Computational and Algebraic Aspects of the Advanced Encryption Standard
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
The Data Encryption Standard (DES) – History
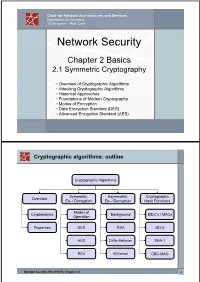
Chair for Network Architectures and Services Department of Informatics TU München – Prof. Carle Network Security Chapter 2 Basics 2.1 Symmetric Cryptography • Overview of Cryptographic Algorithms • Attacking Cryptographic Algorithms • Historical Approaches • Foundations of Modern Cryptography • Modes of Encryption • Data Encryption Standard (DES) • Advanced Encryption Standard (AES) Cryptographic algorithms: outline Cryptographic Algorithms Symmetric Asymmetric Cryptographic Overview En- / Decryption En- / Decryption Hash Functions Modes of Cryptanalysis Background MDC’s / MACs Operation Properties DES RSA MD-5 AES Diffie-Hellman SHA-1 RC4 ElGamal CBC-MAC Network Security, WS 2010/11, Chapter 2.1 2 Basic Terms: Plaintext and Ciphertext Plaintext P The original readable content of a message (or data). P_netsec = „This is network security“ Ciphertext C The encrypted version of the plaintext. C_netsec = „Ff iThtIiDjlyHLPRFxvowf“ encrypt key k1 C P key k2 decrypt In case of symmetric cryptography, k1 = k2. Network Security, WS 2010/11, Chapter 2.1 3 Basic Terms: Block cipher and Stream cipher Block cipher A cipher that encrypts / decrypts inputs of length n to outputs of length n given the corresponding key k. • n is block length Most modern symmetric ciphers are block ciphers, e.g. AES, DES, Twofish, … Stream cipher A symmetric cipher that generats a random bitstream, called key stream, from the symmetric key k. Ciphertext = key stream XOR plaintext Network Security, WS 2010/11, Chapter 2.1 4 Cryptographic algorithms: overview -
Symmetric Encryption: AES
Symmetric Encryption: AES Yan Huang Credits: David Evans (UVA) Advanced Encryption Standard ▪ 1997: NIST initiates program to choose Advanced Encryption Standard to replace DES ▪ Why not just use 3DES? 2 AES Process ▪ Open Design • DES: design criteria for S-boxes kept secret ▪ Many good choices • DES: only one acceptable algorithm ▪ Public cryptanalysis efforts before choice • Heavy involvements of academic community, leading public cryptographers ▪ Conservative (but “quick”): 4 year process 3 AES Requirements ▪ Secure for next 50-100 years ▪ Royalty free ▪ Performance: faster than 3DES ▪ Support 128, 192 and 256 bit keys • Brute force search of 2128 keys at 1 Trillion keys/ second would take 1019 years (109 * age of universe) 4 AES Round 1 ▪ 15 submissions accepted ▪ Weak ciphers quickly eliminated • Magenta broken at conference! ▪ 5 finalists selected: • MARS (IBM) • RC6 (Rivest, et. al.) • Rijndael (Belgian cryptographers) • Serpent (Anderson, Biham, Knudsen) • Twofish (Schneier, et. al.) 5 AES Evaluation Criteria 1. Security Most important, but hardest to measure Resistance to cryptanalysis, randomness of output 2. Cost and Implementation Characteristics Licensing, Computational, Memory Flexibility (different key/block sizes), hardware implementation 6 AES Criteria Tradeoffs ▪ Security v. Performance • How do you measure security? ▪ Simplicity v. Complexity • Need complexity for confusion • Need simplicity to be able to analyze and implement efficiently 7 Breaking a Cipher ▪ Intuitive Impression • Attacker can decrypt secret messages • Reasonable amount of work, actual amount of ciphertext ▪ “Academic” Ideology • Attacker can determine something about the message • Given unlimited number of chosen plaintext-ciphertext pairs • Can perform a very large number of computations, up to, but not including, 2n, where n is the key size in bits (i.e. -

Security Evaluation of GOST 28147-89 in View of International Standardisation
Security Evaluation of GOST 28147-89 In View Of International Standardisation Nicolas T. Courtois University College London, Gower Street, London, UK, [email protected] Abstract. GOST 28147-89 is is a well-known 256-bit block cipher which is a plausible alternative for AES-256 and triple DES which is known to have a much lower implementation cost, see [31]. GOST is implemented in standard crypto libraries such as OpenSSL and Crypto++ [25, 45], and is increasingly popular and used also outside its country of origin and on the Internet [23, 24, 31]. In 2010 GOST was submitted to ISO, to become a worldwide industrial encryption standard. Until 2011 researchers unanimously agreed that GOST could or should be very secure, which was summarized in 2010 in these words: \despite considerable cryptanalytic e®orts spent in the past 20 years, GOST is still not broken", see [31]. Unhappily, it was recently discovered that GOST can be broken and is a deeply flawed cipher. There is a very con- siderable amount of recent not yet published work on cryptanalysis of GOST known to us, see [12]. One simple attack was already presented in February at FSE 2011, see [28]. In this short paper we describe an- other attack, to illustrate the fact that there is now plethora of attacks on GOST, which require much less memory, and don't even require the reflection property [29] to hold, without which the recent attack from [28] wouldn't work. We are also aware of many substantially faster at- tacks and of numerous special even weaker cases, see [12]. -

Thesis Submitted for the Degree of Doctor of Philosophy
Optimizations in Algebraic and Differential Cryptanalysis Theodosis Mourouzis Department of Computer Science University College London A thesis submitted for the degree of Doctor of Philosophy January 2015 Title of the Thesis: Optimizations in Algebraic and Differential Cryptanalysis Ph.D. student: Theodosis Mourouzis Department of Computer Science University College London Address: Gower Street, London, WC1E 6BT E-mail: [email protected] Supervisors: Nicolas T. Courtois Department of Computer Science University College London Address: Gower Street, London, WC1E 6BT E-mail: [email protected] Committee Members: 1. Reviewer 1: Professor Kenny Paterson 2. Reviewer 2: Dr Christophe Petit Day of the Defense: Signature from head of PhD committee: ii Declaration I herewith declare that I have produced this paper without the prohibited assistance of third parties and without making use of aids other than those specified; notions taken over directly or indirectly from other sources have been identified as such. This paper has not previously been presented in identical or similar form to any other English or foreign examination board. The following thesis work was written by Theodosis Mourouzis under the supervision of Dr Nicolas T. Courtois at University College London. Signature from the author: Abstract In this thesis, we study how to enhance current cryptanalytic techniques, especially in Differential Cryptanalysis (DC) and to some degree in Al- gebraic Cryptanalysis (AC), by considering and solving some underlying optimization problems based on the general structure of the algorithm. In the first part, we study techniques for optimizing arbitrary algebraic computations in the general non-commutative setting with respect to sev- eral metrics [42, 44]. -

Public Evaluation Report UEA2/UIA2
ETSI/SAGE Version: 2.0 Technical report Date: 9th September, 2011 Specification of the 3GPP Confidentiality and Integrity Algorithms 128-EEA3 & 128-EIA3. Document 4: Design and Evaluation Report LTE Confidentiality and Integrity Algorithms 128-EEA3 & 128-EIA3. page 1 of 43 Document 4: Design and Evaluation report. Version 2.0 Document History 0.1 20th June 2010 First draft of main technical text 1.0 11th August 2010 First public release 1.1 11th August 2010 A few typos corrected and text improved 1.2 4th January 2011 A modification of ZUC and 128-EIA3 and text improved 1.3 18th January 2011 Further text improvements including better reference to different historic versions of the algorithms 1.4 1st July 2011 Add a new section on timing attacks 2.0 9th September 2011 Final deliverable LTE Confidentiality and Integrity Algorithms 128-EEA3 & 128-EIA3. page 2 of 43 Document 4: Design and Evaluation report. Version 2.0 Reference Keywords 3GPP, security, SAGE, algorithm ETSI Secretariat Postal address F-06921 Sophia Antipolis Cedex - FRANCE Office address 650 Route des Lucioles - Sophia Antipolis Valbonne - FRANCE Tel.: +33 4 92 94 42 00 Fax: +33 4 93 65 47 16 Siret N° 348 623 562 00017 - NAF 742 C Association à but non lucratif enregistrée à la Sous-Préfecture de Grasse (06) N° 7803/88 X.400 c= fr; a=atlas; p=etsi; s=secretariat Internet [email protected] http://www.etsi.fr Copyright Notification No part may be reproduced except as authorized by written permission. The copyright and the foregoing restriction extend to reproduction in all media. -

Kapitel 6 Der Advanced Encryption Standard Rijndael
Kap. 6: Der Advanced Encryption Standard Rijndael Dieses ging von Anfang an davon aus, daß der zu wahlende¨ Algorith- mus stark¨ er sein musse¨ als Triple DES; er sollte zwanzig bis dreißig Jahre lang anwendbar sein und dementsprechende Sicherheit bieten. Nach einer internationalen Konferenz uber¨ die Auswahlkriterien am 15. April 1997 verof¨ fentlichte es am 12. September 1997 die endgultige¨ Ausschreibung. Kapitel 6 Minimalanforderung an die einzureichenden Algorithmen waren da- nach, daß es sich um symmetrische Blockchiffren handeln muß, die min- Der Advanced Encryption Standard Rijndael destens eine Blocklange¨ von 128 Bit bei Schlussell¨ angen¨ von 128 Bit, 192 Bit und 256 Bit vorsieht. §1: Geschichte und Auswahlkriterien Als Kriterien fur¨ die Wahl zwischen den einzelnen Algorithmen wurden DES wurde in Zusammenarbeit mit der National Security Agency der die folgenden Aspekte genannt: Vereinigten Staaten von IBM entwickelt und dann als amerikanischer 1. Sicherheit: Wie sicher ist der Algorithmus im Vergleich zu den Standard verkundet.¨ Diese Vorgehensweise weckte von Anfang an den anderen Kandidaten? Inwieweit ist seine Ausgabe ununterscheidbar Verdacht, daß moglicherweise¨ eine Falltur¨ “ eingebaut sei, insbeson- von der einer Zufallspermutation? Wie gut ist die mathematische ” dere da zumindest ursprunglich¨ nicht alle Design-Kriterien publiziert Basis fur¨ die Sicherheit des Algorithmus begrundet?¨ (Im Gegensatz wurden. zu DES sollten dieses Mal alle Kriterien publiziert werden.) 2. Kosten: Welche Lizensgebuhren¨ werden fallig?¨ -

Algebraic Complexity Reduction and Cryptanalysis of GOST Nicolas T
Algebraic Complexity Reduction and Cryptanalysis of GOST Nicolas T. Courtois University College London, Gower Street, London, UK Abstract. GOST 28147-89 is a well-known Russian government encryp- tion standard. Its large key size of 256 bits at a particularly low imple- mentation cost [83] make that it is widely implemented and used [70, 105, 66, 83, 88]. In 2010 GOST was submitted to ISO to become an inter- national standard. GOST was analysed by Schneier, Biham, Biryukov, Dunkelman, Wagner, various Australian, Japanese, and Russian scien- tists, and all researchers seemed to agree that it looks quite secure. Though the internal structure of GOST seems quite weak compared to DES, and in particular the diffusion is not quite as good, it is always stip- ulated that this should be compensated by a large number of 32 rounds cf. [63, 101, 100, 8] and by the additional non-linearity and diffusion pro- vided by modular additions [63, 84]. At Crypto 2008 the hash function based on this cipher was broken. Yet as far as traditional encryption ap- plications with keys generated at random are concerned, until 2011 no cryptographically significant attack on GOST was found. In this paper we present several new attacks on full 32-rounds GOST. Our methodology is derived from the idea of conditional algebraic attacks on block ciphers [25, 20] which can be defined as attacks in which the prob- lem of key recovery is written as a problem of solving a large system of algebraic equations, and where the attacker makes some \clever" as- sumptions on the cipher which lead to an important simplification in the algebraic description of the problem, which makes it solvable in practice if the assumptions hold. -

Basic Cryptanalysis Methods on Block Ciphers
1 BASIC CRYPTANALYSIS METHODS ON BLOCK CIPHERS A THESIS SUBMITTED TO THE GRADUATE SCHOOL OF APPLIED MATHEMATICS OF MIDDLE EAST TECHNICAL UNIVERSITY BY DILEK˙ C¸ELIK˙ IN PARTIAL FULFILLMENT OF THE REQUIREMENTS FOR THE DEGREE OF MASTER OF SCIENCE IN CRYPTOGRAPHY MAY 2010 Approval of the thesis: BASIC CRYPTANALYSIS METHODS ON BLOCK CIPHERS submitted by DILEK˙ C¸ELIK˙ in partial fulfillment of the requirements for the degree of Master of Science in Department of Cryptography, Middle East Technical University by, Prof. Dr. Ersan AKYILDIZ Director, Graduate School of Applied Mathematics Prof. Dr. Ferruh OZBUDAK¨ Head of Department, Cryptography Assoc. Prof. Dr. Ali DOGANAKSOY˘ Supervisor, Department of Mathematics, METU Examining Committee Members: Prof. Dr. Ferruh OZBUDAK¨ Department of Mathematics, METU Assoc. Prof. Dr. Ali DOGANAKSOY˘ Department of Mathematics, METU Assist. Prof. Dr. Zulf¨ ukar¨ SAYGI Department of Mathematics, TOBB ETU Dr. Muhiddin UGUZ˘ Department of Mathematics, METU Dr. Murat CENK Department of Cryptography, METU Date: I hereby declare that all information in this document has been obtained and presented in accordance with academic rules and ethical conduct. I also declare that, as required by these rules and conduct, I have fully cited and referenced all material and results that are not original to this work. Name, Last Name: DILEK˙ C¸ELIK˙ Signature : iii ABSTRACT BASIC CRYPTANALYSIS METHODS ON BLOCK CIPHERS C¸elik, Dilek M.S., Department of Cryptography Supervisor : Assoc. Prof. Dr. Ali DOGANAKSOY˘ May 2010, 119 pages Differential cryptanalysis and linear cryptanalysis are the first significant methods used to at- tack on block ciphers. These concepts compose the keystones for most of the attacks in recent years. -

Algebraic Cryptanalysis of the Data Encryption Standard
Algebraic Cryptanalysis of the Data Encryption Standard Nicolas T. Courtois1 and Gregory V. Bard2 1University College of London, Gower Street, London, UK, [email protected] 2Fordham University, NY, USA [email protected] Abstract. In spite of growing importance of AES, the Data Encryption Standard is by no means obsolete. DES has never been broken from the practical point of view. The triple DES is believed very secure, is widely used, especially in the financial sector, and should remain so for many many years to come. In addition, some doubts have been risen whether its replacement AES is secure, given the extreme level of “algebraic vulnerability” of the AES S-boxes (their low I/O degree and exceptionally large number of quadratic I/O equations). Is DES secure from the point of view of algebraic cryptanalysis, a new very fast-growing area of research? We do not really hope to break it, but just to advance the field of cryptanalysis. At a first glance, DES seems to be a very poor target — as there is (apparently) no strong algebraic structure of any kind in DES. However in [14] it was shown that “small” S-boxes always have a low I/O degree (cubic for DES as we show below). In addition, due to their low gate count requirements, by introducing additional variables, we can always get an extremely sparse system of quadratic equations. To assess the algebraic vulnerabilities is the easy part, that may appear unproductive. In this paper we demonstrate that in this way, several interesting attacks on a real-life “industrial” block cipher can be found. -

Statistical Cryptanalysis of Block Ciphers
STATISTICAL CRYPTANALYSIS OF BLOCK CIPHERS THÈSE NO 3179 (2005) PRÉSENTÉE À LA FACULTÉ INFORMATIQUE ET COMMUNICATIONS Institut de systèmes de communication SECTION DES SYSTÈMES DE COMMUNICATION ÉCOLE POLYTECHNIQUE FÉDÉRALE DE LAUSANNE POUR L'OBTENTION DU GRADE DE DOCTEUR ÈS SCIENCES PAR Pascal JUNOD ingénieur informaticien dilpômé EPF de nationalité suisse et originaire de Sainte-Croix (VD) acceptée sur proposition du jury: Prof. S. Vaudenay, directeur de thèse Prof. J. Massey, rapporteur Prof. W. Meier, rapporteur Prof. S. Morgenthaler, rapporteur Prof. J. Stern, rapporteur Lausanne, EPFL 2005 to Mimi and Chlo´e Acknowledgments First of all, I would like to warmly thank my supervisor, Prof. Serge Vaude- nay, for having given to me such a wonderful opportunity to perform research in a friendly environment, and for having been the perfect supervisor that every PhD would dream of. I am also very grateful to the president of the jury, Prof. Emre Telatar, and to the reviewers Prof. em. James L. Massey, Prof. Jacques Stern, Prof. Willi Meier, and Prof. Stephan Morgenthaler for having accepted to be part of the jury and for having invested such a lot of time for reviewing this thesis. I would like to express my gratitude to all my (former and current) col- leagues at LASEC for their support and for their friendship: Gildas Avoine, Thomas Baign`eres, Nenad Buncic, Brice Canvel, Martine Corval, Matthieu Finiasz, Yi Lu, Jean Monnerat, Philippe Oechslin, and John Pliam. With- out them, the EPFL (and the crypto) would not be so fun! Without their support, trust and encouragement, the last part of this thesis, FOX, would certainly not be born: I owe to MediaCrypt AG, espe- cially to Ralf Kastmann and Richard Straub many, many, many hours of interesting work. -

Evaluating Algebraic Attacks on the AES
Diplomarbeit Evaluating Algebraic Attacks on the AES Ralf-Philipp Weinmann <[email protected]> Betreuer: Prof. Dr. J. Buchmann, Fachbereich Informatik Fachgebiet Kryptographie und Computeralgebra, Technische Universit¨atDarmstadt 2 Contents 1 Introduction 5 1.1 Algebraic descriptions of AES . 5 1.2 Block ciphers . 6 1.2.1 Iterated Block Ciphers . 6 1.2.2 Key-Iterated Block Ciphers . 6 1.3 Classification of attacks on block ciphers . 7 1.4 Scope of this thesis . 7 2 The family of Mini-Rijndaels 9 2.1 Parameters . 10 2.2 An algorithmic cipher description . 10 2.2.1 AddRoundKey ............................. 10 2.2.2 SubElement .............................. 11 2.2.3 ShiftRows ............................... 12 2.2.4 MixColumns .............................. 12 2.2.5 Key scheduling . 13 3 Systems of polynomial equations 15 3.1 Terminology . 15 3.2 Constructing the equations . 16 3.3 Constructing a system over F2 ........................ 18 3.3.1 The S-Boxes . 18 3.3.2 The linear layer . 19 3.3.3 The key schedule . 20 3.4 Embedding the cipher . 20 3.4.1 The S-Boxes . 20 3.4.2 The linear layer . 21 3.4.3 The key schedule . 22 4 Linearization attacks 31 4.1 Linearization . 31 4.2 The XL Algorithm . 32 4.3 Relinearization . 32 4.4 Extended Sparse Linearization . 33 4.4.1 The final step . 33 3 4 CONTENTS 4.4.2 An example for XSL . 34 5 Observations and experimental results 43 5.1 Implementation . 43 5.2 The original examples . 44 5.3 Applying XSL to a Mini-Rijndael . -

Application of the Composite Field in the Design of an Improved AES S-Box Based on Inversion
INNOV 2014 : The Third International Conference on Communications, Computation, Networks and Technologies Application of the Composite Field in the Design of an Improved AES S-box Based on Inversion Zhao Wang, Xiao Zhang, Sitao Wang, Zhisong Hao and Zhiming Zheng School of Mathematics and Systems Science & LMIB Beijing University of Aeronautics and Astronautics Beijing, China Email: [email protected], [email protected], [email protected], [email protected], [email protected]. Abstract—The hardware implementation of the Substitution-Box AES S-Box (S-box) of the Advanced Encryption Standard (AES) always inv A,v employs composite field GF ((2n)2) to obtain better efficiency. In this paper, an improved class of S-boxes by direct inversion in composite field is presented, and the choice of the subfield leading Hardware Implementation of AES S-Box to the most efficient implementation is discussed. Eliminating the T inv' T -1 A,v field isomorphic transformations, such a composite field is easier to fix and the resulting hardware implementation is more efficient Our S-Box than that of AES S-box. Some common cryptographic character- inv' A,v istics for the composite field based S-boxes are examined, and it turns out that direct inversion in composite field does not weaken the cryptographic characteristics. In addition, a demonstration inv The inversion on GF(28) for the immunity against the potential algebraic attack on AES inv' The inversion on GF((24)2) or GF(((22)2)2) with the replacement of our S-box is given, and it is proven A,v The affine transformAtion of AES T The field conversion from GF(28) to GF((24)2) or GF(((22)2)2) that the revised AES is even more secure than the original AES -1 against the algebraic attack.