Mobile Device Management 101
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Deploying Ios and Tvos Devices Using Apple Configurator 2 and Jamf Pro
Deploying iOS and tvOS Devices Using Apple Configurator 2 and Jamf Pro Technical Paper Jamf Pro 10.9.0 or Later 7 October 2020 © copyright 2002-2020 Jamf. All rights reserved. Jamf has made all efforts to ensure that this guide is accurate. Jamf 100 Washington Ave S Suite 1100 Minneapolis, MN 55401-2155 (612) 605-6625 Jamf, the Jamf Logo, JAMF SOFTWARE®, and the JAMF SOFTWARE Logo® are registered or common law trademarks of JAMF SOFTWARE, LLC in the U.S. and other countries. Apple, Apple Configurator 2, the Apple logo, Apple TV, iTunes, Mac, macOS, OS X, and tvOS are trademarks of Apple Inc., registered in the United States and other countries. IOS is a trademark or registered trademark of Cisco in the U.S. and other countries. All other product and service names mentioned herein are either registered trademarks or trademarks of their respective companies. Contents Contents 4 Introduction 4 What's in This Guide 4 Additional Resources 5 Choosing a Deployment Method 6 Supervision Identities 6 Use a Supervision Identity from Apple Configurator 2 7 Create and Use a Supervision Identity from Jamf Pro 8 Automated Enrollment 8 Requirements 8 Deploying Devices Using Automated Enrollment 11 Manual Enrollment with an Enrollment URL 11 Requirements 11 Deploy Devices Using Manual Enrollment with an Enrollment URL 13 Further Considerations 14 Manual Enrollment with an Enrollment Profile 14 Requirements 14 Create an Enrollment Profile 14 Create and Upload the Supervision Identity 14 Create the "Prepare" Blueprint 15 Create the "Enroll" Blueprint 15 Deploy Devices Using Manual Enrollment with an Enrollment Profile 3 Introduction What's in This Guide This guide provides step-by-step instructions for deploying iOS and tvOS devices using Apple Configurator 2 and Jamf Pro. -
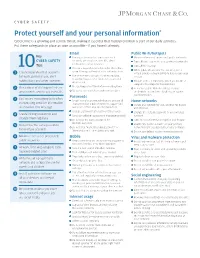
Protect Yourself and Your Personal Information*
CYBER SAFETY Protect yourself and your personal information * Cybercrime is a growing and serious threat, making it essential that fraud prevention is part of our daily activities. Put these safeguards in place as soon as possible—if you haven’t already. Email Public Wi-Fi/hotspots Key Use separate email accounts: one each Minimize the use of unsecured, public networks CYBER SAFETY for work, personal use, user IDs, alerts Turn oF auto connect to non-preferred networks 10 notifications, other interests Tips Turn oF file sharing Choose a reputable email provider that oFers spam filtering and multi-factor authentication When public Wi-Fi cannot be avoided, use a 1 Create separate email accounts virtual private network (VPN) to help secure your for work, personal use, alert Use secure messaging tools when replying session to verified requests for financial or personal notifications and other interests information Disable ad hoc networking, which allows direct computer-to-computer transmissions Encrypt important files before emailing them 2 Be cautious of clicking on links or Never use public Wi-Fi to enter personal attachments sent to you in emails Do not open emails from unknown senders credentials on a website; hackers can capture Passwords your keystrokes 3 Use secure messaging tools when Create complex passwords that are at least 10 Home networks transmitting sensitive information characters; use a mix of numbers, upper- and Create one network for you, another for guests via email or text message lowercase letters and special characters and children -
View Managing Devices and Corporate Data On
Overview Managing Devices & Corporate Data on iOS Overview Overview Contents Businesses everywhere are empowering their employees with iPhone and iPad. Overview Management Basics The key to a successful mobile strategy is balancing IT control with user Separating Work and enablement. By personalizing iOS devices with their own apps and content, Personal Data users take greater ownership and responsibility, leading to higher levels of Flexible Management Options engagement and increased productivity. This is enabled by Apple’s management Summary framework, which provides smart ways to manage corporate data and apps discretely, seamlessly separating work data from personal data. Additionally, users understand how their devices are being managed and trust that their privacy is protected. This document offers guidance on how essential IT control can be achieved while at the same time keeping users enabled with the best tools for their job. It complements the iOS Deployment Reference, a comprehensive online technical reference for deploying and managing iOS devices in your enterprise. To refer to the iOS Deployment Reference, visit help.apple.com/deployment/ios. Managing Devices and Corporate Data on iOS July 2018 2 Management Basics Management Basics With iOS, you can streamline iPhone and iPad deployments using a range of built-in techniques that allow you to simplify account setup, configure policies, distribute apps, and apply device restrictions remotely. Our simple framework With Apple’s unified management framework in iOS, macOS, tvOS, IT can configure and update settings, deploy applications, monitor compliance, query devices, and remotely wipe or lock devices. The framework supports both corporate-owned and user-owned as well as personally-owned devices. -

5Tips for Securing Your Mobile Device for Telehealth
Tips for Securing your Mobile Device 5for Telehealth The Health Insurance Portability and Accountability Act (HIPAA) requires that providers protect your information and not share it without your permission. Telehealth providers are required by law to secure medical information that can be shared electronically by encrypting messages and adding other safeguards into the software they use. However, patients’ devices on the receiving end of care often do not always have these safeguards while some medical devices have been shown to be vulnerable to hackers. It is therefore the responsibility of the patient to secure personal devices. 01 Use a PIN or Passcode to secure device Securing your mobile device is important for ensuring that others do not have access to your confidential information and applications. To protect your iPad, iPhone, Android phone you need to set a passcode. It is a 4- to 6-digit PIN used to grant access to the device, like the code you use for an ATM bank card or a debit card. Securing your Apple (iPhone and iPad) and Android devices In addition to allowing you to secure your phone with a passcode, Newer Apple and Android devices also use biometrics called Touch ID and Face ID on Apple, and Face recognition, Irises, and Fingerprints on some Android devices. These tools use your Face, eyes, and fingerprints as unique identifiers to help secure your devices. Face ID and Face recognition use your facial features in order to unlock your device. Touch ID, which is no longer being used on newer versions of iPhone and iPad, and Fingerprints on Android is a fingerprinting tool. -

Security Checklist
WHITE PAPER Security Checklist Implementing the Center for Internet Security Benchmark Recommendations for securing iPad and iPhone. The Center for Internet Security (CIS) benchmark for iOS is widely regarded as a comprehensive checklist for organizations to follow to secure iPad and iPhone devices. This white paper explains how to implement the independent organization’s recommendations. To see how Jamf Now can help secure and manage your iOS devices, visit www.jamf.com. WHO IS THE CIS? The Center for Internet Security, Inc. (CIS) is a 501c3 nonprofit organization focused on enhancing the cybersecurity readiness and response of public and private sector entities. HOW THE CIS BENCHMARK WAS CREATED The CIS Benchmark was created using a consensus review process comprised of subject matter experts. Consensus participants provide perspective from a diverse set of backgrounds including consulting, software development, audit and compliance, security research, operations, government and legal. Each CIS benchmark undergoes two phases of consensus review. The first phase occurs during initial benchmark development. During this phase, subject matter experts convene to discuss, create and test working drafts of the benchmark. This discussion occurs until consensus has been reached on benchmark recommendations. The second phase begins after the benchmark has been published. During this phase, all feedback provided by the Internet community is reviewed by the consensus team for incorporation in the benchmark. If you are interested in participating in the consensus process, please visit https://www.cisecurity.org/communities/. CIS Management Basics WHAT IS MDM? WHAT ARE BLUEPRINTS? WHAT IS APNs? Mobile device management (MDM) Blueprints define settings on Apple Apple Push Notification service is Apple’s built-in management devices and are distributed to the (APNs) is required for iPad and iPhone framework for iOS, iPadOS, macOS devices via Jamf Now. -

Legal-Process Guidelines for Law Enforcement
Legal Process Guidelines Government & Law Enforcement within the United States These guidelines are provided for use by government and law enforcement agencies within the United States when seeking information from Apple Inc. (“Apple”) about customers of Apple’s devices, products and services. Apple will update these Guidelines as necessary. All other requests for information regarding Apple customers, including customer questions about information disclosure, should be directed to https://www.apple.com/privacy/contact/. These Guidelines do not apply to requests made by government and law enforcement agencies outside the United States to Apple’s relevant local entities. For government and law enforcement information requests, Apple complies with the laws pertaining to global entities that control our data and we provide details as legally required. For all requests from government and law enforcement agencies within the United States for content, with the exception of emergency circumstances (defined in the Electronic Communications Privacy Act 1986, as amended), Apple will only provide content in response to a search issued upon a showing of probable cause, or customer consent. All requests from government and law enforcement agencies outside of the United States for content, with the exception of emergency circumstances (defined below in Emergency Requests), must comply with applicable laws, including the United States Electronic Communications Privacy Act (ECPA). A request under a Mutual Legal Assistance Treaty or the Clarifying Lawful Overseas Use of Data Act (“CLOUD Act”) is in compliance with ECPA. Apple will provide customer content, as it exists in the customer’s account, only in response to such legally valid process. -

Certified Device List for Mobiliti – Phone Channel
Mobiliti™ Certified Device List December 2019 - ASP Version CONFIDENTIAL – LIMITED: Distribution restricted to Fiserv employees and clients © 2011-2019 Fiserv, Inc. or its affiliates. All rights reserved. This work is confidential and its use is strictly limited. Use is permitted only in accordance with the terms of the agreement under which it was furnished. Any other use, duplication, or dissemination without the prior written consent of Fiserv, Inc. or its affiliates is strictly prohibited. The information contained herein is subject to change without notice. Except as specified by the agreement under which the materials are furnished, Fiserv, Inc. and its affiliates do not accept any liabilities with respect to the information contained herein and is not responsible for any direct, indirect, special, consequential or exemplary damages resulting from the use of this information. No warranties, either express or implied, are granted or extended by this document. http://www.fiserv.com Fiserv is a registered trademark of Fiserv, Inc. Other brands and their products are trademarks or registered trademarks of their respective holders and should be noted as such. CONFIDENTIAL – LIMITED: Distribution restricted to Fiserv employees and clients Contents Revision and History .................................................................................................................. 4 Certified Device List for Mobiliti – Phone Channel .................................................................. 5 Scope ..................................................................................................................................................... -

Apple Submission NIST RFI Privacy Framework
Apple Submission in Response to NIST Request for Information Developing a Privacy Framework, Docket No. 181101997-8997-01 January 14, 2018 Apple appreciates this opportunity to comment on NIST’s Request For Information (RFI) regarding its proposed Privacy Framework. Apple supports the development of the Privacy Framework and NIST’s engagement on this important topic. At Apple, we believe privacy is a fundamental human right. We have long embraced the principles of privacy-by-design and privacy-by-default, not because the law requires it, but because it is the right thing for our customers. We’ve proved time and again that great experiences don’t have to come at the expense of privacy and security. Instead, they support them. Every Apple product is designed from the ground up to protect our users’ personal information. We’ve shown that protecting privacy is possible at every level of the technical stack and shown how these protections must evolve over time. Users can protect their devices with Face ID or Touch ID, where their data is converted into a mathematical representation that is encrypted and used only by the Secure Enclave1 on their device, cannot be accessed by the operating system, and is never stored on Apple servers. In communication, we use end-to-end encryption to protect iMessage and FaceTime conversations so that no one but the participants can access them. On the web, Safari was the first browser to block third-party cookies by default, and we introduced Intelligent Tracking Protection to combat the growth of online tracking. When we use data to create better experiences for our users, we work hard to do it in a way that doesn’t compromise privacy. -

Read Apple Pay Faqs
Apple Pay FAQs What is Apple Pay? Apple pay is an easy, secure and private way to pay on iPhone, iPad, Apple Watch and Mac. You can make purchases in stores by holding your compatible device near a contactless reader at participating merchants or when shopping online at participating merchants. You can find more information about Apple Pay and how to set up your card at apple.com. What do I need to use Apple Pay? • Eligible device • Supported card from Texas DPS Credit Union • Latest version of iOS, watchOS or macOS • An Apple ID signed into iCloud What Apple devices are compatible? • iPhone models with Face ID • iPhone models with Touch ID, except for iPhone 5s • iPad Pro, iPad Air, iPad and iPad mini models with Touch ID or Face ID • Apple Watch Series 1 and 2 and later • Mac models with Touch ID How do I add my card to Apple Pay? • On your compatible device, access the Settings app, scroll down to Wallet & Apple Pay, then click Add Card, under Payment Cards and follow the prompts. The card information will be verified and confirm whether you can use your card with Apple Pay. If the Credit Union needs more information to verify your card, you will receive a prompt to contact us. After your card has been verified, you can start using Apple Pay. OR • Go to the Wallet and tap the plus sign. Follow the prompts to add a new card. Tap Next. The card information will be verified and confirm whether you can use your card with Apple Pay. -

Jamf Pro Server
Jamf Pro Administrator's Guide Version 10.1.0 © copyright 2002-2017 Jamf. All rights reserved. Divide is a trademark or registered trademark of Divide, Inc. Jamf has made all efforts to ensure that this guide is accurate. eDirectory is a trademark of Novell, Inc. in the United States and other countries. Jamf 100 Washington Ave S Suite 1100 Google, Android, Google Chrome, and Google Minneapolis, MN 55401-2155 Play are trademarks or registered trademarks of (612) 605-6625 Google Inc. Intel and McAfee Endpoint Protection are either Under the copyright laws, this publication may registered trademarks or trademarks of the Intel not be copied, in whole or in part, without the Corporation in the United States and other written consent of Jamf. countries. The CASPER SUITE, COMPOSER®, Likewise is a trademark of Likewise Software. the COMPOSER Logo®, Jamf, the Jamf Logo, JAMF SOFTWARE®, the JAMF SOFTWARE Logo®, Linux is a registered trademark of Linus Torvalds RECON®, and the RECON Logo® are registered or in the United States and other countries. common law trademarks of JAMF SOFTWARE, LLC in the U.S. and other countries. Microsoft, Microsoft Intune, Active Directory, Azure, Excel, OneNote, Outlook, PowerPoint, ADmitMac is a registered trademark of Thursby Silverlight, Windows, Windows Server, and all Software Systems, Inc. references to Microsoft software are either registered trademarks or trademarks of Adobe, Adobe AIR, Adobe Bridge, Adobe Microsoft Corporation in the United States Premier Pro, Acrobat, After Effects, Creative and/or other countries. Suite, Dreamweaver, Fireworks, Flash Player, Illustrator, InDesign, Lightroom, Photoshop, Mozilla and Firefox are registered trademarks of Prelude, Shockwave, and all references to Adobe the Mozilla Foundation. -

Jamf Pro Installation and Configuration Guide for Mac Version 10.5.0 © Copyright 2002-2018 Jamf
Jamf Pro Installation and Configuration Guide for Mac Version 10.5.0 © copyright 2002-2018 Jamf. All rights reserved. Jamf has made all efforts to ensure that this guide is accurate. Jamf 100 Washington Ave S Suite 1100 Minneapolis, MN 55401-2155 (612) 605-6625 Under the copyright laws, this publication may not be copied, in whole or in part, without the written consent of Jamf. Amazon and Amazon RDS are trademarks of Amazon.com, Inc. or its affiliates in the United States and/or other countries. Apache Tomcat and Tomcat are trademarks of the Apache Software Foundation. Apple, Mac, macOS, OS X, and Safari are trademarks of Apple, Inc. registered in the U.S. and other countries. The CASPER SUITE, COMPOSER®, the COMPOSER Logo®, Jamf, the Jamf Logo, JAMF SOFTWARE®, the JAMF SOFTWARE Logo®, RECON®, and the RECON Logo® are registered or common law trademarks of JAMF SOFTWARE, LLC in the U.S. and other countries. Chrome and Google are trademarks or registered trademarks of Google Inc. Firefox is a registered trademark of the Mozilla Foundation. Intel is a registered trademark of the Intel Corporation in the U.S. and other countries. Java and MySQL are registered trademarks of Oracle and/or its affiliates. Other names may be trademarks of their respective owners. Microsoft, Microsoft Edge, and Windows are either registered trademarks or trademarks of Microsoft Corporation in the United States and other countries. Ubuntu is a registered trademark of Canonical Ltd. All other product and service names mentioned herein are either registered trademarks or trademarks of their respective companies. -

Your Action Is Needed
FOR iPHONE/iPAD OWNERS: YOUR ACTION IS NEEDED YOU MUST FOLLOW the steps below to disconnect your original device from iCloud and unlock it. STEP 1: DISCONNECT FROM iCLOUD If your device is damaged but still working: Go to Settings > Tap on your name/ID > iCloud > Find My iPhone > Turn off the Find My iPhone button > Enter your Apple ID and Password > Tap Turn Off If your device is damaged and won’t turn on: Go to iCloud.com and enter your Apple ID and Password > At the Two-Factor Authentication page, click Find My iPhone > Click the down arrow next to All Devices > Click on the device you are removing > Click Erase iPhone > Click Erase > Enter your Apple ID Password > Answer any Security Questions > Click Continue > At Enter Phone Number prompt, select Next > At Enter Message prompt, select Done > iPhone Erase Pending will be displayed > Click the down arrow next to iPhone > Click the x to the right of your device > Click Remove If your device is lost or stolen: Go to iCloud.com and enter your Apple ID and Password > At the Two-Factor Authentication page, click Find My iPhone > Click the down arrow next to All Devices > Click on the lost/stolen device > Click Lost Mode (iOS 6 or later), or Lock (iOS 5 or earlier) > Follow the onscreen instructions STEP 2: UNLOCK YOUR DEVICE Go to Settings > Tap Touch ID/Face ID & Passcode (Passcode for devices without a Touch or Face ID Sensor) > Enter Passcode > Turn Passcode Off > Turn Off > If prompted, enter Passcode For further assistance, please visit support.apple.com.