Technical Limitations for Designing Applications for Social Media
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

What Is Dart?
1 Dart in Action By Chris Buckett As a language on its own, Dart might be just another language, but when you take into account the whole Dart ecosystem, Dart represents an exciting prospect in the world of web development. In this green paper based on Dart in Action, author Chris Buckett explains how Dart, with its ability to either run natively or be converted to JavaScript and coupled with HTML5 is an ideal solution for building web applications that do not need external plugins to provide all the features. You may also be interested in… What is Dart? The quick answer to the question of what Dart is that it is an open-source structured programming language for creating complex browser based web applications. You can run applications created in Dart by either using a browser that directly supports Dart code, or by converting your Dart code to JavaScript (which happens seamlessly). It is class based, optionally typed, and single threaded (but supports multiple threads through a mechanism called isolates) and has a familiar syntax. In addition to running in browsers, you can also run Dart code on the server, hosted in the Dart virtual machine. The language itself is very similar to Java, C#, and JavaScript. One of the primary goals of the Dart developers is that the language seems familiar. This is a tiny dart script: main() { #A var d = “Dart”; #B String w = “World”; #C print(“Hello ${d} ${w}”); #D } #A Single entry point function main() executes when the script is fully loaded #B Optional typing (no type specified) #C Static typing (String type specified) #D Outputs “Hello Dart World” to the browser console or stdout This script can be embedded within <script type=“application/dart”> tags and run in the Dartium experimental browser, converted to JavaScript using the Frog tool and run in all modern browsers, or saved to a .dart file and run directly on the server using the dart virtual machine executable. -

TIBCO Activematrix® BPM Web Client Developer's Guide Software Release 4.3 April 2019 2
TIBCO ActiveMatrix® BPM Web Client Developer's Guide Software Release 4.3 April 2019 2 Important Information SOME TIBCO SOFTWARE EMBEDS OR BUNDLES OTHER TIBCO SOFTWARE. USE OF SUCH EMBEDDED OR BUNDLED TIBCO SOFTWARE IS SOLELY TO ENABLE THE FUNCTIONALITY (OR PROVIDE LIMITED ADD-ON FUNCTIONALITY) OF THE LICENSED TIBCO SOFTWARE. THE EMBEDDED OR BUNDLED SOFTWARE IS NOT LICENSED TO BE USED OR ACCESSED BY ANY OTHER TIBCO SOFTWARE OR FOR ANY OTHER PURPOSE. USE OF TIBCO SOFTWARE AND THIS DOCUMENT IS SUBJECT TO THE TERMS AND CONDITIONS OF A LICENSE AGREEMENT FOUND IN EITHER A SEPARATELY EXECUTED SOFTWARE LICENSE AGREEMENT, OR, IF THERE IS NO SUCH SEPARATE AGREEMENT, THE CLICKWRAP END USER LICENSE AGREEMENT WHICH IS DISPLAYED DURING DOWNLOAD OR INSTALLATION OF THE SOFTWARE (AND WHICH IS DUPLICATED IN THE LICENSE FILE) OR IF THERE IS NO SUCH SOFTWARE LICENSE AGREEMENT OR CLICKWRAP END USER LICENSE AGREEMENT, THE LICENSE(S) LOCATED IN THE “LICENSE” FILE(S) OF THE SOFTWARE. USE OF THIS DOCUMENT IS SUBJECT TO THOSE TERMS AND CONDITIONS, AND YOUR USE HEREOF SHALL CONSTITUTE ACCEPTANCE OF AND AN AGREEMENT TO BE BOUND BY THE SAME. ANY SOFTWARE ITEM IDENTIFIED AS THIRD PARTY LIBRARY IS AVAILABLE UNDER SEPARATE SOFTWARE LICENSE TERMS AND IS NOT PART OF A TIBCO PRODUCT. AS SUCH, THESE SOFTWARE ITEMS ARE NOT COVERED BY THE TERMS OF YOUR AGREEMENT WITH TIBCO, INCLUDING ANY TERMS CONCERNING SUPPORT, MAINTENANCE, WARRANTIES, AND INDEMNITIES. DOWNLOAD AND USE OF THESE ITEMS IS SOLELY AT YOUR OWN DISCRETION AND SUBJECT TO THE LICENSE TERMS APPLICABLE TO THEM. BY PROCEEDING TO DOWNLOAD, INSTALL OR USE ANY OF THESE ITEMS, YOU ACKNOWLEDGE THE FOREGOING DISTINCTIONS BETWEEN THESE ITEMS AND TIBCO PRODUCTS. -
Attacking AJAX Web Applications Vulns 2.0 for Web 2.0
Attacking AJAX Web Applications Vulns 2.0 for Web 2.0 Alex Stamos Zane Lackey [email protected] [email protected] Blackhat Japan October 5, 2006 Information Security Partners, LLC iSECPartners.com Information Security Partners, LLC www.isecpartners.com Agenda • Introduction – Who are we? – Why care about AJAX? • How does AJAX change Web Attacks? • AJAX Background and Technologies • Attacks Against AJAX – Discovery and Method Manipulation – XSS – Cross-Site Request Forgery • Security of Popular Frameworks – Microsoft ATLAS – Google GWT –Java DWR • Q&A 2 Information Security Partners, LLC www.isecpartners.com Introduction • Who are we? – Consultants for iSEC Partners – Application security consultants and researchers – Based in San Francisco • Why listen to this talk? – New technologies are making web app security much more complicated • This is obvious to anybody who reads the paper – MySpace – Yahoo – Worming of XSS – Our Goals for what you should walk away with: • Basic understanding of AJAX and different AJAX technologies • Knowledge of how AJAX changes web attacks • In-depth knowledge on XSS and XSRF in AJAX • An opinion on whether you can trust your AJAX framework to “take care of security” 3 Information Security Partners, LLC www.isecpartners.com Shameless Plug Slide • Special Thanks to: – Scott Stender, Jesse Burns, and Brad Hill of iSEC Partners – Amit Klein and Jeremiah Grossman for doing great work in this area – Rich Cannings at Google • Books by iSECer Himanshu Dwivedi – Securing Storage – Hackers’ Challenge 3 • We are -

Cliente Twitter Con Compresión De Datos
PROYECTO FIN DE GRADO GRADO EN INGENIERÍA INFROMÁTICA CLIENTE TWITTER CON COMPRESIÓN DE DATOS Autor: Plácido Fernández Declara Tutores: Luis Miguel Sánchez García Rafael Sotomayor Fernández Colmenarejo, Febrero de 2013 RESUMEN La popular red social Twitter es usada hoy en día en diversos lugares y momentos, gracias también a las redes móviles que nos proporcionan conexión a internet en casi cualquier lugar. Twitter permite publicar y mandar mensajes cortos de texto plano con un máximo de 140 caracteres, así como la lectura de estos mensajes cortos de otros usuarios a los que podemos seguir para tal propósito. Hacer uso de este servicio en zonas con buena cobertura, o cuando usamos Wi-fi no supone generalmente ningún problema. Es cuando nos encontramos en zonas de poca cobertura cuando vemos problemas para hacer uso de este servicio, ya que las velocidades de descarga pueden disminuir hasta el punto de necesitar decenas de segundos para disponer de los mensajes cortos, los “Tweets”. A esto hay que añadir que los planes de datos actuales están limitados de alguna forma (al alcanzar un número de Mb), por lo que la cantidad de Mb usada es hoy también un factor importante. Para ello esta aplicación ofrece la experiencia de un cliente Twitter sencillo en el que consultar los “Tweets” de a quien seguimos, así como publicar “Tweets”, haciendo uso de un Proxy que comprime estos datos considerablemente de forma que se reducen los tiempos de descarga para las zonas de poca cobertura y además se reduce el número de Mb consumidos por el dispositivo móvil. Índice de contenido RESUMEN ................................................................................................................................. -
D2.2: Research Data Exchange Solution
H2020-ICT-2018-2 /ICT-28-2018-CSA SOMA: Social Observatory for Disinformation and Social Media Analysis D2.2: Research data exchange solution Project Reference No SOMA [825469] Deliverable D2.2: Research Data exchange (and transparency) solution with platforms Work package WP2: Methods and Analysis for disinformation modeling Type Report Dissemination Level Public Date 30/08/2019 Status Final Authors Lynge Asbjørn Møller, DATALAB, Aarhus University Anja Bechmann, DATALAB, Aarhus University Contributor(s) See fact-checking interviews and meetings in appendix 7.2 Reviewers Noemi Trino, LUISS Datalab, LUISS University Stefano Guarino, LUISS Datalab, LUISS University Document description This deliverable compiles the findings and recommended solutions and actions needed in order to construct a sustainable data exchange model for stakeholders, focusing on a differentiated perspective, one for journalists and the broader community, and one for university-based academic researchers. SOMA-825469 D2.2: Research data exchange solution Document Revision History Version Date Modifications Introduced Modification Reason Modified by v0.1 28/08/2019 Consolidation of first DATALAB, Aarhus draft University v0.2 29/08/2019 Review LUISS Datalab, LUISS University v0.3 30/08/2019 Proofread DATALAB, Aarhus University v1.0 30/08/2019 Final version DATALAB, Aarhus University 30/08/2019 Page | 1 SOMA-825469 D2.2: Research data exchange solution Executive Summary This report provides an evaluation of current solutions for data transparency and exchange with social media platforms, an account of the historic obstacles and developments within the subject and a prioritized list of future scenarios and solutions for data access with social media platforms. The evaluation of current solutions and the historic accounts are based primarily on a systematic review of academic literature on the subject, expanded by an account on the most recent developments and solutions. -
Towards Secure and Reusable Web Applications
Mashups and Modularity: Towards Secure and Reusable Web Applications Antero Taivalsaari Tommi Mikkonen Sun Microsystems Laboratories [email protected] http://research.sun.com/projects/lively 2 Evolution of the Web 1) Simple pages with text and static images only (e.g., http://www.google.com) 2) Animated pages with plug-ins (e.g., http://www.cadillac.com) 3) Rich Internet Applications (e.g., docs.google.com) What's Next? 3 Web Applications – Implications • Web-based software will dramatically change the way people develop, deploy and use software. • No more installations! > Applications will simply run off the Web. • No more upgrades! > Always run the latest application version. • Instant worldwide deployment! > No middlemen or distributors needed. • No CPU dependencies, OS dependencies, ... > The Web is the Platform. 4 Unfortunately... • The web browser was not designed for running real applications. > It was designed in the early 1990s for viewing documents, forms and other page-structured artifacts – not applications. > Programming capabilities on the web were an afterthought, not something inherent in the design of the browser. • Various Rich Internet Application (RIA) technologies have been introduced recently to retrofit application execution capabilities into the web browser. 5 Web Development vs. Conventional Software The Impedance Mismatch Web Development Conventional SW Development - Documents - Applications - Page / form oriented interaction - Direct manipulation - Managed graphics, static layout - Directly drawn, dynamic -

Letter, If Not the Spirit, of One Or the Other Definition
Producing Open Source Software How to Run a Successful Free Software Project Karl Fogel Producing Open Source Software: How to Run a Successful Free Software Project by Karl Fogel Copyright © 2005-2021 Karl Fogel, under the CreativeCommons Attribution-ShareAlike (4.0) license. Version: 2.3214 Home site: https://producingoss.com/ Dedication This book is dedicated to two dear friends without whom it would not have been possible: Karen Under- hill and Jim Blandy. i Table of Contents Preface ............................................................................................................................. vi Why Write This Book? ............................................................................................... vi Who Should Read This Book? ..................................................................................... vi Sources ................................................................................................................... vii Acknowledgements ................................................................................................... viii For the first edition (2005) ................................................................................ viii For the second edition (2021) .............................................................................. ix Disclaimer .............................................................................................................. xiii 1. Introduction ................................................................................................................... -

Diseño De Un Sistema De Monitorización De Dispositivos Móviles
Departamento de Informática PROYECTO FIN DE GRADO DISEÑO DE UN SISTEMA DE MONITORIZACIÓN DE DISPOSITIVOS MÓVILES Autor: Antonio Becerra López Tutor: Luis Miguel Sánchez García Colmenarejo, Septiembre de 2012 1 Diseño de un sistema de monitorización de dispositivos móviles Título: Diseño de un sistema de monitorización de dispositivos móviles Autor: Antonio Becerra López Director: EL TRIBUNAL Presidente: Vocal: Secretario: Realizado el acto de defensa y lectura del Proyecto Fin de Carrera el día __ de _______ de 20__ en Leganés, en la Escuela Politécnica Superior de la Universidad Carlos III de Madrid, acuerda otorgarle la CALIFICACIÓN de VOCAL SECRETARIO PRESIDENTE 1 2 Diseño de un sistema de monitorización de dispositivos móviles Resumen AndroidMonitor es un sistema cuya finalidad consiste en monitorizar distribuidamente dispositivos móviles con el sistema operativo Android. Los teléfonos móviles en la actualidad son un elemento indispensable más de las personas junto con las llaves de casa y la cartera con los documentos personales. En el año 2011, la población total de la Tierra superaba la asombrosa cantidad de siete mil millones de personas. En ese mismo año, se calculaba que el número de teléfonos móviles en el mundo era superior a los 5.600 millones. Los dispositivos móviles cuentan con gran variedad de sensores: acelerómetro, sensor de luz, sensor de temperatura, barómetro, sensor de gravedad, sensor de presión; Sensores que recopilan información de su entorno que puede ser utilizada para comprar la situación del terminal. El objetivo de este proyecto es el análisis, el diseño y el desarrollo de un sistema para monitorizar remotamente los valores de los sensores de dispositivos móviles. -
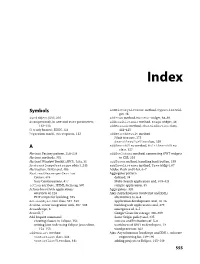
Download the Index
Dewsbury.book Page 555 Wednesday, October 31, 2007 11:03 AM Index Symbols addHistoryListener method, Hyperlink wid- get, 46 $wnd object, JSNI, 216 addItem method, MenuBar widget, 68–69 & (ampersand), in GET and POST parameters, addLoadListener method, Image widget, 44 112–113 addMessage method, ChatWindowView class, { } (curly braces), JSON, 123 444–445 ? (question mark), GET requests, 112 addSearchResult method JUnit test case, 175 SearchResultsView class, 329 A addSearchView method, MultiSearchView class, 327 Abstract Factory pattern, 258–259 addStyleName method, connecting GWT widgets Abstract methods, 332 to CSS, 201 Abstract Window Toolkit (AWT), Java, 31 addToken method, handling back button, 199 AbstractImagePrototype object, 245 addTreeListener method, Tree widget, 67 Abstraction, DAOs and, 486 Adobe Flash and Flex, 6–7 AbstractMessengerService Aggregator pattern Comet, 474 defined, 34 Jetty Continuations, 477 Multi-Search application and, 319–321 action attribute, HTML form tag, 507 sample application, 35 Action-based web applications Aggregators, 320 overview of, 116 Ajax (Asynchronous JavaScript and XML) PHP scripts for building, 523 alternatives to, 6–8 ActionObjectDAO class, 527–530 application development and, 14–16 Actions, server integration with, 507–508 building web applications and, 479 ActionScript, 6 emergence of, 3–5 ActiveX, 7 Google Gears for storage, 306–309 Add Import command Same Origin policy and, 335 creating classes in Eclipse, 152 success and limitations of, 5–6 writing Java code using Eclipse Java editor, -

Google Webtool
Google Web Toolkit Stephen Bilston Stuart Johnson Eric Fath-Kolmes Ai Ci Lin Andrew Nisbet Presentation Goals What is GWT? An overview of GWT's features. When should I use GWT? Who's using it? Finally what you can do with it? What are the risks? What is Google Web Toolkit (GWT)? Develop Webapps using Java Compile the Java to X-browser Javascript Finally a magic bullet to fix Everything! What's so great about it Abstracts away HTML and CSS Makes Client server communcation easy Has robust 3rd party libaraies Easy deployment Eases Web development Lets you avoid HTML and CSS along with all there vairous oddities Many programmers already know java but don't know JavaScript, GWT moves the task of learning from new languages to what is effectively another library Writing javascript can be weird - GWT removes much of the weirdness Makes client server comuncation easy Two easy methods: GWT-RPC Almost makes server commuincation feel like local method calls Has rather good serialization functionality Request Factory Acts like a fake ORM(Object Relational Mapping) for the client side Normal Ajax if you really want to Has robust third party libaries Smart GWT Widgets Dual licensed Ext GWT More Widgets Dual licensed with reduced functionaliy Vaadin Widgets Server Side functionality(validation, etc) Easy depoyment Uses Java Servlets for GWT-RPC and Request Factory Lots of options(Tomcat, JBoss etc..) If your okay with the abstraction leaking a bit you can use anything to do generic AJAX Php Ruby Perl Whatever Using java server side is an easy sell Code Quality Concerns Debugging -With GWT, you can debug java byte code directly as it was executed in a simulated browser environment. -

Ray Cromwell
Building Applications with Google APIs Ray Cromwell Monday, June 1, 2009 “There’s an API for that” • code.google.com shows 60+ APIs • full spectrum (client, server, mobile, cloud) • application oriented (android, opensocial) • Does Google have a Platform? Monday, June 1, 2009 Application Ecosystem Client REST/JSON, GWT, Server ProtocolBuffers Earth PHP Java O3D App Services Media Docs Python Ruby Utility Blogger Spreadsheets Maps/Geo JPA/JDO/Other Translate Base Datastore GViz Social MySQL Search OpenSocial Auth FriendConnect $$$ ... GData Contacts AdSense Checkout Monday, June 1, 2009 Timefire • Store and Index large # of time series data • Scalable Charting Engine • Social Collaboration • Story Telling + Video/Audio sync • Like “Google Maps” but for “Time” Monday, June 1, 2009 Android Version 98% Shared Code with Web version Monday, June 1, 2009 Android • Full API stack • Tight integration with WebKit browser • Local database, 2D and 3D APIs • External XML UI/Layout system • Makes separating presentation from logic easier, benefits code sharing Monday, June 1, 2009 How was this done? • Google Web Toolkit is the Foundation • Target GWT JRE as LCD • Use Guice Dependency Injection for platform-specific APIs • Leverage GWT 1.6 event system Monday, June 1, 2009 Example App Code Device/Service JRE interfaces Guice Android Browser Impl Impl Android GWT Specific Specific Monday, June 1, 2009 Shared Widget Events interface HasClickHandler interface HasClickHandler addClickHandler(injectedHandler) addClickHandler(injectedHandler) Gin binds GwtHandlerImpl -
Information Retrieval and Mining in Distributed Environments Studies in Computational Intelligence,Volume 324 Editor-In-Chief Prof
Alessandro Soro, Eloisa Vargiu, Giuliano Armano, and Gavino Paddeu (Eds.) Information Retrieval and Mining in Distributed Environments Studies in Computational Intelligence,Volume 324 Editor-in-Chief Prof. Janusz Kacprzyk Systems Research Institute Polish Academy of Sciences ul. Newelska 6 01-447 Warsaw Poland E-mail: [email protected] Further volumes of this series can be found on our homepage: springer.com Vol. 313. Imre J. Rudas, J´anos Fodor, and Janusz Kacprzyk (Eds.) Vol. 301. Giuliano Armano, Marco de Gemmis, Computational Intelligence in Engineering, 2010 Giovanni Semeraro, and Eloisa Vargiu (Eds.) ISBN 978-3-642-15219-1 Intelligent Information Access, 2010 Vol. 314. Lorenzo Magnani,Walter Carnielli, and ISBN 978-3-642-13999-4 Claudio Pizzi (Eds.) Vol. 302. Bijaya Ketan Panigrahi,Ajith Abraham, Model-Based Reasoning in Science and Technology, 2010 and Swagatam Das (Eds.) ISBN 978-3-642-15222-1 Computational Intelligence in Power Engineering, 2010 Vol. 315. Mohammad Essaaidi, Michele Malgeri, and ISBN 978-3-642-14012-9 Costin Badica (Eds.) Vol. 303. Joachim Diederich, Cengiz Gunay, and Intelligent Distributed Computing IV, 2010 James M. Hogan ISBN 978-3-642-15210-8 Recruitment Learning, 2010 Vol. 316. Philipp Wolfrum ISBN 978-3-642-14027-3 Information Routing, Correspondence Finding, and Object Vol. 304.Anthony Finn and Lakhmi C. Jain (Eds.) Recognition in the Brain, 2010 Innovations in Defence Support Systems, 2010 ISBN 978-3-642-15253-5 ISBN 978-3-642-14083-9 Vol. 317. Roger Lee (Ed.) Vol. 305. Stefania Montani and Lakhmi C. Jain (Eds.) Computer and Information Science 2010 Successful Case-Based Reasoning Applications-1, 2010 ISBN 978-3-642-15404-1 ISBN 978-3-642-14077-8 Vol.