A Box, Darkly: Obfuscation, Weird Languages, and Code Aesthetics
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Radare2 Book
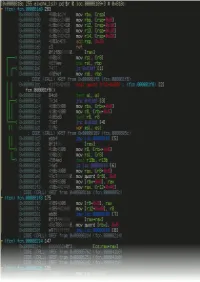
Table of Contents introduction 1.1 Introduction 1.2 History 1.2.1 Overview 1.2.2 Getting radare2 1.2.3 Compilation and Portability 1.2.4 Compilation on Windows 1.2.5 Command-line Flags 1.2.6 Basic Usage 1.2.7 Command Format 1.2.8 Expressions 1.2.9 Rax2 1.2.10 Basic Debugger Session 1.2.11 Contributing to radare2 1.2.12 Configuration 1.3 Colors 1.3.1 Common Configuration Variables 1.3.2 Basic Commands 1.4 Seeking 1.4.1 Block Size 1.4.2 Sections 1.4.3 Mapping Files 1.4.4 Print Modes 1.4.5 Flags 1.4.6 Write 1.4.7 Zoom 1.4.8 Yank/Paste 1.4.9 Comparing Bytes 1.4.10 Visual mode 1.5 Visual Disassembly 1.5.1 2 Searching bytes 1.6 Basic Searches 1.6.1 Configurating the Search 1.6.2 Pattern Search 1.6.3 Automation 1.6.4 Backward Search 1.6.5 Search in Assembly 1.6.6 Searching for AES Keys 1.6.7 Disassembling 1.7 Adding Metadata 1.7.1 ESIL 1.7.2 Scripting 1.8 Loops 1.8.1 Macros 1.8.2 R2pipe 1.8.3 Rabin2 1.9 File Identification 1.9.1 Entrypoint 1.9.2 Imports 1.9.3 Symbols (exports) 1.9.4 Libraries 1.9.5 Strings 1.9.6 Program Sections 1.9.7 Radiff2 1.10 Binary Diffing 1.10.1 Rasm2 1.11 Assemble 1.11.1 Disassemble 1.11.2 Ragg2 1.12 Analysis 1.13 Code Analysis 1.13.1 Rahash2 1.14 Rahash Tool 1.14.1 Debugger 1.15 3 Getting Started 1.15.1 Registers 1.15.2 Remote Access Capabilities 1.16 Remoting Capabilities 1.16.1 Plugins 1.17 Plugins 1.17.1 Crackmes 1.18 IOLI 1.18.1 IOLI 0x00 1.18.1.1 IOLI 0x01 1.18.1.2 Avatao 1.18.2 R3v3rs3 4 1.18.2.1 .intro 1.18.2.1.1 .radare2 1.18.2.1.2 .first_steps 1.18.2.1.3 .main 1.18.2.1.4 .vmloop 1.18.2.1.5 .instructionset 1.18.2.1.6 -

Bypassing Web Application Firewalls
Bypassing Web Application Firewalls Pavol Lupták [email protected] CEO, Nethemba s.r.o Abstract The goal of the presentation is to describe typical obfuscation attacks that allow an attacker to bypass standard security measures such as various input filters, output encoding mechanisms used in web-based intrusion detection systems (IDS), intrusion prevention systems (IPS) and web application firewalls (WAFs). These attacks may include different networking tricks, polymorphic shellcode and various code techniques. At the beginning we analyse and compare different HTML parsing and interpretation approaches used by most-common browsers that can lead to unique attack vectors. Javascript, with a full range of features, represents another effective way that can be used to obfuscate or de-obfuscate code – some existing obfuscation tools are mentioned. We describe how it is possible to construct “non-alphanumeric Javascript code” which does not contain alphabetic or numeric characters, but still can contain malicious executable code. Despite the fact that most current applications are immune to SQL injection attacks, it is still possible to find many vulnerable applications. We focus on different fuzzy techniques (and useful open source SQL injection tools that implement them) which can still be used to bypass weak input validation controls. We conclude our presentation with a demonstration of the most basic obfuscation techniques that can be successfully used to bypass traditional web application firewalls (WAFs). Finally, we briefly describe current mitigation techniques that are recommended for efficient malicious Javascript code analysis and sanitizing user input containing untrusted code. Keywords: WAF, IPS, IDS, obfuscation, SQL injection, XSS, CSS, CSRF. -

C++11 Metaprogramming Applied to Software Obfuscation
C++11 METAPROGRAMMING APPLIED TO SOFTWARE OBFUSCATION SEBASTIEN ANDRIVET About me ! Senior Security Engineer at SCRT (Swiss) ! CTO at ADVTOOLS (Swiss) Sebastien ANDRIVET Cyberfeminist & hacktivist Reverse engineer Intel & ARM C++, C, Obj-C, C# developer Trainer (iOS & Android appsec) PROBLEM Reverse engineering • Reverse engineering of an application if often like following the “white rabbit” • i.e. following string literals • Live demo • Reverse engineering of an application using IDA • Well-known MDM (Mobile Device Management) for iOS A SOLUTION OBFUSCATION What is Obfuscation? Obfuscator O O ( ) = YES! It is also Katy Perry! • (almost) same semantics • obfuscated Obfuscation “Deliberate act of creating source or machine code difficult for humans to understand” – WIKIPEDIA, APRIL 2014 C++ templates OBJECT2 • Example: Stack of objects OBJECT1 • Push • Pop Without templates Stack singers; class Stack { singers.push(britney); void push(void* object); void* pop(); }; Stack apples; apples.push(macintosh); • Reuse the same code (binary) singers apples • Only 1 instance of Stack class With C++ templates template<typename T > Stack<Singer> singers; class Stack singers.push(britney); { void push(T object); T pop(); Stack<Apple> apples; }; apples.push(macintosh); With C++ templates Stack<Singer> singers; singers.push(britney); Stack<Singers> Stack<Apples*> Stack<Apple> apples; apples.push(macintosh); singers apples C++ templates • Two instances of Stack class • One per type • Does not reuse code • By default • Permit optimisations based on types • For ex. reuse code for all pointers to objects • Type safety, verified at compile time Type safety • singers.push(apple); // compilation error Optimisation based on types • Generate different code based on types (template parameters) template<typename T> class MyClass • Example: enable_if { .. -

Magazin Rist 2014.Cdr
RISTian Annual Magazine 2014-15 REGIONAL INSTITUTE OF SCIENCE & TECHNOLOGY Techno City, Kling Road, 9th Mile, Ri-Bhoi, Meghalaya-793101 MAGAZINE COMMITTEE Patron : Mr. M. Hoque, Chairman, ERDF Advisors : Dr. P.C. Mahanta, Director, RIST Dr. U.K. Sharma, Executive Director, RIST Mr. N.I. Laskar, Director, Corporate Communication, RIST Mr. J.U. Choudhury, HR, ERDF EDITORIAL BOARD Co-ordinator: Mr. A.H. Barbhuiya, Registrar, RIST Faculty Editors: Mr. Nabendu Kumar Deb, Asst. Prof. (Physics), Deptt. Of Basic Science and Humanities. Ms. Nabamita Boral, Asst. Prof. (English), Deptt. Of Basic Science and Humanities. Ms. Mandira Baruah, Asst. Prof., Deptt. Of Electrical and Electronics Ms. Baishali Sharma, Administrative Assistant, RIST. Student Editors: Sagorika Raj Chakraborty, 4th sem, EEE Sauvik Dey, 6th sem, CE Gagandeep Kaur, 8th Sem, CSE. Rashmita Mudoi, 8th sem, CSE. Student Co-ordinators: Chinmoyuri Bora, 6th Sem, ECE. Abdul Ghani Kamson, 6th Sem, ECE. Sudeep Sinha, 6th sem, CSE. Saurav Jyoti Das, 6th sem, EEE Illustrator: Santoj Hazarika, 8th Sem, ME Layout & Designing: Giasuddin Ahmed, Graphic Designer, ERDF Jitu Mahanta, DTP Operator, ERDF Printed at : Aman Udyog Pvt. Ltd. Christian Basti, Guwahati-5 i From the faculty editors' desk... “The true sign of intelligence is not knowledge but imagination.” Albert Einstein RISTian is a forum in which the students, faculty members and staffs (RIST Community) can portray their literary talents. This volume, which is n the second, has contributions from the RIST Community in the form of essays, poems, facts, sketches, etc. We offer heartiest thanks to all the contributors. a Putting a magazine together is no cake-walk. -
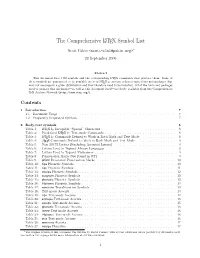
The Comprehensive LATEX Symbol List
The Comprehensive LATEX Symbol List Scott Pakin <[email protected]>∗ 22 September 2005 Abstract This document lists 3300 symbols and the corresponding LATEX commands that produce them. Some of these symbols are guaranteed to be available in every LATEX 2ε system; others require fonts and packages that may not accompany a given distribution and that therefore need to be installed. All of the fonts and packages used to prepare this document—as well as this document itself—are freely available from the Comprehensive TEX Archive Network (http://www.ctan.org/). Contents 1 Introduction 7 1.1 Document Usage . 7 1.2 Frequently Requested Symbols . 7 2 Body-text symbols 8 Table 1: LATEX 2ε Escapable “Special” Characters . 8 Table 2: Predefined LATEX 2ε Text-mode Commands . 8 Table 3: LATEX 2ε Commands Defined to Work in Both Math and Text Mode . 8 Table 4: AMS Commands Defined to Work in Both Math and Text Mode . 9 Table 5: Non-ASCII Letters (Excluding Accented Letters) . 9 Table 6: Letters Used to Typeset African Languages . 9 Table 7: Letters Used to Typeset Vietnamese . 9 Table 8: Punctuation Marks Not Found in OT1 . 9 Table 9: pifont Decorative Punctuation Marks . 10 Table 10: tipa Phonetic Symbols . 10 Table 11: tipx Phonetic Symbols . 11 Table 13: wsuipa Phonetic Symbols . 12 Table 14: wasysym Phonetic Symbols . 12 Table 15: phonetic Phonetic Symbols . 12 Table 16: t4phonet Phonetic Symbols . 13 Table 17: semtrans Transliteration Symbols . 13 Table 18: Text-mode Accents . 13 Table 19: tipa Text-mode Accents . 14 Table 20: extraipa Text-mode Accents . -

Software Protection Through Obfuscation
This document is downloaded from DR‑NTU (https://dr.ntu.edu.sg) Nanyang Technological University, Singapore. Software protection through obfuscation Balachandran, Vivek 2014 Balachandran, V. (2015). Software protection through obfuscation. Doctoral thesis, Nanyang Technological University, Singapore. https://hdl.handle.net/10356/62930 https://doi.org/10.32657/10356/62930 Downloaded on 02 Oct 2021 00:34:50 SGT Software Protection through Obfuscation School of Computer Engineering A Thesis Submitted to the Nanyang Technological University in partial fulfillment of the requirement of the degree of Doctor of Philosophy by Vivek Balachandran under the supervision of Prof. Ng Wee Keong and Prof. Sabu Emmanuel 2015 2 Acknowledgments Foremost, I would like to express my sincere gratitude to my advisors Prof. Sabu Em- manuel and Prof. Ng Wee Keong for the continuous support of my Ph.D study and research, for their patience, motivation, enthusiasm, and immense knowledge. I thank my fellow labmates in Nanyang Technological University, Singapore: Shaheen Ansari, Deepak Subrmanyam, Chia Tee Kiah for their kind support. Many friends have helped me stay sane through these difficult years. Their support and care helped me overcome setbacks and stay focused on my graduate study. I would like to thank Aditya Venkataraman, Chitra Panchapakesan, Ganesh Bharadwaj, Girid- haran Karunagaran, Karthik Raveendran, Manaswini Ramkumar, Manisha Mujumdar, Nirnaya Sarangan, Ponnu Jacob, Roshan Wahab, Shubha Nageswaran,Vidhi Patel and Vipin Pillai for making my life wonderful as a grad student. Last but not the least, I would like to thank my family: my parents G. Balachandran and V. Santhakumari, and my brother Vishakh Balachandran who were always there for me. -

6.858 Final Project
6.858 Final Project Predrag Gruevski Paul Hemberger Andres Romero Albert Wu Introduction Since remote desktop applications are such powerful tools for controlling computers from across the Internet, it stands to reason that adversaries would be motivated to discover and exploit vulnerabilities in such software. In our final project, we explored many of the most popular remote desktop applications for Android clients. Most of them provide little to no security, and we were able to easily create exploits to compromise the keyboard and mouse of the remote machine. Methods We looked at the following popular Android clients (each has at least 100,000 installs on the Google Play app market): 1. TeamViewer for Remote Control 2. Air HID 3. Remote Mouse 4. WiFi Mouse 5. Android Mouse and Keyboard 6. Mobile Mouse Lite 7. Remote Control Collection We installed each of the above clients on an Android phone and the corresponding server on a remote machine running Windows, OS X, or Linux. We used two types of tools for reverse engineering the messaging protocols: 1. Wireshark Wireshark is a network protocol analyzer. Using Wireshark, we were able to analyze incoming and outgoing packets from the remote machine. This was extremely useful for applications using plaintext protocols. 2. Decompilers Tools like Java Decompiler Project, JetBrains dotPeek, Decompile Android, and dex2jar allowed us to decompile many of the client APK files and server executables into very readable Java code. After reverse engineering the protocols, we set up virtual machines running the above applications and send arbitrary keyboard and mouse commands from the host machine via UDP and TCP. -

Achieving Obfuscation Through Self-Modifying Code: a Theoretical Model
Running head: OBFUSCATION THROUGH SELF-MODIFYING CODE 1 Achieving Obfuscation Through Self-Modifying Code: A Theoretical Model Heidi Angelina Waddell A Senior Thesis submitted in partial fulfillment of the requirements for graduation in the Honors Program Liberty University Spring 2020 OBFUSCATION THROUGH SELF-MODIFYING CODE 2 Acceptance of Senior Honors Thesis This Senior Honors Thesis is accepted in partial fulfillment of the requirements for graduation from the Honors Program of Liberty University. _____________________________ Melesa Poole, Ph.D. Thesis Chair ______________________________ Robert Tucker, Ph.D. Committee Member ______________________________ James H. Nutter, D.A. Honors Director ______________________________ Date OBFUSCATION THROUGH SELF-MODIFYING CODE 3 Abstract With the extreme amount of data and software available on networks, the protection of online information is one of the most important tasks of this technological age. There is no such thing as safe computing, and it is inevitable that security breaches will occur. Thus, security professionals and practices focus on two areas: security, preventing a breach from occurring, and resiliency, minimizing the damages once a breach has occurred. One of the most important practices for adding resiliency to source code is through obfuscation, a method of re-writing the code to a form that is virtually unreadable. This makes the code incredibly hard to decipher by attackers, protecting intellectual property and reducing the amount of information gained by the malicious actor. Achieving obfuscation through the use of self-modifying code, code that mutates during runtime, is a complicated but impressive undertaking that creates an incredibly robust obfuscating system. While there is a great amount of research that is still ongoing, the preliminary results of this subject suggest that the application of self-modifying code to obfuscation may yield self-maintaining software capable of healing itself following an attack. -

Socket Extensions for Esoteric Languages
Annals of the University of Craiova, Mathematics and Computer Science Series Volume 41(2), 2014, Pages 271{279 ISSN: 1223-6934 Socket extensions for esoteric languages Radu Dragos¸and Diana Halit¸a˘ Abstract. In this paper we have advanced the first interpreter for the brainfuck (BF) esoteric programming language, entirely written in awk, a fast text processing programming language. However, the main objective remained introducing socket communication to brainfuck pro- gramming language. In order to achieve that goal, we have improved the brainfuck language with a byte long instruction through which it is allowed socket communication. For that, we have advanced a series of procedures in order to test the compatibility of our brainfuck interpreter. Moreover, we have maintained brainfucks minimalism, which is one of the special char- acteristics of this programming language. In the end, we succeeded to map a minimalistic programming language to the client-server paradigm. 2010 Mathematics Subject Classification. 68N15 - Programming languages, 68N20 - Compilers and interpreters. Key words and phrases. brainfuck, socket, interpreter, esoteric languages. 1. Introduction This paper describes a simple interpreter for the brainfuck (BF) esoteric programming language, written in AWK. It is compatible with almost any version of AWK that is supplied within UNIX systems. The interpreter illustrates the use of AWK in implementing small programs using BF language, mainly for proof of concept reasons. 1.1. Motivation. Even if BF is known for its extreme minimalism and it is designed to challenge programmers, it is not usually suitable for practical use. However, the motivation of developing such an application comes from the usage of a simple and easy syntax which can help programmers to deeply understand other programming languages and besides that, other programming paradigms. -

The Intercal Programming Language Revised Reference Manual
THE INTERCAL PROGRAMMING LANGUAGE REVISED REFERENCE MANUAL Donald R. Woods and James M. Lyon C-INTERCAL revisions: Louis Howell and Eric S. Raymond Copyright (C) 1973 by Donald R. Woods and James M. Lyon Copyright (C) 1996 by Eric S. Raymond Redistribution encouragedunder GPL (This version distributed with C-INTERCAL 0.15) -1- 1. INTRODUCTION The names you are about to ignore are true. However, the story has been changed significantly.Any resemblance of the programming language portrayed here to other programming languages, living or dead, is purely coincidental. 1.1 Origin and Purpose The INTERCAL programming language was designed the morning of May 26, 1972 by Donald R. Woods and James M. Lyon, at Princeton University.Exactly when in the morning will become apparent in the course of this manual. Eighteen years later (give ortakeafew months) Eric S. Raymond perpetrated a UNIX-hosted INTERCAL compiler as a weekend hack. The C-INTERCAL implementation has since been maintained and extended by an international community of technomasochists, including Louis Howell, Steve Swales, Michael Ernst, and Brian Raiter. (There was evidently an Atari implementation sometime between these two; notes on it got appended to the INTERCAL-72 manual. The culprits have sensibly declined to identify themselves.) INTERCAL was inspired by one ambition: to have a compiler language which has nothing at all in common with anyother major language. By ’major’ was meant anything with which the authors were at all familiar,e.g., FORTRAN, BASIC, COBOL, ALGOL, SNOBOL, SPITBOL, FOCAL, SOLVE, TEACH, APL, LISP,and PL/I. For the most part, INTERCAL has remained true to this goal, sharing only the basic elements such as variables, arrays, and the ability to do I/O, and eschewing all conventional operations other than the assignment statement (FORTRAN "="). -
Trinary CPE Report
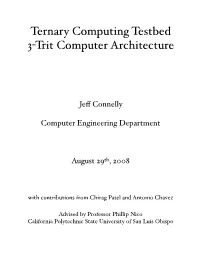
Ternary Computing Testbed 3!Trit Computer Architecture Je" Connelly Computer Engineering Department August 29th, 2008 with contributions from Chirag Patel and Antonio Chavez Advised by Professor Phillip Nico California Polytechnic State University of San Luis Obispo Table of Contents 1. Introduction 1 1.1. Method 1 1.2. Plan 2 1.3. Team and Individual Responsibilities 2 1.3.1. Jeff Connelly 2 1.3.2. Antonio Chavez 2 1.3.3. Chirag Patel 3 2. Background Theory 3 2.1. Base 3 3 2.1.1. Compared to Analog 3 2.1.2. Compared to Digital 4 2.1.3. Compared to Base e 5 2.1.4. Trits, Tribbles, and Trytes 7 2.1.5. Base 9 and 27 9 2.1.6. Text 10 2.2. Logic and Arithmetic 10 3. Application Description 10 3.1. Christmas Lights Game 10 3.2. Guessing Game 11 4. Architecture Description 11 4.1. Power Supply 12 4.2. Instruction Memory 13 4.2.1. Experimental Results 16 4.3. Program Counter 16 4.4. Clock Generator 17 4.5. Processor 18 4.5.1. Registers 18 4.5.2. Input and Output 19 4.5.3. 3-Trit Instruction Set 20 4.5.4. LWI Instruction Example (also known as TCA0) 21 4.5.5. CMP Instruction 25 4.5.5.1. ALU 26 4.5.5.2. CMP Instruction Example 29 4.5.6. BE Instruction 31 4.5.6.1. BE Instruction Example 32 4.5.7. Guessing Game Program 33 5. Evaluation 38 6. Conclusion and Future Directions 39 7. -

Math Symbol Tables
APPENDIX A Math symbol tables A.1 Hebrew and Greek letters Hebrew letters Type Typeset \aleph ℵ \beth ℶ \daleth ℸ \gimel ℷ © Springer International Publishing AG 2016 481 G. Grätzer, More Math Into LATEX, DOI 10.1007/978-3-319-23796-1 482 Appendix A Math symbol tables Greek letters Lowercase Type Typeset Type Typeset Type Typeset \alpha \iota \sigma \beta \kappa \tau \gamma \lambda \upsilon \delta \mu \phi \epsilon \nu \chi \zeta \xi \psi \eta \pi \omega \theta \rho \varepsilon \varpi \varsigma \vartheta \varrho \varphi \digamma ϝ \varkappa Uppercase Type Typeset Type Typeset Type Typeset \Gamma Γ \Xi Ξ \Phi Φ \Delta Δ \Pi Π \Psi Ψ \Theta Θ \Sigma Σ \Omega Ω \Lambda Λ \Upsilon Υ \varGamma \varXi \varPhi \varDelta \varPi \varPsi \varTheta \varSigma \varOmega \varLambda \varUpsilon A.2 Binary relations 483 A.2 Binary relations Type Typeset Type Typeset < < > > = = : ∶ \in ∈ \ni or \owns ∋ \leq or \le ≤ \geq or \ge ≥ \ll ≪ \gg ≫ \prec ≺ \succ ≻ \preceq ⪯ \succeq ⪰ \sim ∼ \approx ≈ \simeq ≃ \cong ≅ \equiv ≡ \doteq ≐ \subset ⊂ \supset ⊃ \subseteq ⊆ \supseteq ⊇ \sqsubseteq ⊑ \sqsupseteq ⊒ \smile ⌣ \frown ⌢ \perp ⟂ \models ⊧ \mid ∣ \parallel ∥ \vdash ⊢ \dashv ⊣ \propto ∝ \asymp ≍ \bowtie ⋈ \sqsubset ⊏ \sqsupset ⊐ \Join ⨝ Note the \colon command used in ∶ → 2, typed as f \colon x \to x^2 484 Appendix A Math symbol tables More binary relations Type Typeset Type Typeset \leqq ≦ \geqq ≧ \leqslant ⩽ \geqslant ⩾ \eqslantless ⪕ \eqslantgtr ⪖ \lesssim ≲ \gtrsim ≳ \lessapprox ⪅ \gtrapprox ⪆ \approxeq ≊ \lessdot