Mactcp Administrator's Guide
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Circuit-Cellar-017.Pdf
EDITOR’S INK CASE is Coming Curtis Franklin, Jr. I t’s fun to watch events come together to form a trend. A and the programmer’s “quality of life” improved. Finally, there while back, I told you that events were coming together that came the trend that would tie everything together. would result in a trend toward using “PC-compatible” platforms Intel pushed to merge desktop microcomputer and embed- for control applications in ever-increasing numbers. Things are ded controllerarchitectureswiththe80186. Here wasa micropro- still rolling along with that trend, and I feel pretty good about the cessor that was code-compatible with the popular 8088 and 80% prediction. I feel so good, in fact, that I’m going to hit you with microprocessors, yet had I/O features more typical of embedded another prediction this time: I predict that most of the people controllers. Through time, the price of IBM PC/XT-clone moth- reading this will be using CASEKomputer-Aided Software erboards dropped to a point where the same I/O, operating Engineering-within the next five years. It doesn’t matter whether system, and memory architectures could be economically used most of your programming time is spent on desktop computer for both desktop computing and control applications. Engineers applications or embedded control, I believe you will start using and control programmers have been introduced to the wonders CASE tools. I’m making this prediction based, not on any sort of of the modern desktop development environment, and the steps blazing insight, but on the logical progression of several industry are short between (for example) the Borland Turbo-language trends. -
Apple Multiple Scan 15 Display
K Service Source Apple Multiple Scan 15 Display K Service Source Basics Apple Multiple Scan 15 Display Basics Overview - 1 Overview The Apple Multiple Scan 15 Display is a color monitor that supports a variety of resolutions, and has a flat, square screen for clear, sharp images. The Apple Multiple Scan 15 Display has a diagonal viewable image size of 13.3 inches. Basics Overview - 2 The Apple Multiple Scan 15 Display features • Optimized screen resolutions (640x480, 800x600, 832x624) • A tilt-swivel base that allows the monitor to be positioned for optimal viewing comfort • MPR II compliance for low electrical and magnetic emissions • Energy Star power conservation compliance K Service Source Specifications Apple Multiple Scan 15 Display Specifications Characteristics - 1 Characteristics Picture Tube 15-in. diagonal flat square shadow mask (13.3-in. viewable image) Multiple scan Polished surface treatment Screen Resolution 640x480, 800x600, or 832x624 1024x768 (only PC and PC-compatibles with a Mac/PC adapter) 0.28-mm dot pitch Scan Rates Vertical refresh rate: 60–75 Hz Horizontal scan rate: 31.77–56.5 kHz Macintosh, VGA, and SVGA compatible Specifications Characteristics - 2 Cable Connector 15-pin miniature D-type Input Signals Video: red, green, and blue analog signals; RS-343A standard; .714 V peak to peak; positive-going Sync on green: RS-343A compatible level; .286 V ± 10% negative-going during blanking intervals Separate Sync: 1 to 5 V peak to peak; negative- or positive-going Composite Sync: 1 to 5 V peak to peak; negative- or positive-going Specifications Characteristics - 3 System Power Macintosh, Macintosh Centris, Macintosh Quadra, some Requirements Macintosh Performas, or any NuBus compatible Macintosh with a Macintosh Display Card 24AC. -
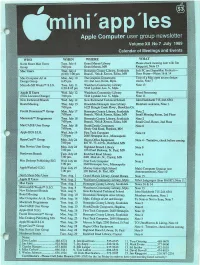
Apple Computer User Group Newsletter Volume XII No 7 July 1989 Calendar of Meetings and Events
""rxr$MyJmx<ww<&m8m5m "\Y??%m Apple Computer user group newsletter Volume XII No 7 July 1989 Calendar of Meetings and Events . -■■: j j ^ l : . .■;v;v:v;v.yiy.v.-.y. WHO WHEN WHERE WHAT North Shore Mac Users Tues. July 4 Grand Marais Library Please check meeting date with Jim Group 7:00 pm Grand Marais, MN Ringquist, Note 15 Mac Users Thur. July 6 Hennepin County Library, Southdale Soft PC and SuperMac Products (6:30) 7:00 pm Branch, 70th & Xerxes, Edina, MN Door Prizes—Notes 16 & 14 Mac Computer Art & Mon. July 10 The Graphics Department Tour of a Mac open access design Design Group 6:45 pm 411 2nd Ave. North, Mpls. studio, Note 7 MicroSoft® Works™ S.l.G. Tues. July 11 Washburn Community Library Note 13 6:30-8:45 pm 5244 Lyndale Ave. S.. Mpls. Apple II Users Wed. July 12 Washburn Community Library Word Processing (Note Location Change) 7:00 pm 5244 Lyndale Ave. S., Mpls. Note 11 New Richmond Branch Wed. July 12 New Richmond Technical School John Hackbarth 715-246-6561 Board Meeting Thur. July 13 Brookdale Hennepin Area Library Members welcome, Note 1. 7:00 pm 6125 Shingle Creek Pkwy., Brooklyn Ctr. Fourth Dimension™ Group Mon. July 17 Hennepin County Library, Southdale Note 2 7:00 pm Branch, 70th & Xerxes, Edina, MN Small Meeting Room, 2nd Floor Macintosh™ Programmer Tues. July 18 Hennepin County Library, Southdale Note 2 7:00 pm. Branch, 70th & Xerxes, Edina, MN Small Conf. Room, 2nd Floor MacCAD/E User Group Tues. July 18 Heath/Zenith Computers Note 8 7:00 pm. -

Macintosh Portable
• Apple Technical Procedures Macintosh Portable Technical Procedures o TABLE OF CONTENTS Section 1 1.2 Product Description Basics 1.2 Features 1.4 Configurations 1.5 Module Identification 1.6 Options 1.10 Connector and Switch Identification 1.10 Rear Panel 1.10 Internal 1.12 Theory of Operation 1.12 Introduction 1.12 Logic Board 1.21 SuperDrive Disk Drive 1.21 Keyboard 1.21 Trackball 1.21 Low-Power Mouse 1.22 LCD Display 1.24 Main and Backup Batteries 1.25 Power Adapter 1.26 Functional Overview 1.29 System Software 1.29 Features of System Software 6.0.4 1.32 Installation Procedure 1.33 Specifications 1.37 Other Information 1.37 Programmer's Switch 1.38 Materials Required Macintosh Portable rev. Oct 89 Contents / i Section 2 2.3 Introduction Take-Apart 2.3 Materials Required 2.3 Power Information 2.3 Electrostatic Discharge (ESD) Precautions 2.4 Rear Cover 2.6 Keyboard Cover 2.8 Main Battery 2.10 Backup Battery 2.12 Option Cards 2.14 SCSI Hard Disk Drive 2.16 Upper Floppy Disk Drive 2.18 Lower Floppy Disk Drive 2.20 Keyboard, Trackball, and Numeric Keypad 2.22 Speaker 2.24 Display Assembly 2.28 LCD Display 2.34 Logic Board Section 3 3.2 Introduction Diagnostics : 3.2 MacTest (Local) 3.3 AppleCAT (Remote) 3.4 Running the Tests from a Hard Disk 3.4 Using AppleCAT/MacTest Portable 3.4 Materials Required 3.4 MacTest Setup 3.6 AppleCAT Setup 3.8 Test Selections 3.10 Looping 3.11 Configuration 3.11 As the Tests Are Running 3.13 AppleCAT/MacTest Portable Menus and Keyboard Equivalents Section 4 4.2 Introduction Troubleshooting 4.2 Before You Start 4.2 How to Use the Symptom Chart 4.2 How to Use the Troubleshooting Flowcharts 4.3 Things To Remember 4.4 Module Exchange Information 4.4 SCSI Hard Disk 4.4 FDHD Floppy Disk Drive 4.4 LCD Display ii / Contents rev. -

Apple Multiple Scan 17 Display
K Service Source Apple Multiple Scan 17 Display K Service Source Basics Apple Multiple Scan 17 Display Basics EEPROM Settings - 1 EEPROM Settings Caution: To prevent data loss or corruption, always save EEPROM settings before you replace the microprocessor board. (See next page.) See Troubleshooting for instructions on saving the EEPROM settings from the old microprocessor board and restoring the settings on the new microprocessor board. If the settings are lost before they can be written to the new EEPROM, the display will be impossible to repair, and the whole display will need to be replaced. Basics EEPROM Settings - 2 Microprocessor Board K Service Source Specifications Apple Multiple Scan 17 Display Specifications Characteristics - 1 Characteristics Picture Tube 17-in. diagonal Trinitron CRT (16.1-in. viewable image) Multiple scan Bonded glass panel with antiglare/antistatic multilayer coating Screen Resolution 640x480, 800x600, 832x624, or 1024x768 0.26-mm stripe pitch Scan Rates Vertical refresh rate: 50 to 150 Hz Horizontal scan rate: 29 to 82 kHz Macintosh, XGA, VGA, SVGA, and VESA compatible Cable Connector 15-pin miniature D-type Specifications Characteristics - 2 Input Signals Video: red, green, and blue analog signals; RS-343A standard;.714 V peak to peak; positive going Sync on green: RS-343A compatible level;.286 V ± 10% negative-going during blanking intervals Separate Sync: 1 to 5 V peak to peak; negative or positive going Composite Sync: 1 to 5 V peak to peak; negative or positive going System Power Macintosh, Macintosh Centris, Macintosh Quadra, or any Requirements NuBus compatible Macintosh with a Macintosh Display Card 24AC. -

PATHWORKS for Macintosh
PATHWORKS for Macintosh MacTCP Administrator's Guide Order Number: AA-PCT5B-TE PATHWORKS for Macintosh MacTCPTM Administrator's Guide Order Number AA-PCT5B-TE January 1991 Revision/Update Information: This is a revised manual. Software Version: PATHWORKS for Macintosh, Version 1.0 VMS Version 5.3 or greater digital equipment corporation maynard, massachusetts '* Apple Computer, Inc. This manual and the software described in it are copyrighted, with all rights reserved. Under the copyright laws, this manual or the software may not be copied, in whole or part, without written consent of Apple, except in the normal use of the software or to make a backup copy of the software. The same proprietary and copyright notices must be affixed to any permitted copies as were affixed to the original. This exception does not a110w copies to be made for others, whether or not sold, but a11 of the material purchased (with all backup copies) may be sold, given, or loaned to another person. Under the law, copying includes translating into another language or format. You may use the software on any computer owned by you, but extra copies cannot be made for this purpose. The Apple logo is a registered trademark of Apple Computer, Inc. Use of the ''keyboard'' Apple logo (Option-Shift-K) for commercial purposes without the prior written consent of Apple may constitute trademark infringement and unfair competition in violation of federal and state laws. © Apple Computer, Inc., 1989, 1990, 1991. Apple Computer, Inc. Microsoft and MS-DOS are 20525 Mariani Avenue registered trademarks of Microsoft Cupertino, CA 95014 Corporation. -

Update to Appletalk Internet Router Administrator's Guide
UPDATE TO APPLETALK INTERNET ROUTER ADMINISTRATOR'S GUIDE This update provides important changes to the information in the AppleTalk Internet Router Administrator's Guide. In particular, the update includes new installation procedures for the AppleTalk Internet Router. Whether you use System 6 or System 7, you should follow the instructions given here; these instructions completely replace those found in Chapter 5, "Installing the AppleTalk Internet Router," of the AppleTalk Internet Router Administrator's Guide. In addition to new installation procedures, this update also contains information about system requirements, using the router with System 7, and running the router concurrently with AppleShare File Server software. What this update contains This update contains six major sections: - "System Requirements" This section specifies the Macintosh computers and the system software you need to operate the AppleTalk Internet Router. - "Running the AppleTalk Internet Router on a System 7 Macintosh" If you are using the router on a System 7 Macintosh, you need to be aware of certain changes in terminology and function between System 6 and System 7. This section explains those changes and also describes the most efficient way to use the router on a Macintosh computer running system software version 7.0 or later. - "Installing the AppleTalk Internet Router on a Hard Disk" This section describes new procedures for installing the router. - "Running the AppleTalk Internet Router Without a Hard Disk" This section explains how to run the router without using a hard disk (for System 6 users only). - "Installing the AppleTalk Internet Router With an AppleShare File Server" This section describes steps you need to take if you are installing the router on a Macintosh that is also running AppleShare File Server software, with specific instructions for both AppleShare version 2.0 and version 3.0 users. -
Macintosh II High-Resolution Display Video Card, Expansion
Macintosh II High-Resolution Display Video Card and Expansion Kit ® Overview Features Benefits The Macintosh® II High-Resolu- Compatible with both the Apple- Requires only one video card for tion Display Video Card pro- Color High-Resolution RGB Monitor either color or monochrome display. and the Apple High-Resolution Mono- Provides a monitor upgrade path vides the Macintosh II family chrome Monitor with no additional interface costs. of computers with a single ........................................................................................................................................... interface for both the Apple® High-Resolution Monochrome Up to 256 colors (or shades of gray) Offers a comprehensive range of ™ at one time from a palette of more than colors for enhancing graphics, presenta- Monitor and the AppleColor 16 million colors/gray levels tion materials, and other documents. High-Resolution RGB Monitor. ........................................................................................................................................... It allows you to display up to 256 colors (or gray levels) Software-selectable display modes Lets you display 2, 4, 16, or 256 co- simultaneously from a palette lors or gray levels with a simple change from the computer’s Control Panel. of more than 16 million. ........................................................................................................................................... In the basic configuration, the card allows for 16 colors or NuBus™ interface Plugs -

Ports and Pinouts
K Service Source Ports and Pinouts Ports and Pinouts Cable Connectors - 1 Cable Connectors The pin numbers shown are for the connectors attached to the ends of the Macintosh peripheral cables, as viewed from the front of the connector. 152 Processor-Direct Slot, 152-Pin 77 76 HDI-30 1 HDI-20 PowerBook Video 25 14 2 30 20 16 6 1 5 1 13 1 HDI-45-pin Mini DIN-4 Apple Desktop Bus Apple AAUI 45 44 43 37 36 35 3 4 (Ethernet) 28 1 7 34 27 19 18 12 2 1 8 3 14 11 10 9 3 2 1 S-Video Mini Din-7Serial Mini Din-8 GeoPort Mini Din-9 7 7 7 4 3 6 8 8 6 IN 2 1 3 5 5 3 9 4 6 5 2 1 2 1 4 DB-15 Mini DIN-4 S-Video 1 8 3 4 2 1 9 15 DB-25 1 13 Composite Video (RCA jack) IN/OUT RF Input 14 25 Sig Gnd 1 25 BR-50 26 50 Microphone Jack Ports and Pinouts GeoPort Mini DIN-9 - 2 GeoPort Mini DIN-9 The back panel of all Power Macintosh models contain two I/O ports for serial telecommunication data. Both sockets accept 9-pin plugs, allowing either port to be independently programmed for asynchronous or synchronous communication formats up to 9600 bps. This includes AppleTalk and the full range of Apple GeoPort protocols. Pin Name Function 1 SCLK (out) Reset pod or get pod attention 2 Sync (in)/SCLK (in) Serial clock from pod (up to 920 Kbit/sec.) 3 TxD- Transmit - 4 Gnd/shield Ground 5 RxD- Receive - 6 TxD+ Transmit + 7 Wake up/TxHS Wake up CPU or do DMA handshake 8 RxD+ Receive + 9 +5V Power to pod (350 mA maximum) Ports and Pinouts Apple Desktop Bus (ADB) Connector - 3 Apple Desktop Bus (ADB) Connector Connector type: Mini DIN-4 male. -

Circuit-Cellar-018.Pdf
1 EDITOR’S I’ve Seen the Future INK Curtis Franklin, Jr. 1 I recently led a panel discussion at the Embedded Systems 32-BIT PROCESSORS Programming Conference. I met interesting people, arranged for a few articles, and ran into lots of folks who were carrying crystal There weren’t many people talking about 8-bit processors at balls in their fanny packs. I thought you might like to know what the show. Intel mentioned the 8051, saying that they have now they say you’re going to be doing in the next few years... shipped over 100,000,000 of them, but that came as a passing statement at their press conference announcing the latest mem- OPERATING SYSTEMS bers of the 80960 family. Motorola was ready and willing to talk about 68030 and 88000 applications, National was discussing the You’re going to be using an operating system. I’m not talking 32000, and everyone was announcing the arrival of the 32-bit about the operating system on your desktop computer, but the future. Once in a while I heard talk about 16-bit chips like the complete multitasking operating system that you’ll be building 80186 and 8096, but there was a noticeable absence of discussion into each and every control project. Depending on who you talk on anything having to do with 8-bit applications. to, you’ll be using an MS-DOS variant, a UNIX variant, or a All of the predictions I’ve talked about are fine and probably specialized embedded 0s for your development. -

Macintosh Quadra 700 Developer Note
® Macintosh Quadra 700 Developer Note ® Developer Note Developer Technical Publications © Apple Computer, Inc. 1991 APPLE COMPUTER, INC. QUALITY, ACCURACY, © 1991, Apple Computer, MacDraw is a registered MERCHANTABILITY, Inc. trademark of Claris OR FITNESS FOR A All rights reserved. Corporation. PARTICULAR PURPOSE. No part of this publication Microsoft is a registered AS A RESULT, THIS may be reproduced, stored trademark of Microsoft MANUAL IS SOLD “AS in a retrieval system, or Corporation. IS,” AND YOU, THE transmitted, in any form or PURCHASER, ARE by any means, mechanical, Motorola is a registered ASSUMING THE electronic, photocopying, trademark of Motorola ENTIRE RISK AS TO recording, or otherwise, Corporation. ITS QUALITY AND without prior written ACCURACY. permission of Apple NuBus is a trademark of Computer, Inc. Printed in Texas Instruments. IN NO EVENT WILL APPLE BE LIABLE FOR the United States of Sony is a trademark of Sony America. DIRECT, INDIRECT, Corporation. SPECIAL, The Apple logo is a LIMITED WARRANTY ON INCIDENTAL, OR registered trademark of MEDIA AND CONSEQUENTIAL Apple Computer, Inc. Use of REPLACEMENT DAMAGES RESULTING the “keyboard” Apple logo FROM ANY DEFECT (Option-Shift-K) for If you discover physical OR INACCURACY IN commercial purposes defects in the manual or in THIS MANUAL, even if without the prior written the media on which a advised of the possibility consent of Apple may software product is of such damages. constitute trademark distributed, APDA will infringement and unfair replace the media or THE WARRANTY AND competition in violation of manual at no charge to REMEDIES SET FORTH federal and state laws. you provided you return ABOVE ARE the item to be replaced EXCLUSIVE AND IN Apple Computer, Inc. -

Macintosh Display Card 4•8 and 8•24 Overview
Macintosh Display Card 4•8 and 8•24 Overview The Macintosh® Display Card 4•8 and perceive-on all Apple displays. The addition, the Macintosh Display Card Macintosh Display Card 8•24 provide card also supports full 24-bit true color 8•24 provides the highest-possible the Apple® Macintosh II familyof on the AppleColor High-Resolution quality interlaced video through the use modular computers with a single RGB Monitor, allowing you to generate of Apple Convolution. A capability that interface to all Apple displays and a images of photographic quality by dis is usually associated with much more broad range of graphics capabilities. playing up to 16.7 million colors expensive systems, Apple Convolution The Macintosh Display Card 4•8 simultaneously. In addition to letting evaluates adjacent lines and pixels on provides support for up to 256 colors or you display and work with photo interlaced video devices, then adjusts shades of gray on the Apple High graphic-quality images, true gray-scale the image on the screen to provide Resolution Monochrome Monitor and and true color capabilities allow you to smoother, more continuous images the AppleColor™ High-Resolution RGB work with lifelike simulations, anima than could otherwise be generated. Monitor. In addition, it provides for up tions, and visual effects. The Macintosh Display Card 4•8 and to 16 levels of gray on the Apple The Macintosh Display Card 4•8 can Macintosh Display Card 8•24 provide a Macintosh Portrait Display and the be upgraded to the Macintosh Display wide range of graphics capabilities, Apple Two-Page Monochrome Monitor.