Operating Systems Security – Assignment 6 Version 1.0.0 – 2015/2016
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Configuring UNIX-Specific Settings: Creating Symbolic Links : Snap
Configuring UNIX-specific settings: Creating symbolic links Snap Creator Framework NetApp September 23, 2021 This PDF was generated from https://docs.netapp.com/us-en/snap-creator- framework/installation/task_creating_symbolic_links_for_domino_plug_in_on_linux_and_solaris_hosts.ht ml on September 23, 2021. Always check docs.netapp.com for the latest. Table of Contents Configuring UNIX-specific settings: Creating symbolic links . 1 Creating symbolic links for the Domino plug-in on Linux and Solaris hosts. 1 Creating symbolic links for the Domino plug-in on AIX hosts. 2 Configuring UNIX-specific settings: Creating symbolic links If you are going to install the Snap Creator Agent on a UNIX operating system (AIX, Linux, and Solaris), for the IBM Domino plug-in to work properly, three symbolic links (symlinks) must be created to link to Domino’s shared object files. Installation procedures vary slightly depending on the operating system. Refer to the appropriate procedure for your operating system. Domino does not support the HP-UX operating system. Creating symbolic links for the Domino plug-in on Linux and Solaris hosts You need to perform this procedure if you want to create symbolic links for the Domino plug-in on Linux and Solaris hosts. You should not copy and paste commands directly from this document; errors (such as incorrectly transferred characters caused by line breaks and hard returns) might result. Copy and paste the commands into a text editor, verify the commands, and then enter them in the CLI console. The paths provided in the following steps refer to the 32-bit systems; 64-bit systems must create simlinks to /usr/lib64 instead of /usr/lib. -

Making Linux Protection Mechanisms Egalitarian with Userfs
Making Linux Protection Mechanisms Egalitarian with UserFS Taesoo Kim and Nickolai Zeldovich MIT CSAIL ABSTRACT firewall rules, forcing applications to invent their own UserFS provides egalitarian OS protection mechanisms protection techniques like system call interposition [15], in Linux. UserFS allows any user—not just the system binary rewriting [30] or analysis [13, 45], or interposing administrator—to allocate Unix user IDs, to use chroot, on system accesses in a language runtime like Javascript. and to set up firewall rules in order to confine untrusted This paper presents the design of UserFS, a kernel code. One key idea in UserFS is representing user IDs as framework that allows any application to use traditional files in a /proc-like file system, thus allowing applica- OS protection mechanisms on a Unix system, and a proto- tions to manage user IDs like any other files, by setting type implementation of UserFS for Linux. UserFS makes permissions and passing file descriptors over Unix do- protection mechanisms egalitarian, so that any user—not main sockets. UserFS addresses several challenges in just the system administrator—can allocate new user IDs, making user IDs egalitarian, including accountability, re- set up firewall rules, and isolate processes using chroot. source allocation, persistence, and UID reuse. We have By using the operating system’s own protection mecha- ported several applications to take advantage of UserFS; nisms, applications can avoid race conditions and ambi- by changing just tens to hundreds of lines of code, we guities associated with system call interposition [14, 43], prevented attackers from exploiting application-level vul- can confine existing code without having to recompile or nerabilities, such as code injection or missing ACL checks rewrite it in a new language, and can enforce a coherent in a PHP-based wiki application. -

Sandboxing 2 Change Root: Chroot()
Sandboxing 2 Change Root: chroot() Oldest Unix isolation mechanism Make a process believe that some subtree is the entire file system File outside of this subtree simply don’t exist Sounds good, but. Sandboxing 2 2 / 47 Chroot Sandboxing 2 3 / 47 Limitations of Chroot Only root can invoke it. (Why?) Setting up minimum necessary environment can be painful The program to execute generally needs to live within the subtree, where it’s exposed Still vulnerable to root compromise Doesn’t protect network identity Sandboxing 2 4 / 47 Root versus Chroot Suppose an ordinary user could use chroot() Create a link to the sudo command Create /etc and /etc/passwd with a known root password Create links to any files you want to read or write Besides, root can escape from chroot() Sandboxing 2 5 / 47 Escaping Chroot What is the current directory? If it’s not under the chroot() tree, try chdir("../../..") Better escape: create device files On Unix, all (non-network) devices have filenames Even physical memory has a filename Create a physical memory device, open it, and change the kernel data structures to remove the restriction Create a disk device, and mount a file system on it. Then chroot() to the real root (On Unix systems, disks other than the root file system are “mounted” as a subtree somewhere) Sandboxing 2 6 / 47 Trying Chroot # mkdir /usr/sandbox /usr/sandbox/bin # cp /bin/sh /usr/sandbox/bin/sh # chroot /usr/sandbox /bin/sh chroot: /bin/sh: Exec format error # mkdir /usr/sandbox/libexec # cp /libexec/ld.elf_so /usr/sandbox/libexec # chroot /usr/sandbox -

Installation Guide LS Nav 2018 (11.0) Contents
LS Nav 2018 (11.0) Installation Guide © 2018 LS Retail ehf. All rights reserved. All trademarks belong to their respective holders. ii Installation Guide LS Nav 2018 (11.0) Contents Contents Installation Guide LS Nav 1 Files in This Version 1 LS Nav Setup File 1 Demonstration Database Backup 1 Documentation 1 Objects 2 Objects \ Uninstall 2 Objects \ Upgrade 2 Objects \ Auto Test 2 Online Help 2 Setup \ LS Nav Rapid Installer 2 Setup \ LS Nav Rapid Start 2 Setup \ LS Nav Toolbox 2 Setup \ LS Printing Station 2 Setup 2 Installation 2 Prerequisites 2 Microsoft Dynamics NAV Application Objects Added or Modified by LS Nav 3 Installing LS Nav in a New Database 4 Installing LS Nav in an Existing Database 4 Uninstall 5 Uninstall the LS Nav xx.x Client Components 5 Uninstall the LS Nav xx.x Service Components 5 Uninstall LS Nav from a Microsoft Dynamics NAV Database 5 Database Compilation 6 System Requirements 6 Security Hardening Guide for LS Nav 7 Clear Data Tables That Are Not Included in the Customer’s License 7 Online Help Installation 7 Installation Guide LS Nav 2018 (11.0) iii Contents Local Setup 8 Remote Setup 8 Older Documents 9 Toolbox Installation 10 See Also 10 Installing the Toolbox 10 Client Components Installer 11 Service Components Installer 12 Install Options (Silent Install) 13 Installing Into a Database (Control Add-Ins Table) 14 Web POS Installation 16 See Also (topics in LS Nav Online Help) 17 Installing Microsoft Dynamics NAV for Web POS 17 Importing Control Add-in for Web POS 17 Web POS in Full-Screen Mode 18 LS Nav Auto Tests 18 Prerequisites 18 Installation 19 Objects needed 19 Running 19 1. -

Getty Scholars' Workspace™ INSTALLATION INSTRUCTIONS
Getty Scholars’ Workspace™ INSTALLATION INSTRUCTIONS This document outlines methods to run the application locally on your personal computer or to do a full installation on a web server. Test Drive with Docker Getty Scholars' Workspace is a multi-tenant web application, so it is intended to be run on a web server. However, if you'd like to run it on your personal computer just to give it a test drive, you can use Docker to create a virtual server environment and run the Workspace locally. Follow the steps below to give it a spin. Scroll further for real deployment instructions. 1. Install Docker on your machine. Follow instructions on the Docker website: https://www.docker.com/ 2. If you are using Docker Machine (Mac or Windows), be sure to start it by using the Docker Quickstart Terminal. Docker is configured to use the default machine with IP 192.168.99.100. 3. At the command line, pull the Getty Scholars' Workspace image. $ docker pull thegetty/scholarsworkspace 4. Run the container. $ docker run -d -p 8080:80 --name=wkspc thegetty/scholarsworkspace supervisord -n 5. Point your browser to `<ip address>:8080/GettyScholarsWorkspace`. Use the IP address noted in Step 2. 6. The Drupal administrator login is `scholar` and the password is `workspace`. Be sure to change these in the Drupal admin interface. 7. To shut it down, stop the container: $ docker stop wkspc Web Server Installation These installation instructions assume you are installing Getty Scholars' Workspace on a server (virtual or physical) with a clean new instance of Ubuntu 14.04 as the operating system. -

The Linux Command Line
The Linux Command Line Fifth Internet Edition William Shotts A LinuxCommand.org Book Copyright ©2008-2019, William E. Shotts, Jr. This work is licensed under the Creative Commons Attribution-Noncommercial-No De- rivative Works 3.0 United States License. To view a copy of this license, visit the link above or send a letter to Creative Commons, PO Box 1866, Mountain View, CA 94042. A version of this book is also available in printed form, published by No Starch Press. Copies may be purchased wherever fine books are sold. No Starch Press also offers elec- tronic formats for popular e-readers. They can be reached at: https://www.nostarch.com. Linux® is the registered trademark of Linus Torvalds. All other trademarks belong to their respective owners. This book is part of the LinuxCommand.org project, a site for Linux education and advo- cacy devoted to helping users of legacy operating systems migrate into the future. You may contact the LinuxCommand.org project at http://linuxcommand.org. Release History Version Date Description 19.01A January 28, 2019 Fifth Internet Edition (Corrected TOC) 19.01 January 17, 2019 Fifth Internet Edition. 17.10 October 19, 2017 Fourth Internet Edition. 16.07 July 28, 2016 Third Internet Edition. 13.07 July 6, 2013 Second Internet Edition. 09.12 December 14, 2009 First Internet Edition. Table of Contents Introduction....................................................................................................xvi Why Use the Command Line?......................................................................................xvi -

After Upgrade and Reboot with Install Configuration Set to Yes, the BIG-IP
K33233632: After upgrade and reboot with Install Configuration set to Yes, the BIG-IP appears to have hung or lost all configuration and mcpd, gtmd, named and others are in a restart loop Support Solution Original Publication Date: Jan 28, 2020 Update Date: Mar 25, 2021 Details Description After you upgrade the BIG-IP system to BIG-IP 14.1.2 and later, certain daemons (e.g. mcpd, gtmd, and named) may be in a restart loop and the BIG-IP appears to have hung or lost all configuration. Additionally, the device may exhibit the following symptoms: You observe error messages similar to the following in /var/log/ltm (below is an example of an mcpd restart loop): err mcpd[8710]: 01070734:3: Configuration error: MCPProcessor::initializeDB: can't chmod for directory (/config/filestore/files_d/<directory_names>) err (Permission denied). err mcpd[8710]: 01070596:3: An unexpected failure has occurred, can't chmod for directory (/config /filestore/files_d/<directory_names>) err (Permission denied). - sys/validation/FileObject.cpp, line 612, exiting... You observe error messages similar to the following in /var/log/ltm: 01420006:3: Loading configuration process failed. You observe error messages similar to the following in /var/log/auditd/audit.log (below is an example for an mcpd restart loop): Note: The message contains denied and unlabeled_t shown in bold below. type=AVC msg=audit(day_time): avc: denied { setattr } for pid=13624 comm="mcpd" name=" external_monitor_d" dev="dm-11" ino=307 scontext=system_u:system_r:mcpd_t:s0 tcontext=system_u:object_r:unlabeled_t:s0 tclass=dir The Configuration utility displays the following: The configuration has not yet loaded. -
Install and Run External Command Line Softwares
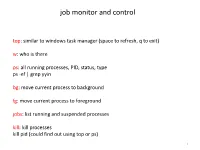
job monitor and control top: similar to windows task manager (space to refresh, q to exit) w: who is there ps: all running processes, PID, status, type ps -ef | grep yyin bg: move current process to background fg: move current process to foreground jobs: list running and suspended processes kill: kill processes kill pid (could find out using top or ps) 1 sort, cut, uniq, join, paste, sed, grep, awk, wc, diff, comm, cat All types of bioinformatics sequence analyses are essentially text processing. Unix Shell has the above commands that are very useful for processing texts and also allows the output from one command to be passed to another command as input using pipe (“|”). less cosmicRaw.txt | cut -f2,3,4,5,8,13 | awk '$5==22' | cut -f1 | sort -u | wc This makes the processing of files using Shell very convenient and very powerful: you do not need to write output to intermediate files or load all data into the memory. For example, combining different Unix commands for text processing is like passing an item through a manufacturing pipeline when you only care about the final product 2 Hands on example 1: cosmic mutation data - Go to UCSC genome browser website: http://genome.ucsc.edu/ - On the left, find the Downloads link - Click on Human - Click on Annotation database - Ctrl+f and then search “cosmic” - On “cosmic.txt.gz” right-click -> copy link address - Go to the terminal and wget the above link (middle click or Shift+Insert to paste what you copied) - Similarly, download the “cosmicRaw.txt.gz” file - Under your home, create a folder -

Install Guide - UNIX Oracle CSE
Information Engineering Technology Install Guide - UNIX Oracle CSE Release 8.7.3 © Information Engineering Technology Ltd 2020 www.iet.uk Table Of Contents Introduction ............................................................................................................................................................................... 3 Architecture .................................................................................................................................................................................... 3 Communications ............................................................................................................................................................................. 3 About The Installation Guides .................................................................................................................................................... 4 Software for Download .............................................................................................................................................................. 4 Server Install – UNIX / Oracle CSE ............................................................................................................................................... 5 Pre-Requisites ................................................................................................................................................................................. 5 Who Should Perform this Installation? .......................................................................................................................................... -

Ubuntu Server Guide Basic Installation Preparing to Install
Ubuntu Server Guide Welcome to the Ubuntu Server Guide! This site includes information on using Ubuntu Server for the latest LTS release, Ubuntu 20.04 LTS (Focal Fossa). For an offline version as well as versions for previous releases see below. Improving the Documentation If you find any errors or have suggestions for improvements to pages, please use the link at thebottomof each topic titled: “Help improve this document in the forum.” This link will take you to the Server Discourse forum for the specific page you are viewing. There you can share your comments or let us know aboutbugs with any page. PDFs and Previous Releases Below are links to the previous Ubuntu Server release server guides as well as an offline copy of the current version of this site: Ubuntu 20.04 LTS (Focal Fossa): PDF Ubuntu 18.04 LTS (Bionic Beaver): Web and PDF Ubuntu 16.04 LTS (Xenial Xerus): Web and PDF Support There are a couple of different ways that the Ubuntu Server edition is supported: commercial support and community support. The main commercial support (and development funding) is available from Canonical, Ltd. They supply reasonably- priced support contracts on a per desktop or per-server basis. For more information see the Ubuntu Advantage page. Community support is also provided by dedicated individuals and companies that wish to make Ubuntu the best distribution possible. Support is provided through multiple mailing lists, IRC channels, forums, blogs, wikis, etc. The large amount of information available can be overwhelming, but a good search engine query can usually provide an answer to your questions. -
SUSE Linux Enterprise Server 12 Does Not Provide the Repair System Anymore
General System Troubleshooting Sascha Wehnert Premium Service Engineer Attachmate Group Germany GmbH [email protected] What is this about? • This session will cover the following topics: ‒ How to speed up a service request ‒ How to gather system information using supportconfig ‒ Configure serial console in grub to trace kernel boot messages ‒ Accessing a non booting systems using the rescue system ‒ System crash situations and how to prepare (i586/x86_64 only) 2 The challenge of a service request • Complete service request description: “We need to increase our disk space.” 3 The challenge of a service request • Which SUSE® Linux Enterprise Server version? • Is this a physical or virtual environment? • If virtual, what virtualization solution is being used? • If physical, local SCSI RAID array? What hardware? • If using HBAs, dm-multipathing or iSCSI connected disks or a 3rd party solution? • Disk and system partition layout? • What has been done so far? What was achieved? What failed? • What information do I need in order to help? 4 What information would be needed? • SUSE Linux Enterprise Server version → /etc/SuSE-release, uname -a • Physical → dmidecode XEN → /proc/xen/xsd_port KVM → /proc/modules • Hardware information → hwinfo • Partition information → parted -l, /etc/fstab • Multipathing/iSCSI → multipath, iscsiadm • Console output or /var/log/YaST2/y2log in case YaST2 has been used 5 supportconfig • Since SUSE Linux Enterprise Server 10 SP4 included in default installation. • Maintained package, updates available via patch channels. For best results always have latest version installed from channels installed. • One single command to get (almost) everything. • Splits data into files separated by topic. • Can be modified to exclude certain data, either via /etc/supportconfig.conf or command options. -
REV OBSERVER for UNIX/LINUX
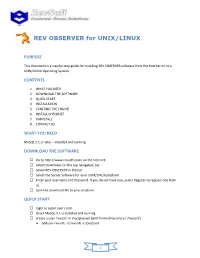
REV OBSERVER for UNIX/LINUX PURPOSE This document is a step by step guide for installing REV OBSERVER software from the Internet on to a UNIX/LINUX Operating System. CONTENTS 1. WHAT YOU NEED 2. DOWNLOAD THE SOFTWARE 3. QUICK START 4. INSTALLATION 5. STARTING THE ENGINE 6. INSTALL CHECKLIST 7. UNINSTALL 8. CONTACT US WHAT YOU NEED MySQL 5.1 or later – installed and running. DOWNLOAD THE SOFTWARE Go to http://www.revsoft.com/ on the Internet. Select Downloads on the top navigation bar. Select REV OBSERVER in the list. Select the Server Software for your UNIX/LINUX platform. Enter your Username and Password. If you do not have one, select Register to request one from us. Save the download file to your machine. QUICK START login as super user / root check MySQL 5.1 is installed and running create a user 'revsoft' in /etc/passwd (with home directory as '/revsoft') adduser revsoft -d /revsoft -s /bin/bash 1 unpack the install file: gunzip RevSoft-Observer-Engine-ENTXXX-XXX.tar.gz tar xvf RevSoft-Observer-Engine-ENTXXX-XXX.tar run the checklist: ./roinstall checklist install the product: ./roinstall now login as user 'revsoft' start REV OBSERVER cd /revsoft/Observer/Engine ./roengine start INSTALLATION Login as super user / root Add a new user revsoft to the local password file using: adduser revsoft -d /revsoft -s /bin/bash Create a new folder using this command: mkdir /revsoft Create a temporary folder using this command: mkdir /revsoft/temp Copy or move the downloaded file to the temporary folder: cp RevSoft-Observer-Engine-ENTXXX-XXX.tar.gz