Key Generation for Internet of Things: a Contemporary Survey
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Public-Key Cryptography
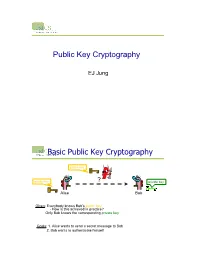
Public Key Cryptography EJ Jung Basic Public Key Cryptography public key public key ? private key Alice Bob Given: Everybody knows Bob’s public key - How is this achieved in practice? Only Bob knows the corresponding private key Goals: 1. Alice wants to send a secret message to Bob 2. Bob wants to authenticate himself Requirements for Public-Key Crypto ! Key generation: computationally easy to generate a pair (public key PK, private key SK) • Computationally infeasible to determine private key PK given only public key PK ! Encryption: given plaintext M and public key PK, easy to compute ciphertext C=EPK(M) ! Decryption: given ciphertext C=EPK(M) and private key SK, easy to compute plaintext M • Infeasible to compute M from C without SK • Decrypt(SK,Encrypt(PK,M))=M Requirements for Public-Key Cryptography 1. Computationally easy for a party B to generate a pair (public key KUb, private key KRb) 2. Easy for sender to generate ciphertext: C = EKUb (M ) 3. Easy for the receiver to decrypt ciphertect using private key: M = DKRb (C) = DKRb[EKUb (M )] Henric Johnson 4 Requirements for Public-Key Cryptography 4. Computationally infeasible to determine private key (KRb) knowing public key (KUb) 5. Computationally infeasible to recover message M, knowing KUb and ciphertext C 6. Either of the two keys can be used for encryption, with the other used for decryption: M = DKRb[EKUb (M )] = DKUb[EKRb (M )] Henric Johnson 5 Public-Key Cryptographic Algorithms ! RSA and Diffie-Hellman ! RSA - Ron Rives, Adi Shamir and Len Adleman at MIT, in 1977. • RSA -

Meet the Samsung Galaxy On5
Meet the Samsung Galaxy On5. Packed with essentials, the Galaxy On5 has what you need to do what you want. Screen Whether you’re scrolling through photos or connecting with friends and family, you’ll get a bright, full picture on the 5.0" HD display. Expandable Memory With 8GB¹ of built-in memory, you can store more than 5,000 photos or 2,500 songs² directly on your device. Get up to an additional 128GB of memory with a microSD card³ so you can enjoy more of your favorite music, photos and games on the go. Easy Mode Simplify your experience when you turn on Easy Mode. Featuring fewer, larger icons and simpler app interactions, Easy Mode lets you get to your favorites quickly. Technical specifi cations Display 5.0" HD 720 x 1280 Processor Exynos 3475 1.3 GHz Quad-Core OS Android™ 6.0, Marshmallow Connectivity Wi-Fi: 802.11 b/g/n 2.4 GHz Bluetooth v4.1 Camera 5MP main 2MP front-facing Memory 1.5GB RAM 8GB ROM¹ Expandable up to 128GB³ Battery 2,600 mAh Dimensions 5.64" x 2.83" x 0.33" Weight 5.26 oz HAC value M3/T3 Battery talk time⁴ Up to 16 hours Battery standby time⁴ Up to 19 days ¹Portion of memory occupied by existing content. ²Based on 1MB per picture or 2MB per song. ³Memory card sold separately. ⁴Based on laboratory testing. Results may vary. Battery power consumption depends on factors such as network configuration, carrier network, signal strength, operating temperature, features selected, vibrate mode, backlight settings, browser use, frequency of calls, and voice, data and other application-usage patterns. -

A Password-Based Key Derivation Algorithm Using the KBRP Method
American Journal of Applied Sciences 5 (7): 777-782, 2008 ISSN 1546-9239 © 2008 Science Publications A Password-Based Key Derivation Algorithm Using the KBRP Method 1Shakir M. Hussain and 2Hussein Al-Bahadili 1Faculty of CSIT, Applied Science University, P.O. Box 22, Amman 11931, Jordan 2Faculty of Information Systems and Technology, Arab Academy for Banking and Financial Sciences, P.O. Box 13190, Amman 11942, Jordan Abstract: This study presents a new efficient password-based strong key derivation algorithm using the key based random permutation the KBRP method. The algorithm consists of five steps, the first three steps are similar to those formed the KBRP method. The last two steps are added to derive a key and to ensure that the derived key has all the characteristics of a strong key. In order to demonstrate the efficiency of the algorithm, a number of keys are derived using various passwords of different content and length. The features of the derived keys show a good agreement with all characteristics of strong keys. In addition, they are compared with features of keys generated using the WLAN strong key generator v2.2 by Warewolf Labs. Key words: Key derivation, key generation, strong key, random permutation, Key Based Random Permutation (KBRP), key authentication, password authentication, key exchange INTRODUCTION • The key size must be long enough so that it can not Key derivation is the process of generating one or be easily broken more keys for cryptography and authentication, where a • The key should have the highest possible entropy key is a sequence of characters that controls the process (close to unity) [1,2] of a cryptographic or authentication algorithm . -

Authentication and Key Distribution in Computer Networks and Distributed Systems
13 Authentication and key distribution in computer networks and distributed systems Rolf Oppliger University of Berne Institute for Computer Science and Applied Mathematics {JAM) Neubruckstrasse 10, CH-3012 Bern Phone +41 31 631 89 51, Fax +41 31 631 39 65, [email protected] Abstract Authentication and key distribution systems are used in computer networks and dis tributed systems to provide security services at the application layer. There are several authentication and key distribution systems currently available, and this paper focuses on Kerberos (OSF DCE), NetSP, SPX, TESS and SESAME. The systems are outlined and reviewed with special regard to the security services they offer, the cryptographic techniques they use, their conformance to international standards, and their availability and exportability. Keywords Authentication, key distribution, Kerberos, NetSP, SPX, TESS, SESAME 1 INTRODUCTION Authentication and key distribution systems are used in computer networks and dis tributed systems to provide security services at the application layer. There are several authentication and key distribution systems currently available, and this paper focuses on Kerberos (OSF DCE), NetSP, SPX, TESS and SESAME. The systems are outlined and reviewed with special regard to the security services they offer, the cryptographic techniques they use, their conformance to international standards, and their availability and exportability. It is assumed that the reader of this paper is familiar with the funda mentals of cryptography, and the use of cryptographic techniques in computer networks and distributed systems (Oppliger, 1992 and Schneier, 1994). The following notation is used in this paper: • Capital letters are used to refer to principals (users, clients and servers). -

Pressure Sensor/ Rohs 3-Screen Display Sensor Monitor IP65
Remote Type Pressure Sensor/ RoHS 3-Screen Display Sensor Monitor IP65 Pressure Sensor for General Fluids PSE57२ Series Rated pressure range 0 to 1 MPa −100 to 100 kPa 0 to 500 kPa 0 to 2 MPa 0 to 5 MPa 0 to 10 MPa Withstand voltage 500 VAC <Twice that of the PSE560> Materials of Parts in Contact with Fluid Piping port C3604 + Nickel plating Pressure sensor Al2O3 (Alumina 96%) Square ring FKM NewNew 3-Screen Display Sensor Monitor PSE300AC Series Change the settings while checking the measured value. Visualization of Settings Set value (Threshold value) Main screen Measured value (Current pressure value) Hysteresis value Sub screen Delay time Label (Display item), Set value (Threshold value) Peak value Bottom value PSE57२/PSE300AC Series CAT.ES100-119A Pressure Sensor for General Fluids PSE57२ Series bPSE570/573/574 Materials of parts in bPSE575/576/577 Materials of parts in contact with fl uid contact with fl uid (1 MPa/100 kPa/500 kPa) (2 MPa/5 MPa/10 MPa) Pressure sensor PressurePre sensor O-ring Al2O3 Port size AlA 2O3 (Alumina 96%) FKM + Grease (Alumina 96%) R1/4 (with M5 female thread) Square ring FKM Port size Fitting R1/8, 1/4 Fitting C3604 + (with M5 female thread) C3604 + Nickel plating Nickel plating Series Variations Series Variations Proof Proof Model Rated pressure range pressure Model Rated pressure range pressure −100 kPa 0 100 kPa 500 kPa 1 MPa 2 MPa 5 MPa 10 MPa −100 kPa 0 100 kPa 500 kPa 1 MPa 2 MPa 5 MPa 10 MPa 3.0 5.0 PSE570 PSE575 1 MPa MPa 2 MPa MPa 600 12.5 PSE573 ± PSE576 100 kPa kPa 5 MPa MPa 10 MPa 1.5 30 PSE574 -

35 Articles, 2016-07-30 18:01 1
Articles 35 articles, 2016-07-30 18:01 First Windows 10 Redstone 2 Build Shows Up Online, 1 Public Release in August (0.02/1) The Anniversary Update is also referred to as Redstone 1, so the second Redstone update is what comes next, with sources claiming that the public debut will take place in the spring. Microsoft, however, is ready to start work on it in August, and the first builds are likely to be released to insiders soon after the debut of the Anniversary Update. And according to BuildFeed, the first Windows 10 Redstone 2 build 14894 was already compiled on July 27, and Microsoft is testing it internally. For the moment, however, nobody can tell for sure whether the exact same build will be released to insiders too, but the chances are that it won’t as Microsoft compiles new builds daily, and a release candidate will only come later when we get closer to the launch date. What this build does actually is to confirm that work on Redstone 2 has already started and that Insiders will soon receive new goodies to try out on their PCs and mobile devices. Of course, it’s premature to discuss features and improvements that will be part of the first Windows 10 Redstone 2 builds, but given the fact that it’s just the first version, don’t expect any breaking changes to be released so early. Usually, new features are released throughout the development process, and engineers are now just trying to lay off the foundation for this be possible in the next builds. -

TRANSPORT LAYER SECURITY (TLS) Lokesh Phani Bodavula
TRANSPORT LAYER SECURITY (TLS) Lokesh Phani Bodavula October 2015 Abstract 1 Introduction The security of Electronic commerce is completely in the hands of Cryptogra- phy. Most of the transactions through e-commerce sites, auction sites, on-line banking, stock trading and many more are exchanged over the network. SSL or TLS are the additional layers that are required in order to obtain authen- tication, privacy and integrity for all kinds of communication going through network. This paper focuses on the additional layer (TLS) which is responsi- ble for the whole communication. Transport Layer Security is a protocol that is responsible for offering privacy between the communicating applications and their users on Internet. TLS is inserted between the application layer and the network layer-where the session layer is in the OSI model TLS, however, requires a reliable transport channel-typically TCP. 2 History Instead of the end-to-end argument and the S-HTTP proposal the developers at Netscape Communications introduced an interesting secured connection concept of low-layer and high-layer security. For achieving this type of security there em- ployed a new intermediate layer between the transport layer and the application layer which is called as Secure Sockets Layer (SSL). SSL is the starting stage for the evolution of different transport layer security protocols. Technically SSL protocol is assigned to the transport layer because of its functionality is deeply inter-winded with the one of a transport layer protocol like TCP. Coming to history of Transport layer protocols as soon as the National Center for Super- computing Application (NCSA) released the first popular Web browser called Mosaic 1.0 in 1993, Netscape Communications started working on SSL protocol. -

An Efficient Watermarking and Key Generation Technique Using DWT Algorithm in Three- Dimensional Image
International Journal of Recent Technology and Engineering (IJRTE) ISSN: 2277-3878, Volume-8 Issue-2, July 2019 An Efficient Watermarking and Key Generation Technique Using DWT Algorithm in Three- Dimensional Image R. Saikumar, D. Napoleon Abstract:Discrete Wavelet Transform is the algorithm which obtained by compressive sensing. It is a novel technology can be used to increase the contrast of an image for better visual used to compress the data at a higher rate than the quality of an image. The histogram value for original image with highest bins is taken for embedding the data into an image to conventional method. The compression and encryption are perform the histogram equalization for repeating the process achieved by a single linear measurement step through a simultaneously. Information can be embedded into the source measurement matrix, which can be generated by the secret image with some bit value, for recovering the original image key. This key can be shared only among the sender and the without any loss of the pixels. DWT is the first algorithm which has achieved the image contrast enhancement accurately. This receiver at the time of sending and receiving data as a approach maintained the original visual quality of an image even multimedia file. though themessage bits are embedded into the contrast-enhanced images. The proposed work with an original watermarking II. LITERATURE REVIEW scheme based on the least significant bit technique. As a substitute of embedding the data into a simple image as Y. Sridhar et al: An author says about the unique structure watermarking, least significant bitmethod by utilizing the three about the scalable coding for PRNG images which have wavelets transform is applied in the proposed system in order to been encrypted. -

Seminar Manual Pressure Sensors
R R ! ! "" # ! $ ! ! " " # R ! " # $% % & #' ( '(& "! ) '('*# '(%+#! '( '((,- " # '. '(./ 0 '1 '(12 %% ) # *+, - % * !, , * % ! %1 %'2 %1 %%!! % %% , ( %' %) %''3 ! % %'%! (4 %'( ( %'.5# " (' %'16 (( . ## %%6 ! (( %%'& " (. #. / , #& %(5 ( %('$ () %, & % R * * #$% * #$ * (6 1 ('6 7 11 (% 7# 1 (( 1 #" '01- & (' # ('' % ('%+# 1 # " % &( (% # ) (%' " (%%+# )4 (%( "! ) (%.2 )' (%15 )% ##!, , ( (( # ). (('6 )1 ((%, #2 3 #*4 %% 3 (16 % (1' # % (1%8 9 ( $ 3* 5 6 & ( R : ! ! 3 ! " # !"" "!"" # , # # ! 2 " " # Absolute pressure vacuum closed vessel 3 ;8 3 !!2 !"" " !! !# !! '% Level measurement open vessel 3 ';< 3 ' ! " ! 2 ! " ! '(' : ! . R Level measurement closed vessel 3 %;< ' 3 % ! " ! ! 2 !"" " ! " " ! ! ,9 . Flow measurement 3 (;3 8 3 ( ! " " 2 !""" !" " ! '(. '1 2 " " # " !"" 3 ' "# " ! ! # "!"" '% # " 9 : ! 1 R +#! 2# 44!(44 # ! !" #! (2 # '. " + # 9 " ! "#! ! 3 .;,# 2# !#! !/#! !! !" " !! 3 1 ! " 2 ! ! ! 8 == ! ! " : ! R Accumulator charged at Accumulator discharged at max. operating -

Phone Compatibility
Phone Compatibility • Compatible with iPhone models 4S and above using iOS versions 7 or higher. Last Updated: February 14, 2017 • Compatible with phone models using Android versions 4.1 (Jelly Bean) or higher, and that have the following four sensors: Accelerometer, Gyroscope, Magnetometer, GPS/Location Services. • Phone compatibility information is provided by phone manufacturers and third-party sources. While every attempt is made to ensure the accuracy of this information, this list should only be used as a guide. As phones are consistently introduced to market, this list may not be all inclusive and will be updated as new information is received. Please check your phone for the required sensors and operating system. Brand Phone Compatible Non-Compatible Acer Acer Iconia Talk S • Acer Acer Jade Primo • Acer Acer Liquid E3 • Acer Acer Liquid E600 • Acer Acer Liquid E700 • Acer Acer Liquid Jade • Acer Acer Liquid Jade 2 • Acer Acer Liquid Jade Primo • Acer Acer Liquid Jade S • Acer Acer Liquid Jade Z • Acer Acer Liquid M220 • Acer Acer Liquid S1 • Acer Acer Liquid S2 • Acer Acer Liquid X1 • Acer Acer Liquid X2 • Acer Acer Liquid Z200 • Acer Acer Liquid Z220 • Acer Acer Liquid Z3 • Acer Acer Liquid Z4 • Acer Acer Liquid Z410 • Acer Acer Liquid Z5 • Acer Acer Liquid Z500 • Acer Acer Liquid Z520 • Acer Acer Liquid Z6 • Acer Acer Liquid Z6 Plus • Acer Acer Liquid Zest • Acer Acer Liquid Zest Plus • Acer Acer Predator 8 • Alcatel Alcatel Fierce • Alcatel Alcatel Fierce 4 • Alcatel Alcatel Flash Plus 2 • Alcatel Alcatel Go Play • Alcatel Alcatel Idol 4 • Alcatel Alcatel Idol 4s • Alcatel Alcatel One Touch Fire C • Alcatel Alcatel One Touch Fire E • Alcatel Alcatel One Touch Fire S • 1 Phone Compatibility • Compatible with iPhone models 4S and above using iOS versions 7 or higher. -

Data Encryption Standard (DES)
6 Data Encryption Standard (DES) Objectives In this chapter, we discuss the Data Encryption Standard (DES), the modern symmetric-key block cipher. The following are our main objectives for this chapter: + To review a short history of DES + To defi ne the basic structure of DES + To describe the details of building elements of DES + To describe the round keys generation process + To analyze DES he emphasis is on how DES uses a Feistel cipher to achieve confusion and diffusion of bits from the Tplaintext to the ciphertext. 6.1 INTRODUCTION The Data Encryption Standard (DES) is a symmetric-key block cipher published by the National Institute of Standards and Technology (NIST). 6.1.1 History In 1973, NIST published a request for proposals for a national symmetric-key cryptosystem. A proposal from IBM, a modifi cation of a project called Lucifer, was accepted as DES. DES was published in the Federal Register in March 1975 as a draft of the Federal Information Processing Standard (FIPS). After the publication, the draft was criticized severely for two reasons. First, critics questioned the small key length (only 56 bits), which could make the cipher vulnerable to brute-force attack. Second, critics were concerned about some hidden design behind the internal structure of DES. They were suspicious that some part of the structure (the S-boxes) may have some hidden trapdoor that would allow the National Security Agency (NSA) to decrypt the messages without the need for the key. Later IBM designers mentioned that the internal structure was designed to prevent differential cryptanalysis. -

Brand Old Device
# New Device Old Device - Brand Old Device - Model Name 1 Galaxy A6+ Asus Asus Zenfone 2 Laser ZE500KL 2 Galaxy A6+ Asus Asus Zenfone 2 Laser ZE601KL 3 Galaxy A6+ Asus Asus ZenFone 2 ZE550ML 4 Galaxy A6+ Asus Asus Zenfone 2 ZE551ML 5 Galaxy A6+ Asus Asus Zenfone 3 Laser 6 Galaxy A6+ Asus Asus Zenfone 3 Max ZC520TL 7 Galaxy A6+ Asus Asus Zenfone 3 Max ZC553KL 8 Galaxy A6+ Asus Asus Zenfone 3 ZE520KL 9 Galaxy A6+ Asus Asus Zenfone 3 ZE552KL 10 Galaxy A6+ Asus Asus Zenfone 3s Max 11 Galaxy A6+ Asus Asus Zenfone Max 12 Galaxy A6+ Asus Asus Zenfone Selfie 13 Galaxy A6+ Asus Asus ZenFone Zoom ZX550 14 Galaxy A6+ Gionee Gionee A1 15 Galaxy A6+ Gionee Gionee A1 Lite 16 Galaxy A6+ Gionee Gionee A1 Plus 17 Galaxy A6+ Gionee Gionee Elife E8 18 Galaxy A6+ Gionee Gionee Elife S Plus 19 Galaxy A6+ Gionee Gionee Elife S7 20 Galaxy A6+ Gionee Gionee F103 21 Galaxy A6+ Gionee Gionee F103 Pro 22 Galaxy A6+ Gionee Gionee Marathon M4 23 Galaxy A6+ Gionee Gionee Marathon M5 24 Galaxy A6+ Gionee Gionee marathon M5 Lite 25 Galaxy A6+ Gionee Gionee Marathon M5 Plus 26 Galaxy A6+ Gionee Gionee P5L 27 Galaxy A6+ Gionee Gionee P7 Max 28 Galaxy A6+ Gionee Gionee S6 29 Galaxy A6+ Gionee Gionee S6 Pro 30 Galaxy A6+ Gionee Gionee S6s 31 Galaxy A6+ Gionee Gionee X1s 32 Galaxy A6+ Google Google Pixel 33 Galaxy A6+ Google Google Pixel XL LTE 34 Galaxy A6+ Google Nexus 5X 35 Galaxy A6+ Google Nexus 6 36 Galaxy A6+ Google Nexus 6P 37 Galaxy A6+ HTC Htc 10 38 Galaxy A6+ HTC Htc Desire 10 Pro 39 Galaxy A6+ HTC Htc Desire 628 40 Galaxy A6+ HTC HTC Desire 630 41 Galaxy A6+