The Art of Computer Virus Research and Defense.Pdf
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Virus Bulletin, August 1994
ISSN 0956-9979 AUGUST 1994 THE INTERNATIONAL PUBLICATION ON COMPUTER VIRUS PREVENTION, RECOGNITION AND REMOVAL Editor: Richard Ford CONTENTS Technical Editor: Fridrik Skulason Consulting Editor: Edward Wilding, EDITORIAL Network Security Management, UK Bigger, By Being Better? 2 VIRUS PREVALENCE TABLE 3 NEWS Central Point Merger Completed 3 Pathogen Author Arrested 3 IBM PC VIRUSES (UPDATE) 4 IN THIS ISSUE: INSIGHT CARO explained. Many people have no idea what Schwartau on Security 6 CARO is, what it does, or how to join it. Everything you ever wanted to know about the organisation but were FEATURE afraid to ask is on pp.8-9. CARO: A Personal View 8 The professionals professional. For the first time VIRUS ANALYSES ever, VB reviews AVP, one of Russias leading virus 1. AntiCMOS - Brain Damage 9 scanners: have researchers behind the former Iron 2. A Pile of Junk? 11 Curtain made as many advances in their work as those in 3. Pure Thoughts 13 the West? FEATURE The Lotus position. Lotus has adopted a novel ap- Epidemic Virus Control 15 proach to the prevention of large-scale virus outbreaks within the company. How effective is its technique, and PRODUCT REVIEWS is it a practical alternative in other companies? See p.15. 1. AVP - A Professional Choice 18 2. NetShield 1.5 21 END NOTES & NEWS 24 VIRUS BULLETIN ©1994 Virus Bulletin Ltd, 21 The Quadrant, Abingdon, Oxfordshire, OX14 3YS, England. Tel. +44 (0)235 555139. /94/$0.00+2.50 No part of this publication may be reproduced, stored in a retrieval system, or transmitted in any form without the prior written permission of the publishers. -

Hackers Hit Supermarket Self-Checkout Lanes, Steal Money
December 15, 2011 INSIDE THIS ISSUE Hackers Hit Supermarket Self-Checkout Lanes, Steal Hackers Hit Supermarket Self- Money from Shoppers Checkout Lanes, Steal Money Ars Technica from Shoppers Microsoft's New Windows Criminals have tampered with the credit and debit card readers at self-checkout Defender Tool Runs Outside lanes in more than 20 supermarkets operated by a [U.S.] California chain, Windows allowing them to steal money from shoppers who used the compromised machines. The chain, Lucky Supermarkets, which is owned by Save Mart, is now inspecting the rest of its 234 stores in northern California and northern Nevada MICROSOFT and urging customers who used self-checkout lanes to close their bank and credit RESOURCES card accounts. Microsoft Security Home Related reading: Magnetic Strip Technology in Our Credit Cards Facilitates Fraud. Microsoft Trustworthy Computing Analysis: Microsoft Security Sites It is the holiday season so it seemed appropriate to report on security stories Worldwide affecting shoppers. Stories about electronic skimmers and identity theft are definitely not something new in our world today — as a matter of fact they are a daily occurrence. The availability of credit card skimmers for a really cheap price and the profit made when an identity is sold make this a very lucrative business. In the current economy people seem to be using this business model to earn extra money as indicated by these stories on the FBI [U.S. Federal Bureau of Investigation] website. While it is important to be extra careful about packages being stolen from your doorstep during the holidays, it pays to be extra vigilant about your credit card information and identity as well. -

59520611.Pdf
SOFTWARE • The software provides the commands that tell the hardware what tasks to perform, what to read and write, how to send the end result (the output) to a monitor and/or printer. • Software is the programs and data that a computer uses. • Software is kept on some hardware device such as a hard disk or floppy disk, but it itself is intangible. • Software consists of both programs and data. Programs are lists of instructions for the processor. Data can be any information that a program needs: character data, numerical data, image data, audio data, and countless other types. KINDS OF SOFTWARE • Application software (usually called just "applications") are programs that people use to get their work done. It may include data entry; update query and report programs, productivity software for spreadsheets, word processing, databases and custom accounting programs for payroll, billing and inventory. It is designed to help people with specific task such as making a spreadsheet of creating a graphic image. Example of Application Software: Word Processor Microsoft Word Lotus Word Pro Word Perfect Spreadsheet Software Microsoft Excel Lotus 123 Quicken Presentation Software Microsoft PowerPoint Lotus Freelance Graphics Database Software Microsoft Access Lotus Approach Web Browser Internet Explorer Netscape Navigator PIM (Personal Information Manager) - software designed to organize names, addresses, and random notes for easy and efficient retrieval. It is just like an electronic equivalent of a conven- tional book-type personal organizer. PIM usually features an automatic dialing telephone list, a programmable calendar and an automatic reminder scheduler. It is ideal for people with hectic schedules who spend a lot of time working with their computers. -
Microsoft Security Intelligence Report
Microsoft Security Intelligence Report Volume 20 | July through December, 2015 This document is for informational purposes only. MICROSOFT MAKES NO WARRANTIES, EXPRESS, IMPLIED, OR STATUTORY, AS TO THE INFORMATION IN THIS DOCUMENT. This document is provided “as-is.” Information and views expressed in this document, including URL and other Internet website references, may change without notice. You bear the risk of using it. Copyright © 2016 Microsoft Corporation. All rights reserved. The names of actual companies and products mentioned herein may be the trademarks of their respective owners. Authors Charlie Anthe Dana Kaufman Anthony Penta Cloud and Enterprise Security Azure Active Directory Team Safety Platform Nir Ben Zvi Nasos Kladakis Ina Ragragio Enterprise and Cloud Group Azure Active Directory Team Windows and Devices Group Patti Chrzan Daniel Kondratyuk Tim Rains Microsoft Digital Crimes Unit Azure Active Directory Team Commercial Communications Bulent Egilmez Andrea Lelli Paul Rebriy Office 365 - Information Windows Defender Labs Bing Protection Geoff McDonald Stefan Sellmer Elia Florio Windows Defender Labs Windows Defender Labs Windows Defender Labs Michael McLaughlin Mark Simos Chad Foster Identity Services Enterprise Cybersecurity Bing Group Nam Ng Roger Grimes Enterprise Cybersecurity Vikram Thakur Microsoft IT Group Windows Defender Labs Paul Henry Niall O'Sullivan Alex Weinert Wadeware LLC Microsoft Digital Crimes Unit Azure Active Directory Team Beth Jester Daryl Pecelj Terry Zink Windows Defender Microsoft IT Information -

Sistemi Operativi Real-Time Marco Cesati Lezione R13 Sistemi Operativi Real-Time – II Schema Della Lezione
Sistemi operativi real-time Marco Cesati Lezione R13 Sistemi operativi real-time – II Schema della lezione Caratteristiche comuni VxWorks LynxOS Sistemi embedded e real-time QNX eCos Windows Linux come RTOS 15 gennaio 2013 Marco Cesati Dipartimento di Ingegneria Civile e Ingegneria Informatica Università degli Studi di Roma Tor Vergata SERT’13 R13.1 Sistemi operativi Di cosa parliamo in questa lezione? real-time Marco Cesati In questa lezione descriviamo brevemente alcuni dei più diffusi sistemi operativi real-time Schema della lezione Caratteristiche comuni VxWorks LynxOS 1 Caratteristiche comuni degli RTOS QNX 2 VxWorks eCos 3 LynxOS Windows Linux come RTOS 4 QNX Neutrino 5 eCos 6 Windows Embedded CE 7 Linux come RTOS SERT’13 R13.2 Sistemi operativi Caratteristiche comuni dei principali RTOS real-time Marco Cesati Corrispondenza agli standard: generalmente le API sono proprietarie, ma gli RTOS offrono anche compatibilità (compliancy) o conformità (conformancy) allo standard Real-Time POSIX Modularità e Scalabilità: il kernel ha una dimensione Schema della lezione Caratteristiche comuni (footprint) ridotta e le sue funzionalità sono configurabili VxWorks Dimensione del codice: spesso basati su microkernel LynxOS QNX Velocità e Efficienza: basso overhead per cambi di eCos contesto, latenza delle interruzioni e primitive di Windows sincronizzazione Linux come RTOS Porzioni di codice non interrompibile: generalmente molto corte e di durata predicibile Gestione delle interruzioni “separata”: interrupt handler corto e predicibile, ISR lunga -
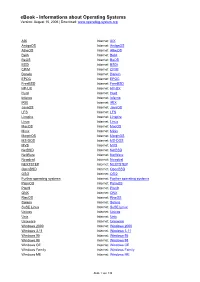
Ebook - Informations About Operating Systems Version: August 15, 2006 | Download
eBook - Informations about Operating Systems Version: August 15, 2006 | Download: www.operating-system.org AIX Internet: AIX AmigaOS Internet: AmigaOS AtheOS Internet: AtheOS BeIA Internet: BeIA BeOS Internet: BeOS BSDi Internet: BSDi CP/M Internet: CP/M Darwin Internet: Darwin EPOC Internet: EPOC FreeBSD Internet: FreeBSD HP-UX Internet: HP-UX Hurd Internet: Hurd Inferno Internet: Inferno IRIX Internet: IRIX JavaOS Internet: JavaOS LFS Internet: LFS Linspire Internet: Linspire Linux Internet: Linux MacOS Internet: MacOS Minix Internet: Minix MorphOS Internet: MorphOS MS-DOS Internet: MS-DOS MVS Internet: MVS NetBSD Internet: NetBSD NetWare Internet: NetWare Newdeal Internet: Newdeal NEXTSTEP Internet: NEXTSTEP OpenBSD Internet: OpenBSD OS/2 Internet: OS/2 Further operating systems Internet: Further operating systems PalmOS Internet: PalmOS Plan9 Internet: Plan9 QNX Internet: QNX RiscOS Internet: RiscOS Solaris Internet: Solaris SuSE Linux Internet: SuSE Linux Unicos Internet: Unicos Unix Internet: Unix Unixware Internet: Unixware Windows 2000 Internet: Windows 2000 Windows 3.11 Internet: Windows 3.11 Windows 95 Internet: Windows 95 Windows 98 Internet: Windows 98 Windows CE Internet: Windows CE Windows Family Internet: Windows Family Windows ME Internet: Windows ME Seite 1 von 138 eBook - Informations about Operating Systems Version: August 15, 2006 | Download: www.operating-system.org Windows NT 3.1 Internet: Windows NT 3.1 Windows NT 4.0 Internet: Windows NT 4.0 Windows Server 2003 Internet: Windows Server 2003 Windows Vista Internet: Windows Vista Windows XP Internet: Windows XP Apple - Company Internet: Apple - Company AT&T - Company Internet: AT&T - Company Be Inc. - Company Internet: Be Inc. - Company BSD Family Internet: BSD Family Cray Inc. -

Strategies of Computer Worms
304543_ch09.qxd 1/7/05 9:05 AM Page 313 CHAPTER 9 Strategies of Computer Worms “Worm: n., A self-replicating program able to propagate itself across network, typically having a detrimental effect.” —Concise Oxford English Dictionary, Revised Tenth Edition 313 304543_ch09.qxd 1/7/05 9:05 AM Page 314 Chapter 9—Strategies of Computer Worms 9.1 Introduction This chapter discusses the generic (or at least “typical”) structure of advanced computer worms and the common strategies that computer worms use to invade new target systems. Computer worms primarily replicate on networks, but they represent a subclass of computer viruses. Interestingly enough, even in security research communities, many people imply that computer worms are dramatically different from computer viruses. In fact, even within CARO (Computer Antivirus Researchers Organization), researchers do not share a common view about what exactly can be classified as a “worm.” We wish to share a common view, but well, at least a few of us agree that all computer worms are ultimately viruses1. Let me explain. The network-oriented infection strategy is indeed a primary difference between viruses and computer worms. Moreover, worms usually do not need to infect files but propagate as standalone programs. Additionally, several worms can take con- trol of remote systems without any help from the users, usually exploiting a vul- nerability or set of vulnerabilities. These usual characteristics of computer worms, however, do not always hold. Table 9.1 shows several well-known threats. Table -

Paradise Lost , Book III, Line 18
_Paradise Lost_, book III, line 18 %%%%%%%%%%%%%%%%%%%%%%%% ++++++++++Hacker's Encyclopedia++++++++ ===========by Logik Bomb (FOA)======== <http://www.xmission.com/~ryder/hack.html> ---------------(1997- Revised Second Edition)-------- ##################V2.5################## %%%%%%%%%%%%%%%%%%%%%%%% "[W]atch where you go once you have entered here, and to whom you turn! Do not be misled by that wide and easy passage!" And my Guide [said] to him: "That is not your concern; it is his fate to enter every door. This has been willed where what is willed must be, and is not yours to question. Say no more." -Dante Alighieri _The Inferno_, 1321 Translated by John Ciardi Acknowledgments ---------------------------- Dedicated to all those who disseminate information, forbidden or otherwise. Also, I should note that a few of these entries are taken from "A Complete List of Hacker Slang and Other Things," Version 1C, by Casual, Bloodwing and Crusader; this doc started out as an unofficial update. However, I've updated, altered, expanded, re-written and otherwise torn apart the original document, so I'd be surprised if you could find any vestiges of the original file left. I think the list is very informative; it came out in 1990, though, which makes it somewhat outdated. I also got a lot of information from the works listed in my bibliography, (it's at the end, after all the quotes) as well as many miscellaneous back issues of such e-zines as _Cheap Truth _, _40Hex_, the _LOD/H Technical Journals_ and _Phrack Magazine_; and print magazines such as _Internet Underground_, _Macworld_, _Mondo 2000_, _Newsweek_, _2600: The Hacker Quarterly_, _U.S. News & World Report_, _Time_, and _Wired_; in addition to various people I've consulted. -
Tangled Web : Tales of Digital Crime from the Shadows of Cyberspace
TANGLED WEB Tales of Digital Crime from the Shadows of Cyberspace RICHARD POWER A Division of Macmillan USA 201 West 103rd Street, Indianapolis, Indiana 46290 Tangled Web: Tales of Digital Crime Associate Publisher from the Shadows of Cyberspace Tracy Dunkelberger Copyright 2000 by Que Corporation Acquisitions Editor All rights reserved. No part of this book shall be reproduced, stored in a Kathryn Purdum retrieval system, or transmitted by any means, electronic, mechanical, pho- Development Editor tocopying, recording, or otherwise, without written permission from the Hugh Vandivier publisher. No patent liability is assumed with respect to the use of the infor- mation contained herein. Although every precaution has been taken in the Managing Editor preparation of this book, the publisher and author assume no responsibility Thomas Hayes for errors or omissions. Nor is any liability assumed for damages resulting from the use of the information contained herein. Project Editor International Standard Book Number: 0-7897-2443-x Tonya Simpson Library of Congress Catalog Card Number: 00-106209 Copy Editor Printed in the United States of America Michael Dietsch First Printing: September 2000 Indexer 02 01 00 4 3 2 Erika Millen Trademarks Proofreader Benjamin Berg All terms mentioned in this book that are known to be trademarks or ser- vice marks have been appropriately capitalized. Que Corporation cannot Team Coordinator attest to the accuracy of this information. Use of a term in this book should Vicki Harding not be regarded as affecting the validity of any trademark or service mark. Design Manager Warning and Disclaimer Sandra Schroeder Every effort has been made to make this book as complete and as accurate Cover Designer as possible, but no warranty or fitness is implied. -
Dictionary of Health Information Technology and Security
DICTIONARY OF HEALTH INFORMATION TECHNOLOGY AND SECURITY Dr. David Edward Marcinko, MBA , CFP© Certifi ed Medical Planner© Editor-in-Chief Hope Rachel Hetico, RN, MSHA, CPHQ Certifi ed Medical Planner© Managing Editor NEW YORK 33021009_FM1.indd021009_FM1.indd i 003/17/20073/17/2007 116:48:506:48:50 Copyright © 2007 Springer Publishing Company, LLC All rights reserved. No part of this publication may be reproduced, stored in a retrieval system, or transmit- ted in any form or by any means, electronic, mechanical, photocopying, recording, or otherwise, without the prior permission of Springer Publishing Company, LLC. Springer Publishing Company, LLC 11 West 42nd Street New York, NY 10036 www.springerpub.com Acquisitions Editor: Sheri W. Sussman Production Editor: Carol Cain Cover design: Mimi Flow Composition: Apex Publishing, LLC 07 08 09 10/ 5 4 3 2 1 Library of Congress Cataloging-in-Publication Data Dictionary of health information technology and security / David Edward Marcinko, editor-in-chief, Hope Rachel Hetico, managing editor. p. ; cm. Includes bibliographical references. ISBN-13: 978-0-8261-4995-4 (alk. paper) ISBN-10: 0-8261-4995-2 (alk. paper) 1. Medical informatics—Dictionaries. 2. Medicine—Information technology—Dictionaries. 3. Medical informatics—Security measures— Dictionaries. I. Marcinko, David E. (David Edward) II. Hetico, Hope R. [DNLM: 1. Informatics—Dictionary—English. 2. Medical Informatics— Dictionary—English. 3. Computer Communication Networks—Dictionary— English. 4. Computer Security—Dictionary—English. W 13 D557165 2007] R858.D53 2007 610.3—dc22 2007005879 Printed in the United States of America by RR Donnelley. 33021009_FM1.indd021009_FM1.indd iiii 003/17/20073/17/2007 116:48:516:48:51 Th e Dictionary of Health Information Technology and Security is dedicated to Edward Anthony Marcinko Sr., and Edward Anthony Marcinko Jr., of Fell’s Point, Maryland. -

The Future of Airline Distribution, 2016 - 2021
The Future of Airline Distribution, 2016 - 2021 By Henry H. Harteveldt, Atmosphere Research Group CONTENTS 3 INTRODUCTION 5 RESEARCH METHODOLOGY 7 EXECUTIVE SUMMARY 9 HOW SHOULD AIRLINES PREPARE TO SERVE THE AIRLINE TRAVELER OF 2021? 26 TECHNOLOGY INNOVATION AND THE EVOLVING TECHNOLOGY LANDSCAPE 29 AIRLINE DISTRIBUTION IN 2021 70 CONCLUSION 72 ENDNOTES © 2016 International Air Transport Association. All rights reserved. 2 INTRODUCTION Introduction from Atmosphere Research Atmosphere Research Group is honored to have Airlines that want to become true retailers are once again been selected by IATA to prepare this well-positioned to do so. Carriers have an abun- report on the future of airline distribution. We dance of technologies, including cloud comput- believe that the five-year timeframe this report ing, artificial intelligence, and mobility, that they covers – 2016 to 2021 – will see the successful can use to help them bring their products to mar- introduction of true retailing among the world’s ket in more meaningful ways. IATA’s NDC, One airlines and their distribution partners. Order, and NGISS initiatives are being brought to market to help airlines be more successful busi- This report reflects Atmosphere Research’s in- nesses. As each airline independently contem- dependent and objective analysis based on our plates its distribution strategies and tactics, we extensive industry and consumer research (for hope this report will serve as a helpful resource. more information about how the research was conducted, please refer to the “Research Method- ology” section). © 2016 International Air Transport Association. All rights reserved. 3 Future of Distribution Report 2016-2021 Introduction from IATA In 2012 IATA commissioned Atmosphere Research Game changes are prompted by consumer needs, to conduct a survey on the Future of Airline Dis- or by the ability to offer new solutions. -
Chapter 3: Viruses, Worms, and Blended Threats
Chapter 3 Chapter 3: Viruses, Worms, and Blended Threats.........................................................................46 Evolution of Viruses and Countermeasures...................................................................................46 The Early Days of Viruses.................................................................................................47 Beyond Annoyance: The Proliferation of Destructive Viruses .........................................48 Wiping Out Hard Drives—CIH Virus ...................................................................48 Virus Programming for the Masses 1: Macro Viruses...........................................48 Virus Programming for the Masses 2: Virus Generators.......................................50 Evolving Threats, Evolving Countermeasures ..................................................................51 Detecting Viruses...................................................................................................51 Radical Evolution—Polymorphic and Metamorphic Viruses ...............................53 Detecting Complex Viruses ...................................................................................55 State of Virus Detection.........................................................................................55 Trends in Virus Evolution..................................................................................................56 Worms and Vulnerabilities ............................................................................................................57