Connecting to the WAN
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Leased-Line Replacement
Leased-Line REPLACEMENT Utilizing gigabit wireless links to provide fiber-like performance at significant savings compared to leased lines. WHITE PAPER Leased-Line Replacement T1 (1.5 Mbps) line is not enough capacity to handle the need, four T1s When considering high-bandwidth connections between locations, the are ordered from the telco at a monthly rate of $500 each ($2,000 per thinking used to be that the only way to get service was to pick up the month). This twelve month commitment also requires a startup fee of phone, call the Local Exchange Carrier (LEC) and order a circuit. As long $1,000 to cover equipment and provisioning of the circuits. This amounts as the startup costs and monthly recurring charges were within the IT to $25,000 for the one year lease to provide a 6 Mbps connection budget, and the IT manager and business administrators were content between the corporate headquarters and the satellite office. with the level of service provided, writing a monthly check to the LEC was not a problem. If troubles were encountered with the service, a In the second scenario, a DS3 leased line is used to connect a school’s phone call to the provider was all that was necessary to resolve the LAN to the district office backbone three miles away. Services such as problem. voice, data, Internet access, and classroom video are transported over the circuit. To establish service, the local carrier requires a startup fee Businesses relying on leased lines find a wide range of performance of $3,000 that covers the cost of edge devices, as well as installation options tailored to suit their needs, from T1/E1 (1.5/2 Mbps), multiple and commissioning. -

Multimedia, Internet, On-Line
Section IV: Multimedia, the Internet, and On-Line Services High-End Digital Video Applications Larry Amiot Electronic and Computing Technologies Division Argonne National Laboratory The emphasis of this paper is on the high-end applications Internet and Intranet that are driving digital video. The research with which I am involved at Argonne National Laboratory is not done on dig- The packet video networks which currently support many ital video per se, but rather on how the research applications applications such as file transfer, Mbone video (talking at the laboratory drive its requirements for digital video. The heads), and World Wide Web browsing are limiting for high- paper will define what digital video is, what some of its com- quality video because of the low throughput one can achieve ponents are, and then discuss a few applications that are dri- via the Internet or intranets. Examples of national packet ving the development of these components. The focus will be switched networks developed in the last several years include on what digital video means to individuals in the research the National Science Foundation Network (NSFNet). The and education community. Department of Energy had its own network called ESNET, and the National Aeronautics and Space Administration The Digital Video Environment (NASA) had a network as well. Recently, the NSFNet was de- commissioned, and commercial interests are now starting to In 1996, a group of people from several universities in the fill that void. Research and education communities are find- Midwest and from Argonne formed a Video Working Group. ing, however, that this new commercial Internet is too re- This body tried to define the areas of digital video of impor- stricting and does not meet their throughput requirements; it tance to their institutions. -

Digital Subscriber Lines and Cable Modems Digital Subscriber Lines and Cable Modems
Digital Subscriber Lines and Cable Modems Digital Subscriber Lines and Cable Modems Paul Sabatino, [email protected] This paper details the impact of new advances in residential broadband networking, including ADSL, HDSL, VDSL, RADSL, cable modems. History as well as future trends of these technologies are also addressed. OtherReports on Recent Advances in Networking Back to Raj Jain's Home Page Table of Contents ● 1. Introduction ● 2. DSL Technologies ❍ 2.1 ADSL ■ 2.1.1 Competing Standards ■ 2.1.2 Trends ❍ 2.2 HDSL ❍ 2.3 SDSL ❍ 2.4 VDSL ❍ 2.5 RADSL ❍ 2.6 DSL Comparison Chart ● 3. Cable Modems ❍ 3.1 IEEE 802.14 ❍ 3.2 Model of Operation ● 4. Future Trends ❍ 4.1 Current Trials ● 5. Summary ● 6. Glossary ● 7. References http://www.cis.ohio-state.edu/~jain/cis788-97/rbb/index.htm (1 of 14) [2/7/2000 10:59:54 AM] Digital Subscriber Lines and Cable Modems 1. Introduction The widespread use of the Internet and especially the World Wide Web have opened up a need for high bandwidth network services that can be brought directly to subscriber's homes. These services would provide the needed bandwidth to surf the web at lightning fast speeds and allow new technologies such as video conferencing and video on demand. Currently, Digital Subscriber Line (DSL) and Cable modem technologies look to be the most cost effective and practical methods of delivering broadband network services to the masses. <-- Back to Table of Contents 2. DSL Technologies Digital Subscriber Line A Digital Subscriber Line makes use of the current copper infrastructure to supply broadband services. -
Glossary of Communications Terms for Relay Engineers
Glossary of Communications Terms For Relay Engineers A Working Group Report from the H14 WG Of the H – Relaying Communications Subcommittee May 2008 Participants Roger Ray, Chairman Ray Young, Vice Chairman Marc Benou Oscar Bolado Jim Huddelston Stan Klein Ken Martin John Miller Tim Phillippe Mark Simon Mal Swanson Disclaimer This document has been prepared in order to give the Protective Relay Engineer an insight and understanding of communication terms that they may encounter in their work. It is not meant to be a substitute for or replace the IEEE Dictionary. Glossary of Communications Terms For Relay Engineers AAL - ATM Adaptation Layer The standards layer that allows multiple applications to have data converted to and from the ATM cell. A protocol used that translates higher layer services into the size and format of an ATM cell. ACCUNET Switched 56 An AT&T digital service providing switched (dialup) digital service at 56 Kbps. ACCUNET T1.5 An AT&T tariffed data oriented digital service that provides leased end-to-end customer premises terminated T-1 links. ACCUNET T1.5 Reserved A disaster recovery service whereby a switched 1.544 Mbps link is available between COs and is activated when AT&T is notified of the T-1 link failure. ACCUNET T45 An AT&T tariffed service that provides 45 Mbps, DS3 service which can carry 28 T-1 connections (672 voice channels). ACD - Automatic Call Distributor A telephone facility that manages incoming calls and handles them based on the number called and an associated database of handling instructions. ADPCM - Adaptive Differential Pulse Code Modulation A speech coding method which uses fewer bits than the traditional PCM (Pulse Code Modulation). -
Guide to Leased Lines
Guide to Leased Lines 1 WHAT IS A LEASED LINE? The term ‘leased line’ refers to a dedicated connection that allows communication between two sites (a point‐to‐point leased line) or between a site and the Internet (an internet leased line). Leased lines typically deliver bandwidth over a leased fibre connection, although copper local tails can sometimes be used as well. Leased lines are considered a premium connectivity product because unlike various broadband services leased lines are dedicated, uncontended data lines with symmetrical bandwidth speeds. With dedicated lines, users can get higher speeds of service and a higher service level guarantee. 2 WHAT ARE THE BENEFITS OF A LEASED LINE? More bandwidth – leased lines can deliver between 2Mbit/s to 1,000Mbit/s of connectivity to most UK businesses, and up to 10Gbit/s in some urban locations. Consistent speeds – your bandwidth is reserved exclusively for your use, so you can experience a consistently high data throughput at all times – even during peak usage periods. Fast upload speeds – leased lines are symmetrical, meaning you get the same high speed upstream as you get ownstream. This is ideal for VoIP, terminal services, online data backup, video conferencing, server hosting and the sending of large files. Unlimited data transfer – you can use your connection flat out, all the time. You can do whatever you like with it (subject to the law). There are no extra charges if you go over some arbitrary monthly usage quota. No‐one’s going to slow down your connection if you exceed an unspecified ‘fair usage’ limit. -

Wide Area Network
Wide area network A wide area network (WAN) is a telecommunications network or computer network that extends over a large geographical distance. Wide area networks are often established with leased telecommunication circuits.[1] Business, education and government entities use wide area networks to relay data to staff, students, clients, buyers, and suppliers from various locations across the world. In essence, this mode of telecommunication allows a business to effectively carry out its daily function regardless of location. The Internet may be considered a WAN.[2] Related terms for other types of networks are personal area networks (PANs), local area networks (LANs), campus area networks (CANs), or metropolitan area networks (MANs) which are usually limited to a room, building, campus or specific metropolitan area respectively. Contents Design options Connection technology List of WAN types See also References External links Design options The textbook definition of a WAN is a computer network spanning regions, countries, or even the world.[3] However, in terms of the application of computer networking protocols and concepts, it may be best to view WANs as computer networking technologies used to transmit data over long distances, and between different LANs, MANs and other localised computer networking architectures. This distinction stems from the fact that common LAN technologies operating at lower layers of the OSI model (such as the forms of Ethernet or Wi-Fi) are often designed for physically proximal networks, and thus cannot transmit data over tens, hundreds or even thousands of miles or kilometres. WANs do not just necessarily connect physically disparate LANs. A CAN, for example, may have a localized backbone of a WAN technology, which connects different LANs within a campus. -

Understanding Wide Area Networks
Understanding Wide Area Networks Module 7 Objectives Skills/Concepts Objective Domain Objective Domain Description Number Understanding routing Understanding routers 2.2 Defining common WAN Understanding wide area 1.3 technologies and networks (wan’s) connections Routing • Routing is the process of managing the flow of data between network segments and between hosts or routers • Data is sent along a path according to the IP networks and individual IP addresses of the hosts • A router is a network device that maintains tables of information about other routers on the network or internetwork Static and Dynamic Routing • A static route is a path that is manually configured and remains constant throughout the router’s operation • A dynamic route is a path that is generated dynamically by using special routing protocols Static Dynamic Dynamic Routing • Dynamic routing method has two conceptual parts: • Routing protocol used to convey information about the network environment • Routing Algorithm that determines paths through the network • Common Dynamic routing protocols: • Distance vector routing protocols: Advertise the number of hops to a network destination (distance) and the direction a packet can reach a network destination (vector). Sends updates at regularly scheduled intervals, and can take time for route changes to be updated • Link state routing protocols: Provide updates only when a network link changes state • Distance Vector Routing • Routing Information Protocol (RIP) • Link State Routing • Open Shortest Path First (OSPF) Interior -

The Internet Development Process: Observations and Reflections
The Internet Development Process: Observations and Reflections Pål Spilling University Graduate Center (UNIK), Kjeller, Norway [email protected] Abstract. Based on the experience of being part of the team that developed the internet, the author will look back and provide a history of the Norwegian participation. The author will attempt to answer a number of questions such as why was The Norwegian Defense Research Establishment (FFI) invited to participate in the development process, what did Norway contribute to in the project, and what did Norway benefit from its participation? Keywords: ARPANET, DARPA, Ethernet, Internet, PRNET. 1 A Short Historical Résumé The development of the internet went through two main phases. The first one laid the foundation for packet switching in a single network called ARPANET. The main idea behind the development of ARPANET was resource sharing [1]. At that time computers, software, and communication lines were very expensive, meaning that these resources had to be shared among as many users as possible. The development started at the end of 1968. The U.S. Defense Advanced Research Project Agency (DARPA) funded and directed it in a national project. It became operational in 1970; in a few years, it spanned the U.S. from west to east with one arm westward to Hawaii and one arm eastward to Kjeller, Norway, and then onwards to London. The next phase, the “internet project,” started in the latter half of 1974 [2]. The purpose of the project was to develop technologies to interconnect networks based on different communication principles, enabling end-to-end communications between computers connected to different networks. -

Original Page 2
PUERTO RICO TELEPHONE COMPANY, INC. Local Tariff Fifth Revision - Page F-7-1 Canceling Fourth Revision - Page F-7-1 ADDITIONAL SERVICES TARIFF SCHEDULE (Cont.) SECTION 7 – LEASED LINE SERVICE 7.1 General Leased Line Service provides the necessary facilities to enable the customer and authorized users to communicate between specified locations. (T) 7.1.1 The connections provided under the Leased Line Service can be either analog or (M,T) digital. Analog connections are differentiated by spectrum and bandwidth. Digital | connections are differentiated by bit rates. | | 7.1.2 Following is a brief description of each type of Leased Line Service: | | A. Metallic – a channel for the transmission of low speed varying signals at | rates up to 30 baud. | | B. Telegraph Grade – a channel for the transmission of binary signals at rates | of 0 to 75 baud or 0 to 150 baud. | | C. Voice Grade – a channel for the transmission of analog signals within an | approximate bandwidth of 300 to 3000 Hz. | | D. Program Audio – a channel for the transmission of audio signals. The | nominal frequency bandwidths are from 200 to 3500 Hz, from 100 to 5000 | Hz, from 50 to 8000 Hz, or from 50 to 15000 Hz. | | E. Digital Data – a channel for the digital transmission of synchronous serial | data rates of 2.4, 4.8, 9.6, 19.2, 56.0 or 64.0 Kbps. | | F. High Capacity – a channel for the transmission of synchronous serial digital | data at rates of 1.544, 6.312 or 44.736 Mbps. (M,T) (E) 7.2 Regulations 7.2.1 Leased Line Service is furnished subject to the availability of facilities and is provided over facilities elected by the Company. -
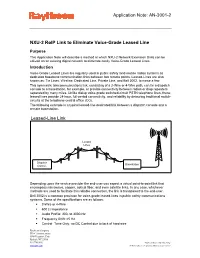
NXU-2 Roip Link to Eliminate Voice-Grade Leased Line
Application Note: AN-3001-2 NXU-2 RoIP Link to Eliminate Voice-Grade Leased Line Purpose This Application Note will describe a method at which NXU-2 Network Extension Units can be utilized on an existing digital network to eliminate costly Voice-Grade Leased Lines. Introduction Voice-Grade Leased Lines are regularly used in public safety land-mobile radios systems as dedicated baseband communication links between two remote points. Leased-Lines are also known as: Tie Lines, Wireline, Dedicated Line, Private Line, and Bell 3002, to name a few. This symmetric telecommunications link, consisting of a 2-Wire or 4-Wire path, can tie a dispatch console to a basestation, for example, or provide connectivity between radios or drop repeaters separated by many miles. Unlike dialup voice-grade switched-circuit PSTN telephone lines, these leased lines provide 24-hour, full-period connectivity, and reliability by detouring traditional switch- circuits at the telephone central office (CO). The following example is a typical leased-line dedicated link between a dispatch console and a remote basestation. Leased-Line Link Leased Lines Dispatch Basestation Console Depending upon the service provider the end-user can expect a virtual point-to-point link that encompass microwave, copper, optical fiber, and even satellite links. In any case, whichever methods are used to facilitate this reliable connection, the link is transparent to the end-user. Bell 3002 is a common provision for voice-grade leased-lines in public safety communications systems. Some of the specifications are as follows: 2-Wire or 4-Wire 600 Ω Impedance Audio Profile: 300- to 3000-Hz Frequency Shift: ±5 Hz Control: Tone Only, no DC Control due to lack of hard wire Raytheon Company JPS Communications 5800 Departure Drive Raleigh, NC 27616 919.790.1011 © Raytheon.Data is subject to change. -

Proxim Wireless for Governments and Municipalities
Proxim Wireless for Governments and Municipalities Municipalities and Governments demand secure, reliable and cost-effective solutions that can scale easily to connect various departments such as public works, fire and police departments etc. Typically, governments have been using leased line solutions, which involve connecting distant offices with copper or fiber. The Internet Service Provider charges the customer (governments) on a recurring basis, along with one time installation and deployment charges. As one might guess, these solutions result in high OPex and CAPex budgets. For over 30 years, Proxim’s line of outdoor point to point and multipoint solutions have provided secure, scalable, robust and high capacity solutions for governments all across the globe. Proxim Tsunami® radios are capable of operating in a wide range of frequencies with solutions from 25 Mbps to 600 Mbps +real world throughput. Proxim also provides indoor and outdoor WiFi for increased collaboration between teams inside offices and field and first responder teams. Proxim Enables a Wide Variety of Government Applications 1 Replace Leased Line Connections 2 Indoor and Outdoor WiFi 3 Video Surveillance © Proxim Wireless. All rights reserved. 1 Proxim Wireless Solutions Replace Leased Line Connections Proxim helps rapidly deploy cost-effective network solutions that come at a fraction of the traditional leased line costs. There are no recurring costs involved and Proxim’s solutions come at relatively low capital costs. In addition, wireless solutions are immune to cable cuts that are an inherent risk when deploying wirelines based solutions; making wireless networks a perfect solution for primary or secondary backup connectivity needs. Indoor and Outdoor WiFi Proxim’s ORiNOCO® product line features outdoor and indoor high speed WiFi Access Points capable of delivering speeds of up to 1750 Mbps. -

Point-To-Point Connections
CHAPTER 3 Point-to-Point Connections Objectives Upon completion of this chapter ■ What are the fundamentals of point-to-point ■ How is a PPP session established? serial communications across a WAN? ■ How do you configure PPP encapsulation on ■ How do you configure HDLC encapsulation a point-to-point serial link? on a point-to-point serial link? ■ How do you configure PPP authentication ■ What are the benefits of using PPP over protocols? HDLC in a WAN? ■ How are the show and debug commands ■ What is the PPP layered architecture and the used to troubleshoot PPP? functions of LCP and NCP? Key Terms This chapter uses the following key terms. You can find the definitions in the glossary. point-to-point connections page 80 primary station page 99 clock skew page 82 Cisco 7000 page 103 time-division multiplexing (TDM) page 85 trunk lines page 105 statistical time-division multiplexing Link Control Protocol (LCP) page 105 (STDM) page 85 Network Control Protocols (NCPs) page 105 data stream page 85 Novell IPX page 105 transmission link page 85 SNA Control Protocol page 105 demarcation point page 88 Password Authentication Protocol null modem page 91 (PAP) page 119 DS (digital signal level) page 94 Challenge Handshake Authentication Protocol (CHAP) page 119 E1 page 95 fragmentation page 119 E3 page 95 reassembly page 119 bit-oriented page 97 message digest 5 (MD5) page 130 Synchronous Data Link Control (SDLC) page 97 TACACS/TACACS+ page 135 004_9781587133329_ch03.indd4_9781587133329_ch03.indd 7799 33/13/14/13/14 22:56:56 AAMM 80 Connecting Networks Companion Guide Introduction (3.0.1.1) One of the most common types of WAN connections, especially in long-distance communications, is a point-to-point connection, also called a serial or leased line connection.