Android Rooting and Installing Custom Rom's
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Bootstomp: on the Security of Bootloaders in Mobile Devices
BootStomp: On the Security of Bootloaders in Mobile Devices Nilo Redini, Aravind Machiry, Dipanjan Das, Yanick Fratantonio, Antonio Bianchi, Eric Gustafson, Yan Shoshitaishvili, Christopher Kruegel, and Giovanni Vigna, UC Santa Barbara https://www.usenix.org/conference/usenixsecurity17/technical-sessions/presentation/redini This paper is included in the Proceedings of the 26th USENIX Security Symposium August 16–18, 2017 • Vancouver, BC, Canada ISBN 978-1-931971-40-9 Open access to the Proceedings of the 26th USENIX Security Symposium is sponsored by USENIX BootStomp: On the Security of Bootloaders in Mobile Devices Nilo Redini, Aravind Machiry, Dipanjan Das, Yanick Fratantonio, Antonio Bianchi, Eric Gustafson, Yan Shoshitaishvili, Christopher Kruegel, and Giovanni Vigna fnredini, machiry, dipanjan, yanick, antoniob, edg, yans, chris, [email protected] University of California, Santa Barbara Abstract by proposing simple mitigation steps that can be im- plemented by manufacturers to safeguard the bootloader Modern mobile bootloaders play an important role in and OS from all of the discovered attacks, using already- both the function and the security of the device. They deployed hardware features. help ensure the Chain of Trust (CoT), where each stage of the boot process verifies the integrity and origin of 1 Introduction the following stage before executing it. This process, in theory, should be immune even to attackers gaining With the critical importance of the integrity of today’s full control over the operating system, and should pre- mobile and embedded devices, vendors have imple- vent persistent compromise of a device’s CoT. However, mented a string of inter-dependent mechanisms aimed at not only do these bootloaders necessarily need to take removing the possibility of persistent compromise from untrusted input from an attacker in control of the OS in the device. -
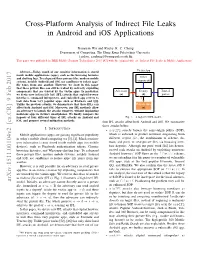
Cross-Platform Analysis of Indirect File Leaks in Android and Ios Applications
Cross-Platform Analysis of Indirect File Leaks in Android and iOS Applications Daoyuan Wu and Rocky K. C. Chang Department of Computing, The Hong Kong Polytechnic University fcsdwu, [email protected] This paper was published in IEEE Mobile Security Technologies 2015 [47] with the original title of “Indirect File Leaks in Mobile Applications”. Victim App Abstract—Today, much of our sensitive information is stored inside mobile applications (apps), such as the browsing histories and chatting logs. To safeguard these privacy files, modern mobile Other systems, notably Android and iOS, use sandboxes to isolate apps’ components file zones from one another. However, we show in this paper that these private files can still be leaked by indirectly exploiting components that are trusted by the victim apps. In particular, Adversary Deputy Trusted we devise new indirect file leak (IFL) attacks that exploit browser (a) (d) parties interfaces, command interpreters, and embedded app servers to leak data from very popular apps, such as Evernote and QQ. Unlike the previous attacks, we demonstrate that these IFLs can Private files affect both Android and iOS. Moreover, our IFL methods allow (s) an adversary to launch the attacks remotely, without implanting malicious apps in victim’s smartphones. We finally compare the impacts of four different types of IFL attacks on Android and Fig. 1. A high-level IFL model. iOS, and propose several mitigation methods. four IFL attacks affect both Android and iOS. We summarize these attacks below. I. INTRODUCTION • sopIFL attacks bypass the same-origin policy (SOP), Mobile applications (apps) are gaining significant popularity which is enforced to protect resources originating from in today’s mobile cloud computing era [3], [4]. -
UPLC™ Universal Power-Line Carrier
UPLC™ Universal Power-Line Carrier CU4I-VER02 Installation Guide AMETEK Power Instruments 4050 N.W. 121st Avenue Coral Springs, FL 33065 1–800–785–7274 www.pulsartech.com THE BRIGHT STAR IN UTILITY COMMUNICATIONS March 2006 Trademarks All terms mentioned in this book that are known to be trademarks or service marks are listed below. In addition, terms suspected of being trademarks or service marks have been appropriately capital- ized. Ametek cannot attest to the accuracy of this information. Use of a term in this book should not be regarded as affecting the validity of any trademark or service mark. This publication includes fonts and/or images from CorelDRAW which are protected by the copyright laws of the U.S., Canada and elsewhere. Used under license. IBM and PC are registered trademarks of the International Business Machines Corporation. ST is a registered trademark of AT&T Windows is a registered trademark of Microsoft Corp. Universal Power-Line Carrier Installation Guide ESD WARNING! YOU MUST BE PROPERLY GROUNDED, TO PREVENT DAMAGE FROM STATIC ELECTRICITY, BEFORE HANDLING ANY AND ALL MODULES OR EQUIPMENT FROM AMETEK. All semiconductor components used, are sensitive to and can be damaged by the discharge of static electricity. Be sure to observe all Electrostatic Discharge (ESD) precautions when handling modules or individual components. March 2006 Page i Important Change Notification This document supercedes the preliminary version of the UPLC Installation Guide. The following list shows the most recent publication date for the new information. A publication date in bold type indicates changes to that information since the previous publication. -
MINDSTORMS EV3 User Guide
User Guide TABLE OF CONTENTS Introduction + Welcome ...................................................................................................................... 3 + How to Use This Guide .................................................................................... 4 + Help ................................................................................................................................. 5 EV3 Technology + Overview ..................................................................................................................... 6 + EV3 Brick ..................................................................................................................... 7 Overview ...................................................................................................................... 7 Installing Batteries ............................................................................................... 10 Turning On the EV3 Brick ................................................................................ 11 + EV3 Motors ................................................................................................................. 12 Large Motor ............................................................................................................... 12 Medium Motor ......................................................................................................... 12 + EV3 Sensors ............................................................................................................ -

SMM Rootkits
SMM Rootkits: A New Breed of OS Independent Malware Shawn Embleton Sherri Sparks Cliff Zou University of Central Florida University of Central Florida University of Central Florida [email protected] [email protected] [email protected] ABSTRACT 1. INTRODUCTION The emergence of hardware virtualization technology has led to A rootkit consists of a set of programs that work to subvert the development of OS independent malware such as the Virtual control of an Operating System from its legitimate users [16]. If Machine based rootkits (VMBRs). In this paper, we draw one were asked to classify viruses and worms by a single defining attention to a different but related threat that exists on many characteristic, the first word to come to mind would probably be commodity systems in operation today: The System Management replication. In contrast, the single defining characteristic of a Mode based rootkit (SMBR). System Management Mode (SMM) rootkit is stealth. Viruses reproduce, but rootkits hide. They hide is a relatively obscure mode on Intel processors used for low-level by compromising the communication conduit between an hardware control. It has its own private memory space and Operating System and its users. Secondary to hiding themselves, execution environment which is generally invisible to code rootkits are generally capable of gathering and manipulating running outside (e.g., the Operating System). Furthermore, SMM information on the target machine. They may, for example, log a code is completely non-preemptible, lacks any concept of victim user’s keystrokes to obtain passwords or manipulate the privilege level, and is immune to memory protection mechanisms. -

A Comparative Analysis of Mobile Operating Systems Rina
International Journal of Computer Sciences and Engineering Open Access Research Paper Vol.-6, Issue-12, Dec 2018 E-ISSN: 2347-2693 A Comparative Analysis of mobile Operating Systems Rina Dept of IT, GGDSD College, Chandigarh ,India *Corresponding Author: [email protected] Available online at: www.ijcseonline.org Accepted: 09/Dec/2018, Published: 31/Dec/2018 Abstract: The paper is based on the review of several research studies carried out on different mobile operating systems. A mobile operating system (or mobile OS) is an operating system for phones, tablets, smart watches, or other mobile devices which acts as an interface between users and mobiles. The use of mobile devices in our life is ever increasing. Nowadays everyone is using mobile phones from a lay man to businessmen to fulfill their basic requirements of life. We cannot even imagine our life without mobile phones. Therefore, it becomes very difficult for the mobile industries to provide best features and easy to use interface to its customer. Due to rapid advancement of the technology, the mobile industry is also continuously growing. The paper attempts to give a comparative study of operating systems used in mobile phones on the basis of their features, user interface and many more factors. Keywords: Mobile Operating system, iOS, Android, Smartphone, Windows. I. INTRUDUCTION concludes research work with future use of mobile technology. Mobile operating system is the interface between user and mobile phones to communicate and it provides many more II. HISTORY features which is essential to run mobile devices. It manages all the resources to be used in an efficient way and provides The term smart phone was first described by the company a user friendly interface to the users. -

Nujj University of California, Berkeley School of Information Karen Hsu
Nujj University of California, Berkeley School of Information Karen Hsu Kesava Mallela Alana Pechon Nujj • Table of Contents Abstract 1 Introduction 2 Problem Statement 2 Objective 2 Literature Review 3 Competitive Analysis 4 Comparison matrix 4 Competition 5 Hypothesis 6 Use Case Scenarios 7 Overall System Design 10 Server-side 12 Design 12 Implementation 12 Twitter and Nujj 14 Client-side 15 Design 17 Implementation 17 Future Work 18 Extended Functionality in Future Implementations 18 Acknowledgements 19 Abstract Nujj is a location based service for mobile device users that enables users to tie electronic notes to physical locations. It is intended as an initial exploration into some of the many scenarios made possible by the rapidly increasing ubiquity of location-aware mobile devices. It should be noted that this does not limit the user to a device with a GPS embedded; location data can now also be gleaned through methods such as cell tower triangulation and WiFi IP address lookup. Within this report, both social and technical considerations associated with exposing a user’s location are discussed. The system envisioned addresses privacy concerns, as well as attempts to overcome the poor rate of adoption of current location based services already competing in the marketplace. Although several possible use cases are offered, it is the authors’ firm belief that a well-designed location- based service should not attempt to anticipate all, or even most, of the potential ways that users will find to take advantage of it. Rather, the service should be focused on building a system that is sufficiently robust yet flexible to allow users to pursue their own ideas. -
The Myth of the Superuser: Fear, Risk, and Harm Online
The Myth of the Superuser: Fear, Risk, and Harm Online ∗ Paul Ohm Fear of the powerful computer user, the “Superuser,” dominates debates about online conflict. He is a mythic figure: difficult to find, immune to technological constraints, and aware of legal loopholes. Policymakers, fearful of his power, too often overreact by passing overbroad, ambiguous laws intended to ensnare the Superuser but which are instead used against inculpable, ordinary users. This response is unwarranted because the Superuser is often a marginal figure whose power has been greatly exaggerated. The exaggerated focus on the Superuser reveals a pathological characteristic of the study of power, crime, and security online, which springs from a widely held fear of the Internet. Building on the social science fear literature, this Article challenges the conventional wisdom and ∗ Associate Professor of Law and Telecommunications, University of Colorado Law School. Thanks to Tim Wu, Orin Kerr, Phil Weiser, Julie Cohen, Pierre Schlag, Brett Frischmann, Victor Fleischer, Miranda Fleischer, Viva Moffat, and Jean Camp for their helpful comments. Thanks also for suggestions and support from participants in the University of Colorado Law School Faculty Workshop, including Clare Huntington, Nestor Davidson, Scott Peppett, Mimi Wesson, Amy Schmitz, Sarah Krakoff, and Brad Bernthal; the Intellectual Property Scholars Conference; and the Telecommunications Policy Research Conference. Thanks also to Todd Blair and Michael Beylkin for outstanding research assistance. 1327 1328 University of California, Davis [Vol. 41:1327 standard assumptions about the role of experts. Unlike dispassionate experts in other fields, computer experts are as susceptible as laypeople to exaggerate the power of the Superuser. -

Free, Functional, and Secure
Free, Functional, and Secure Dante Catalfamo What is OpenBSD? Not Linux? ● Unix-like ● Similar layout ● Similar tools ● POSIX ● NOT the same History ● Originated at AT&T, who were unable to compete in the industry (1970s) ● Given to Universities for educational purposes ● Universities improved the code under the BSD license The License The license: ● Retain the copyright notice ● No warranty ● Don’t use the author's name to promote the product History Cont’d ● After 15 years, the partnership ended ● Almost the entire OS had been rewritten ● The university released the (now mostly BSD licensed) code for free History Cont’d ● AT&T launching Unix System Labories (USL) ● Sued UC Berkeley ● Berkeley fought back, claiming the code didn’t belong to AT&T ● 2 year lawsuit ● AT&T lost, and was found guilty of violating the BSD license History Cont’d ● BSD4.4-Lite released ● The only operating system ever released incomplete ● This became the base of FreeBSD and NetBSD, and eventually OpenBSD and MacOS History Cont’d ● Theo DeRaadt ○ Originally a NetBSD developer ○ Forked NetBSD into OpenBSD after disagreement the direction of the project *fork* Innovations W^X ● Pioneered by the OpenBSD project in 3.3 in 2002, strictly enforced in 6.0 ● Memory can either be write or execute, but but both (XOR) ● Similar to PaX Linux kernel extension (developed later) AnonCVS ● First project with a public source tree featuring version control (1995) ● Now an extremely popular model of software development anonymous anonymous anonymous anonymous anonymous IPSec ● First free operating system to implement an IPSec VPN stack Privilege Separation ● First implemented in 3.2 ● Split a program into processes performing different sub-functions ● Now used in almost all privileged programs in OpenBSD like httpd, bgpd, dhcpd, syslog, sndio, etc. -
Jasperreports Server Administrator Guide
TIBCO JASPERREPORTS® SERVER ADMINISTRATOR GUIDE RELEASE 6.1 http://www.jaspersoft.com Copyright ©2005-2015, TIBCO Software Inc. All rights reserved. Printed in the U.S.A. TIBCO, the TIBCO logo, TIBCO Jaspersoft, the TIBCO Jaspersoft logo, TIBCO Jaspersoft iReport Designer, TIBCO JasperReports Library, TIBCO JasperReports Server, TIBCO Jaspersoft OLAP, TIBCO Jaspersoft Studio, and TIBCO Jaspersoft ETL are trademarks and/or registered trademarks of TIBCO Software Inc. in the United States and in jurisdictions throughout the world. All other company and product names are or may be trade names or trademarks of their respective owners. This is version 0915-JSP61-24 of the JasperReports Server Administrator Guide. TABLE OF CONTENTS Chapter 1 Overview of JasperReports Server Administration 11 1.1 Overview of Organizations 12 1.1.1 Single Default Organization 12 1.1.2 Multiple Organizations 13 1.1.3 Levels of Administrators 13 1.2 Overview of the Repository 14 1.2.1 Folder Structure 14 1.2.2 Resources 14 1.2.3 Sample Data 15 1.2.4 Browsing and Searching 16 1.3 Overview of Users and Roles 17 1.3.1 Administering Users and Roles 17 1.3.2 Delegated Administration 17 1.4 Overview of Security 18 1.5 Administrator Login 20 1.5.1 JasperReports Server Heartbeat 20 1.5.2 Administrator Email 20 1.6 Administrator Pages 21 Chapter 2 Organization, User, and Role Management 23 2.1 Managing Organizations 24 2.1.1 Viewing Organization Properties 25 2.1.2 Creating an Organization 25 2.1.3 Default Folders for Organizations 26 2.1.4 Editing an Organization 27 2.1.5 Deleting an Organization 28 2.2 Managing Users 28 2.2.1 Viewing User Properties 29 2.2.2 Creating a User 30 2.2.3 Editing a User 31 2.2.4 Enabling or Disabling Multiple Users 32 2.2.5 Deleting One or More Users 32 2.3 Managing Roles 32 TIBCO Software Inc. -

Download Rooted Apps Andrpid Download Rooted Apps Andrpid
download rooted apps andrpid Download rooted apps andrpid. Completing the CAPTCHA proves you are a human and gives you temporary access to the web property. What can I do to prevent this in the future? If you are on a personal connection, like at home, you can run an anti-virus scan on your device to make sure it is not infected with malware. If you are at an office or shared network, you can ask the network administrator to run a scan across the network looking for misconfigured or infected devices. Another way to prevent getting this page in the future is to use Privacy Pass. You may need to download version 2.0 now from the Chrome Web Store. Cloudflare Ray ID: 67da3c732955c3d9 • Your IP : 188.246.226.140 • Performance & security by Cloudflare. 10 Best Rooting Apps For Android in 2021. Rooting apps are the best way to root any android device in One Click. There are lots of rooting apps for android that are available on the internet. Rooting Android devices helps in increasing the capabilities of the device. Rooting apps are very handy for getting Root access, allow users to get superuser privileges on the Android operating system, or run actions that require system privileges and get more control over it. In other words, When you root your Android phone you can control how it works and improve its functionality. There was a time when performing root was a complicated business but today the process has smoothened a lot due to a lot of rooting apps are available with great features. -

We Hack Wii / USB Loader
Don't upgrade to Wii Firmware 4.2! Instead of updating your Wii firmware, you can just use DOP-Mii to update specific channels such as the Nintendo Channel or Wii Shop Channel without updating the Wii System Menu. This will allow you to shop with the latest Wii Shop Channel without updating the Wii System Menu. However, the guide below DOES work if you are on 4.2 and want to hack your Wii. Don't use IOS60-Patcher for launching games from SD! Instead use DOP-Mii to re-install IOS60 (if you are on Wii Firmware 4.0 or 4.1) or IOS70 (if you are on Wii Firmware 4.2) with the signature hash check (trucha bug). Also, if you are using Preloader and you "dop" IOS60 or IOS70, remember to reinstall Preloader after "doping"; otherwise, you won't be able to load the System Menu. Instead, boot HBC through Preloader to reinstall it. What is USB Loader? USB Loader is an application for the Nintendo Wii which allows you to to install and load your backup ISO game files to/from a USB storage device. It also allows you to create such backups straight from the original DVD, or you can put ISO files which you have backed up to your computer onto your USB drive and load them from there. This guide will prepare your Wii to use USB Loader GX , which will launch both the USB drive and burned DVD-R discs. What if I just want homebrew? If you don't want to launch backup games and just want to enjoy the world of homebrew, homemade games and applications for the Wii, then you only need to follow steps 2 through 4; it couldn't be simpler.