Easyhook: Down & Dirty with Microsoft Windows
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Microsoft and Cray to Unveil $25,000 Windows-Based Supercomputer
AAll About Microsoft: l lCodeTracker A monthly look at Microsoft’s codenames and what they Areveal about the direction of the company. b o u t M i c r o s o f t : All About Microsoft CodeTracker Keeping track of Microsoft's myriad codenames is an (almost) full-time occupation. I know, as I spend a lot of my work hours tracking down the latest names in the hopes of being able to better keep tabs on what's coming next from the Redmondians. Each month, I'll be releasing an updated, downloadable version of the CodeTracker. I'll add new codenames -- arranged in alphabetical order by codename -- of forthcoming Microsoft products and technologies. I also will note timing changes (date slips, the release of a new test build, the disappearance of a planned deliverable) for entries that are already part of the Tracker. Once Microsoft releases the final version of a product or technology I've been tracking, I will remove it from the Tracker. In that way, the CodeTracker will remain focused on futures. (An aside about the Tracker: A question mark in place of an entry means I have insufficient information to hazard even an educated guess about a particular category.) If you have suggested new entries or corrections to existing ones, please drop me an e-mail at mjf at microsofttracker dot com. Thanks! Mary Jo Foley, Editor, ZDNet's "All About Microsoft" blog This Month's Theme: Big iron needs love, too If you went by nothing but blog and publication headlines, you might think mobile phones and slates are where all the innovation is these days. -

Discovery Attender User Guide
Welcome Sherpa Software's Discovery Attender is a software tool designed to automate the search and collection of electronically stored information across a variety of platforms. This dynamic solution sits behind the firewall and enables in-house talent to identify and gather responsive information in a timely, defensible manner. The Discovery Attender interface is designed to be intuitive and user friendly. The Welcome Screen (above) serves as the gateway to the product. From here you can directly open the PreSearch Tool or create a project. A project serves as a repository for a collection - related searches and associated result sets. Once a new pro- ject is created, the MAIN CONSOLE acts as the central hub to allow you to control the creation, processing, and organization of searches. From here, you can access a Search Wizard which guides you through the step-by- step process of creating a new search. The MAIN CONSOLE also provides access to the Result Management features to view, organize, export and report on the messages, attachments and files that are found during your custom searches. Where to Begin To effectively filter and produce data with Discovery Attender, you must first create a project . Once a project is created, follow the steps below to begin the process: Step Action Description 1 Create and Run A Search A setup wizard leads you through the process of selecting locations and criteria to include in your search. Once started, the chosen data stores are scanned to find items (called results) that match the selected criteria. Information and metadata from these results are stored in the search data- bases. -

Advance Dynamic Malware Analysis Using Api Hooking
www.ijecs.in International Journal Of Engineering And Computer Science ISSN:2319-7242 Volume – 5 Issue -03 March, 2016 Page No. 16038-16040 Advance Dynamic Malware Analysis Using Api Hooking Ajay Kumar , Shubham Goyal Department of computer science Shivaji College, University of Delhi, Delhi, India [email protected] [email protected] Abstract— As in real world, in virtual world also there are type of Analysis is ineffective against many sophisticated people who want to take advantage of you by exploiting you software. Advanced static analysis consists of reverse- whether it would be your money, your status or your personal engineering the malware’s internals by loading the executable information etc. MALWARE helps these people into a disassembler and looking at the program instructions in accomplishing their goals. The security of modern computer order to discover what the program does. Advanced static systems depends on the ability by the users to keep software, analysis tells you exactly what the program does. OS and antivirus products up-to-date. To protect legitimate users from these threats, I made a tool B. Dynamic Malware Analysis (ADVANCE DYNAMIC MALWARE ANAYSIS USING API This is done by watching and monitoring the behavior of the HOOKING) that will inform you about every task that malware while running on the host. Virtual machines and software (malware) is doing over your machine at run-time Sandboxes are extensively used for this type of analysis. The Index Terms— API Hooking, Hooking, DLL injection, Detour malware is debugged while running using a debugger to watch the behavior of the malware step by step while its instructions are being processed by the processor and their live effects on I. -

Software License Agreement (EULA)
Third-party Computer Software AutoVu™ ALPR cameras • angular-animate (https://docs.angularjs.org/api/ngAnimate) licensed under the terms of the MIT License (https://github.com/angular/angular.js/blob/master/LICENSE). © 2010-2016 Google, Inc. http://angularjs.org • angular-base64 (https://github.com/ninjatronic/angular-base64) licensed under the terms of the MIT License (https://github.com/ninjatronic/angular-base64/blob/master/LICENSE). © 2010 Nick Galbreath © 2013 Pete Martin • angular-translate (https://github.com/angular-translate/angular-translate) licensed under the terms of the MIT License (https://github.com/angular-translate/angular-translate/blob/master/LICENSE). © 2014 [email protected] • angular-translate-handler-log (https://github.com/angular-translate/bower-angular-translate-handler-log) licensed under the terms of the MIT License (https://github.com/angular-translate/angular-translate/blob/master/LICENSE). © 2014 [email protected] • angular-translate-loader-static-files (https://github.com/angular-translate/bower-angular-translate-loader-static-files) licensed under the terms of the MIT License (https://github.com/angular-translate/angular-translate/blob/master/LICENSE). © 2014 [email protected] • Angular Google Maps (http://angular-ui.github.io/angular-google-maps/#!/) licensed under the terms of the MIT License (https://opensource.org/licenses/MIT). © 2013-2016 angular-google-maps • AngularJS (http://angularjs.org/) licensed under the terms of the MIT License (https://github.com/angular/angular.js/blob/master/LICENSE). © 2010-2016 Google, Inc. http://angularjs.org • AngularUI Bootstrap (http://angular-ui.github.io/bootstrap/) licensed under the terms of the MIT License (https://github.com/angular- ui/bootstrap/blob/master/LICENSE). -

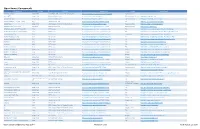
Focus Type Applies To
Focus Type Applies To All Power Tools All All Power Tools Team Foundation Server All Templates Team Foundation Server All Integration Provider Team Foundation Server All Power Tools Team Foundation Server All Power Tools Team Foundation Server All Integration Provider Team Foundation Server Architecture Power Tools Visual Studio Architecture Power Tools Visual Studio Architecture Templates Visual Studio Architecture Integration Provider Oracle Architecture Templates Expression Builds Power Tools Team Foundation Server Builds Integration Provider Visual Studio Builds Power Tools Team Foundation Server Builds Templates Team Foundation Server Builds Power Tools Team Foundation Server Builds Power Tools Team Foundation Server Builds Power Tools Team Foundation Server Coding Power Tools Visual Studio Coding Integration Provider Visual Studio Coding Azure Integration Visual Studio Coding Integration Provider Dynamics CRM Coding Documentation Visual Studio Coding Integration Provider Visual Studio Coding Templates Visual Studio Coding Documentation Visual Studio Coding Templates SharePoint Coding Templates SharePoint Coding Integration Provider Visual Studio Coding Integration Provider Visual Studio Coding Templates SharePoint Coding Power Tools Visual Studio Coding Power Tools Visual Studio Coding Templates SharePoint Coding Templates Visual Studio Coding Templates Visual Studio Coding Templates Visual Studio Coding Power Tools Visual Studio Coding Integration Provider SharePoint Coding Templates Visual Studio Coding Templates SharePoint Coding -
A Malware Analysis and Artifact Capture Tool Dallas Wright Dakota State University
Dakota State University Beadle Scholar Masters Theses & Doctoral Dissertations Spring 3-2019 A Malware Analysis and Artifact Capture Tool Dallas Wright Dakota State University Follow this and additional works at: https://scholar.dsu.edu/theses Part of the Information Security Commons, and the Systems Architecture Commons Recommended Citation Wright, Dallas, "A Malware Analysis and Artifact Capture Tool" (2019). Masters Theses & Doctoral Dissertations. 327. https://scholar.dsu.edu/theses/327 This Dissertation is brought to you for free and open access by Beadle Scholar. It has been accepted for inclusion in Masters Theses & Doctoral Dissertations by an authorized administrator of Beadle Scholar. For more information, please contact [email protected]. A MALWARE ANALYSIS AND ARTIFACT CAPTURE TOOL A dissertation submitted to Dakota State University in partial fulfillment of the requirements for the degree of Doctor of Philosophy in Cyber Operations March 2019 By Dallas Wright Dissertation Committee: Dr. Wayne Pauli Dr. Josh Stroschein Dr. Jun Liu ii iii Abstract Malware authors attempt to obfuscate and hide their execution objectives in their program’s static and dynamic states. This paper provides a novel approach to aid analysis by introducing a malware analysis tool which is quick to set up and use with respect to other existing tools. The tool allows for the intercepting and capturing of malware artifacts while providing dynamic control of process flow. Capturing malware artifacts allows an analyst to more quickly and comprehensively understand malware behavior and obfuscation techniques and doing so interactively allows multiple code paths to be explored. The faster that malware can be analyzed the quicker the systems and data compromised by it can be determined and its infection stopped. -
Introducing Microsoft SQL Server 2014 Technical Overview
Introducing Windows 8.1 for IT Professionals Introducing Introducing Windows 8.1 for IT Professionals Get a head start evaluating Windows 8.1—with early technical Note insights from award-winning journalist and Windows expert Ed This title is also available as a free Bott. This guide introduces new features and capabilities, providing eBook from Microsoft at: a practical, high-level overview for IT professionals ready to begin http://aka.ms/mspressfree deployment planning now. About the Author Preview new features and enhanced capabilities, Ed Bott is an award-winning journalist including: known to millions of readers through two decades of writing for leading • The Windows 8.1 user experience industry publications and more than 25 • Deployment tools and technologies books on Microsoft Office and Windows, • Security features including Windows 7 Inside Out and • Internet Explorer 11 Microsoft Office Inside Out: 2013 Edition. • Delivering Windows Store apps • Recovery options • Networking and remote access • Virtualization Introducing • Windows RT 8.1 • Managing mobile devices Also see Microsoft SQL Server 2014 Windows 8.1 Administration Microsoft Office Pocket Consultant Inside Out Essentials & Configuration 2013 Edition ISBN: 9780735682658 ISBN: 9780735669062 Storage, Security, & Networking Technical Overview ISBN: 9780735682610 U.S.A. $9.99 Canada $10.99 [Recommended] n Operating Systems/Windows Celebrating 30 years! ROSS MISTRY STACIA MISNER PUBLISHED BY Microsoft Press A Division of Microsoft Corporation One Microsoft Way Redmond, Washington 98052-6399 Copyright © 2014 by Microsoft Corporation All rights reserved. No part of the contents of this book may be reproduced or transmitted in any form or by any means without the written permission of the publisher. -

Snap on Windows an Intel-Sponsored, Open-Source Telemetry Framework IT 447 April 4, 2017
Snap on Windows An Intel-sponsored, open-source telemetry framework IT 447 April 4, 2017 Phillip Anderson McKade Clements Devin Durtschi Mathew Kuhn Jesse Millar Coach: Dr. Jay Ekstrom Sponsor: Taylor Thomas Table of Contents Table of Contents Executive Summary Introduction Concept Definition Background Stakeholders Intel Companies with Windows Systems Operators of Windows Systems Open-source Maintainers of the Snap Project Members of the Snap Community Stakeholder Requirements Validation Verification System Definition System Requirements Logical Architecture Project Component Details Build Windows Test Environment Perfmon Plugin Sysinternals Plugin Active Directory Plugin Create an Automated Build Script for Snap Critical Path Verification and Validation Project Management Objective Statement List of Deliverables Conclusion References Appendix Source Code Constraint Matrix Governance Framework Communication Acceptance Documentation Gantt Chart Executive Summary Snap for Windows is a Brigham Young University Information Technology 2016-2017 capstone project. Snap is an open-source telemetry system headed by Intel, meant to facilitate the remote monitoring of large networks and company infrastructures. Snap works through three types of “plugins,” which allow for modularized collecting, processing, and publishing of system metrics. These metrics can include data such as cpu usage, number of processes running on a system, and memory available. Previously, Snap’s functionalities were constrained to Linux systems only, and were not compatible with Windows. This prevented a large portion of company infrastructures from utilizing Snap, as companies typically run the Windows operating system on a large portion of their network. The objective for this project included automating Snap’s build process onto Windows through a build script and creating three separate collector plugins based on the Windows’ Perfmon, Active Directory, and Sysinternals applications. -

Automate Windows Environments with Ansible
Automate Windows Environments with Ansible Orcun Atakan [email protected] Sr. Solution Architect, Red Hat ANSIBLE AUTOMATION FOR WINDOWS What we’ll be discussing today What is Ansible? Windows Management with Ansible What is DSC? Why Use Ansible with DSC? Demo: Rolling update of a .NET application on Windows 2 37,000+ 2800+ 500,000+ Stars on GitHub Ansible modules Downloads a month 3 WHY ANSIBLE? (for Windows) SIMPLE POWERFUL AGENTLESS Human readable automation Enable many use cases Ideal for Windows remoting No special coding skills needed Works hand-in-hand with DSC resources No agents to exploit or update Tasks executed in order Easy platform enablement Standards-based WinRM Usable by every team Leverage Powershell Get productive quickly ANSIBLE AUTOMATION WORKS ACROSS TEAMS BUSINESS DEV/QA COMPUTE NETWORK/SECURITY I.T. OPERATIONS 5 WINDOWS AUTOMATION 100+ 1,300+ Windows Powershell DSC Modules resources ansible.com/windows WHAT CAN I DO USING ANSIBLE FOR WINDOWS Native Windows support uses PowerShell remoting to manage Windows in the same Ansible agentless way ● Install and uninstall MSIs ● Gather facts on Windows hosts ● Enable and disable Windows features ● Start, stop, and manage Windows Services ● Create and Manage local users and groups ● Manage Windows packages via Chocolatey package manager ● Manage and install Windows updates ● Fetch files from remote sites ● Push and execute any Powershell scripts 7 Playbook Example 1/2 - hosts: new_servers tasks: - name: ensure common OS updates are current win_updates: register: update_result -
Meridium V3.6X Open Source Licenses (PDF Format)
Open Source Components Component Version License License Link Usage Home Page .NET Zip Library Unspecified SharpZipLib GPL License (GPL w/exception) http://www.icsharpcode.net/opensource/sharpziplib/ Dynamic Library http://dotnetziplib.codeplex.com/ 32feet.NET Unspecified Microsoft Public License http://opensource.org/licenses/MS-PL File + Dynamic Library http://32feet.codeplex.com AjaxControlToolkit Unspecified Microsoft Public License http://opensource.org/licenses/MS-PL Dynamic Library http://ajaxcontroltoolkit.codeplex.com/ Android - platform - external - okhttp 4.3_r1 Apache License 2.0 http://www.apache.org/licenses/LICENSE-2.0.html File http://developer.android.com/index.html angleproject Unspecified BSD 3-clause "New" or "Revised" License http://opensource.org/licenses/BSD-3-Clause Dynamic Library http://code.google.com/p/angleproject/ Apache Lucene - Lucene.Net 3.0.3-RC2 Apache License 2.0 http://www.apache.org/licenses/LICENSE-2.0.html Dynamic Library http://lucenenet.apache.org/ AttributeRouting (ASP.NET Web API) 3.5.6 MIT License http://www.opensource.org/licenses/mit-license.php File http://www.nuget.org/packages/AttributeRouting.WebApi AttributeRouting (Self-hosted Web API) 3.5.6 MIT License http://www.opensource.org/licenses/mit-license.php File http://www.nuget.org/packages/AttributeRouting.WebApi.Hosted AttributeRouting.Core 3.5.6 MIT License http://www.opensource.org/licenses/mit-license.php Component http://www.nuget.org/packages/AttributeRouting.Core AttributeRouting.Core.Http 3.5.6 MIT License http://www.opensource.org/licenses/mit-license.php -
Practical Malware Analysis
PRAISE FOR PRACTICAL MALWARE ANALYSIS Digital Forensics Book of the Year, FORENSIC 4CAST AWARDS 2013 “A hands-on introduction to malware analysis. I’d recommend it to anyone who wants to dissect Windows malware.” —Ilfak Guilfanov, CREATOR OF IDA PRO “The book every malware analyst should keep handy.” —Richard Bejtlich, CSO OF MANDIANT & FOUNDER OF TAOSECURITY “This book does exactly what it promises on the cover; it’s crammed with detail and has an intensely practical approach, but it’s well organised enough that you can keep it around as handy reference.” —Mary Branscombe, ZDNET “If you’re starting out in malware analysis, or if you are are coming to analysis from another discipline, I’d recommend having a nose.” —Paul Baccas, NAKED SECURITY FROM SOPHOS “An excellent crash course in malware analysis.” —Dino Dai Zovi, INDEPENDENT SECURITY CONSULTANT “The most comprehensive guide to analysis of malware, offering detailed coverage of all the essential skills required to understand the specific challenges presented by modern malware.” —Chris Eagle, SENIOR LECTURER OF COMPUTER SCIENCE AT THE NAVAL POSTGRADUATE SCHOOL “A great introduction to malware analysis. All chapters contain detailed technical explanations and hands-on lab exercises to get you immediate exposure to real malware.” —Sebastian Porst, GOOGLE SOFTWARE ENGINEER “Brings reverse-engineering to readers of all skill levels. Technically rich and accessible, the labs will lead you to a deeper understanding of the art and science of reverse-engineering. I strongly believe this will become the defacto text for learning malware analysis in the future.” —Danny Quist, PHD, FOUNDER OF OFFENSIVE COMPUTING “An awesome book . -
Windows Tool Reference
AppendixChapter A1 Windows Tool Reference Windows Management Tools This appendix lists sets of Windows management, maintenance, configuration, and monitor- ing tools that you may not be familiar with. Some are not automatically installed by Windows Setup but instead are hidden away in obscure folders on your Windows Setup DVD or CD- ROM. Others must be downloaded or purchased from Microsoft. They can be a great help in using, updating, and managing Windows. We’ll discuss the following tool kits: ■ Standard Tools—Our pick of handy programs installed by Windows Setup that we think are unappreciated and not well-enough known. ■ Support Tools—A set of useful command-line and GUI programs that can be installed from your Windows Setup DVD or CD-ROM. ■ Value-Added Tools—Several more sets of utilities hidden away on the Windows Setup CD-ROM. ■ Windows Ultimate Extras and PowerToys for XP—Accessories that can be downloaded for free from microsoft.com. The PowerToys include TweakUI, a program that lets you make adjustments to more Windows settings than you knew existed. ■ Resource Kits—A set of books published by Microsoft for some versions of Windows that includes a CD-ROM containing hundreds of utility programs. What you may not have known is that in some cases you can download the Resource Kit program toolkits with- out purchasing the books. ■ Subsystem for UNIX-Based Applications (SUA)—A package of network services and command-line tools that provide a nearly complete UNIX environment. It can be installed only on Windows Vista Ultimate and Enterprise, and Windows Server 2003.