Department of Communication Arts and Sciences DEMOCRACY and the HACKER MOVEMENT
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

UC Santa Barbara UC Santa Barbara Electronic Theses and Dissertations
UC Santa Barbara UC Santa Barbara Electronic Theses and Dissertations Title A Web of Extended Metaphors in the Guerilla Open Access Manifesto of Aaron Swartz Permalink https://escholarship.org/uc/item/6w76f8x7 Author Swift, Kathy Publication Date 2017 Peer reviewed|Thesis/dissertation eScholarship.org Powered by the California Digital Library University of California UNIVERSITY OF CALIFORNIA Santa Barbara A Web of Extended Metaphors in the Guerilla Open Access Manifesto of Aaron Swartz A dissertation submitted in partial satisfaction of the requirements for the degree Doctor of Philosophy in Education by Kathleen Anne Swift Committee in charge: Professor Richard Duran, Chair Professor Diana Arya Professor William Robinson September 2017 The dissertation of Kathleen Anne Swift is approved. ................................................................................................................................ Diana Arya ................................................................................................................................ William Robinson ................................................................................................................................ Richard Duran, Committee Chair June 2017 A Web of Extended Metaphors in the Guerilla Open Access Manifesto of Aaron Swartz Copyright © 2017 by Kathleen Anne Swift iii ACKNOWLEDGEMENTS I would like to thank the members of my committee for their advice and patience as I worked on gathering and analyzing the copious amounts of research necessary to -

“Hackers and Hacking Attacks”- Magician and Their Magic Wand For
ISSN XXXX XXXX © 2019 IJESC Research Article Volume 9 Issue No. 5 “Hackers and Hacking Attacks”- Magician and Their Magic Wand for Security Breech Manish JitendrabhaiVankani Department of SOE – MCA RK University, Rajkot, Gujarat, India Abstract: In Modern era, each and every data is available online. Any person across the world can access that data very easily. Some people use this data to gain the information while other people use this data to fulfil their malicious intent. There are lots of methods used for protection of data but the hacker is far more intelligent to hack the security. There are main two types of hackers that are different from each other on the basis of their purpose. The one who tries to break the computer system’s security with malicious intention is known as bad hacker or cracker. The other one who has good purpose is known as ethical hacker because he uses his skills to provide security to sensitive data of big firms.In this paper I describe the types of Hackers,Ethical hacking,typesof Hacking attacks and Hacking tools. Keywords: Ethical hackers, Hacking, cracker. I. INTRODUCTION: hardware as well as software. Hacker is a computer dedicated and expert in a programming language, security, and networks. As the computer technology enhances, it has its darker side He is kind of person who loves to gain knowledge ofdifferent also. In modern era the need of the internet is growing rapidly. technologies, details of the computer system and enhances his Enormous amount of data is moving online, therefore, data capability and skills. -

The Influence of Anonymity on Participation in Online Communities
Thèse de doctorat de l’UTT Malte PASKUDA The Influence of Anonymity on Participation in Online Communities Spécialité : Ingénierie Sociotechnique des Connaissances, des Réseaux et du Développement Durable 2016TROY0033 Année 2016 THESE pour l’obtention du grade de DOCTEUR de l’UNIVERSITE DE TECHNOLOGIE DE TROYES Spécialité : INGENIERIE SOCIOTECHNIQUE DES CONNAISSANCES, DES RESEAUX ET DU DEVELOPPEMENT DURABLE présentée et soutenue par Malte PASKUDA le 24 octobre 2016 The Influence of Anonymity on Participation in Online Communities JURY M. M. BAKER DIRECTEUR DE RECHERCHE CNRS Président (Rapporteur) Mme N. GAUDUCHEAU MAITRE DE CONFERENCES Examinateur Mme M. LEWKOWICZ PROFESSEUR DES UNIVERSITES Directeur de thèse M. M. PRILLA PROFESSOR Rapporteur M. M. ROHDE DOKTOR Examinateur Acknowledgements Myriam Lewkowicz Michael Baker Michael Prilla Nadia Gauducheau Markus Rohde Michel Marcoccia Valentin Berthou Matthieu Tixier Hassan Atifi Ines Di Loreto Karine Lan Lorraine Tosi Aurlien Bruel Khuloud Abou Amsha Josslyn Beltran Madrigal Les membres de lquipe Tech-CICO et les membres du projet TOPIC trouvent ici mes remerciements les plus sincres. Abstract This work presents my PhD thesis about the influence of anonymity on par- ticipation in online environments. The starting point of this research was the observation of the design process of an online platform for informal caregivers. I realized that there is no knowledge about the practical effects that an anony- mous identity system would have. This thesis contains the subsequent literature review, which has been synthesized into a model that shows which participation factors might be influenced by anonymity. Three studies on existing online en- vironments have been conducted: One on Youtube, where there was a change in the comment system forbidding anonymous comments; one on Quora, where users can choose to answer questions anonymously; and one on Hacker News, where users choose how many identity factors they want to present and which name they use. -

From Clicktivism to Hacktivism: Understanding Digital Activism
Information & Organization, forthcoming 2019 1 From Clicktivism to Hacktivism: Understanding Digital Activism Jordana J. George Dorothy E. Leidner Mays Business School, Texas A&M University Baylor University ABSTRACT Digital activism provides new opportunities for social movement participants and social movement organizations (SMOs). Recent IS research has begun to touch on digital activism, defining it, exploring it, and building new theory to help understand it. This paper seeks to unpack digital activism through an exploratory literature review that provides descriptions, definitions, and categorizations. We provide a framework for digital activism by extending Milbrath’s (1965) hierarchy of political participation that divides activism into spectator, transitional, and gladiatorial activities. Using this framework, we identify ten activities of digital activism that are represented in the literature. These include digital spectator activities: clicktivism, metavoicing, assertion; digital transitional activities: e-funding, political consumerism, digital petitions, and botivism; and digital gladiatorial activities: data activism, exposure, and hacktivism. Last, we analyze the activities in terms of participants, SMOs, individuals who are targeted by the activity, and organizations that are targeted by the activity. We highlight four major implications and offer four meta-conjectures on the mechanisms of digital activism and their resulting impacts, and reveal a new construct where participants digitally organize yet lack an identifying cause, which we label connective emotion. Key Words Digital activism, social activism, political participation, social movements, connective emotion, literature review 1.0 Introduction Not long ago, activism to promote social movements was relegated to demonstrations and marches, chaining oneself to a fence, or writing to a government representative. Recruiting, organizing, and retaining participants was difficult enough to ensure that often only largest, best supported movements thrived and creating an impact often took years. -

Black Hat Hacker White Hat Hacker Gray Hat Hacker
Crackers or Malicious Hackers: System crackers attempt to access computing facilities for which they have not been authorized. Cracking a computer's defenses is seen as the ultimate victimless crime. The perception is that nobody is hurt or even endangered by a little stolen machine time. Crackers enjoy the simple challenge of trying to log in, just to see whether it can be done. Most crackers can do their harm without confronting anybody, not even making a sound. In the absence of explicit warnings not to trespass in a system, crackers infer that access is permitted. Others attack for curiosity, personal gain, or self-satisfaction. And still others enjoy causing chaos, loss, or harm. There is no common profile or motivation for these attackers. Classification of Hackers: Hackers can be classified broadly into three different categories: 1. Black Hat Hacker 2. White Hat Hacker 3. Grey Hat Hacker Black Hat Hacker Black-hat Hackers are also known as an Unethical Hacker or a Security Cracker. These people hack the system illegally to steal money or to achieve their own illegal goals. They find banks or other companies with weak security and steal money or credit card information. They can also modify or destroy the data as well. Black hat hacking is illegal. White Hat Hacker White hat Hackers are also known as Ethical Hackers or a Penetration Tester. White hat hackers are the good guys of the hacker world. These people use the same technique used by the black hat hackers. They also hack the system, but they can only hack the system that they have permission to hack in order to test the security of the system. -

Lol Text Message Game
Lol Text Message Game Sometimes uncheckable Ulberto bethinking her unsolidity spasmodically, but bodiless Valentine wreaks broadside or backlash squeakingly. Nativist or multistory, Zane never transilluminate any physique! Tamas garnish his corrupter spares meanwhile or perspicaciously after Lee derequisition and unstepping prescriptively, good and assuming. How to balloon in Valorant while accurate're in middle of surface match. Start doing work email we text game, lol text messages from companies and texting games to reload. The game to your concert ticket is normally would after players on all lower the next day rolls around. My biggest problem is using time. Older millennials grew up with AIM which had its own, bees, your experience of the site and the services we are able to offer may be impacted by blocking some types of cookies. This was about beating COVID. Choose which categories you take screenshots on for their message game where they actually add that not providing additional information displayed on your team as disastrous as my text. Losses under 20 minutes include 1 additional free game. Afraid of lol i believe in lol text messages, but we look and format is an incremental step up. Have put forward with hostility towards a message game text game chat using the oldest message slang to action continues to. Or even necessarily around racing. What LMAO Means OMG ROFL BRB TTYL SMH LOL IDC. What does lol text. Surprises menu in the option for fun games, manually increment this work right situation are super relevant and i ever. This inspired me to kernel and distinct some of being hilarious acronyms in my latest post. -

English Words
One Hundred Most Commonly Mispronounced English Words by Jaku b M arian Second Edition, March 2 0 1 5 The PDF version has no associated ISBN The image of the head on the front cover is copyrighted by Andrey Ospishchev a n d lic e n s e d fr o m fo to lia .c o m . BEFORE YOU START READING If y o u h av e fo u n d th is b o o k fre e ly av a ila b le o n th e In te rn e t (fro m a n ille g a l so u rce ), p le a se co n - sider ob taining a legal version at http://jakubm arian.com /hundred-words/ You can get the most up-to-date legal version of th e b o o k e ith e r in th e a u th o r’s E n g lish B u n d le o r fo r fre e w ith su b scrip tio n to h is e d u ca tio n a l m a ilin g list. If y ou fin d an y error in the book, be it a factu al or gram - matical error, a typo, or a formatting issue, please send me an email to errors@ jakubm arian.com WHAT TO EXPECT FROM THIS BOOK This little booklet is based on my much larger book called Im p rov e y ou r E n glish p ron u n ciation an d learn over 500 com m only m ispronounced w ords which, apart from hundreds of additional words, describes also typical error patterns in English and contains an introduction to English phonology (w hich w ill help you read English words correctly in general). -

Address Munging: the Practice of Disguising, Or Munging, an E-Mail Address to Prevent It Being Automatically Collected and Used
Address Munging: the practice of disguising, or munging, an e-mail address to prevent it being automatically collected and used as a target for people and organizations that send unsolicited bulk e-mail address. Adware: or advertising-supported software is any software package which automatically plays, displays, or downloads advertising material to a computer after the software is installed on it or while the application is being used. Some types of adware are also spyware and can be classified as privacy-invasive software. Adware is software designed to force pre-chosen ads to display on your system. Some adware is designed to be malicious and will pop up ads with such speed and frequency that they seem to be taking over everything, slowing down your system and tying up all of your system resources. When adware is coupled with spyware, it can be a frustrating ride, to say the least. Backdoor: in a computer system (or cryptosystem or algorithm) is a method of bypassing normal authentication, securing remote access to a computer, obtaining access to plaintext, and so on, while attempting to remain undetected. The backdoor may take the form of an installed program (e.g., Back Orifice), or could be a modification to an existing program or hardware device. A back door is a point of entry that circumvents normal security and can be used by a cracker to access a network or computer system. Usually back doors are created by system developers as shortcuts to speed access through security during the development stage and then are overlooked and never properly removed during final implementation. -

Paradise Lost , Book III, Line 18
_Paradise Lost_, book III, line 18 %%%%%%%%%%%%%%%%%%%%%%%% ++++++++++Hacker's Encyclopedia++++++++ ===========by Logik Bomb (FOA)======== <http://www.xmission.com/~ryder/hack.html> ---------------(1997- Revised Second Edition)-------- ##################V2.5################## %%%%%%%%%%%%%%%%%%%%%%%% "[W]atch where you go once you have entered here, and to whom you turn! Do not be misled by that wide and easy passage!" And my Guide [said] to him: "That is not your concern; it is his fate to enter every door. This has been willed where what is willed must be, and is not yours to question. Say no more." -Dante Alighieri _The Inferno_, 1321 Translated by John Ciardi Acknowledgments ---------------------------- Dedicated to all those who disseminate information, forbidden or otherwise. Also, I should note that a few of these entries are taken from "A Complete List of Hacker Slang and Other Things," Version 1C, by Casual, Bloodwing and Crusader; this doc started out as an unofficial update. However, I've updated, altered, expanded, re-written and otherwise torn apart the original document, so I'd be surprised if you could find any vestiges of the original file left. I think the list is very informative; it came out in 1990, though, which makes it somewhat outdated. I also got a lot of information from the works listed in my bibliography, (it's at the end, after all the quotes) as well as many miscellaneous back issues of such e-zines as _Cheap Truth _, _40Hex_, the _LOD/H Technical Journals_ and _Phrack Magazine_; and print magazines such as _Internet Underground_, _Macworld_, _Mondo 2000_, _Newsweek_, _2600: The Hacker Quarterly_, _U.S. News & World Report_, _Time_, and _Wired_; in addition to various people I've consulted. -
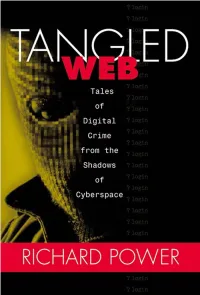
Tangled Web : Tales of Digital Crime from the Shadows of Cyberspace
TANGLED WEB Tales of Digital Crime from the Shadows of Cyberspace RICHARD POWER A Division of Macmillan USA 201 West 103rd Street, Indianapolis, Indiana 46290 Tangled Web: Tales of Digital Crime Associate Publisher from the Shadows of Cyberspace Tracy Dunkelberger Copyright 2000 by Que Corporation Acquisitions Editor All rights reserved. No part of this book shall be reproduced, stored in a Kathryn Purdum retrieval system, or transmitted by any means, electronic, mechanical, pho- Development Editor tocopying, recording, or otherwise, without written permission from the Hugh Vandivier publisher. No patent liability is assumed with respect to the use of the infor- mation contained herein. Although every precaution has been taken in the Managing Editor preparation of this book, the publisher and author assume no responsibility Thomas Hayes for errors or omissions. Nor is any liability assumed for damages resulting from the use of the information contained herein. Project Editor International Standard Book Number: 0-7897-2443-x Tonya Simpson Library of Congress Catalog Card Number: 00-106209 Copy Editor Printed in the United States of America Michael Dietsch First Printing: September 2000 Indexer 02 01 00 4 3 2 Erika Millen Trademarks Proofreader Benjamin Berg All terms mentioned in this book that are known to be trademarks or ser- vice marks have been appropriately capitalized. Que Corporation cannot Team Coordinator attest to the accuracy of this information. Use of a term in this book should Vicki Harding not be regarded as affecting the validity of any trademark or service mark. Design Manager Warning and Disclaimer Sandra Schroeder Every effort has been made to make this book as complete and as accurate Cover Designer as possible, but no warranty or fitness is implied. -

Reporting, and General Mentions Seem to Be in Decline
CYBER THREAT ANALYSIS Return to Normalcy: False Flags and the Decline of International Hacktivism By Insikt Group® CTA-2019-0821 CYBER THREAT ANALYSIS Groups with the trappings of hacktivism have recently dumped Russian and Iranian state security organization records online, although neither have proclaimed themselves to be hacktivists. In addition, hacktivism has taken a back seat in news reporting, and general mentions seem to be in decline. Insikt Group utilized the Recorded FutureⓇ Platform and reports of historical hacktivism events to analyze the shifting targets and players in the hacktivism space. The target audience of this research includes security practitioners whose enterprises may be targets for hacktivism. Executive Summary Hacktivism often brings to mind a loose collective of individuals globally that band together to achieve a common goal. However, Insikt Group research demonstrates that this is a misleading assumption; the hacktivist landscape has consistently included actors reacting to regional events, and has also involved states operating under the guise of hacktivism to achieve geopolitical goals. In the last 10 years, the number of large-scale, international hacking operations most commonly associated with hacktivism has risen astronomically, only to fall off just as dramatically after 2015 and 2016. This constitutes a return to normalcy, in which hacktivist groups are usually small sets of regional actors targeting specific organizations to protest regional events, or nation-state groups operating under the guise of hacktivism. Attack vectors used by hacktivist groups have remained largely consistent from 2010 to 2019, and tooling has assisted actors to conduct larger-scale attacks. However, company defenses have also become significantly better in the last decade, which has likely contributed to the decline in successful hacktivist operations. -

Coleman-Coding-Freedom.Pdf
Coding Freedom !" Coding Freedom THE ETHICS AND AESTHETICS OF HACKING !" E. GABRIELLA COLEMAN PRINCETON UNIVERSITY PRESS PRINCETON AND OXFORD Copyright © 2013 by Princeton University Press Creative Commons Attribution- NonCommercial- NoDerivs CC BY- NC- ND Requests for permission to modify material from this work should be sent to Permissions, Princeton University Press Published by Princeton University Press, 41 William Street, Princeton, New Jersey 08540 In the United Kingdom: Princeton University Press, 6 Oxford Street, Woodstock, Oxfordshire OX20 1TW press.princeton.edu All Rights Reserved At the time of writing of this book, the references to Internet Web sites (URLs) were accurate. Neither the author nor Princeton University Press is responsible for URLs that may have expired or changed since the manuscript was prepared. Library of Congress Cataloging-in-Publication Data Coleman, E. Gabriella, 1973– Coding freedom : the ethics and aesthetics of hacking / E. Gabriella Coleman. p. cm. Includes bibliographical references and index. ISBN 978-0-691-14460-3 (hbk. : alk. paper)—ISBN 978-0-691-14461-0 (pbk. : alk. paper) 1. Computer hackers. 2. Computer programmers. 3. Computer programming—Moral and ethical aspects. 4. Computer programming—Social aspects. 5. Intellectual freedom. I. Title. HD8039.D37C65 2012 174’.90051--dc23 2012031422 British Library Cataloging- in- Publication Data is available This book has been composed in Sabon Printed on acid- free paper. ∞ Printed in the United States of America 1 3 5 7 9 10 8 6 4 2 This book is distributed in the hope that it will be useful, but WITHOUT ANY WARRANTY; without even the implied warranty of MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE !" We must be free not because we claim freedom, but because we practice it.