Malware Analysis (CS6038) Week 08.1 Static Analyzers
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Hostscan 4.8.01064 Antimalware and Firewall Support Charts
HostScan 4.8.01064 Antimalware and Firewall Support Charts 10/1/19 © 2019 Cisco and/or its affiliates. All rights reserved. This document is Cisco public. Page 1 of 76 Contents HostScan Version 4.8.01064 Antimalware and Firewall Support Charts ............................................................................... 3 Antimalware and Firewall Attributes Supported by HostScan .................................................................................................. 3 OPSWAT Version Information ................................................................................................................................................. 5 Cisco AnyConnect HostScan Antimalware Compliance Module v4.3.890.0 for Windows .................................................. 5 Cisco AnyConnect HostScan Firewall Compliance Module v4.3.890.0 for Windows ........................................................ 44 Cisco AnyConnect HostScan Antimalware Compliance Module v4.3.824.0 for macos .................................................... 65 Cisco AnyConnect HostScan Firewall Compliance Module v4.3.824.0 for macOS ........................................................... 71 Cisco AnyConnect HostScan Antimalware Compliance Module v4.3.730.0 for Linux ...................................................... 73 Cisco AnyConnect HostScan Firewall Compliance Module v4.3.730.0 for Linux .............................................................. 76 ©201 9 Cisco and/or its affiliates. All rights reserved. This document is Cisco Public. -

Virusscan Enterprise 7.1.0 Installation Guide
Installation Guide Revision 1.0 VirusScan® Enterprise version 7.1.0 COPYRIGHT © 2003 Networks Associates Technology, Inc. All Rights Reserved. No part of this publication may be reproduced, transmitted, transcribed, stored in a retrieval system, or translated into any language in any form or by any means without the written permission of Networks Associates Technology, Inc., or its suppliers or affiliate companies. To obtain this permission, write to the attention of the Network Associates legal department at: 5000 Headquarters Drive, Plano, Texas 75024, or call +1-972-963-8000. TRADEMARK ATTRIBUTIONS Active Firewall, Active Security, Active Security (in Katakana), ActiveHelp, ActiveShield, AntiVirus Anyware and design, Appera, AVERT, Bomb Shelter, Certified Network Expert, Clean-Up, CleanUp Wizard, ClickNet, CNX, CNX Certification Certified Network Expert and design, Covert, Design (stylized N), Disk Minder, Distributed Sniffer System, Distributed Sniffer System (in Katakana), Dr Solomon’s, Dr Solomon’s label, E and Design, Entercept, Enterprise SecureCast, Enterprise SecureCast (in Katakana), ePolicy Orchestrator, Event Orchestrator (in Katakana), EZ SetUp, First Aid, ForceField, GMT, GroupShield, GroupShield (in Katakana), Guard Dog, HelpDesk, HelpDesk IQ, HomeGuard, Hunter, Impermia, InfiniStream, Intrusion Prevention Through Innovation, IntruShield, IntruVert Networks, LANGuru, LANGuru (in Katakana), M and design, Magic Solutions, Magic Solutions (in Katakana), Magic University, MagicSpy, MagicTree, McAfee, McAfee (in Katakana), -

Sécurité Et Antivirus Sur Mac
Sécurité et antivirus sur Mac Sécurité et antivirus sur Mac ............................................................................................................. 1 Sécurité : le discours officiel et les faits ......................................................................................... 3 Sécurité : les types de menace en activité ..................................................................................... 4 Les failles de sécurité ......................................................................................................................................... 4 Trojans ................................................................................................................................................................. 4 Phishing, vol d'identité ..................................................................................................................................... 5 Les mécanismes de défense standard ............................................................................................ 6 Quelles défenses contre des logiciels malveillants ? ................................................................. 7 Le chiffrement de données sous Mac OS X .................................................................................... 8 Antivirus sur Mac : est-ce bien nécessaire ? ................................................................................. 9 Les suites de sécurité sur Mac ....................................................................................................... -
Linux Security Review 2015
Linux Security Review 2015 www.av-comparatives.org AV-Comparatives Linux Security Review Language: English May 2015 Last revision: 26 th May 2015 www.av-comparatives.org -1- Linux Security Review 2015 www.av-comparatives.org Contents Introduction ....................................................................................................................... 3 Reviewed products ............................................................................................................... 4 Malware for Linux systems ..................................................................................................... 5 Linux security advice ............................................................................................................ 6 Items covered in the review .................................................................................................. 7 Avast File Server Security ...................................................................................................... 8 AVG Free Edition for Linux.................................................................................................... 11 Bitdefender Antivirus Scanner for Unices ................................................................................ 13 Clam Antivirus for Linux ....................................................................................................... 17 Comodo Antivirus for Linux .................................................................................................. 20 Dr.Web Anti-virus for -

Mcafee Virusscan Enterprise Protect Your Desktops and File Servers from Malicious Threats
DATA SHEET McAfee VirusScan Enterprise Protect your desktops and file servers from malicious threats Keeping networks free from a wide range of threats—viruses, worms, rootkits, and Trojans— Key Advantages is more challenging than ever. Whether your organization is a global enterprise with full-time security staff or a small or medium-size business, McAfee® VirusScan® Enterprise software Unbeatable malware detection and removal ensures that your endpoint servers, desktops, and laptops remain free from malware. Protect your files from viruses, worms, rootkits, Trojans, and other threats. McAfee VirusScan Enterprise software combines techniques. With port blocking, file-name blocking, antivirus, antispyware, firewall, and intrusion prevention folder/directory lockdown, file share lockdown, and Proactive protection from zero- technologies to proactively detect and remove malware. infection trace and block, you can stop many new and day attacks Proactive protection against new It reduces the cost of managing outbreak responses, unknown malware files cold. and unknown buffer-overflow stops zero-day threats, and mitigates the window of Proactive Protection from Attacks exploits that target vulnerabilities in vulnerability—the time between the discovery of a Microsoft applications vulnerability and when fixes are deployed. Plus, with McAfee VirusScan Enterprise software is the industry’s first anti-malware software to offer patented intrusion Leverage McAfee GTI McAfee VirusScan Enterprise software, you have The worldwide presence of McAfee prevention with application-specific buffer-overflow the flexibility to detect and block malware based on Labs enables McAfee VirusScan your business needs: on access, on demand, or on a technology. Now, you can protect your users Enterprise software to leverage schedule. -

Actively Tested
Actively Tested (Immediately as significant updates and samples are available) (80% or higher detection rate) Regularly Tested (Occasionally if many new samples or significant updates are available) (60 - 80% detection rate) Tested when the mood strikes (60% or lower detection rates) For Comparison, not Excluded from future testing (read notes below) an actual Antivirus Malware Family (by year) # Malware Sample Type MD5 Hash Avast 7.0 (38501 - 39902) Sophos 8.0.14C - 9.0.3 Intego VirusBarrier 2013 10.7.3 Avira 1.0.0.64 VirusBarrier Express 1.1.6 (79) ESET 5.0.110.0 Kaspersky Security 13 - 14.0.0.177 Dr Web 6.0.3 (201204200) F-Secure 0.1.11361 Panda Antivirus 1.4 (72) - 1.5 (74) Comodo MacKeeper 2.5.1 (304) - 261 iAntivirus 1.1.4 (282) ProtectMac 1.3.2 - 1.3.4 Norton 12.5 (59) ClamXav 2.3.6 - 2.5 (293) Bitdefender (App Store) 2.21 BitDefender 2.30 - 3.0.6681 eScan 5.5-7 McAfee Endpoint Protection for McAfee Internet Security for Mac McAfee Security 1.2.0 (1549) Trend Micro Titanium 2.0.1279 Webroot 8.0.3.182 : 104 Dr Web Light 6.0.6 (201207050) FortiClient 5.0.4.116 MacScan 2.9.4 File Quarantine / XProtect Norton 11.1.1 (2) Trend Micro Smart Sur. 1.6.1101 Intego VirusBarrier X6 10.6.17 McAfee VirusScan for Mac 8.6.1 Quick Heal Total Sec 1.0 McAfee Virex 7.7 (163) Magician 1.4.3 Vipre 1.0.51 Mac Malware Remover 1.1.6 Mac Free Free $29.99 Free Free (App Store) $39.99 $39.95 €26 €29,99 $49.99 Free $89.95 Free $44.99 $49.99 Free Free $49.95 $29.95 $153 for 3 Macs (Business) $79.99 (Consumer) $109.65 for 3 Macs (Business) $29.95 (possible discount) -
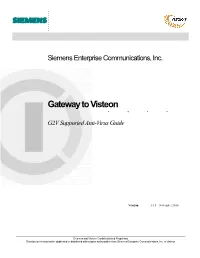
Gateway to Visteon G2V Supported Anti-Virus Guide
. Siemens Enterprise Communications, Inc. ........Gateway to Visteon G2V Supported Anti-Virus Guide Version: 1.6.5 – November 2010 Siemens and Visteon Confidential and Proprietary This document may not be duplicated or distributed without prior authorization from Siemens Enterprise Communications, Inc. or Visteon . Supported Anti-Virus Software The following Anti-Virus applications are fully supported. It is highly recommended that one of the following applications be used for accessing G2V. Please note that this list will change as new versions are released by their vendors. Normally, the current and previous release of these applications will remain on the supported list. Newer versions released may not be immediately supported or compatible, please consult this list before updating to a newer version. Vendor Product Version Windows XP Windows Vista Windows 7 McAfee, Inc. VirusScan Enterprise 8.7.x ✔ ✔ ✔ VirusScan 2009 13.x ✔ ✔ ‐‐ VirusScan 2010 14.x ✔ ✔ ✔ Symantec Corp. Norton Anti-Virus 2010 17.x ✔ ✔ ‐‐ Norton Anti-Virus 2011 18.x ✔ ✔ ✔ Symantec Endpoint Protection 11.x ✔ ✔ ✔ Symantec Endpoint Protection 12.x ✔ ✔ ✔ Trend Micro, Inc. Anti‐Virus 17.x ✔ ✔ ‐‐ Anti‐Virus 17.5 ✔ ✔ ✔ OfficeScan 8.x ✔ ✔ ‐‐ OfficeScan 10.x ✔ ✔ ✔ Notes: Please see the notes at the end of this guide for special instructions for Vista users with Norton Anti-Virus 2009. The products highlighted in yellow will be removed from the supported list in the next update. If you are using one of these products, you should consider upgrading to a newer version. Compatible Anti-Virus Software The applications below have been specified as compatible by the Anti-Virus Host Check vendor. Support for these applications may be removed at any time, especially in the case of older versions that may be at or near end-of-life status. -

Cisco Identity Services Engine Release 1.2 Supported Windows
Cisco Identity Services Engine Supported Windows AV/AS Products Compliance Module Version 3.5.6317.2 This document provides Windows 8/7/Vista/XP AV/AS support information on the Cisco NAC Agent version 4.9.0.x and later. For other support information and complete release updates, refer to the Release Notes for Cisco Identity Services Engine corresponding to your Cisco Identity Services Engine release version. Supported Windows AV/AS Product Summary Added New AV Definition Support: COMODO Antivirus 5.x COMODO Internet Security 3.5.x COMODO Internet Security 3.x COMODO Internet Security 4.x Kingsoft Internet Security 2013.x Added New AV Products Support: V3 Click 1.x avast! Internet Security 8.x avast! Premier 8.x avast! Pro Antivirus 8.x Gen-X Total Security 1.x K7UltimateSecurity 13.x Kaspersky Endpoint Security 10.x Kaspersky PURE 13.x Norman Security Suite 10.x Supported Windows AntiVirus Products Product Name Product Version Installation Virus Definition Live Update 360Safe.com 360 Antivirus 1.x 4.9.0.28 / 3.4.21.1 4.9.0.28 / 3.4.21.1 yes 360 Antivirus 3.x 4.9.0.29 / 3.5.5767.2 4.9.0.29 / 3.5.5767.2 - 360杀毒 1.x 4.9.0.28 / 3.4.21.1 4.9.0.28 / 3.4.21.1 - 360杀毒 2.x 4.9.0.29 / 3.4.25.1 4.9.0.29 / 3.4.25.1 - 360杀毒 3.x 4.9.0.29 / 3.5.2101.2 - Other 360Safe.com Antivirus x 4.9.0.29 / 3.5.2101.2 - AEC, spol. -

Virusscan Enterprise 7.0 Installation Guide
Installation Guide Revision 1.0 VirusScan® Enterprise version 8.0i COPYRIGHT Copyright © 2004 Networks Associates Technology, Inc. All Rights Reserved. No part of this publication may be reproduced, transmitted, transcribed, stored in a retrieval system, or translated into any language in any form or by any means without the written permission of Networks Associates Technology, Inc., or its suppliers or affiliate companies. To obtain this permission, write to the attention of the Network Associates legal department at: 5000 Headquarters Drive, Plano, Texas 75024, or call +1-972-963-8000. TRADEMARK ATTRIBUTIONS Active Firewall, Active Security, ActiveSecurity (in Katakana), ActiveHelp, ActiveShield, AntiVirus Anyware and design, Bomb Shelter, Certified Network Expert, Clean-Up, CleanUp Wizard, ClickNet, CNX, CNX Certification Certified Network Expert and design, Covert, Design (Stylized E), Design (Stylized N), Disk Minder, Distributed Sniffer System, Distributed Sniffer System (in Katakana), Dr Solomon’s, Dr Solomon’s label, Entercept, Enterprise SecureCast, Enterprise SecureCast (in Katakana), ePolicy Orchestrator, EZ SetUp, First Aid, ForceField, GMT, GroupShield, GroupShield (in Katakana), Guard Dog, HomeGuard, Hunter, IntruShield, Intrusion Prevention Through Innovation, IntruVert Networks, LANGuru, LANGuru (in Katakana), M and Design, McAfee, McAfee (in Katakana), McAfee and design, McAfee.com, McAfee VirusScan, NA Network Associates, Net Tools, Net Tools (in Katakana), NetCrypto, NetOctopus, NetScan, NetShield, NetStalker, Network -

Linuxshield™ Version 1.5
Product Guide LinuxShield™ version 1.5 McAfee® System Protection Industry-leading intrusion prevention solutions COPYRIGHT Copyright © 2007 McAfee, Inc. All Rights Reserved. No part of this publication may be reproduced, transmitted, transcribed, stored in a retrieval system, or translated into any language in any form or by any means without the written permission of McAfee, Inc., or its suppliers or affiliate companies. TRADEMARK ATTRIBUTIONS ACTIVE FIREWALL, ACTIVE SECURITY, ACTIVESECURITY (AND IN KATAKANA), ACTIVESHIELD, CLEAN-UP, DESIGN (STYLIZED E), DESIGN (STYLIZED N), ENTERCEPT, EPOLICY ORCHESTRATOR, FIRST AID, FOUNDSTONE, GROUPSHIELD, GROUPSHIELD (AND IN KATAKANA), INTRUSHIELD, INTRUSION PREVENTION THROUGH INNOVATION, MCAFEE, MCAFEE (AND IN KATAKANA), MCAFEE AND DESIGN, MCAFEE.COM, MCAFEE VIRUSSCAN, NET TOOLS, NET TOOLS (AND IN KATAKANA), NETSCAN, NETSHIELD, NUTS & BOLTS, OIL CHANGE, PRIMESUPPORT, SPAMKILLER, THREATSCAN, TOTAL VIRUS DEFENSE, VIREX, VIRUS FORUM, VIRUSCAN, VIRUSSCAN, VIRUSSCAN (AND IN KATAKANA), WEBSCAN, WEBSHIELD, WEBSHIELD (AND IN KATAKANA) are registered trademarks or trademarks of McAfee, Inc. and/or its affiliates in the US and/or other countries. The color red in connection with security is distinctive of McAfee brand products. All other registered and unregistered trademarks herein are the sole property of their respective owners. LICENSE INFORMATION License Agreement NOTICE TO ALL USERS: CAREFULLY READ THE APPROPRIATE LEGAL AGREEMENT CORRESPONDING TO THE LICENSE YOU PURCHASED, WHICH SETS FORTH THE GENERAL TERMS AND CONDITIONS FOR THE USE OF THE LICENSED SOFTWARE. IF YOU DO NOT KNOW WHICH TYPE OF LICENSE YOU HAVE ACQUIRED, PLEASE CONSULT THE SALES AND OTHER RELATED LICENSE GRANT OR PURCHASE ORDER DOCUMENTS THAT ACCOMPANIES YOUR SOFTWARE PACKAGING OR THAT YOU HAVE RECEIVED SEPARATELY AS PART OF THE PURCHASE (AS A BOOKLET, A FILE ON THE PRODUCT CD, OR A FILE AVAILABLE ON THE WEB SITE FROM WHICH YOU DOWNLOADED THE SOFTWARE PACKAGE). -
Security Alert Tipsheet.Qx
Peachpit Essential books for the creative community TechTV's Top Cyber-crime Survival Tips The Internet can be a dangerous place if you leave yourself open to attack from nefarious cyber-thieves and crippling viruses. TechTV personality Becky Worley tells the true tales of victims who have fought back against these online predators and TechTV's Security Alert: Stories of Real People Protecting Themselves from offers practical self-defense techniques in her new book, TechTV's Security Alert: Identity Theft, Viruses, and Scams Stories of Real People Protecting Themselves from Identity Theft, Viruses, and by Becky Worley Scams. Nervous? Don't be. We've compiled some of the book's most helpful tips right here in this handy survival guide. Identity Theft, Who Owns Me Now? Order Your Credit Report The three major credit bureaus in the United States are Equifax, Secure Your Social Security Card Experian, and TransUnion. These companies do not share informa- Put your Social Security card somewhere safe. Take it out of your tion with one another, so you should order a report from all three wallet! Finding a Social Security card or number in a stolen purse or use a service, such as TrueCredit.com (www.truecredit.com), to or wallet is a jackpot for ID thieves. get a unified report. Lock Down Personal Data at Home • Equifax Credit Information Services, Inc. Secure your personal data in your own home. Use a locked firebox Call 800-525-6285 / TDD 800-255-0056 and ask the and keep it someplace a little more obscure, or just choose a more operator to call the Auto Disclosure line at 800-685-1111 out-of-the way spot for your really key personal data. -

Securview 6-0-6 Antivirus Software Installation
® SecurView 6-0-6 Antivirus Software Installation 1. Introduction Antivirus software is an effective way to combat computer viruses, trojans, worms, and other malicious software that may attempt to compromise the integrity of a system. It is essential that antivirus software is installed and configured correctly and kept up to date for it to be an effective tool. Hologic has tested SecurView with the antivirus products in the reference list for the benefit of our customers. 1.1. Purpose To install antivirus software on SecurView Workstation 6-0-6 products. 1.2. Scope This document applies to all SecurView products with version 6-0-6 software. 1.3. Estimated Time Installation of antivirus products takes the network technician approximately 30 minutes to complete, including configuration. 1.4. Reference List This document provides instructions for the following products. • Symantec AntiVirus Corporate Edition version 10.x • Symantec Endpoint Protection Client 11.x • Symantec Endpoint Protection Small Business Edition (V12) • McAfee VirusScan Enterprise version 8.5.0i • McAfee VirusScan Enterprise version 8.7i • Microsoft Forefront Client Security version 1.x • Sophos Endpoint Security and Control 9 • Trend Micro OfficeScan 10.5 m Note: These products must be provided by the customer. Load only the client software. 1.5. Definitions • LiveUpdate – A feature that allows servers and clients to retrieve updates from an internal server or Symantec’s official LiveUpdate server. • Managed – The client system is configured to send virus alerts, as well as retrieve virus updates from an internal parent Symantec server. • Real-Time – Real-time scanning of each file that is loaded in RAM.