Data Encryption Standard (DES)
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Improved Cryptanalysis of the Reduced Grøstl Compression Function, ECHO Permutation and AES Block Cipher
Improved Cryptanalysis of the Reduced Grøstl Compression Function, ECHO Permutation and AES Block Cipher Florian Mendel1, Thomas Peyrin2, Christian Rechberger1, and Martin Schl¨affer1 1 IAIK, Graz University of Technology, Austria 2 Ingenico, France [email protected],[email protected] Abstract. In this paper, we propose two new ways to mount attacks on the SHA-3 candidates Grøstl, and ECHO, and apply these attacks also to the AES. Our results improve upon and extend the rebound attack. Using the new techniques, we are able to extend the number of rounds in which available degrees of freedom can be used. As a result, we present the first attack on 7 rounds for the Grøstl-256 output transformation3 and improve the semi-free-start collision attack on 6 rounds. Further, we present an improved known-key distinguisher for 7 rounds of the AES block cipher and the internal permutation used in ECHO. Keywords: hash function, block cipher, cryptanalysis, semi-free-start collision, known-key distinguisher 1 Introduction Recently, a new wave of hash function proposals appeared, following a call for submissions to the SHA-3 contest organized by NIST [26]. In order to analyze these proposals, the toolbox which is at the cryptanalysts' disposal needs to be extended. Meet-in-the-middle and differential attacks are commonly used. A recent extension of differential cryptanalysis to hash functions is the rebound attack [22] originally applied to reduced (7.5 rounds) Whirlpool (standardized since 2000 by ISO/IEC 10118-3:2004) and a reduced version (6 rounds) of the SHA-3 candidate Grøstl-256 [14], which both have 10 rounds in total. -
Public-Key Cryptography
Public Key Cryptography EJ Jung Basic Public Key Cryptography public key public key ? private key Alice Bob Given: Everybody knows Bob’s public key - How is this achieved in practice? Only Bob knows the corresponding private key Goals: 1. Alice wants to send a secret message to Bob 2. Bob wants to authenticate himself Requirements for Public-Key Crypto ! Key generation: computationally easy to generate a pair (public key PK, private key SK) • Computationally infeasible to determine private key PK given only public key PK ! Encryption: given plaintext M and public key PK, easy to compute ciphertext C=EPK(M) ! Decryption: given ciphertext C=EPK(M) and private key SK, easy to compute plaintext M • Infeasible to compute M from C without SK • Decrypt(SK,Encrypt(PK,M))=M Requirements for Public-Key Cryptography 1. Computationally easy for a party B to generate a pair (public key KUb, private key KRb) 2. Easy for sender to generate ciphertext: C = EKUb (M ) 3. Easy for the receiver to decrypt ciphertect using private key: M = DKRb (C) = DKRb[EKUb (M )] Henric Johnson 4 Requirements for Public-Key Cryptography 4. Computationally infeasible to determine private key (KRb) knowing public key (KUb) 5. Computationally infeasible to recover message M, knowing KUb and ciphertext C 6. Either of the two keys can be used for encryption, with the other used for decryption: M = DKRb[EKUb (M )] = DKUb[EKRb (M )] Henric Johnson 5 Public-Key Cryptographic Algorithms ! RSA and Diffie-Hellman ! RSA - Ron Rives, Adi Shamir and Len Adleman at MIT, in 1977. • RSA -

Key-Dependent Approximations in Cryptanalysis. an Application of Multiple Z4 and Non-Linear Approximations
KEY-DEPENDENT APPROXIMATIONS IN CRYPTANALYSIS. AN APPLICATION OF MULTIPLE Z4 AND NON-LINEAR APPROXIMATIONS. FX Standaert, G Rouvroy, G Piret, JJ Quisquater, JD Legat Universite Catholique de Louvain, UCL Crypto Group, Place du Levant, 3, 1348 Louvain-la-Neuve, standaert,rouvroy,piret,quisquater,[email protected] Linear cryptanalysis is a powerful cryptanalytic technique that makes use of a linear approximation over some rounds of a cipher, combined with one (or two) round(s) of key guess. This key guess is usually performed by a partial decryp- tion over every possible key. In this paper, we investigate a particular class of non-linear boolean functions that allows to mount key-dependent approximations of s-boxes. Replacing the classical key guess by these key-dependent approxima- tions allows to quickly distinguish a set of keys including the correct one. By combining different relations, we can make up a system of equations whose solu- tion is the correct key. The resulting attack allows larger flexibility and improves the success rate in some contexts. We apply it to the block cipher Q. In parallel, we propose a chosen-plaintext attack against Q that reduces the required number of plaintext-ciphertext pairs from 297 to 287. 1. INTRODUCTION In its basic version, linear cryptanalysis is a known-plaintext attack that uses a linear relation between input-bits, output-bits and key-bits of an encryption algorithm that holds with a certain probability. If enough plaintext-ciphertext pairs are provided, this approximation can be used to assign probabilities to the possible keys and to locate the most probable one. -
Vector Boolean Functions: Applications in Symmetric Cryptography
Vector Boolean Functions: Applications in Symmetric Cryptography José Antonio Álvarez Cubero Departamento de Matemática Aplicada a las Tecnologías de la Información y las Comunicaciones Universidad Politécnica de Madrid This dissertation is submitted for the degree of Doctor Ingeniero de Telecomunicación Escuela Técnica Superior de Ingenieros de Telecomunicación November 2015 I would like to thank my wife, Isabel, for her love, kindness and support she has shown during the past years it has taken me to finalize this thesis. Furthermore I would also liketo thank my parents for their endless love and support. Last but not least, I would like to thank my loved ones such as my daughter and sisters who have supported me throughout entire process, both by keeping me harmonious and helping me putting pieces together. I will be grateful forever for your love. Declaration The following papers have been published or accepted for publication, and contain material based on the content of this thesis. 1. [7] Álvarez-Cubero, J. A. and Zufiria, P. J. (expected 2016). Algorithm xxx: VBF: A library of C++ classes for vector Boolean functions in cryptography. ACM Transactions on Mathematical Software. (In Press: http://toms.acm.org/Upcoming.html) 2. [6] Álvarez-Cubero, J. A. and Zufiria, P. J. (2012). Cryptographic Criteria on Vector Boolean Functions, chapter 3, pages 51–70. Cryptography and Security in Computing, Jaydip Sen (Ed.), http://www.intechopen.com/books/cryptography-and-security-in-computing/ cryptographic-criteria-on-vector-boolean-functions. (Published) 3. [5] Álvarez-Cubero, J. A. and Zufiria, P. J. (2010). A C++ class for analysing vector Boolean functions from a cryptographic perspective. -

A Quantitative Study of Advanced Encryption Standard Performance
United States Military Academy USMA Digital Commons West Point ETD 12-2018 A Quantitative Study of Advanced Encryption Standard Performance as it Relates to Cryptographic Attack Feasibility Daniel Hawthorne United States Military Academy, [email protected] Follow this and additional works at: https://digitalcommons.usmalibrary.org/faculty_etd Part of the Information Security Commons Recommended Citation Hawthorne, Daniel, "A Quantitative Study of Advanced Encryption Standard Performance as it Relates to Cryptographic Attack Feasibility" (2018). West Point ETD. 9. https://digitalcommons.usmalibrary.org/faculty_etd/9 This Doctoral Dissertation is brought to you for free and open access by USMA Digital Commons. It has been accepted for inclusion in West Point ETD by an authorized administrator of USMA Digital Commons. For more information, please contact [email protected]. A QUANTITATIVE STUDY OF ADVANCED ENCRYPTION STANDARD PERFORMANCE AS IT RELATES TO CRYPTOGRAPHIC ATTACK FEASIBILITY A Dissertation Presented in Partial Fulfillment of the Requirements for the Degree of Doctor of Computer Science By Daniel Stephen Hawthorne Colorado Technical University December, 2018 Committee Dr. Richard Livingood, Ph.D., Chair Dr. Kelly Hughes, DCS, Committee Member Dr. James O. Webb, Ph.D., Committee Member December 17, 2018 © Daniel Stephen Hawthorne, 2018 1 Abstract The advanced encryption standard (AES) is the premier symmetric key cryptosystem in use today. Given its prevalence, the security provided by AES is of utmost importance. Technology is advancing at an incredible rate, in both capability and popularity, much faster than its rate of advancement in the late 1990s when AES was selected as the replacement standard for DES. Although the literature surrounding AES is robust, most studies fall into either theoretical or practical yet infeasible. -

Quasi-Orthogonal Sequences for Code-Division Multiple-Access Systems Kyeongcheol Yang, Member, IEEE, Young-Ky Kim, and P
982 IEEE TRANSACTIONS ON INFORMATION THEORY, VOL. 46, NO. 3, MAY 2000 Quasi-Orthogonal Sequences for Code-Division Multiple-Access Systems Kyeongcheol Yang, Member, IEEE, Young-Ky Kim, and P. Vijay Kumar, Member, IEEE Abstract—In this paper, the notion of quasi-orthogonal se- correlation between two binary sequences and of quence (QOS) as a means of increasing the number of channels the same length is given by in synchronous code-division multiple-access (CDMA) systems that employ Walsh sequences for spreading information signals and separating channels is introduced. It is shown that a QOS sequence may be regarded as a class of bent (almost bent) functions possessing, in addition, a certain window property. Such sequences while increasing system capacity, minimize interference where is computed modulo for all . It is easily to the existing set of Walsh sequences. The window property gives shown that where denotes the the system the ability to handle variable data rates. A general procedure of constructing QOS's from well-known families of Hamming distance of two vectors and . Two sequences are binary sequences with good correlation, including the Kasami and said to be orthogonal if their correlation is zero. Gold sequence families, as well as from the binary Kerdock code Let be a family of binary is provided. Examples of QOS's are presented for small lengths. sequences of period . The family is said to be orthogonal if Some examples of quaternary QOS's drawn from Family are any two sequences are mutually orthogonal, that is, also included. for any and . For example, the Walsh sequence family of Index Terms—Bent functions, code-division multiple-access sys- length is orthogonal. -

Public Key Cryptography And
PublicPublic KeyKey CryptographyCryptography andand RSARSA Raj Jain Washington University in Saint Louis Saint Louis, MO 63130 [email protected] Audio/Video recordings of this lecture are available at: http://www.cse.wustl.edu/~jain/cse571-11/ Washington University in St. Louis CSE571S ©2011 Raj Jain 9-1 OverviewOverview 1. Public Key Encryption 2. Symmetric vs. Public-Key 3. RSA Public Key Encryption 4. RSA Key Construction 5. Optimizing Private Key Operations 6. RSA Security These slides are based partly on Lawrie Brown’s slides supplied with William Stallings’s book “Cryptography and Network Security: Principles and Practice,” 5th Ed, 2011. Washington University in St. Louis CSE571S ©2011 Raj Jain 9-2 PublicPublic KeyKey EncryptionEncryption Invented in 1975 by Diffie and Hellman at Stanford Encrypted_Message = Encrypt(Key1, Message) Message = Decrypt(Key2, Encrypted_Message) Key1 Key2 Text Ciphertext Text Keys are interchangeable: Key2 Key1 Text Ciphertext Text One key is made public while the other is kept private Sender knows only public key of the receiver Asymmetric Washington University in St. Louis CSE571S ©2011 Raj Jain 9-3 PublicPublic KeyKey EncryptionEncryption ExampleExample Rivest, Shamir, and Adleman at MIT RSA: Encrypted_Message = m3 mod 187 Message = Encrypted_Message107 mod 187 Key1 = <3,187>, Key2 = <107,187> Message = 5 Encrypted Message = 53 = 125 Message = 125107 mod 187 = 5 = 125(64+32+8+2+1) mod 187 = {(12564 mod 187)(12532 mod 187)... (1252 mod 187)(125 mod 187)} mod 187 Washington University in -
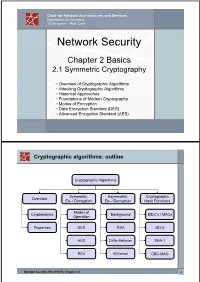
The Data Encryption Standard (DES) – History
Chair for Network Architectures and Services Department of Informatics TU München – Prof. Carle Network Security Chapter 2 Basics 2.1 Symmetric Cryptography • Overview of Cryptographic Algorithms • Attacking Cryptographic Algorithms • Historical Approaches • Foundations of Modern Cryptography • Modes of Encryption • Data Encryption Standard (DES) • Advanced Encryption Standard (AES) Cryptographic algorithms: outline Cryptographic Algorithms Symmetric Asymmetric Cryptographic Overview En- / Decryption En- / Decryption Hash Functions Modes of Cryptanalysis Background MDC’s / MACs Operation Properties DES RSA MD-5 AES Diffie-Hellman SHA-1 RC4 ElGamal CBC-MAC Network Security, WS 2010/11, Chapter 2.1 2 Basic Terms: Plaintext and Ciphertext Plaintext P The original readable content of a message (or data). P_netsec = „This is network security“ Ciphertext C The encrypted version of the plaintext. C_netsec = „Ff iThtIiDjlyHLPRFxvowf“ encrypt key k1 C P key k2 decrypt In case of symmetric cryptography, k1 = k2. Network Security, WS 2010/11, Chapter 2.1 3 Basic Terms: Block cipher and Stream cipher Block cipher A cipher that encrypts / decrypts inputs of length n to outputs of length n given the corresponding key k. • n is block length Most modern symmetric ciphers are block ciphers, e.g. AES, DES, Twofish, … Stream cipher A symmetric cipher that generats a random bitstream, called key stream, from the symmetric key k. Ciphertext = key stream XOR plaintext Network Security, WS 2010/11, Chapter 2.1 4 Cryptographic algorithms: overview -
Blockchain Beyond Cryptocurrency Or Is Private Chain a Hoax Or How I Lose Money in Bitcoin but Still Decide to Get in the Research
Blockchain Beyond Cryptocurrency Or Is Private Chain a Hoax Or How I Lose Money in Bitcoin but still Decide to Get in the Research Hong Wan Edward P. Fitts Department of Industrial and Systems Engineering Sept 2019 In this talk: • Blockchain and trust • Different kinds of blockchain • Cases and Examples • Discussions First Things First https://images.app.goo.gl/JuNznV8dZKTaHWEf9 Disclaimer Block and Chain https://youtu.be/SSo_EIwHSd4 https://youtu.be/SSo_EIwHSd4 Blockchain Design Questions • Who can access data: Private vs. Public • Who can validate data/add block: Permissioned vs Permissionless • Consensus to be used: Trade-off among security and efficiency. https://www.google.com/url?sa=i&rct=j&q=&esrc=s&source=images&cd=&ved=2ahUKEwinjN2s7_DkAhXlmeAKHXxhAIUQjRx6BAgBEAQ&url=ht tps%3A%2F%2F101blockchains.com%2Fconsensus-algorithms-blockchain%2F&psig=AOvVaw23pKh4qS8W_xgyajJ3aFl9&ust=1569669093339830 Bad News First • “Private blockchains are completely uninteresting… -- the only reason to operate one is to ride on the blockchain hype…” Bruce Schneier Tonight we will talk about cryptocurrencies… .everything you don’t understand money combined by everything you don’t understand about computers…. Cryptocurrencies: Last Week Tonight with John Oliver (HBO) https://www.schneier.com/blog/archives/2019/02/blockchain_and_.html http://shorturl.at/ahsRU, shorturl.at/gETV2 https://www.google.com/url?sa=i&rct=j&q=&esrc=s&source=images&cd=&ved=2ahUKEwj- https://d279m997dpfwgl.cloudfront.net/wp/2017/11/Trustp72L7vDkAhVjQt8KHU18CjsQjRx6BAgBEAQ&url=https%3A%2F%2Fwww.wbur.org%2Fonpoint%2F2017%2F11%2F20%2Fwho-can-cropped.jpg-you- -
Advanced Encryption Standard (Aes) Modes of Operation
ADVANCED ENCRYPTION STANDARD (AES) MODES OF OPERATION 1 Arya Rohan Under the guidance of Dr. Edward Schneider University of Maryland, College Park MISSION: TO SIMULATE BLOCK CIPHER MODES OF OPERATION FOR AES IN MATLAB Simulation of the AES (Rijndael Algorithm) in MATLAB for 128 bit key-length. Simulation of the five block cipher modes of operation for AES as per FIPS publication. Comparison of the five modes based on Avalanche Effect. Future Work 2 OUTLINE A brief history of AES Galois Field Theory De-Ciphering the Algorithm-ENCRYPTION De-Ciphering the Algorithm-DECRYPTION Block Cipher Modes of Operation Avalanche Effect Simulation in MATLAB Conclusion & Future Work References 3 A BRIEF HISTORY OF AES 4 In January 1997, researchers world-over were invited by NIST to submit proposals for a new standard to be called Advanced Encryption Standard (AES). From 15 serious proposals, the Rijndael algorithm proposed by Vincent Rijmen and Joan Daemen, two Belgian cryptographers won the contest. The Rijndael algorithm supported plaintext sizes of 128, 192 and 256 bits, as well as, key-lengths of 128, 192 and 256 bits. The Rijndael algorithm is based on the Galois field theory and hence it gives the algorithm provable 5 security properties. GALOIS FIELD 6 GALOIS FIELD - GROUP Group/Albelian Group: A group G or {G, .} is a set of elements with a binary operation denoted by . , that associates to each ordered pair (a, b) of elements in G an element (a . b) such that the following properties are obeyed: Closure: If a & b belong to G, then a . b also belongs to G. -

Chapter 3 – Block Ciphers and the Data Encryption Standard
Chapter 3 –Block Ciphers and the Data Cryptography and Network Encryption Standard Security All the afternoon Mungo had been working on Stern's Chapter 3 code, principally with the aid of the latest messages which he had copied down at the Nevin Square drop. Stern was very confident. He must be well aware London Central knew about that drop. It was obvious Fifth Edition that they didn't care how often Mungo read their messages, so confident were they in the by William Stallings impenetrability of the code. —Talking to Strange Men, Ruth Rendell Lecture slides by Lawrie Brown Modern Block Ciphers Block vs Stream Ciphers now look at modern block ciphers • block ciphers process messages in blocks, each one of the most widely used types of of which is then en/decrypted cryptographic algorithms • like a substitution on very big characters provide secrecy /hii/authentication services – 64‐bits or more focus on DES (Data Encryption Standard) • stream ciphers process messages a bit or byte at a time when en/decrypting to illustrate block cipher design principles • many current ciphers are block ciphers – better analysed – broader range of applications Block vs Stream Ciphers Block Cipher Principles • most symmetric block ciphers are based on a Feistel Cipher Structure • needed since must be able to decrypt ciphertext to recover messages efficiently • bloc k cihiphers lklook like an extremely large substitution • would need table of 264 entries for a 64‐bit block • instead create from smaller building blocks • using idea of a product cipher 1 Claude -

Impossible Differentials in Twofish
Twofish Technical Report #5 Impossible differentials in Twofish Niels Ferguson∗ October 19, 1999 Abstract We show how an impossible-differential attack, first applied to DEAL by Knudsen, can be applied to Twofish. This attack breaks six rounds of the 256-bit key version using 2256 steps; it cannot be extended to seven or more Twofish rounds. Keywords: Twofish, cryptography, cryptanalysis, impossible differential, block cipher, AES. Current web site: http://www.counterpane.com/twofish.html 1 Introduction 2.1 Twofish as a pure Feistel cipher Twofish is one of the finalists for the AES [SKW+98, As mentioned in [SKW+98, section 7.9] and SKW+99]. In [Knu98a, Knu98b] Lars Knudsen used [SKW+99, section 7.9.3] we can rewrite Twofish to a 5-round impossible differential to attack DEAL. be a pure Feistel cipher. We will demonstrate how Eli Biham, Alex Biryukov, and Adi Shamir gave the this is done. The main idea is to save up all the ro- technique the name of `impossible differential', and tations until just before the output whitening, and applied it with great success to Skipjack [BBS99]. apply them there. We will use primes to denote the In this report we show how Knudsen's attack can values in our new representation. We start with the be applied to Twofish. We use the notation from round values: [SKW+98] and [SKW+99]; readers not familiar with R0 = ROL(Rr;0; (r + 1)=2 ) the notation should consult one of these references. r;0 b c R0 = ROR(Rr;1; (r + 1)=2 ) r;1 b c R0 = ROL(Rr;2; r=2 ) 2 The attack r;2 b c R0 = ROR(Rr;3; r=2 ) r;3 b c Knudsen's 5-round impossible differential works for To get the same output we update the rule to com- any Feistel cipher where the round function is in- pute the output whitening.