An Analysis of a Sparse Linearization Attack on the Advanced Encryption Standard
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
The Data Encryption Standard (DES) – History
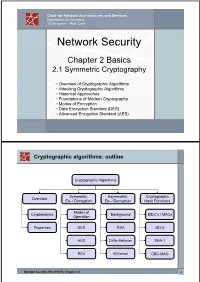
Chair for Network Architectures and Services Department of Informatics TU München – Prof. Carle Network Security Chapter 2 Basics 2.1 Symmetric Cryptography • Overview of Cryptographic Algorithms • Attacking Cryptographic Algorithms • Historical Approaches • Foundations of Modern Cryptography • Modes of Encryption • Data Encryption Standard (DES) • Advanced Encryption Standard (AES) Cryptographic algorithms: outline Cryptographic Algorithms Symmetric Asymmetric Cryptographic Overview En- / Decryption En- / Decryption Hash Functions Modes of Cryptanalysis Background MDC’s / MACs Operation Properties DES RSA MD-5 AES Diffie-Hellman SHA-1 RC4 ElGamal CBC-MAC Network Security, WS 2010/11, Chapter 2.1 2 Basic Terms: Plaintext and Ciphertext Plaintext P The original readable content of a message (or data). P_netsec = „This is network security“ Ciphertext C The encrypted version of the plaintext. C_netsec = „Ff iThtIiDjlyHLPRFxvowf“ encrypt key k1 C P key k2 decrypt In case of symmetric cryptography, k1 = k2. Network Security, WS 2010/11, Chapter 2.1 3 Basic Terms: Block cipher and Stream cipher Block cipher A cipher that encrypts / decrypts inputs of length n to outputs of length n given the corresponding key k. • n is block length Most modern symmetric ciphers are block ciphers, e.g. AES, DES, Twofish, … Stream cipher A symmetric cipher that generats a random bitstream, called key stream, from the symmetric key k. Ciphertext = key stream XOR plaintext Network Security, WS 2010/11, Chapter 2.1 4 Cryptographic algorithms: overview -

Related-Key Cryptanalysis of 3-WAY, Biham-DES,CAST, DES-X, Newdes, RC2, and TEA
Related-Key Cryptanalysis of 3-WAY, Biham-DES,CAST, DES-X, NewDES, RC2, and TEA John Kelsey Bruce Schneier David Wagner Counterpane Systems U.C. Berkeley kelsey,schneier @counterpane.com [email protected] f g Abstract. We present new related-key attacks on the block ciphers 3- WAY, Biham-DES, CAST, DES-X, NewDES, RC2, and TEA. Differen- tial related-key attacks allow both keys and plaintexts to be chosen with specific differences [KSW96]. Our attacks build on the original work, showing how to adapt the general attack to deal with the difficulties of the individual algorithms. We also give specific design principles to protect against these attacks. 1 Introduction Related-key cryptanalysis assumes that the attacker learns the encryption of certain plaintexts not only under the original (unknown) key K, but also under some derived keys K0 = f(K). In a chosen-related-key attack, the attacker specifies how the key is to be changed; known-related-key attacks are those where the key difference is known, but cannot be chosen by the attacker. We emphasize that the attacker knows or chooses the relationship between keys, not the actual key values. These techniques have been developed in [Knu93b, Bih94, KSW96]. Related-key cryptanalysis is a practical attack on key-exchange protocols that do not guarantee key-integrity|an attacker may be able to flip bits in the key without knowing the key|and key-update protocols that update keys using a known function: e.g., K, K + 1, K + 2, etc. Related-key attacks were also used against rotor machines: operators sometimes set rotors incorrectly. -

Performance and Energy Efficiency of Block Ciphers in Personal Digital Assistants
Performance and Energy Efficiency of Block Ciphers in Personal Digital Assistants Creighton T. R. Hager, Scott F. Midkiff, Jung-Min Park, Thomas L. Martin Bradley Department of Electrical and Computer Engineering Virginia Polytechnic Institute and State University Blacksburg, Virginia 24061 USA {chager, midkiff, jungmin, tlmartin} @ vt.edu Abstract algorithms may consume more energy and drain the PDA battery faster than using less secure algorithms. Due to Encryption algorithms can be used to help secure the processing requirements and the limited computing wireless communications, but securing data also power in many PDAs, using strong cryptographic consumes resources. The goal of this research is to algorithms may also significantly increase the delay provide users or system developers of personal digital between data transmissions. Thus, users and, perhaps assistants and applications with the associated time and more importantly, software and system designers need to energy costs of using specific encryption algorithms. be aware of the benefits and costs of using various Four block ciphers (RC2, Blowfish, XTEA, and AES) were encryption algorithms. considered. The experiments included encryption and This research answers questions regarding energy decryption tasks with different cipher and file size consumption and execution time for various encryption combinations. The resource impact of the block ciphers algorithms executing on a PDA platform with the goal of were evaluated using the latency, throughput, energy- helping software and system developers design more latency product, and throughput/energy ratio metrics. effective applications and systems and of allowing end We found that RC2 encrypts faster and uses less users to better utilize the capabilities of PDA devices. -

Hemiunu Used Numerically Tagged Surface Ratios to Mark Ceilings Inside the Great Pyramid Hinting at Designed Spaces Still Hidden Within
Archaeological Discovery, 2018, 6, 319-337 http://www.scirp.org/journal/ad ISSN Online: 2331-1967 ISSN Print: 2331-1959 Hemiunu Used Numerically Tagged Surface Ratios to Mark Ceilings inside the Great Pyramid Hinting at Designed Spaces Still Hidden Within Manu Seyfzadeh Institute for the Study of the Origins of Civilization (ISOC)1, Boston University’s College of General Studies, Boston, USA How to cite this paper: Seyfzadeh, M. Abstract (2018). Hemiunu Used Numerically Tagged Surface Ratios to Mark Ceilings inside the In 1883, W. M. Flinders Petrie noticed that the vertical thickness and height Great Pyramid Hinting at Designed Spaces of certain stone courses of the Great Pyramid2 of Khufu/Cheops at Giza, Still Hidden Within. Archaeological Dis- Egypt markedly increase compared to those immediately lower periodically covery, 6, 319-337. https://doi.org/10.4236/ad.2018.64016 and conspicuously interrupting a general trend of progressive course thinning towards the summit. Having calculated the surface area of each course, Petrie Received: September 10, 2018 further noted that the courses immediately below such discrete stone thick- Accepted: October 5, 2018 Published: October 8, 2018 ness peaks tended to mark integer multiples of 1/25th of the surface area at ground level. Here I show that the probable architect of the Great Pyramid, Copyright © 2018 by author and Khufu’s vizier Hemiunu, conceptualized its vertical construction design using Scientific Research Publishing Inc. surface areas based on the same numerical principles used to design his own This work is licensed under the Creative Commons Attribution International mastaba in Giza’s western cemetery and conspicuously used this numerical License (CC BY 4.0). -

Development of the Advanced Encryption Standard
Volume 126, Article No. 126024 (2021) https://doi.org/10.6028/jres.126.024 Journal of Research of the National Institute of Standards and Technology Development of the Advanced Encryption Standard Miles E. Smid Formerly: Computer Security Division, National Institute of Standards and Technology, Gaithersburg, MD 20899, USA [email protected] Strong cryptographic algorithms are essential for the protection of stored and transmitted data throughout the world. This publication discusses the development of Federal Information Processing Standards Publication (FIPS) 197, which specifies a cryptographic algorithm known as the Advanced Encryption Standard (AES). The AES was the result of a cooperative multiyear effort involving the U.S. government, industry, and the academic community. Several difficult problems that had to be resolved during the standard’s development are discussed, and the eventual solutions are presented. The author writes from his viewpoint as former leader of the Security Technology Group and later as acting director of the Computer Security Division at the National Institute of Standards and Technology, where he was responsible for the AES development. Key words: Advanced Encryption Standard (AES); consensus process; cryptography; Data Encryption Standard (DES); security requirements, SKIPJACK. Accepted: June 18, 2021 Published: August 16, 2021; Current Version: August 23, 2021 This article was sponsored by James Foti, Computer Security Division, Information Technology Laboratory, National Institute of Standards and Technology (NIST). The views expressed represent those of the author and not necessarily those of NIST. https://doi.org/10.6028/jres.126.024 1. Introduction In the late 1990s, the National Institute of Standards and Technology (NIST) was about to decide if it was going to specify a new cryptographic algorithm standard for the protection of U.S. -
Symmetric Encryption: AES
Symmetric Encryption: AES Yan Huang Credits: David Evans (UVA) Advanced Encryption Standard ▪ 1997: NIST initiates program to choose Advanced Encryption Standard to replace DES ▪ Why not just use 3DES? 2 AES Process ▪ Open Design • DES: design criteria for S-boxes kept secret ▪ Many good choices • DES: only one acceptable algorithm ▪ Public cryptanalysis efforts before choice • Heavy involvements of academic community, leading public cryptographers ▪ Conservative (but “quick”): 4 year process 3 AES Requirements ▪ Secure for next 50-100 years ▪ Royalty free ▪ Performance: faster than 3DES ▪ Support 128, 192 and 256 bit keys • Brute force search of 2128 keys at 1 Trillion keys/ second would take 1019 years (109 * age of universe) 4 AES Round 1 ▪ 15 submissions accepted ▪ Weak ciphers quickly eliminated • Magenta broken at conference! ▪ 5 finalists selected: • MARS (IBM) • RC6 (Rivest, et. al.) • Rijndael (Belgian cryptographers) • Serpent (Anderson, Biham, Knudsen) • Twofish (Schneier, et. al.) 5 AES Evaluation Criteria 1. Security Most important, but hardest to measure Resistance to cryptanalysis, randomness of output 2. Cost and Implementation Characteristics Licensing, Computational, Memory Flexibility (different key/block sizes), hardware implementation 6 AES Criteria Tradeoffs ▪ Security v. Performance • How do you measure security? ▪ Simplicity v. Complexity • Need complexity for confusion • Need simplicity to be able to analyze and implement efficiently 7 Breaking a Cipher ▪ Intuitive Impression • Attacker can decrypt secret messages • Reasonable amount of work, actual amount of ciphertext ▪ “Academic” Ideology • Attacker can determine something about the message • Given unlimited number of chosen plaintext-ciphertext pairs • Can perform a very large number of computations, up to, but not including, 2n, where n is the key size in bits (i.e. -
Security in Sensor Networks in Section 6
CS 588: Cryptography SSeeccuurriittyy iinn SSeennssoorr NNeettwwoorrkkss By: Stavan Parikh Tracy Barger David Friedman Date: December 6, 2001 Table of Contents 1. INTRODUCTION .................................................................................................................................... 1 2. SENSOR NETWORKS............................................................................................................................ 2 2.1. CONSTRAINTS...................................................................................................................................... 2 2.1.1. Hardware .................................................................................................................................... 2 2.1.2. Energy......................................................................................................................................... 2 2.1.3. Communication & Addressing .................................................................................................... 3 2.1.4. Trust Model................................................................................................................................. 3 2.2. SECURITY REQUIREMENTS .................................................................................................................. 3 2.2.1. Confidentiality............................................................................................................................. 3 2.2.2. Authenticity ................................................................................................................................ -

Applications of Search Techniques to Cryptanalysis and the Construction of Cipher Components. James David Mclaughlin Submitted F
Applications of search techniques to cryptanalysis and the construction of cipher components. James David McLaughlin Submitted for the degree of Doctor of Philosophy (PhD) University of York Department of Computer Science September 2012 2 Abstract In this dissertation, we investigate the ways in which search techniques, and in particular metaheuristic search techniques, can be used in cryptology. We address the design of simple cryptographic components (Boolean functions), before moving on to more complex entities (S-boxes). The emphasis then shifts from the construction of cryptographic arte- facts to the related area of cryptanalysis, in which we first derive non-linear approximations to S-boxes more powerful than the existing linear approximations, and then exploit these in cryptanalytic attacks against the ciphers DES and Serpent. Contents 1 Introduction. 11 1.1 The Structure of this Thesis . 12 2 A brief history of cryptography and cryptanalysis. 14 3 Literature review 20 3.1 Information on various types of block cipher, and a brief description of the Data Encryption Standard. 20 3.1.1 Feistel ciphers . 21 3.1.2 Other types of block cipher . 23 3.1.3 Confusion and diffusion . 24 3.2 Linear cryptanalysis. 26 3.2.1 The attack. 27 3.3 Differential cryptanalysis. 35 3.3.1 The attack. 39 3.3.2 Variants of the differential cryptanalytic attack . 44 3.4 Stream ciphers based on linear feedback shift registers . 48 3.5 A brief introduction to metaheuristics . 52 3.5.1 Hill-climbing . 55 3.5.2 Simulated annealing . 57 3.5.3 Memetic algorithms . 58 3.5.4 Ant algorithms . -

(Advance Encryption Scheme (AES)) and Multicrypt Encryption Scheme
International Journal of Scientific and Research Publications, Volume 2, Issue 4, April 2012 1 ISSN 2250-3153 Analysis of comparison between Single Encryption (Advance Encryption Scheme (AES)) and Multicrypt Encryption Scheme Vibha Verma, Mr. Avinash Dhole Computer Science & Engineering, Raipur Institute of Technology, Raipur, Chhattisgarh, India [email protected], [email protected] Abstract- Advanced Encryption Standard (AES) is a suggested a couple of changes, which Rivest incorporated. After specification for the encryption of electronic data. It supersedes further negotiations, the cipher was approved for export in 1989. DES. The algorithm described by AES is a symmetric-key Along with RC4, RC2 with a 40-bit key size was treated algorithm, meaning the same key is used for both encrypting and favourably under US export regulations for cryptography. decrypting the data. Multicrypt is a scheme that allows for the Initially, the details of the algorithm were kept secret — encryption of any file or files. The scheme offers various private- proprietary to RSA Security — but on 29th January, 1996, source key encryption algorithms, such as DES, 3DES, RC2, and AES. code for RC2 was anonymously posted to the Internet on the AES (Advanced Encryption Standard) is the strongest encryption Usenet forum, sci.crypt. Mentions of CodeView and SoftICE and is used in various financial and public institutions where (popular debuggers) suggest that it had been reverse engineered. confidential, private information is important. A similar disclosure had occurred earlier with RC4. RC2 is a 64-bit block cipher with a variable size key. Its 18 Index Terms- AES, Multycrypt, Cryptography, Networking, rounds are arranged as a source-heavy Feistel network, with 16 Encryption, DES, 3DES, RC2 rounds of one type (MIXING) punctuated by two rounds of another type (MASHING). -

Kapitel 6 Der Advanced Encryption Standard Rijndael
Kap. 6: Der Advanced Encryption Standard Rijndael Dieses ging von Anfang an davon aus, daß der zu wahlende¨ Algorith- mus stark¨ er sein musse¨ als Triple DES; er sollte zwanzig bis dreißig Jahre lang anwendbar sein und dementsprechende Sicherheit bieten. Nach einer internationalen Konferenz uber¨ die Auswahlkriterien am 15. April 1997 verof¨ fentlichte es am 12. September 1997 die endgultige¨ Ausschreibung. Kapitel 6 Minimalanforderung an die einzureichenden Algorithmen waren da- nach, daß es sich um symmetrische Blockchiffren handeln muß, die min- Der Advanced Encryption Standard Rijndael destens eine Blocklange¨ von 128 Bit bei Schlussell¨ angen¨ von 128 Bit, 192 Bit und 256 Bit vorsieht. §1: Geschichte und Auswahlkriterien Als Kriterien fur¨ die Wahl zwischen den einzelnen Algorithmen wurden DES wurde in Zusammenarbeit mit der National Security Agency der die folgenden Aspekte genannt: Vereinigten Staaten von IBM entwickelt und dann als amerikanischer 1. Sicherheit: Wie sicher ist der Algorithmus im Vergleich zu den Standard verkundet.¨ Diese Vorgehensweise weckte von Anfang an den anderen Kandidaten? Inwieweit ist seine Ausgabe ununterscheidbar Verdacht, daß moglicherweise¨ eine Falltur¨ “ eingebaut sei, insbeson- von der einer Zufallspermutation? Wie gut ist die mathematische ” dere da zumindest ursprunglich¨ nicht alle Design-Kriterien publiziert Basis fur¨ die Sicherheit des Algorithmus begrundet?¨ (Im Gegensatz wurden. zu DES sollten dieses Mal alle Kriterien publiziert werden.) 2. Kosten: Welche Lizensgebuhren¨ werden fallig?¨ -

An Introduction of Advanced Encryption Algorithm: a Preview
International Journal of Science and Research (IJSR) ISSN (Online): 2319-7064 Impact Factor (2012): 3.358 An Introduction of Advanced Encryption Algorithm: A Preview Asfiya Shireen Shaikh Mukhtar1, Ghousiya Farheen Shaikh Mukhtar2 Master of Computer Application Radhikatai Pandav College of Engineering, Nagpur, Maharashtra, India Master of Computer Application, S S Maniyar College of computer and Management, Nagpur, Maharashtra, India Abstract: In a recent era, Network security is playing the important role in communication system. Almost all organization either private or government can transfer the data over internet. So the security of electronic data is very important issue. Cryptography is technique to secure the data by using Encryption and Decryption Process. Cryptography is science of “secret information “it is the art of hiding the information by Encryption and Decryption. Encryption is the process to convert the Plaintext into unreadable format known ciphertext and Decryption is the process to convert cipher text into plaintext. Numbers of algorithm used for encryption and Decryption like DES, 2DES, 3DES, RSA, RC2, RC4, RSA, IDEA, Blowfish, AES but AES algorithm is more efficient and Effective AES algorithm is 128 bit block oriented symmetric key encryption algorithm. In this paper I describe the brief introduction of AES algorithm .My paper is divide into following Section. In I Section I Present the brief introduction of AES (Advance Encryption Standard) Algorithm, In II Section I Present the different Cryptography algorithm, In III Section I Present comparison of AES algorithm with different cryptography algorithm, In IV Section I Present the Modified AES algorithm and Text and Image Encryption by using AES algorithm, In V Section I Present Future Enhancement of AES algorithm and Conclusion. -

Basic Cryptanalysis Methods on Block Ciphers
1 BASIC CRYPTANALYSIS METHODS ON BLOCK CIPHERS A THESIS SUBMITTED TO THE GRADUATE SCHOOL OF APPLIED MATHEMATICS OF MIDDLE EAST TECHNICAL UNIVERSITY BY DILEK˙ C¸ELIK˙ IN PARTIAL FULFILLMENT OF THE REQUIREMENTS FOR THE DEGREE OF MASTER OF SCIENCE IN CRYPTOGRAPHY MAY 2010 Approval of the thesis: BASIC CRYPTANALYSIS METHODS ON BLOCK CIPHERS submitted by DILEK˙ C¸ELIK˙ in partial fulfillment of the requirements for the degree of Master of Science in Department of Cryptography, Middle East Technical University by, Prof. Dr. Ersan AKYILDIZ Director, Graduate School of Applied Mathematics Prof. Dr. Ferruh OZBUDAK¨ Head of Department, Cryptography Assoc. Prof. Dr. Ali DOGANAKSOY˘ Supervisor, Department of Mathematics, METU Examining Committee Members: Prof. Dr. Ferruh OZBUDAK¨ Department of Mathematics, METU Assoc. Prof. Dr. Ali DOGANAKSOY˘ Department of Mathematics, METU Assist. Prof. Dr. Zulf¨ ukar¨ SAYGI Department of Mathematics, TOBB ETU Dr. Muhiddin UGUZ˘ Department of Mathematics, METU Dr. Murat CENK Department of Cryptography, METU Date: I hereby declare that all information in this document has been obtained and presented in accordance with academic rules and ethical conduct. I also declare that, as required by these rules and conduct, I have fully cited and referenced all material and results that are not original to this work. Name, Last Name: DILEK˙ C¸ELIK˙ Signature : iii ABSTRACT BASIC CRYPTANALYSIS METHODS ON BLOCK CIPHERS C¸elik, Dilek M.S., Department of Cryptography Supervisor : Assoc. Prof. Dr. Ali DOGANAKSOY˘ May 2010, 119 pages Differential cryptanalysis and linear cryptanalysis are the first significant methods used to at- tack on block ciphers. These concepts compose the keystones for most of the attacks in recent years.