Public-Key Cryptanalysis
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

An Integrated Symmetric Key Cryptographic Method
I.J.Modern Education and Computer Science, 2012, 5, 1-9 Published Online June 2012 in MECS (http://www.mecs-press.org/) DOI: 10.5815/ijmecs.2012.05.01 An Integrated Symmetric Key Cryptographic Method – Amalgamation of TTJSA Algorithm , Advanced Caesar Cipher Algorithm, Bit Rotation and Reversal Method: SJA Algorithm Somdip Dey Department of Computer Science, St. Xavier’s College [Autonomous], Kolkata, India. Email: [email protected] Joyshree Nath A.K. Chaudhuri School of IT, Calcutta University, Kolkata, India. Email: [email protected] Asoke Nath Department of Computer Science, St. Xavier’s College [Autonomous], Kolkata, India. Email: [email protected] Abstract—In this paper the authors present a new In banking system the data must be fully secured. Under integrated symmetric-key cryptographic method, named no circumstances the authentic data should go to hacker. SJA, which is the combination of advanced Caesar Cipher In defense the security of data is much more prominent. method, TTJSA method, Bit wise Rotation and Reversal The leakage of data in defense system can be highly fatal method. The encryption method consists of three basic and can cause too much destruction. Due to this security steps: 1) Encryption Technique using Advanced Caesar issue different cryptographic methods are used by Cipher, 2) Encryption Technique using TTJSA Algorithm, different organizations and government institutions to and 3) Encryption Technique using Bit wise Rotation and protect their data online. But, cryptography hackers are Reversal. TTJSA Algorithm, used in this method, is again always trying to break the cryptographic methods or a combination of generalized modified Vernam Cipher retrieve keys by different means. -

Investigation of Some Cryptographic Properties of the 8X8 S-Boxes Created by Quasigroups
Computer Science Journal of Moldova, vol.28, no.3(84), 2020 Investigation of Some Cryptographic Properties of the 8x8 S-boxes Created by Quasigroups Aleksandra Mileva, Aleksandra Stojanova, Duˇsan Bikov, Yunqing Xu Abstract We investigate several cryptographic properties in 8-bit S- boxes obtained by quasigroups of order 4 and 16 with several different algebraic constructions. Additionally, we offer a new construction of N-bit S-boxes by using different number of two layers – the layer of bijectional quasigroup string transformations, and the layer of modular addition with N-bit constants. The best produced 8-bit S-boxes so far are regular and have algebraic degree 7, nonlinearity 98 (linearity 60), differential uniformity 8, and autocorrelation 88. Additionally we obtained 8-bit S-boxes with nonlinearity 100 (linearity 56), differential uniformity 10, autocorrelation 88, and minimal algebraic degree 6. Relatively small set of performed experiments compared with the extremly large set of possible experiments suggests that these results can be improved in the future. Keywords: 8-bit S-boxes, nonlinearity, differential unifor- mity, autocorrelation. MSC 2010: 20N05, 94A60. 1 Introduction The main building blocks for obtaining confusion in all modern block ciphers are so called substitution boxes, or S-boxes. Usually, they work with much less data (for example, 4 or 8 bits) than the block size, so they need to be highly nonlinear. Two of the most successful attacks against modern block ciphers are linear cryptanalysis (introduced by ©2020 by CSJM; A. Mileva, A. Stojanova, D. Bikov, Y. Xu 346 Investigation of Some Cryptographic Properties of 8x8 S-boxes . -

Security Evaluation of the K2 Stream Cipher
Security Evaluation of the K2 Stream Cipher Editors: Andrey Bogdanov, Bart Preneel, and Vincent Rijmen Contributors: Andrey Bodganov, Nicky Mouha, Gautham Sekar, Elmar Tischhauser, Deniz Toz, Kerem Varıcı, Vesselin Velichkov, and Meiqin Wang Katholieke Universiteit Leuven Department of Electrical Engineering ESAT/SCD-COSIC Interdisciplinary Institute for BroadBand Technology (IBBT) Kasteelpark Arenberg 10, bus 2446 B-3001 Leuven-Heverlee, Belgium Version 1.1 | 7 March 2011 i Security Evaluation of K2 7 March 2011 Contents 1 Executive Summary 1 2 Linear Attacks 3 2.1 Overview . 3 2.2 Linear Relations for FSR-A and FSR-B . 3 2.3 Linear Approximation of the NLF . 5 2.4 Complexity Estimation . 5 3 Algebraic Attacks 6 4 Correlation Attacks 10 4.1 Introduction . 10 4.2 Combination Generators and Linear Complexity . 10 4.3 Description of the Correlation Attack . 11 4.4 Application of the Correlation Attack to KCipher-2 . 13 4.5 Fast Correlation Attacks . 14 5 Differential Attacks 14 5.1 Properties of Components . 14 5.1.1 Substitution . 15 5.1.2 Linear Permutation . 15 5.2 Key Ideas of the Attacks . 18 5.3 Related-Key Attacks . 19 5.4 Related-IV Attacks . 20 5.5 Related Key/IV Attacks . 21 5.6 Conclusion and Remarks . 21 6 Guess-and-Determine Attacks 25 6.1 Word-Oriented Guess-and-Determine . 25 6.2 Byte-Oriented Guess-and-Determine . 27 7 Period Considerations 28 8 Statistical Properties 29 9 Distinguishing Attacks 31 9.1 Preliminaries . 31 9.2 Mod n Cryptanalysis of Weakened KCipher-2 . 32 9.2.1 Other Reduced Versions of KCipher-2 . -

Identifying Open Research Problems in Cryptography by Surveying Cryptographic Functions and Operations 1
International Journal of Grid and Distributed Computing Vol. 10, No. 11 (2017), pp.79-98 http://dx.doi.org/10.14257/ijgdc.2017.10.11.08 Identifying Open Research Problems in Cryptography by Surveying Cryptographic Functions and Operations 1 Rahul Saha1, G. Geetha2, Gulshan Kumar3 and Hye-Jim Kim4 1,3School of Computer Science and Engineering, Lovely Professional University, Punjab, India 2Division of Research and Development, Lovely Professional University, Punjab, India 4Business Administration Research Institute, Sungshin W. University, 2 Bomun-ro 34da gil, Seongbuk-gu, Seoul, Republic of Korea Abstract Cryptography has always been a core component of security domain. Different security services such as confidentiality, integrity, availability, authentication, non-repudiation and access control, are provided by a number of cryptographic algorithms including block ciphers, stream ciphers and hash functions. Though the algorithms are public and cryptographic strength depends on the usage of the keys, the ciphertext analysis using different functions and operations used in the algorithms can lead to the path of revealing a key completely or partially. It is hard to find any survey till date which identifies different operations and functions used in cryptography. In this paper, we have categorized our survey of cryptographic functions and operations in the algorithms in three categories: block ciphers, stream ciphers and cryptanalysis attacks which are executable in different parts of the algorithms. This survey will help the budding researchers in the society of crypto for identifying different operations and functions in cryptographic algorithms. Keywords: cryptography; block; stream; cipher; plaintext; ciphertext; functions; research problems 1. Introduction Cryptography [1] in the previous time was analogous to encryption where the main task was to convert the readable message to an unreadable format. -

Impossible Differential Cryptanalysis of the Lightweight Block Ciphers TEA, XTEA and HIGHT
Impossible Differential Cryptanalysis of the Lightweight Block Ciphers TEA, XTEA and HIGHT Jiazhe Chen1;2;3?, Meiqin Wang1;2;3??, and Bart Preneel2;3 1 Key Laboratory of Cryptologic Technology and Information Security, Ministry of Education, School of Mathematics, Shandong University, Jinan 250100, China 2 Department of Electrical Engineering ESAT/SCD-COSIC, Katholieke Universiteit Leuven, Kasteelpark Arenberg 10, B-3001 Heverlee, Belgium 3 Interdisciplinary Institute for BroadBand Technology (IBBT), Belgium [email protected] Abstract. TEA, XTEA and HIGHT are lightweight block ciphers with 64-bit block sizes and 128-bit keys. The round functions of the three ci- phers are based on the simple operations XOR, modular addition and shift/rotation. TEA and XTEA are Feistel ciphers with 64 rounds de- signed by Needham and Wheeler, where XTEA is a successor of TEA, which was proposed by the same authors as an enhanced version of TEA. HIGHT, which is designed by Hong et al., is a generalized Feistel cipher with 32 rounds. These block ciphers are simple and easy to implement but their diffusion is slow, which allows us to find some impossible prop- erties. This paper proposes a method to identify the impossible differentials for TEA and XTEA by using the weak diffusion, where the impossible differential comes from a bit contradiction. Our method finds a 14-round impossible differential of XTEA and a 13-round impossible differential of TEA, which result in impossible differential attacks on 23-round XTEA and 17-round TEA, respectively. These attacks significantly improve the previous impossible differential attacks on 14-round XTEA and 11-round TEA given by Moon et al. -

New Cryptanalysis of Block Ciphers with Low Algebraic Degree
New Cryptanalysis of Block Ciphers with Low Algebraic Degree Bing Sun1,LongjiangQu1,andChaoLi1,2 1 Department of Mathematics and System Science, Science College of National University of Defense Technology, Changsha, China, 410073 2 State Key Laboratory of Information Security, Graduate University of Chinese Academy of Sciences, China, 10039 happy [email protected], ljqu [email protected] Abstract. Improved interpolation attack and new integral attack are proposed in this paper, and they can be applied to block ciphers using round functions with low algebraic degree. In the new attacks, we can determine not only the degree of the polynomial, but also coefficients of some special terms. Thus instead of guessing the round keys one by one, we can get the round keys by solving some algebraic equations over finite field. The new methods are applied to PURE block cipher successfully. The improved interpolation attacks can recover the first round key of 8-round PURE in less than a second; r-round PURE with r ≤ 21 is breakable with about 3r−2 chosen plaintexts and the time complexity is 3r−2 encryptions; 22-round PURE is breakable with both data and time complexities being about 3 × 320. The new integral attacks can break PURE with rounds up to 21 with 232 encryptions and 22-round with 3 × 232 encryptions. This means that PURE with up to 22 rounds is breakable on a personal computer. Keywords: block cipher, Feistel cipher, interpolation attack, integral attack. 1 Introduction For some ciphers, the round function can be described either by a low degree polynomial or by a quotient of two low degree polynomials over finite field with characteristic 2. -
S3-020672 Group Release Function
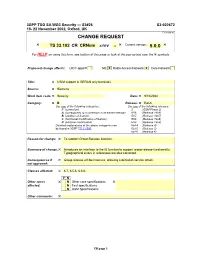
3GPP TSG SA WG3 Security — S3#26 S3-020672 19- 22 November 2002, Oxford, UK CR-Form-v7 CHANGE REQUEST ! ! Current version: ! TS 33.102 CR CRNum ! rev - 5.0.0 For HELP on using this form, see bottom of this page or look at the pop-up text over the ! symbols. Proposed change affects: UICC apps! ME X Radio Access Network X Core Network Title: ! USIM support in GERAN only terminals Source: ! Siemens Work item code: ! Security Date: ! 9/10/2002 Category: ! B Release: ! Rel-5 Use one of the following categories: Use one of the following releases: F (correction) 2 (GSM Phase 2) A (corresponds to a correction in an earlier release) R96 (Release 1996) B (addition of feature), R97 (Release 1997) C (functional modification of feature) R98 (Release 1998) D (editorial modification) R99 (Release 1999) Detailed explanations of the above categories can Rel-4 (Release 4) be found in 3GPP TR 21.900. Rel-5 (Release 5) Rel-6 (Release 6) Reason for change: ! To support Group Release function. Summary of change: ! Introduces an interface to the f8 function to support group release functionality. Typographical errors in references are also corrected. Consequences if ! Group release will be insecure, allowing a denial-of-service attack. not approved: Clauses affected: ! 6.7, 6.5.6, 6.6.6. Y N Other specs ! N Other core specifications ! affected: N Test specifications N O&M Specifications Other comments: ! CR page 1 3GPP TS aa.bbb vX.Y.Z (YYYY-MM) CR page 2 6.5.6 UIA identification Each UMTS Integrity Algorithm (UIA) will be assigned a 4-bit identifier. -
Cryptanalysis of Symmetric Encryption Algorithms Colin Chaigneau
Cryptanalysis of symmetric encryption algorithms Colin Chaigneau To cite this version: Colin Chaigneau. Cryptanalysis of symmetric encryption algorithms. Cryptography and Security [cs.CR]. Université Paris-Saclay, 2018. English. NNT : 2018SACLV086. tel-02012149 HAL Id: tel-02012149 https://tel.archives-ouvertes.fr/tel-02012149 Submitted on 8 Feb 2019 HAL is a multi-disciplinary open access L’archive ouverte pluridisciplinaire HAL, est archive for the deposit and dissemination of sci- destinée au dépôt et à la diffusion de documents entific research documents, whether they are pub- scientifiques de niveau recherche, publiés ou non, lished or not. The documents may come from émanant des établissements d’enseignement et de teaching and research institutions in France or recherche français ou étrangers, des laboratoires abroad, or from public or private research centers. publics ou privés. Cryptanalyse des algorithmes de chiffrement symetrique´ These` de doctorat de l’Universite´ Paris-Saclay prepar´ ee´ a` l’Universite´ de Versailles Saint-Quentin-en-Yvelines NNT : 2018SACLV086 Ecole doctorale n◦580 Sciences et Technologies de l’Information et de la Communication (STIC) Specialit´ e´ de doctorat : Mathematiques` et Informatique These` present´ ee´ et soutenue a` Versailles, le mercredi 28 novembre 2018, par Colin Chaigneau Composition du Jury : M. Louis GOUBIN Professeur, Universite´ de Versailles President´ Saint-Quentin-en-Yvelines, France M. Thierry BERGER Professeur Em´ erite,´ Universite´ de Limoges, France Rapporteur Mme. Mar´ıa NAYA-PLASENCIA Directrice de Recherche, INRIA Paris, France Rapporteure M. Patrick DERBEZ Maˆıtre de Conference,´ Universite´ de Rennes 1, France Examinateur Mme. Marine MINIER Professeure, Universite´ de Lorraine, France Examinatrice M. Gilles VAN ASSCHE Senior Principal Cryptographer, STMicroelectronics, Examinateur Belgique M. -

UES Application Report
UES Application Report https://apps.fas.usda.gov/ues/WebApp/Application/ApplicationReport United States Department of Agriculture Unified Export Strategy Home UES Financial Reports In Reports Out Tools About FAS Help You are here : Home > UES > Application > Application Report Welcome naega1!, PART - [Author][Cashier][Contributor] [ Log Off ] UES Application Report The entire UES Application for the chosen year is displayed here. Scroll to see the entire report or to navigate to a specific section, you can click directly on the Table of Contents sections. 2017 Unified Export Strategy Application Participant: North American Export Grain Association (NAEGA) Table of Contents 1.SECTION 1: PROFILE, INDUSTRY EXPORT GOAL, AND CONTRIBUTIONS 1.1 Applicant Profile 1.1.1 Participant Profile 1.1.2 Office 1.1.3 Contact 1.1.4 Industry 1.1.5 Industry Personnel 1.1.6 MAP/FMD Start/End Dates from Plan Submittal 1.1.7 Resource Request Table 1.2 Industry Export Goals 1.3 Promised Contributions 1.4 Proposals 2.SECTION 2: MARKET ANALYSIS, ASSESSMENT, AND STRATEGY 2.1 Market Definitions 2.2 Promoted Commodities 2.3 Targeted Market Assessment 3.SECTION 3: FOREIGN OFFICES AND ADMINISTRATIVE COSTS 3.1 Administrative Budget (Admin Activity) Summary For MAP, FMD Section 108 And TASC 3.2 Worldwide US Personnel Cost Summary: FMD 3.3 Worldwide Contingent Liabilities Summary: FMD 1 of 61 6/3/2016 11:33 AM UES Application Report https://apps.fas.usda.gov/ues/WebApp/Application/ApplicationReport 1.SECTION 1: PROFILE, INDUSTRY EXPORT GOAL, AND CONTRIBUTIONS 1.1 Applicant Profile 1.1.1 Participant Profile Description: The North American Export Grain Association, Inc. -

Cryptanalysis of Full Sprout ∗
Cryptanalysis of Full Sprout ∗ Virginie Lallemand and Mar´ıaNaya-Plasencia Inria, France Abstract. A new method for reducing the internal state size of stream cipher registers has been proposed in FSE 2015, allowing to reduce the area in hardware implementations. Along with it, an instantiated pro- posal of a cipher was also proposed: Sprout. In this paper, we analyze the security of Sprout, and we propose an attack that recovers the whole key more than 210 times faster than exhaustive search and has very low data complexity. The attack can be seen as a divide-and-conquer evolved technique, that exploits the non-linear influence of the key bits on the update function. We have implemented the attack on a toy version of Sprout, that conserves the main properties exploited in the attack. The attack completely matches the expected complexities predicted by our theoretical cryptanalysis, which proves its validity. We believe that our attack shows that a more careful analysis should be done in order to instantiate the proposed design method. Keywords: Stream cipher, Cryptanalysis, Lightweight, Sprout. 1 Introduction The need of low-cost cryptosystems for several emerging applications like RFID tags and sensor networks has drawn considerable attention to the area of lightweight primitives over the last years. Indeed, those new applications have very limited resources and necessitate specific algorithms that ensure a perfect balance be- tween security, power consumption, area size and memory needed. The strong demand from the community (for instance, [5]) and from the industry has led to the design of an enormous amount of promising such primitives, with differ- ent implementation features. -

Rockpoint Acquires UES Highrise for $218M with Wells Fargo Loan
The Insider’s Weekly Guide to the Commercial Mortgage Industry In This Issue 1 Rockpoint Acquires UES Highrise for $218M With Wells Fargo Loan 1 Bank of America Finances Ten Almaden Buy in Deal Brokered by HFF 3 U.S. CMBS Delinquency Declines Further After Hitting Five-Year Low 3 NYCB Recapitalizes 216 East 45th Street 3 Deutsche Bank Finances Related High Line Acquisition 5 Greystone Further Expands Freddie Mac Loan Offering. 5 Hotel REIT Takes $150M Unsecured Term Loan Facility “Dodd-Frank greatly concerns me. We had historic changes to banking rules after 2008.” —Ed Lombardo From Q&A on page 7 Rockpoint Acquires UES Highrise for $218M With Bank of America Finances Ten Almaden Wells Fargo Loan Buy in Deal Brokered by HFF Rockpoint Group acquired The Wim- The 205,261-square-foot property, built a HFF secured $76.6 million in acquisi- bledon, a 28-story apartment high-rise on few blocks from Central Park in 1980, con- tion financing on behalf of KBS Capital the Upper East Side, for $218 million, or tains 223 apartment units and 6,200 square Advisors for its $116.7 million purchase $977,578 per unit, with a $115 million loan feet of ground-floor retail space occupied of a 309,255-square-foot office building in from Wells Fargo, city records show. by a Citibank branch. downtown San Jose, Calif. The Boston-based real estate investment J.P. Morgan’s asset management arm The three-year, floating-rate loan from firm purchased the luxury rental building bought The Wimbledon from New York- Bank of America was provided to KBS at 200 East 82nd Street from J.P. -

An Examination of the Seed Rain and Seed Bank and Evidence of Seed Exchange Between a Beech Gap and a Spruce Forest in the Great Smoky Mountains
University of Tennessee, Knoxville TRACE: Tennessee Research and Creative Exchange Masters Theses Graduate School 8-1981 An Examination of the Seed Rain and Seed Bank and Evidence of Seed Exchange Between a Beech Gap and a Spruce Forest in the Great Smoky Mountains Noel Bruce Pavlovic University of Tennessee - Knoxville Follow this and additional works at: https://trace.tennessee.edu/utk_gradthes Part of the Life Sciences Commons Recommended Citation Pavlovic, Noel Bruce, "An Examination of the Seed Rain and Seed Bank and Evidence of Seed Exchange Between a Beech Gap and a Spruce Forest in the Great Smoky Mountains. " Master's Thesis, University of Tennessee, 1981. https://trace.tennessee.edu/utk_gradthes/1433 This Thesis is brought to you for free and open access by the Graduate School at TRACE: Tennessee Research and Creative Exchange. It has been accepted for inclusion in Masters Theses by an authorized administrator of TRACE: Tennessee Research and Creative Exchange. For more information, please contact [email protected]. To the Graduate Council: I am submitting herewith a thesis written by Noel Bruce Pavlovic entitled "An Examination of the Seed Rain and Seed Bank and Evidence of Seed Exchange Between a Beech Gap and a Spruce Forest in the Great Smoky Mountains." I have examined the final electronic copy of this thesis for form and content and recommend that it be accepted in partial fulfillment of the requirements for the degree of Master of Science, with a major in Ecology and Evolutionary Biology. E. E. C. Clebsch, Major Professor We have read this thesis and recommend its acceptance: H.