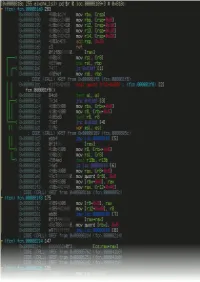
Looking Inside an Iphone App Binary
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Radare2 Book
Table of Contents introduction 1.1 Introduction 1.2 History 1.2.1 Overview 1.2.2 Getting radare2 1.2.3 Compilation and Portability 1.2.4 Compilation on Windows 1.2.5 Command-line Flags 1.2.6 Basic Usage 1.2.7 Command Format 1.2.8 Expressions 1.2.9 Rax2 1.2.10 Basic Debugger Session 1.2.11 Contributing to radare2 1.2.12 Configuration 1.3 Colors 1.3.1 Common Configuration Variables 1.3.2 Basic Commands 1.4 Seeking 1.4.1 Block Size 1.4.2 Sections 1.4.3 Mapping Files 1.4.4 Print Modes 1.4.5 Flags 1.4.6 Write 1.4.7 Zoom 1.4.8 Yank/Paste 1.4.9 Comparing Bytes 1.4.10 Visual mode 1.5 Visual Disassembly 1.5.1 2 Searching bytes 1.6 Basic Searches 1.6.1 Configurating the Search 1.6.2 Pattern Search 1.6.3 Automation 1.6.4 Backward Search 1.6.5 Search in Assembly 1.6.6 Searching for AES Keys 1.6.7 Disassembling 1.7 Adding Metadata 1.7.1 ESIL 1.7.2 Scripting 1.8 Loops 1.8.1 Macros 1.8.2 R2pipe 1.8.3 Rabin2 1.9 File Identification 1.9.1 Entrypoint 1.9.2 Imports 1.9.3 Symbols (exports) 1.9.4 Libraries 1.9.5 Strings 1.9.6 Program Sections 1.9.7 Radiff2 1.10 Binary Diffing 1.10.1 Rasm2 1.11 Assemble 1.11.1 Disassemble 1.11.2 Ragg2 1.12 Analysis 1.13 Code Analysis 1.13.1 Rahash2 1.14 Rahash Tool 1.14.1 Debugger 1.15 3 Getting Started 1.15.1 Registers 1.15.2 Remote Access Capabilities 1.16 Remoting Capabilities 1.16.1 Plugins 1.17 Plugins 1.17.1 Crackmes 1.18 IOLI 1.18.1 IOLI 0x00 1.18.1.1 IOLI 0x01 1.18.1.2 Avatao 1.18.2 R3v3rs3 4 1.18.2.1 .intro 1.18.2.1.1 .radare2 1.18.2.1.2 .first_steps 1.18.2.1.3 .main 1.18.2.1.4 .vmloop 1.18.2.1.5 .instructionset 1.18.2.1.6 -

Cygwin User's Guide
Cygwin User’s Guide Cygwin User’s Guide ii Copyright © Cygwin authors Permission is granted to make and distribute verbatim copies of this documentation provided the copyright notice and this per- mission notice are preserved on all copies. Permission is granted to copy and distribute modified versions of this documentation under the conditions for verbatim copying, provided that the entire resulting derived work is distributed under the terms of a permission notice identical to this one. Permission is granted to copy and distribute translations of this documentation into another language, under the above conditions for modified versions, except that this permission notice may be stated in a translation approved by the Free Software Foundation. Cygwin User’s Guide iii Contents 1 Cygwin Overview 1 1.1 What is it? . .1 1.2 Quick Start Guide for those more experienced with Windows . .1 1.3 Quick Start Guide for those more experienced with UNIX . .1 1.4 Are the Cygwin tools free software? . .2 1.5 A brief history of the Cygwin project . .2 1.6 Highlights of Cygwin Functionality . .3 1.6.1 Introduction . .3 1.6.2 Permissions and Security . .3 1.6.3 File Access . .3 1.6.4 Text Mode vs. Binary Mode . .4 1.6.5 ANSI C Library . .4 1.6.6 Process Creation . .5 1.6.6.1 Problems with process creation . .5 1.6.7 Signals . .6 1.6.8 Sockets . .6 1.6.9 Select . .7 1.7 What’s new and what changed in Cygwin . .7 1.7.1 What’s new and what changed in 3.2 . -

Android Malware and Analysis
ANDROID MALWARE AND ANALYSIS Ken Dunham • Shane Hartman Jose Andre Morales Manu Quintans • Tim Strazzere Click here to buy Android Malware and Analysis CRC Press Taylor & Francis Group 6000 Broken Sound Parkway NW, Suite 300 Boca Raton, FL 33487-2742 © 2015 by Taylor & Francis Group, LLC CRC Press is an imprint of Taylor & Francis Group, an Informa business No claim to original U.S. Government works Printed on acid-free paper Version Date: 20140918 International Standard Book Number-13: 978-1-4822-5219-4 (Hardback) This book contains information obtained from authentic and highly regarded sources. Reasonable efforts have been made to publish reliable data and information, but the author and publisher cannot assume responsibility for the validity of all materials or the consequences of their use. The authors and publishers have attempted to trace the copyright holders of all material reproduced in this publication and apologize to copyright holders if permission to publish in this form has not been obtained. If any copyright material has not been acknowledged please write and let us know so we may rectify in any future reprint. Except as permitted under U.S. Copyright Law, no part of this book may be reprinted, reproduced, transmit- ted, or utilized in any form by any electronic, mechanical, or other means, now known or hereafter invented, including photocopying, microfilming, and recording, or in any information storage or retrieval system, without written permission from the publishers. For permission to photocopy or use material electronically from this work, please access www.copyright. com (http://www.copyright.com/) or contact the Copyright Clearance Center, Inc. -

Chapter 1. Origins of Mac OS X
1 Chapter 1. Origins of Mac OS X "Most ideas come from previous ideas." Alan Curtis Kay The Mac OS X operating system represents a rather successful coming together of paradigms, ideologies, and technologies that have often resisted each other in the past. A good example is the cordial relationship that exists between the command-line and graphical interfaces in Mac OS X. The system is a result of the trials and tribulations of Apple and NeXT, as well as their user and developer communities. Mac OS X exemplifies how a capable system can result from the direct or indirect efforts of corporations, academic and research communities, the Open Source and Free Software movements, and, of course, individuals. Apple has been around since 1976, and many accounts of its history have been told. If the story of Apple as a company is fascinating, so is the technical history of Apple's operating systems. In this chapter,[1] we will trace the history of Mac OS X, discussing several technologies whose confluence eventually led to the modern-day Apple operating system. [1] This book's accompanying web site (www.osxbook.com) provides a more detailed technical history of all of Apple's operating systems. 1 2 2 1 1.1. Apple's Quest for the[2] Operating System [2] Whereas the word "the" is used here to designate prominence and desirability, it is an interesting coincidence that "THE" was the name of a multiprogramming system described by Edsger W. Dijkstra in a 1968 paper. It was March 1988. The Macintosh had been around for four years. -

Analyzing and Detecting Emerging Internet of Things Malware: a Graph-Based Approach
This is the author's version of an article that has been published in this journal. Changes were made to this version by the publisher prior to publication. The final version of record is available at http://dx.doi.org/10.1109/JIOT.2019.2925929 1 Analyzing and Detecting Emerging Internet of Things Malware: A Graph-based Approach Hisham Alasmaryzy, Aminollah Khormaliy, Afsah Anwary, Jeman Parky, Jinchun Choi{y, Ahmed Abusnainay, Amro Awady, DaeHun Nyang{, and Aziz Mohaiseny yUniversity of Central Florida zKing Khalid University {Inha University Abstract—The steady growth in the number of deployed Linux-like capabilities. In particular, Busybox is widely used Internet of Things (IoT) devices has been paralleled with an equal to achieve the desired functionality; based on a light-weighted growth in the number of malicious software (malware) targeting structure, it supports utilities needed for IoT devices. those devices. In this work, we build a detection mechanism of IoT malware utilizing Control Flow Graphs (CFGs). To motivate On the other hand, and due to common structures, the for our detection mechanism, we contrast the underlying char- Linux capabilities of the IoT systems inherit and extend the acteristics of IoT malware to other types of malware—Android potential threats to the Linux system. Executable and Linkable malware, which are also Linux-based—across multiple features. Format (ELF), a standard format for executable and object The preliminary analyses reveal that the Android malware have code, is sometimes exploited as an object of malware. The high density, strong closeness and betweenness, and a larger number of nodes. -

Intel® Oneapi Programming Guide
Intel® oneAPI Programming Guide Intel Corporation www.intel.com Notices and Disclaimers Contents Notices and Disclaimers....................................................................... 5 Chapter 1: Introduction oneAPI Programming Model Overview ..........................................................7 Data Parallel C++ (DPC++)................................................................8 oneAPI Toolkit Distribution..................................................................9 About This Guide.......................................................................................9 Related Documentation ..............................................................................9 Chapter 2: oneAPI Programming Model Sample Program ..................................................................................... 10 Platform Model........................................................................................ 14 Execution Model ...................................................................................... 15 Memory Model ........................................................................................ 17 Memory Objects.............................................................................. 19 Accessors....................................................................................... 19 Synchronization .............................................................................. 20 Unified Shared Memory.................................................................... 20 Kernel Programming -

Pooch Manual In
What’s New As of August 21, 2011, Pooch is updated to version 1.8.3 for use with OS X 10.7 “Lion”: Pooch users can renew their subscriptions today! Please see http://daugerresearch.com/pooch for more! On November 17, 2009, Pooch was updated to version 1.8: • Linux: Pooch can now cluster nodes running 64-bit Linux, combined with Mac • 64-bit: Major internal revisions for 64-bit, particularly updated data types and structures, for Mac OS X 10.6 "Snow Leopard" and 64-bit Linux • Sockets: Major revisions to internal networking to adapt to BSD Sockets, as recommended by Apple moving forward and required for Linux • POSIX Paths: Major revisions to internal file specification format in favor of POSIX paths, recommended by Apple moving forward and required for Linux • mDNS: Adapted usage of Bonjour service discovery to use Apple's Open Source mDNS library • Pooch Binary directory: Added Pooch binary directory support, making possible launching jobs using a remotely-compiled executable • Minor updates and fixes needed for Mac OS X 10.6 "Snow Leopard" Current Pooch users can renew their subscriptions today! Please see http://daugerresearch.com/pooch for more! On April 16, 2008, Pooch was updated to version 1.7.6: • Mac OS X 10.5 “Leopard” spurs updates in a variety of Pooch technologies: • Network Scan window • Preferences window • Keychain access • Launching via, detection of, and commands to the Terminal • Behind the Login window behavior • Other user interface and infrastructure adjustments • Open MPI support: • Complete MPI support using libraries -
SSMUG Feb Newsletter UPCOMING MEETINGS Page 2 Ƒƒ
February 2008 UPCOMING MEETINGS Apple reports best MARCH Search Engine quarterly revenue and Optimization of Web Sites. earnings in its history Special Meeting Notice Announcing financial results for its A shortened version of a seminar. fiscal 2008 first quarter, which The full seminar on Search ended December 29, 2007, Apple Engine Optimazation costs today posted revenue of $9.6 billion $39.00 but we get a free preview at and net quarterly profit of $1.58 the March meeting! billion, or $1.76 per diluted share. These results compare to revenue Meetings will be held from June of $7.1 billion and net quarterly through December at the Grande profit of $1 billion, or $1.14 per Prairie Public Library. diluted share, in the year-ago quarter. In attaining its highest revenue and earnings in company APPLE NEWS history, Apple shipped 2,319,000 Andrea Jung Joins Apple’s Macs, a 44% unit growth and 47% revenue growth over the year ago Board of Directors quarter; sold 22,121,000 iPods, representing five percent unit CUPERTINO, California—January growth and 17 percent revenue 7—Apple® today announced that growth over the year-ago quarter; Andrea Jung, chairman and chief and sold 2,315,000 iPhones in the executive officer of Avon Products, quarter. [Jan 22, 2008] was elected to Apple’s board of directors. Andrea also serves on the board of directors of the General Electric Company and is a member Tickled pink over new of the New York Presbyterian iPod nano Hospital board of trustees and the Catalyst board of directors. -
Cygwin User's Guide
Cygwin User’s Guide i Cygwin User’s Guide Cygwin User’s Guide ii Copyright © 1998, 1999, 2000, 2001, 2002, 2003, 2004, 2005, 2006, 2007, 2008, 2009, 2010, 2011, 2012 Red Hat, Inc. Permission is granted to make and distribute verbatim copies of this documentation provided the copyright notice and this per- mission notice are preserved on all copies. Permission is granted to copy and distribute modified versions of this documentation under the conditions for verbatim copying, provided that the entire resulting derived work is distributed under the terms of a permission notice identical to this one. Permission is granted to copy and distribute translations of this documentation into another language, under the above conditions for modified versions, except that this permission notice may be stated in a translation approved by the Free Software Foundation. Cygwin User’s Guide iii Contents 1 Cygwin Overview 1 1.1 What is it? . .1 1.2 Quick Start Guide for those more experienced with Windows . .1 1.3 Quick Start Guide for those more experienced with UNIX . .1 1.4 Are the Cygwin tools free software? . .2 1.5 A brief history of the Cygwin project . .2 1.6 Highlights of Cygwin Functionality . .3 1.6.1 Introduction . .3 1.6.2 Permissions and Security . .3 1.6.3 File Access . .3 1.6.4 Text Mode vs. Binary Mode . .4 1.6.5 ANSI C Library . .5 1.6.6 Process Creation . .5 1.6.6.1 Problems with process creation . .5 1.6.7 Signals . .6 1.6.8 Sockets . .6 1.6.9 Select . -

Vtouch Support User Guide Contents Introduction
vTouch Support User Guide Contents Introduction ................................................................ 3 What is vTouch Support? .......................................................................................3 Monitor Support ..................................................................................................... 3 Initial Setup ................................................................. 4 Where to get vTouch Support ................................................................................4 Installing vTouch on Big Sur ....................................................................................5 For Intel Systems ..................................................................................................... 5 For Silicon (M1 chip) Systems.................................................................................. 6 Installing UPDD in Big Sur .......................................................................................7 Intel systems ........................................................................................................... 7 Silicon systems ........................................................................................................ 7 Connection Methods ..............................................................................................8 Using the Applications ................................................. 9 UPDD Commander .................................................................................................9 Setup -

Key-Based Self-Driven Compression in Columnar Binary JSON
Otto von Guericke University of Magdeburg Department of Computer Science Master's Thesis Key-Based Self-Driven Compression in Columnar Binary JSON Author: Oskar Kirmis November 4, 2019 Advisors: Prof. Dr. rer. nat. habil. Gunter Saake M. Sc. Marcus Pinnecke Institute for Technical and Business Information Systems / Database Research Group Kirmis, Oskar: Key-Based Self-Driven Compression in Columnar Binary JSON Master's Thesis, Otto von Guericke University of Magdeburg, 2019 Abstract A large part of the data that is available today in organizations or publicly is provided in semi-structured form. To perform analytical tasks on these { mostly read-only { semi-structured datasets, Carbon archives were developed as a column-oriented storage format. Its main focus is to allow cache-efficient access to fields across records. As many semi-structured datasets mainly consist of string data and the denormalization introduces redundancy, a lot of storage space is required. However, in Carbon archives { besides a deduplication of strings { there is currently no compression implemented. The goal of this thesis is to discuss, implement and evaluate suitable compression tech- niques to reduce the amount of storage required and to speed up analytical queries on Carbon archives. Therefore, a compressor is implemented that can be configured to apply a combination of up to three different compression algorithms to the string data of Carbon archives. This compressor can be applied with a different configuration per column (per JSON object key). To find suitable combinations of compression algo- rithms for each column, one manual and two self-driven approaches are implemented and evaluated. On a set of ten publicly available semi-structured datasets of different kinds and sizes, the string data can be compressed down to about 53% on average, reducing the whole datasets' size by 20%. -
Android Reverse Engineering: Understanding Third-Party Applications
Android reverse engineering: understanding third-party applications Vicente Aguilera Díaz OWASP Spain Chapter Leader Co-founder of Internet Security Auditors [email protected] Twitter: @vaguileradiaz www.vicenteaguileradiaz.com OWASP EU Tour 2013 Copyright © The OWASP Foundation June 5, 2013. Bucharest (Romania) Permission is granted to copy, distribute and/or modify this document under the terms of the OWASP License. The OWASP Foundation http://www.owasp.org Who I am? VICENTE AGUILERA DÍAZ Co-founder of Internet Security Auditors OWASP Spain Chapter Leader More info: www.vicenteaguileradiaz.com OWASP 2 Agenda Reverse engineering: definition and objectives Application analysis workflow Malware identification in Android apps OWASP 3 Reverse engineering: definition and objectives Definition Refers to the process of analyzing a system to identify its components and their interrelationships, and create representations of the system in another form or a higher level of abstraction. [1] Objetives The purpose of reverse engineering is not to make changes or to replicate the system under analysis, but to understand how it was built. OWASP 4 Application analysis workflow Original APK Analyze Decompress and Rebuild Dissassemble APK Modify Scope of this presentation Modified APK OWASP 5 Application analysis workflow App Name SaveAPK Astro File Manager Real APK Leecher APK apktool radare2 unzip AndroidManifest.xml /lib apktool.yml /META-INF /assets /res /res resources.arsc AXMLPrinter2.jar Disasm /smali AndroidManifest.xml Human-readable