 How Do I...? .............................................................................................................................................. 2 Understanding Login with Amazon ........................................................................................................... 3 Login with Amazon Conceptual Overview ................................................................................................. 4 Single Sign-On (SSO) for Web ................................................................................................................. 6 Single Sign-On (SSO) for Mobile ............................................................................................................. 7 Access Token ............................................................................................................................................ 7 Authorization Code ................................................................................................................................... 7 Refresh Token .......................................................................................................................................... -
Windows Server Security Best Practices
Windows Server Security – Best Practices v.3.0.5 Windows Server Security Best Practices Revised – February 7, 2020 Version 2.0.0 ______________________________________________________________________________________ Page 1 of 10 Windows Server Security – Best Practices v.3.0.5 Initial Document Created by: 2009 Windows Server Security Best Practices Committee Document Creation Date: August 21, 2009 Revision Revised by: 2019 Windows Server Security Best Practices Committee Revision Date: February 7, 2020 Version Number: 2.0.0 Acknowledgments The final release document is a collaborative work between the following committee members: Freddie Lewis Khushbu Desai Theodore McDonald Tanya Sootes Usage The ever-changing nature of information technology prevents this document from being entirely inclusive but should serve as a general guideline. This document is not intended to supersede or replace policy. Please feel free to query the Windows Server Team ([email protected]) or the Systems Administrator Group ([email protected]) for additional guidance. ______________________________________________________________________________________ Page 2 of 10 Windows Server Security – Best Practices v.3.0.5 Table of Contents Initial Document 2 Revision 2 Acknowledgments 2 Usage 2 1. Security Best Practices 5 1.1. User Environment 5 1.1.1. Server Account Control 5 1.1.2. Administrator and Equivalents 5 1.1.3. Delegating Control 5 1.1.4. Password Policy 5 1.2. File and Print Serving 5 1.2.1. Folder and NTFS Permissions 5 1.2.2. Print Management 6 1.3. Remote Access 6 1.3.1. Remote Desktop 6 1.3.2. Off-Campus Access 6 1.4. OS Configuration and Maintenance 6 1.4.1. -

Geekos Overview
CMSC 412 GeekOS overview GeekOS Overview A. Udaya Shankar [email protected] Jeffrey K. Hollingsworth [email protected] 2/12/2014 Abstract This document gives an overview of the GeekOS distribution (for 412- Spring 2014) and related background on QEMU and x86. It describes some operations in GeekOS in more detail, in particular, initialization, low-level interrupt handling and context switching, thread creation, and user program spawning. Contents 1. Introduction ..................................................................................................................................................................... 2 2. Qemu ............................................................................................................................................................................... 3 3. Intel x86 real mode .......................................................................................................................................................... 4 4. Intel x86 protected mode ................................................................................................................................................. 5 5. Booting and kernel initialization ...................................................................................................................................... 8 6. Context switching .......................................................................................................................................................... 11 6.1. Context state ............................................................................................................................................................. -

SOS Internals
Understanding a Simple Operating System SOS is a Simple Operating System designed for the 32-bit x86 architecture. Its purpose is to understand basic concepts of operating system design. These notes are meant to help you recall the class discussions. Chapter 1 : Starting Up SOS 3 Registers in the IA-32 x86 Architecture BIOS (Basic Input/Ouput System) Routines Real Mode Addressing Organization of SOS on Disk and Memory Master Boot Record SOS Startup A20 Line 32-bit Protected Mode Addressing Privilege Level Global Descriptor Table (GDT) More on Privilege Levels The GDT Setup Enabling Protected Mode Calling main() Chapter 2 : SOS Initializations 10 In main() Disk Initialization Display Initialization Setting Up Interrupt Handlers Interrupt Descriptor Table (IDT) A Default Interrupt Handler Load IDT The Programmable Interrupt Controller (PIC) The Keyboard Interrupt Handler Starting the Console Putting It All Together Chapter 3: SOS1 – Single-tasking SOS 16 Running User Programs GDT Entries Default Exception Handler User Programs Executable Format System Calls Creating User Programs The run Command Understanding a Simple Operating System The DUMB Memory Manager Program Address Space Process Control Block Switching to a User Program Kernel-Mode Stack Chapter 4 : SOS2 – Multi-tasking SOS 24 Running Multiple User Programs NAÏVE Memory Manager Programmable Interval Timer (PIT) Process States Timer Interrupt Handler Sleep System Call The run Command Process Queue The Scheduler The Complete Picture ps Command Chapter 5 : SOS3 – Paging in SOS 31 -

Assignment No. 6 Aim: Write X86/64 ALP To
Assignment No. 6 Att Perm Oral Total Sign (2) (5) (3) (10) Aim: Write X86/64 ALP to switch from real mode to protected mode and display the values of GDTR, LDTR, IDTR, TR and MSW Registers. 6.1 Theory: Real Mode: Real mode, also called real address mode, is an operating mode of all x86-compatible CPUs. Real mode is characterized by a 20-bit segmented memory address space (giving exactly 1 MiB of addressable memory) and unlimited direct software access to all addressable memory, I/O addresses and peripheral hardware. Real mode provides no support for memory protection, multitasking, or code privilege levels. Protected Mode: In computing, protected mode, also called protected virtual address mode is an operational mode of x86-compatible central processing units (CPUs). It allows system software to use features such as virtual memory, paging and safe multi-tasking designed to increase an operating system's control over application software. When a processor that supports x86 protected mode is powered on, it begins executing instructions in real mode, in order to maintain backward compatibility with earlier x86 processors. Protected mode may only be entered after the system software sets up several descriptor tables and enables the Protection Enable (PE) bit in the control register 0 (CR0). Control Register : Global Descriptor Table Register This register holds the 32-bit base address and 16-bit segment limit for the global descriptor table (GDT). When a reference is made to data in memory, a segment selector is used to find a segment descriptor in the GDT or LDT. -

Server Support Interview Questions and Answers Guide
Server Support Interview Questions And Answers Guide. Global Guideline. https://www.globalguideline.com/ Server Support Interview Questions And Answers Global Guideline . COM Server Support Job Interview Preparation Guide. Question # 1 Tell me where are cluster logs stored? Answer:- Please share your answers. Read More Answers. Question # 2 What are the Logical / Physical Structures of the AD Environment? Answer:- Active Directory Logical components are Forests, Trees, Domains, OUs and Objects. Active Directory Physical components are Domain Controllers, Sites and subnets. Read More Answers. Question # 3 What applications or services use AD application partitions? Name a couple? Answer:- Application partition contains the information of application data and other data related to application as well. But it does not contain any data related AD object such as USER, COMPUTER and GROUP. The saved data will be replicated to some of the particular DC not to all the DCs. Read More Answers. Question # 4 What are the types of hard disks used in servers? Answer:- Mostly we use scsi hardrive in server due few reason to it, high scalability & flexibility in raid array, faster from other type of hdd interface like-sata,ata,ide also it reliable & compatible with older scsi devices Read More Answers. Question # 5 What are some of the command-line tools available for managing a Windows 2003 Server/Active Directory environment? Answer:- Command Line Tools 1) GPupdate 2) Where 3) SystemInfo 4) CSVDE 5) LDIFDE 6) CMDCONS 7) Ipconfig 8) RoboCopy 9) CMDHere 10) PathPing Read More Answers. Question # 6 What if a FSMO server role fails? Answer:- FSMO roles are important role in server .