Deciphering Histone Code of Transcriptional Regulation in Malaria
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Subcloning, Expression, and Enzymatic Study of PRMT5
Georgia State University ScholarWorks @ Georgia State University Biology Theses Department of Biology Summer 7-12-2010 Subcloning, Expression, and Enzymatic Study of PRMT5 Ran Guo Georgia State University Follow this and additional works at: https://scholarworks.gsu.edu/biology_theses Part of the Biology Commons Recommended Citation Guo, Ran, "Subcloning, Expression, and Enzymatic Study of PRMT5." Thesis, Georgia State University, 2010. https://scholarworks.gsu.edu/biology_theses/26 This Thesis is brought to you for free and open access by the Department of Biology at ScholarWorks @ Georgia State University. It has been accepted for inclusion in Biology Theses by an authorized administrator of ScholarWorks @ Georgia State University. For more information, please contact [email protected]. SUBCLONING, EXPRESSION, AND ENZYMATIC STUDY OF PRMT5 by RAN GUO Under the Direction of Yujun George Zheng ABSTRACT Protein arginine methyltransferases (PRMTs) mediate the transfer of methyl groups to arginine residues in histone and non-histone proteins. PRMT5 is an important member of PRMTs which symmetrically dimethylates arginine 8 in histone H3 (H3R8) and arginine 3 in histone H4 (H4R3). PRMT5 was reported to inhibit some tumor suppressors in leukemia and lymphoma cells and regulate p53 gene, through affecting the promoter of p53. Through methylation of H4R3, PRMT5 can recruit DNA-methyltransferase 3A (DNMT3A) which regulates gene transcription. All the above suggest that PRMT5 has an important function of suppressing cell apoptosis and is a potential anticancer target. Currently, the enzymatic activities of PRMT5 are not clearly understood. In our study, we improved the protein expression methodology and greatly enhanced the yield and quality of the recombinant PRMT5. -

Chip Validated H4k5ac (Clone RM140) Antibody with Positive and Negative Primer Sets
www.chromatrap.com Clywedog Rd South Wrexham Industrial Estate Wrexham LL13 9XS, United Kingdom Tel: +44 (0) 1978 666239/40 Email: [email protected] ChIP Validated H4K5ac (Clone RM140) Antibody with Positive and Negative Primer Sets Catalogue no: 900029 Chromatrap®’s ChIP Validated H4K5ac Antibody with Positive Primer Set provides a complete set of tools to assist with a successful ChIP assay. Including: H4K5ac antibody, control rabbit IgG, and positive primer set. The ChIP Validated H4K5ac Antibody with Positive Primer Set is not suitable for use with non-human species. Background: Histone 4 (H4) is one of the five core histone proteins, comprising the protein component of chromatin. H4 is ubiquitous within chromosomes and can be found bound to most gene sequences throughout the genome. Acetylation of lysine 5 on histone 4 (H4K5ac) is associated with open chromatin and active gene transcription. H4K5ac has been shown to have roles in epigenetic bookmarking, a process where genetic information is passed onto daughter cells during cell division. A rabbit IgG is included in this Antibody Primer Set as a negative control for the ChIP experiment. The H4K5ac positive primer set recognises the promoter of the GAPDH gene, associated with active transcription and is a suitable target for this antibody. Suggested Usage: Component Suggested Dilution Figure H4K5ac 2:1 (antibody: chromatin) 1 Rabbit IgG 2:1 (antibody: chromatin) 1 Positive Primer Set Dilute from 4M (provided) to 1M working concentration Please note: Optimal dilutions should be determined by the user. These volumes are stated as guidelines only. Advancements in Epigenetics *This product is for research use only. -

Inferring Causal Relationships Among Different Histone Modifications and Gene Expression
Downloaded from genome.cshlp.org on September 28, 2021 - Published by Cold Spring Harbor Laboratory Press Inferring Causal Relationships among Different Histone Modifications and Gene Expression Hong Yu*, Shanshan Zhu*, Bing Zhou*, Huiling Xue and Jing-Dong J. Han Chinese Academy of Sciences Key Laboratory of Molecular Developmental Biology, Center for Molecular Systems Biology, Institute of Genetics and Developmental Biology, Chinese Academy of Sciences, Datun Road, Beijing, 100101, China * These authors contributed equally to this work. Correspondence should be addressed to J.-D.J.H ([email protected]). Running title: histone modification and gene expression network Keywords: histone modification, gene expression, Bayesian network, causal relationship, epigenetics 1 Downloaded from genome.cshlp.org on September 28, 2021 - Published by Cold Spring Harbor Laboratory Press Abstract Histone modifications are major epigenetic factors regulating gene expression. They play important roles in maintaining stem cell pluripotency and in cancer pathogenesis. Different modifications may combine to form complex ‘histone codes’. Recent high throughput technologies, such as ‘ChIP-chip’ and ‘ChIP-seq’, have generated high resolution maps for many histone modifications on the human genome. Here we use these maps to build a Bayesian network to infer causal and combinatorial relationships among histone modifications and gene expression. A pilot network derived by the same method among polycomb group (PcG) genes and H3K27 trimethylation is accurately supported by current literature. Our unbiased network model among histone modifications is also well supported by cross validation results. It not only confirmed already known relationships, such as those of H3K27me3 to gene silencing, H3K4me3 to gene activation, and the effect of bivalent modification of both H3K4me3 and H3K27me3, but also identified many other relationships that may predict new epigenetic interactions important in epigenetic gene regulation. -

PCAF-Dependent Epigenetic Changes Promote Axonal Regeneration in the Central Nervous System
ARTICLE Received 13 Dec 2013 | Accepted 27 Feb 2014 | Published 1 Apr 2014 DOI: 10.1038/ncomms4527 PCAF-dependent epigenetic changes promote axonal regeneration in the central nervous system Radhika Puttagunta1,*, Andrea Tedeschi2,*, Marilia Grando So´ria1,3, Arnau Hervera1,4, Ricco Lindner1,3, Khizr I. Rathore1, Perrine Gaub1,3, Yashashree Joshi1,3,5, Tuan Nguyen1, Antonio Schmandke1, Claudia J. Laskowski2, Anne-Laurence Boutillier6, Frank Bradke2 & Simone Di Giovanni1,4 Axonal regenerative failure is a major cause of neurological impairment following central nervous system (CNS) but not peripheral nervous system (PNS) injury. Notably, PNS injury triggers a coordinated regenerative gene expression programme. However, the molecular link between retrograde signalling and the regulation of this gene expression programme that leads to the differential regenerative capacity remains elusive. Here we show through systematic epigenetic studies that the histone acetyltransferase p300/CBP-associated factor (PCAF) promotes acetylation of histone 3 Lys 9 at the promoters of established key regeneration-associated genes following a peripheral but not a central axonal injury. Furthermore, we find that extracellular signal-regulated kinase (ERK)-mediated retrograde signalling is required for PCAF-dependent regenerative gene reprogramming. Finally, PCAF is necessary for conditioning-dependent axonal regeneration and also singularly promotes regeneration after spinal cord injury. Thus, we find a specific epigenetic mechanism that regulates axonal regeneration of CNS axons, suggesting novel targets for clinical application. 1 Laboratory for NeuroRegeneration and Repair, Center for Neurology, Hertie Institute for Clinical Brain Research, University of Tu¨bingen, 72076 Tu¨bingen, Germany. 2 Department of Axonal Growth and Regeneration, German Center for Neurodegenerative Disease, 53175 Bonn, Germany. -
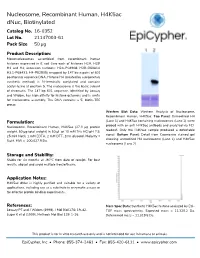
16-0352 Technical Data Sheet
Nucleosome, Recombinant Human, H4K5ac dNuc, Biotinylated Catalog No. 16-0352 Lot No. 21147003-61 Pack Size 50 µg Product Description: Mononucleosomes assembled from recombinant human histones expressed in E. coli (two each of histones H2A, H2B, H3 and H4; accession numbers: H2A-P04908; H2B-O60814; H3.1-P68431; H4-P62805) wrapped by 147 base pairs of 601 positioning sequence DNA. Histone H4 (created by a proprietary synthetic method) is N-terminally acetylated and contains acetyl-lysine at position 5. The nucleosome is the basic subunit of chromatin. The 147 bp 601 sequence, identified by Lowary and Widom, has high affinity for histone octamers and is useful for nucleosome assembly. The DNA contains a 5’ biotin-TEG group. Western Blot Data: Western Analysis of Nucleosome, Recombinant Human, H4K5ac. Top Panel: Unmodified H4 Formulation: (Lane 1) and H4K5ac containing nucleosomes (Lane 2) were probed with an anti-H4K5ac antibody and analyzed via ECL Nucleosome, Recombinant Human, H4K5ac (27.3 µg protein readout. Only the H4K5ac sample produced a detectable weight, 50 µg total weight) in 50 µL of 10 mM Tris HCl pH 7.5, signal. Bottom Panel: Detail from Coomassie stained gel 25 mM NaCl, 1 mM EDTA, 2 mM DTT, 20% glycerol. Molarity = showing unmodified H4 nucleosome (Lane 1) and H4K5ac 5 μM. MW = 200,027.9 Da. nucleosome (Lane 2). Storage and Stability: Stable for six months at -80°C from date of receipt. For best results, aliquot and avoid multiple freeze/thaws. Application Notes: H4K5ac dNuc is highly purified and suitable for a variety of applications, including use as a substrate in enzymatic assays or for effector protein binding experiments. -

BMC Genomics Biomed Central
BMC Genomics BioMed Central Research article Open Access Determination of enriched histone modifications in non-genic portions of the human genome Jeffrey A Rosenfeld1,2,3, Zhibin Wang4, Dustin E Schones4, Keji Zhao4, Rob DeSalle3 and Michael Q Zhang*1 Address: 1Cold Spring Harbor Laboratory, Cold Spring Harbor, NY 11724 USA, 2Department of Biology, New York University, New York, NY USA, 3American Museum of Natural History, New York, NY USA and 4Laboratory of Molecular Immunology, National Heart, Lung and Blood Institute, NIH, Bethesda, MD USA Email: Jeffrey A Rosenfeld - [email protected]; Zhibin Wang - [email protected]; Dustin E Schones - [email protected]; Keji Zhao - [email protected]; Rob DeSalle - [email protected]; Michael Q Zhang* - [email protected] * Corresponding author Published: 31 March 2009 Received: 8 September 2008 Accepted: 31 March 2009 BMC Genomics 2009, 10:143 doi:10.1186/1471-2164-10-143 This article is available from: http://www.biomedcentral.com/1471-2164/10/143 © 2009 Rosenfeld et al; licensee BioMed Central Ltd. This is an Open Access article distributed under the terms of the Creative Commons Attribution License (http://creativecommons.org/licenses/by/2.0), which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited. Abstract Background: Chromatin immunoprecipitation followed by high-throughput sequencing (ChIP- seq) has recently been used to identify the modification patterns for the methylation and acetylation of many different histone tails in genes and enhancers. Results: We have extended the analysis of histone modifications to gene deserts, pericentromeres and subtelomeres. Using data from human CD4+ T cells, we have found that each of these non- genic regions has a particular profile of histone modifications that distinguish it from the other non- coding regions. -

Screening HDAC Inhibitors
APPLICATION NOTE Cellular Imaging and Analysis Key Features • Identify candidate compounds using high throughput biochemical AlphaLISA® assays • Validate candidates in a high content imaging approach HDAC inhibitor Screening HDAC Inhibitors – A Workflow Introduction Comprising High An epigenetic trait is a stably inherited phenotype resulting from changes in a Throughput and High chromosome without alterations in the Content Screening DNA sequence [Berger et al., 2009]. Key mechanisms of epigenetic gene regulation are pathways which affect the packaging of DNA into chromatin, thereby determining the accessibility of DNA to transcription. These pathways include DNA methylation, chromatin remodeling and histone modifications. Aberrations in epigenetic mechanisms are well known to be associated with the biology of cancer, which suggests that epigenetic enzymes may be promising cancer drug targets [Ducasse and Brown, 2006]. In comparison to normal cells, cancer cell genomes are characterized by, among other things, a decrease in histone modifications such as acetylation [Ropero and Esteller, 2007]. Histone acetylation by histone acetyltransferases leads to loosening of DNA-histone interactions, allowing gene expression. In contrast, histone deacetylation by histone deacetylases (HDACs) increases the interaction between DNA and histones and leads to a decrease in gene expression (Figure 1). To perform the AlphaLISA assay, all steps were performed as previously described [Rodriguez-Suarez et al., 2011]. Briefly, HDAC-1 was pre-incubated with different concentrations of the HDAC inhibitor TSA, or Assay Buffer alone, for 5 min at room temperature, before addition of the H3K9ac peptide (AnaSpec, 64361). After 1h of enzymatic reaction time, AlphaLISA Acceptor Beads (PerkinElmer, AL138C) were added and the reaction mix was incubated for 1h, followed by addition of Streptavidin Figure 1: DNA accessibility is regulated by acetylation of core histones. -

Nucleosome Eviction Along with H3k9ac Deposition Enhances Sox2 Binding During Human Neuroectodermal Commitment
Cell Death and Differentiation (2017) 24, 1121–1131 OPEN Official journal of the Cell Death Differentiation Association www.nature.com/cdd Nucleosome eviction along with H3K9ac deposition enhances Sox2 binding during human neuroectodermal commitment Yanhua Du1,2, Zhenping Liu2, Xinkai Cao2, Xiaolong Chen2, Zhenyu Chen3, Xiaobai Zhang2, Xiaoqing Zhang*,1,3 and Cizhong Jiang*,1,2 Neuroectoderm is an important neural precursor. However, chromatin remodeling and its epigenetic regulatory roles during the differentiation of human neuroectodermal cells (hNECs) from human embryonic stem cells (hESCs) remain largely unexplored. Here, we obtained hNECs through directed differentiation from hESCs, and determined chromatin states in the two cell types. Upon differentiation, H2A.Z-mediated nucleosome depletion leads to an open chromatin structure in promoters and upregulates expression of neuroectodermal genes. Increase in H3K9ac signals and decrease in H3K27me3 signals in promoters result in an active chromatin state and activate neuroectodermal genes. Conversely, decrease in H3K9ac signals and increase in H3K27me3 signals in promoters repress pluripotency genes. Moreover, H3K9ac signals facilitate the pluripotency factor Sox2 binding to target sites unique to hNECs. Knockdown of the acetyltransferase Kat2b erases H3K9ac signals, disrupts Sox2 binding, and fails the differentiation. Our results demonstrate a hierarchy of epigenetic regulation of gene expression during the differentiation of hNECs from hESCs through chromatin remodeling. Cell Death and Differentiation (2017) 24, 1121–1131; doi:10.1038/cdd.2017.62; published online 5 May 2017 Chromatin remodeling offers the epigenetic basis for tran- that H3K4me3 and H3K27me3 effectively distinguish genes scriptional regulation and has a pivotal role in many biological with different expression levels and reflect lineage potential.11 A processes such as cell differentiation, embryonic develop- recent HPLC-MS-based quantitative proteomics identified ment, and so on. -

Histone Methylation Regulation in Neurodegenerative Disorders
International Journal of Molecular Sciences Review Histone Methylation Regulation in Neurodegenerative Disorders Balapal S. Basavarajappa 1,2,3,4,* and Shivakumar Subbanna 1 1 Division of Analytical Psychopharmacology, Nathan Kline Institute for Psychiatric Research, Orangeburg, NY 10962, USA; [email protected] 2 New York State Psychiatric Institute, New York, NY 10032, USA 3 Department of Psychiatry, College of Physicians & Surgeons, Columbia University, New York, NY 10032, USA 4 New York University Langone Medical Center, Department of Psychiatry, New York, NY 10016, USA * Correspondence: [email protected]; Tel.: +1-845-398-3234; Fax: +1-845-398-5451 Abstract: Advances achieved with molecular biology and genomics technologies have permitted investigators to discover epigenetic mechanisms, such as DNA methylation and histone posttransla- tional modifications, which are critical for gene expression in almost all tissues and in brain health and disease. These advances have influenced much interest in understanding the dysregulation of epigenetic mechanisms in neurodegenerative disorders. Although these disorders diverge in their fundamental causes and pathophysiology, several involve the dysregulation of histone methylation- mediated gene expression. Interestingly, epigenetic remodeling via histone methylation in specific brain regions has been suggested to play a critical function in the neurobiology of psychiatric disor- ders, including that related to neurodegenerative diseases. Prominently, epigenetic dysregulation currently brings considerable interest as an essential player in neurodegenerative disorders, such as Alzheimer’s disease (AD), Parkinson’s disease (PD), Huntington’s disease (HD), Amyotrophic lateral sclerosis (ALS) and drugs of abuse, including alcohol abuse disorder, where it may facilitate connections between genetic and environmental risk factors or directly influence disease-specific Citation: Basavarajappa, B.S.; Subbanna, S. -

Stepwise Histone Modifications Are Mediated by Multiple Enzymes That
ARTICLE Received 4 Apr 2013 | Accepted 29 Oct 2013 | Published 26 Nov 2013 DOI: 10.1038/ncomms3841 Stepwise histone modifications are mediated by multiple enzymes that rapidly associate with nascent DNA during replication Svetlana Petruk1, Kathryn L. Black1, Sina K. Kovermann2, Hugh W. Brock2 & Alexander Mazo1 The mechanism of epigenetic inheritance following DNA replication may involve dissociation of chromosomal proteins from parental DNA and reassembly on daughter strands in a specific order. Here we investigated the behaviour of different types of chromosomal proteins using newly developed methods that allow assessment of the assembly of proteins during DNA replication. Unexpectedly, most chromatin-modifying proteins tested, including methylases, demethylases, acetyltransferases and a deacetylase, are found in close proximity to PCNA or associate with short nascent DNA. Histone modifications occur in a temporal order following DNA replication, mediated by complex activities of different enzymes. In contrast, components of several major nucleosome-remodelling complexes are dissociated from parental DNA, and are later recruited to nascent DNA following replication. Epigenetic inheritance of gene expression patterns may require many aspects of chromatin structure to remain in close proximity to the replication complex followed by reassembly on nascent DNA shortly after replication. 1 Department of Biochemistry and Molecular Biology and Kimmel Cancer Center, Thomas Jefferson University, 1020 Locust Street, Philadelphia, Pennsylvania 19107, USA. 2 Department of Zoology, University of British Columbia, 6270 University Boulevard, Vancouver, British Columbia, Canada V6T 1Z4. Correspondence and requests for materials should be addressed to A.M. (email: [email protected]). NATURE COMMUNICATIONS | 4:2841 | DOI: 10.1038/ncomms3841 | www.nature.com/naturecommunications 1 & 2013 Macmillan Publishers Limited. -

New Insights Into the Role of Histone Changes in Aging
International Journal of Molecular Sciences Review New Insights into the Role of Histone Changes in Aging Sun-Ju Yi and Kyunghwan Kim * Department of Biology, School of Biological Sciences, College of Natural Sciences, Chungbuk National University, Cheongju 28644, Chungbuk, Korea; [email protected] * Correspondence: [email protected]; Tel.: +82-(43)-2612292 Received: 14 October 2020; Accepted: 2 November 2020; Published: 3 November 2020 Abstract: Aging is the progressive decline or loss of function at the cellular, tissue, and organismal levels that ultimately leads to death. A number of external and internal factors, including diet, exercise, metabolic dysfunction, genome instability, and epigenetic imbalance, affect the lifespan of an organism. These aging factors regulate transcriptome changes related to the aging process through chromatin remodeling. Many epigenetic regulators, such as histone modification, histone variants, and ATP-dependent chromatin remodeling factors, play roles in chromatin reorganization. The key to understanding the role of gene regulatory networks in aging lies in characterizing the epigenetic regulators responsible for reorganizing and potentiating particular chromatin structures. This review covers epigenetic studies on aging, discusses the impact of epigenetic modifications on gene expression, and provides future directions in this area. Keywords: aging; histone level; histone modification; histone variant; chromatin remodeling; epigenetics 1. Introduction An individual organism undergoes a series of developmental stages, including birth, growth, maturity, aging, and death. Aging is the gradual and continuous decline or loss of function at the cellular, tissue, and organismal levels with the passage of time. Aging is considered to begin in early adulthood, but is regarded as an integral part of life since other stages also affect the aging process [1]. -

Global Histone Modifications in Breast Cancer Correlate with Tumor Phenotypes, Prognostic Factors, and Patient Outcome
Published OnlineFirst April 14, 2009; DOI: 10.1158/0008-5472.CAN-08-3907 Research Article Global Histone Modifications in Breast Cancer Correlate with Tumor Phenotypes, Prognostic Factors, and Patient Outcome Somaia E. Elsheikh,1,7 Andrew R. Green,1 Emad A. Rakha,1 Des G. Powe,1 Rabab A. Ahmed,1,8 Hilary M. Collins,2 Daniele Soria,3 Jonathan M. Garibaldi,3 Claire E. Paish,1 Amr A. Ammar,7 Matthew J. Grainge,4 Graham R. Ball,6 Magdy K. Abdelghany,2,9 Luisa Martinez-Pomares,5 David M. Heery,2 and Ian O. Ellis1 1Department of Histopathology, School of Molecular Medical Sciences, University of Nottingham and Nottingham Universities Hospital Trust, Schools of 2Pharmacy and 3Computer Science, 4Division of Epidemiology and Public Health, and 5School of Molecular Medical Sciences, Institute of Infection, Immunity and Inflammation, University of Nottingham; 6Division of Life Sciences, Nottingham Trent University, Nottingham, United Kingdom; 7Department of Pathology, Faculty of Medicine, Menoufyia University, Menoufyia, Egypt; 8Department of Pathology, Faculty of Medicine, Asuit University, Asuit, Egypt; and 9Department of Pathology, Faculty of Medicine, Suez Canal University, Ismailia, Egypt Abstract Introduction Post-translational histone modifications are known to be Breast cancer is a heterogeneous disease ranging from altered in cancer cells, and loss of selected histone acetylation premalignant hyperproliferation to invasive and metastatic carci- and methylation marks has recently been shown to predict nomas (1). Disease progression is poorly understood but is likely patient outcome in human carcinoma. Immunohistochemistry due to the accumulation of genetic mutations leading to was used to detect a series of histone lysine acetylation widespread changes in gene expression and, in particular, affecting (H3K9ac, H3K18ac, H4K12ac, and H4K16ac), lysine methyla- the expression of tumor suppressors and oncogenes (2).