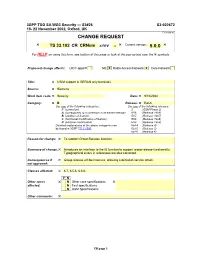
UES (cipher)
Top View
- Key-Dependent S-Box Manipulations
- Cryptanalyses of Some Multimedia Encryption Schemes
- A Design Methodology for Secured Ics Using Dynamic Current Mode Logic
- Cryptanalysis of Symmetric Cryptographic Primitives
- JAMBU Lightweight Authenticated Encryption Mode and AES-JAMBU
- Green Cryptanalysis: Meet-In-The-Middle Key-Recovery for the Full KASUMI Cipher ?
- Original Papers
- Block Ciphers
- Practical Applications of Homomorphic Encryption
- Tweakable Block Ciphers
- A Advanced Encryption Standard See AES AES 35–64 AES Process And
- Improved Impossible Differential Cryptanalysis of Large-Block Rijndael
- Cryptanalysis of Reduced-Round SIMON32 and SIMON48⋆
- JAMBU Lightweight Authenticated Encryption Mode and AES-JAMBU (V1)
- Twofish: a 128-Bit Block Cipher
- New Impossible Differential Attacks On
- Analysis of Brute-Force Attack in UES Over DES
- Improbable Differential Cryptanalysis