Hash Pile Ups: Using Collisions to Identify Unknown Hash Functions
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

PHC: Status Quo
PHC: status quo JP Aumasson @veorq / http://aumasson.jp academic background principal cryptographer at Kudelski Security, .ch applied crypto research and outreach BLAKE, BLAKE2, SipHash, NORX Crypto Coding Standard Password Hashing Competition Open Crypto Audit Project board member do you use passwords? this talk might interest you! Oct 2013 "hash" = 3DES-ECB( static key, password ) users' hint made the guess game easy... (credit Jeremi Gosney / Stricture Group) May 2014; "encrypted passwords" (?) last week that's only the reported/published cases Lesson if Adobe, eBay, and Avast fail to protect their users' passwords, what about others? users using "weak passwords"? ITsec people using "weak defenses"? developers using "weak hashes"? cryptographers, who never bothered? agenda 1. how (not) to protect passwords 2. the Password Hashing Competition (PHC) 3. the 24-2 PHC candidates 4. next steps, and how to contribute WARNING this is NOT about bikeshed topics as: password policies password managers password-strength meters will-technology-X-replace-passwords? 1. how (not) to protect passwords solution of the 60's store "password" or the modern alternative: obviously a bad idea (assuming the server and its DB are compromised) solution of the early 70's store hash("password") "one-way": can't be efficiently inverted vulnerable to: ● efficient dictionary attacks and bruteforce ● time-memory tradeoffs (rainbow tables, etc.) solution of the late 70's store hash("password", salt) "one-way": can't be efficiently inverted immune to time-memory tradeoffs vulnerable to: ● dictionary attacks and bruteforce (but has to be repeated for different hashes) solution of the 2000's store hash("password", salt, cost) "one-way": can't be efficiently inverted immune to time-memory tradeoffs inefficient dictionary attacks and bruteforce main ideas: ● be "slow" ● especially on attackers' hardware (GPU, FPGA) => exploit fast CPU memory access/writes PBKDF2 (Kaliski, 2000) NIST and PKCS standard in Truecrypt, iOS, etc. -

SPHINCS: Practical Stateless Hash-Based Signatures
SPHINCS: practical stateless hash-based signatures Daniel J. Bernstein1;3, Daira Hopwood2, Andreas Hülsing3, Tanja Lange3, Ruben Niederhagen3, Louiza Papachristodoulou4, Peter Schwabe4, and Zooko Wilcox O'Hearn2 1 Department of Computer Science University of Illinois at Chicago Chicago, IL 606077045, USA [email protected] 2 Least Authority 3450 Emerson Ave. Boulder, CO 803056452 USA [email protected],[email protected] 3 Department of Mathematics and Computer Science Technische Universiteit Eindhoven P.O. Box 513, 5600 MB Eindhoven, The Netherlands [email protected], [email protected], [email protected] 4 Radboud University Nijmegen Digital Security Group P.O. Box 9010, 6500 GL Nijmegen, The Netherlands [email protected], [email protected] Abstract. This paper introduces a high-security post-quantum stateless hash-based sig- nature scheme that signs hundreds of messages per second on a modern 4-core 3.5GHz Intel CPU. Signatures are 41 KB, public keys are 1 KB, and private keys are 1 KB. The signature scheme is designed to provide long-term 2128 security even against attackers equipped with quantum computers. Unlike most hash-based designs, this signature scheme is stateless, allowing it to be a drop-in replacement for current signature schemes. Keywords: post-quantum cryptography, one-time signatures, few-time signatures, hyper- trees, vectorized implementation 1 Introduction It is not at all clear how to securely sign operating-system updates, web-site certicates, etc. once an attacker has constructed a large quantum computer: RSA and ECC are perceived today as being small and fast, but they are broken in polynomial time by Shor's algorithm. -

Forgery and Key Recovery Attacks for Calico
Forgery and Key Recovery Attacks for Calico Christoph Dobraunig, Maria Eichlseder, Florian Mendel, Martin Schl¨affer Institute for Applied Information Processing and Communications Graz University of Technology Inffeldgasse 16a, A-8010 Graz, Austria April 1, 2014 1 Calico v8 Calico [3] is an authenticated encryption design submitted to the CAESAR competition by Christopher Taylor. In Calico v8 in reference mode, ChaCha-14 and SipHash-2-4 work together in an Encrypt-then-MAC scheme. For this purpose, the key is split into a Cipher Key KC and a MAC Key KM . The plaintext is encrypted with ChaCha under the Cipher Key to a ciphertext with the same length as the plaintext. Then, the tag is calculated as the SipHash MAC of the concatenated ciphertext and associated data. The key used for SipHash is generated by xoring the nonce to the (lower, least significant part of the) MAC Key: (C; T ) = EncCalico(KC k KM ; N; A; P ); where k is concatenation, and with ⊕ denoting xor, the ciphertext and tag are calculated vi C = EncChaCha-14(KC ; N; P ) T = MACSipHash-2-4(KM ⊕ N; C k A): Here, A; P; C denote associated data, plaintext and ciphertext, respectively, all of arbitrary length. T is the 64-bit tag, N the 64-bit nonce, and the 384-bit key K is split into a 256-bit encryption and 128-bit authentication part, K = KC k KM . 2 Missing Domain Separation As shown above, the tag is calculated over the concatenation C k A of ciphertext and asso- ciated data. Due to the missing domain separation between ciphertext and associated data in the generation of the tag, the following attack is feasible. -

Differential Cryptanalysis of Siphash
Differential Cryptanalysis of SipHash Christoph Dobraunig, Florian Mendel, and Martin Schl¨affer IAIK, Graz University of Technology, Austria [email protected] Abstract. SipHash is an ARX based message authentication code de- veloped by Aumasson and Bernstein. SipHash was designed to be fast on short messages. Already, a lot of implementations and applications for SipHash exist, whereas the cryptanalysis of SipHash lacks behind. In this paper, we provide the first published third-party cryptanalysis of SipHash regarding differential cryptanalysis. We use existing auto- matic tools to find differential characteristics for SipHash. To improve the quality of the results, we propose several extensions for these tools to find differential characteristics. For instance, to get a good probabil- ity estimation for differential characteristics in SipHash, we generalize the concepts presented by Mouha et al. and Velichkov et al. to calcu- late the probability of ARX functions. Our results are a characteristic for SipHash-2-4 with a probability of 2−236:3 and a distinguisher for the Finalization of SipHash-2-4 with practical complexity. Even though our results do not pose any threat to the security of SipHash-2-4, they sig- nificantly improve the results of the designers and give new insights in the security of SipHash-2-4. Keywords: message authentication code, MAC, cryptanalysis, differ- ential cryptanalysis, SipHash, S-functions, cyclic S-functions 1 Introduction A message authentication code (MAC) is a cryptographic primitive, which is used to ensure the integrity and the origin of messages. Normally, a MAC takes a secret key K and a message M as input and produces a fixed size tag T .A receiver of such a message-tag-pair verifies the authenticity of the message by simply recalculating the tag T for the message and compare it with the received one. -

Lightweight Macs from Universal Hash Functions
Lightweight MACs from Universal Hash Functions S´ebastienDuval Ga¨etanLeurent November 13, 2019 REASSURE Introduction Design of MAC611 Benchmarks Conclusion 2 / 21 Authentication I Need for lightweight crypto I Relatively few authentication solutions compared to encryption I Our goal: design a fast MAC, MAC611, for 32-bit micro-controllers Introduction Design of MAC611 Benchmarks Conclusion 3 / 21 MACs Message Authentication Code I Definition: Tag t = Hk (m) I Security: bound on the proba. that an adversary forges a valid tag MAC constructions: I Block-Cipher-based (CBC-MAC, PMAC) I Hash-Function-based (HMAC) I from scratch (Pelican MAC, Chaskey) I from Universal Hash Functions (GMAC, Poly1305-AES) Lightweight MACs Chaskey, SipHash, TuLP, LightMAC, QUARK, SPONGENT Aim for 64-bit security Introduction Design of MAC611 Benchmarks Conclusion 3 / 21 MACs Message Authentication Code I Definition: Tag t = Hk (m) I Security: bound on the proba. that an adversary forges a valid tag MAC constructions: I Block-Cipher-based (CBC-MAC, PMAC) I Hash-Function-based (HMAC) I from scratch (Pelican MAC, Chaskey) I from Universal Hash Functions (GMAC, Poly1305-AES) Lightweight MACs Chaskey, SipHash, TuLP, LightMAC, QUARK, SPONGENT Aim for 64-bit security Introduction Design of MAC611 Benchmarks Conclusion 4 / 21 [Almost] Universal Hash Functions A family H : A B is: ! "-almost universal ("-AU) m = m0 A; h H : h(m) = h(m0) " H 8 6 2 jf 2 gj ≤ j j "-almost XOR universal ("-AXU) m = m0 A; d B; h H : h(m) h(m0) = d " H 8 6 2 8 2 jf 2 ⊕ gj ≤ j j H "-AXU H "-AU, -

Research Intuitions of Hashing Crypto System
Published by : International Journal of Engineering Research & Technology (IJERT) http://www.ijert.org ISSN: 2278-0181 Vol. 9 Issue 12, December-2020 Research Intuitions of Hashing Crypto System 1Rojasree. V, 2Gnana Jayanthi. J, 3Christy Sujatha. D PG & Research Department of Computer Science, Rajah Serfoji Govt. College(A), (Affiliated to Bharathidasan University), Thanjavur-613005, Tamilnadu, India. Abstract—Data transition over the internet has become there is no correlation between input and output bits; and no inevitable. Most data transmitted in the form of multimedia. correlation between output bits, etc. The data transmission must be less complex and user friendly To ensure about the originator of the message, Message at the same time with more security. Message authentication Authentication Code (MAC) is used which can be and integrity is one of the major issues in security data implemented using either symmetric Stream cipher Transmission. There are plenty of methods used to ensure the integrity of data when it is send from the receiver and before it cryptography or Hashing cryptography techniques. reaches the corresponding receiver. If these messages are However, MAC is limited with (i) Establishment of Shared tampered in the midst, it should be intimated to the receiver Secret and (ii) Inability to Provide Non-Repudiation. Even and discarded. Hash algorithms are supposed to provide the some kind of attacks is found like Content modification, integrity but almost all the algorithms have confirmed Sequence modification, Timing modification etc. breakable or less secure. In this review, the performances of This paper is aimed to discuss the several security various hash functions are studied with an analysis from the algorithms based on hash functions in cryptography to point of view of various researchers. -

Security Policy: Java Crypto Module
FIPS 140-2 Non-Proprietary Security Policy: Java Crypto Module FIPS 140-2 Non-Proprietary Security Policy Trend Micro Java Crypto Module Software Version 1.0 Document Version 1.2 August 30, 2018 Prepared For: Prepared By: Trend Micro Inc. SafeLogic Inc. 225 E. John Carpenter Freeway, Suite 1500 530 Lytton Ave, Suite 200 Irving, Texas 75062 Palo Alto, CA 94301 www.trendmicro.com www.safelogic.com Document Version 1.1 © Trend Micro Page 1 of 34 FIPS 140-2 Non-Proprietary Security Policy: Java Crypto Module Abstract This document provides a non-proprietary FIPS 140-2 Security Policy for the Trend Micro Java Crypto Module. Document Version 1.1 © Trend Micro Page 2 of 34 FIPS 140-2 Non-Proprietary Security Policy: Java Crypto Module Table of Contents 1 Introduction .............................................................................................................................................. 5 1.1 About FIPS 140 ............................................................................................................................................. 5 1.2 About this Document .................................................................................................................................... 5 1.3 External Resources ....................................................................................................................................... 5 1.4 Notices ......................................................................................................................................................... -

Two Provably Secure Password Hashing Algorithms
Pleco and Plectron – Two Provably Secure Password Hashing Algorithms Bo Zhu, Xinxin Fan, and Guang Gong Department of Electrical and Computer Engineering, University of Waterloo, Canada {bo.zhu,x5fan,ggong}@uwaterloo.ca ABSTRACT are two fundamental limitations of password-based authen- Password-based authentication has been widely deployed in tication: 1) Users routinely pick poor passwords which are practice due to its simplicity and efficiency. Storing pass- particularly subject to dictionary attacks or brute-force search; words and deriving cryptographic keys from passwords in and 2) A device or server storing a large number of passwords a secure manner are crucial for many security systems and is consistently a juicy target for attackers, and how to store services. However, choices of well-studied password hashing passwords securely and minimize damages if the device or algorithms are extremely limited, as their security require- server has been breached is non-trivial. As an effective coun- ments and design principles are different from common cryp- termeasure, all passwords should be obscured together with tographic algorithms. In this paper, we propose two practi- user-specific, random and high-entropy salts by applying a cal password hashing algorithms, Pleco and Plectron. one-way function, namely password hashing, before storing They are built upon well-understood cryptographic algo- them in the device or server. During authentication, the rithms, and combine advantages of symmetric and asymmet- user's input is processed in the same way and then the re- ric primitives. By employing the Rabin cryptosystem, we sult is compared with the one stored in the device or server. -

Analyse, Modellierung Und Hashcat-Basierte Implementierung Von Angriffen Auf Passwortgeschutzte¨ Systeme Unter Einbeziehung Des Faktors Mensch
Analyse, Modellierung und hashcat-basierte Implementierung von Angriffen auf passwortgeschutzte¨ Systeme unter Einbeziehung des Faktors Mensch Bachelorarbeit im Studiengang Medieninformatik zur Erlangung des akademischen Grades Bachelor of Science Fachbereich Medien Hochschule Dusseldorf¨ Lukas Friedrichs Matrikel-Nr.: 526560 Datum: 10. September 2018 Erst- und Zweitprufer¨ Prof. Dr.-Ing. Holger Schmidt Prof. Dr.-Ing. M.Sc. Markus Dahm Eidesstattliche Erkl¨arung Ich erkl¨are hiermit an Eides statt, dass ich die vorliegende Bachelorarbeit selbst¨andig und ohne unzul¨assige fremde Hilfe angefertigt habe. Die verwendeten Quellen sind vollst¨andig zitiert. Diese Arbeit wurde weder in gleicher noch ¨ahnlicher Form einem anderen Prufungsamt¨ vorgelegt oder ver¨offentlicht. Ich erkl¨are mich ausdrucklich¨ da- mit einverstanden, dass diese Arbeit mittels eines Dienstes zur Erkennung von Pla- giaten uberpr¨ uft¨ wird. Ort, Datum Lukas Friedrichs Kontaktinformationen Lukas Friedrichs Rottberger Straße 201 42551 Velbert | [email protected] i Zusammenfassung Analyse, Modellierung und hashcat-basierte Implementierung von Angriffen auf passwortgeschutzte¨ Systeme unter Einbeziehung des Faktors Mensch Lukas Friedrichs In der vorliegenden Bachelorarbeit geht es um das menschliche Verhalten bei der Pass- worterstellung. Hierbei wird die M¨oglichkeit untersucht dieses menschliche Verhalten uber¨ die Software hashcat nachzubilden, um so Passw¨orter effizienter anzugreifen. Durch die Konzeption und den Test von Passwortangriffsszenarien, deren Fokus auf dem Faktor Mensch liegt, wird versucht aufzuzeigen, dass selbst sichere Passwortver- fahren, durch das individuelle Verhalten von Menschen an Sicherheit verlieren k¨onnen. Zudem werden die Tests der Szenarien Schw¨achen der Software hashcat aufzeigen, die im sp¨ateren Verlauf der Arbeit als Grundlage fur¨ die Entwicklung einer selbst- programmierten Erweiterung von hashcat dienen. -

Fast Keyed Hash/Pseudo-Random Function Using SIMD Multiply and Permute
Fast keyed hash/pseudo-random function using SIMD multiply and permute J. Alakuijala, B. Cox, and J. Wassenberg Google Research February 7, 2017 Abstract HighwayHash is a new pseudo-random function based on SIMD multiply and permute instructions for thorough and fast hashing. It is 5.2 times as fast as SipHash for 1 KiB inputs. An open-source implementation is available under a permissive license. We discuss design choices and provide statistical analysis, speed measurements and preliminary cryptanalysis. Assuming it withstands further analysis, strengthened variants may also substantially accelerate file checksums and stream ciphers. 1 Introduction Hash functions are widely used for message authentication, efficient searching and `random' decisions. When attackers are able to find collisions (multiple inputs with the same hash result), they can mount denial of service attacks or disturb applications expecting uniformly distributed inputs. So-called `keyed-hash' functions prevent this by using a secret key to ensure the outputs arXiv:1612.06257v3 [cs.CR] 6 Feb 2017 are unpredictable. These functions are constructed such that an attacker who controls the inputs still cannot deduce the key, nor predict future outputs. The authors of SipHash refer to these as `strong pseudo-random functions' [1]. However, existing approaches are too slow for large-scale use. In this paper, we introduce two alternatives that are about 2 and 5 times as fast as SipHash. We are mainly interested in generating random numbers and message authentication, for which 64-bit hashes are sufficient. These are not `collision- resistant' because adversaries willing to spend considerable CPU time could 1 q π 64 find a collision after hashing about 2 2 inputs. -
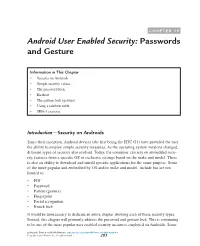
CHAPTER 19 Android User Enabled Security: Passwords and Gesture
CHAPTER 19 Android User Enabled Security: Passwords and Gesture Information in This Chapter • Security on Androids • Simple security values • The password lock • Hashcat • The pattern lock (gesture) • Using a rainbow table • SHA-1 exercise Introduction—Security on Androids Since their inception, Android devices (the first being the HTC G1) have provided the user the ability to employ simple security measures. As the operating system versions changed, different types of security also evolved. Today, the consumer can rely on embedded secu- rity features from a specific OS or exclusive settings based on the make and model. There is also an ability to download and install specific applications for the same purpose. Some of the more popular and embedded by OS and/or make and model, include but are not limited to: • PIN • Password • Pattern (gesture) • Fingerprint • Facial recognition • Knock lock It would be unnecessary to dedicate an entire chapter showing each of these security types. Instead, this chapter will primarily address the password and gesture lock. This is continuing to be one of the more popular user enabled security measures employed on Androids. Some Seeking the Truth from Mobile Evidence. http://dx.doi.org/10.1016/B978-0-12-811056-0.00019-4 Copyright © 2018 Elsevier Inc. All rights reserved. 283 284 Chapter 19 of you may be reading this and saying, “My ______ (fill in the blank) unit/machine/utility can get past that security. What do I need to know more about this process?” Yes, in the forensic utility market, many makes and models are supported for bypassing the gesture lock. -

Performance of Message Authentication Codes for Secure Ethernet
Performance of Message Authentication Codes for Secure Ethernet Philipp Hagenlocher Advisors: Dominik Scholz & Fabien Geyer Seminar Future Internet SS2018 Chair of Network Architectures and Services Departments of Informatics, Technical University of Munich Email: [email protected] ABSTRACT connection establishment in order to waste resources on the Cyclic redundancy checks within Ethernet do not provide server until a denial of service is reached. To combat this data integrity, which can be solved by using message au- attack scheme, a hash function is used to compute a hash thentication codes (MACs) within Ethernet frames. This combining the IP address of the client, port numbers and a paper gives theoretical background on hash functions and timestamp. This hash is then used as the sequence number hash-based MACs, different schemes are compared for the for the packet. This way the client is identified by this hash, usage in Ethernet frames by multiple attributes such as thus the server can free old resources if a new SYN is sent by performance, output lengths and security. The functions the client. Another important usage for hash functions are Poly1305, Skein and BLAKE2 are tested for throughput lookup tables, where hash functions are used to group val- against implementations of a SHA-2 HMAC and SipHash ues into segments that can be retrieved in faster time than and the results are discussed. Numerical measurements and a simple lookup in a set of elements. results show that Poly1305 is a suitable candidate for the usage as a per-packet MAC. 1.1 Outline This paper is structured as follows: At first it will explain Keywords the theory behind hash functions and hash-based MACs in Message Authentication Codes, Hash functions, Performance Section 2.