Public Access Computers, Libraries, and the Poor: Do Neighborhood Factors Make a Difference?
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Foundation API Client Library PHP – Usage Examples By: Juergen Rolf Revision Version: 1.2
Foundation API Client Library PHP – Usage Examples By: Juergen Rolf Revision Version: 1.2 Revision Date: 2019-09-17 Company Unrestricted Foundation API Client Library PHP – Installation Guide Document Information Document Details File Name MDG Foundation API Client Library PHP - Usage Examples_v1_2 external.docx Contents Usage Examples and Tutorial introduction for the Foundation API Client Library - PHP Author Juergen Rolf Version 1.2 Date 2019-09-17 Intended Audience This document provides a few examples helping the reader to understand the necessary mechanisms to request data from the Market Data Gateway (MDG). The intended audience are application developers who want to get a feeling for the way they can request and receive data from the MDG. Revision History Revision Date Version Notes Author Status 2017-12-04 1.0 Initial Release J. Rolf Released 2018-03-27 1.1 Adjustments for external J. Rolf Released release 2019-09-17 1.2 Minor bugfixes J. Ockel Released References No. Document Version Date 1. Quick Start Guide - Market Data Gateway (MDG) 1.1 2018-03-27 APIs external 2. MDG Foundation API Client Library PHP – Installation 1.2 2019-09-17 Guide external Company Unrestricted Copyright © 2018 FactSet Digital Solutions GmbH. All rights reserved. Revision Version 1.2, Revision Date 2019-09-17, Author: Juergen Rolf www.factset.com | 2 Foundation API Client Library PHP – Installation Guide Table of Contents Document Information ............................................................................................................................ -
Chapter 6: the Linker
6. The Linker 6-1 Chapter 6: The Linker References: • Brian W. Kernighan / Dennis M. Ritchie: The C Programming Language, 2nd Ed. Prentice-Hall, 1988. • Samuel P. Harbison / Guy L. Steele Jr.: C — A Reference Manual, 4th Ed. Prentice-Hall, 1995. • Online Documentation of Microsoft Visual C++ 6.0 (Standard Edition): MSDN Library: Visual Studio 6.0 release. • Horst Wettstein: Assemblierer und Binder (in German). Carl Hanser Verlag, 1979. • Peter Rechenberg, Gustav Pomberger (Eds.): Informatik-Handbuch (in German). Carl Hanser Verlag, 1997. Kapitel 12: Systemsoftware (H. M¨ossenb¨ock). Stefan Brass: Computer Science III Universit¨atGiessen, 2001 6. The Linker 6-2 Overview ' $ 1. Introduction (Overview) & % 2. Object Files, Libraries, and the Linker 3. Make 4. Dynamic Linking Stefan Brass: Computer Science III Universit¨atGiessen, 2001 6. The Linker 6-3 Introduction (1) • Often, a program consists of several modules which are separately compiled. Reasons are: The program is large. Even with fast computers, editing and compiling a single file with a million lines leads to unnecessary delays. The program is developed by several people. Different programmers cannot easily edit the same file at the same time. (There is software for collaborative work that permits that, but it is still a research topic.) A large program is easier to understand if it is divided into natural units. E.g. each module defines one data type with its operations. Stefan Brass: Computer Science III Universit¨atGiessen, 2001 6. The Linker 6-4 Introduction (2) • Reasons for splitting a program into several source files (continued): The same module might be used in different pro- grams (e.g. -

Message from the Editor
Article Reading Qualitative Studies Margarete Sandelowski University of North Carolina at Chapel Hill Chapel Hill, North Carolina, USA Julie Barroso University of North Carolina at Chapel Hill Chapel Hill, North Carolina, USA © 2002 Sandelowski et al. This is an Open Access article distributed under the terms of the Creative Commons Attribution License (http://creativecommons.org/licenses/by/2.0), which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited. Abstract In this article, the authors hope to shift the debate in the practice disciplines concerning quality in qualitative research from a preoccupation with epistemic criteria toward consideration of aesthetic and rhetorical concerns. They see epistemic criteria as inevitably including aesthetic and rhetorical concerns. The authors argue here for a reconceptualization of the research report as a literary technology that mediates between researcher/writer and reviewer/reader. The evaluation of these reports should thus be treated as occasions in which readers seek to make texts meaningful, rather than for the rigid application of standards and criteria. The authors draw from reader-response theories, literature on rhetoric and representation in science, and findings from an on-going methodological research project involving the appraisal of a set of qualitative studies. Keywords: Reader-response, reading, representation, rhetoric, qualitative research, quality criteria, writing Acknowledgments: We thank the members of -
HP Openvms Utility Routines Manual
HP OpenVMS Utility Routines Manual Order Number: BA554-90019 June 2010 This manual describes the OpenVMS utility routines, a set of routines that provide a programming interface to various OpenVMS utilities. Revision/Update Information: This manual supersedes the HP OpenVMS Utility Routines Manual, OpenVMS Alpha Version 8.3. Software Version: OpenVMS Version 8.4 for Integrity servers OpenVMS Alpha Version 8.4 Hewlett-Packard Company Palo Alto, California © Copyright 2010 Hewlett-Packard Development Company, L.P. Confidential computer software. Valid license from HP required for possession, use or copying. Consistent with FAR 12.211 and 12.212, Commercial Computer Software, Computer Software Documentation, and Technical Data for Commercial Items are licensed to the U.S. Government under vendor’s standard commercial license. The information contained herein is subject to change without notice. The only warranties for HP products and services are set forth in the express warranty statements accompanying such products and services. Nothing herein should be construed as constituting an additional warranty. HP shall not be liable for technical or editorial errors or omissions contained herein. Intel and Itanium are trademarks or registered trademarks of Intel Corporation or its subsidiaries in the United States and other countries. ZK4493 The HP OpenVMS documentation set is available on CD. This document was prepared using DECdocument, Version 3.3-1B. Contents Preface ............................................................ xvii 1 Introduction to Utility Routines 2 Access Control List (ACL) Editor Routine 2.1 Introduction to the ACL Editor Routine ........................... ACL–1 2.2 Using the ACL Editor Routine: An Example ....................... ACL–1 2.3 ACL Editor Routine . ........................................ ACL–2 ACLEDIT$EDIT ........................................... -

The Programming Language Concurrent Pascal
IEEE TRANSACTIONS ON SOFTWARE ENGINEERING, VOL. SE-I, No.2, JUNE 1975 199 The Programming Language Concurrent Pascal PER BRINCH HANSEN Abstract-The paper describes a new programming language Disk buffer for structured programming of computer operating systems. It e.lt tends the sequential programming language Pascal with concurx:~t programming tools called processes and monitors. Section I eltplains these concepts informally by means of pictures illustrating a hier archical design of a simple spooling system. Section II uses the same enmple to introduce the language notation. The main contribu~on of Concurrent Pascal is to extend the monitor concept with an .ex Producer process Consumer process plicit hierarchy Of access' rights to shared data structures that can Fig. 1. Process communication. be stated in the program text and checked by a compiler. Index Terms-Abstract data types, access rights, classes, con current processes, concurrent programming languages, hierarchical operating systems, monitors, scheduling, structured multiprogram ming. Access rights Private data Sequential 1. THE PURPOSE OF CONCURRENT PASCAL program A. Background Fig. 2. Process. INCE 1972 I have been working on a new programming .. language for structured programming of computer S The next picture shows a process component in more operating systems. This language is called Concurrent detail (Fig. 2). Pascal. It extends the sequential programming language A process consists of a private data structure and a Pascal with concurrent programming tools called processes sequential program that can operate on the data. One and monitors [1J-[3]' process cannot operate on the private data of another This is an informal description of Concurrent Pascal. -
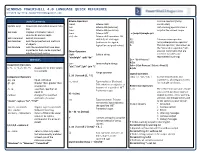
WINDOWS POWERSHELL 4.0 LANGUAGE QUICK REFERENCE Created By
WINDOWS POWERSHELL 4.0 LANGUAGE QUICK REFERENCE Created by http://powershellmagazine.com Useful Commands Bitwise Operators , Comma operator (Array -band Bitwise AND constructor) Update-Help Downloads and installs newest help -bor Bitwise OR (inclusive) . Dot-sourcing operator runs a files -bxor Bitwise OR (exclusive) script in the current scope Get-Help Displays information about -bnot Bitwise NOT . c:\scripts\sample.ps1 commands and concepts -shl, -shr Bitwise shift operators. Bit Get-Command Gets all commands shift left, bit shift right $( ) Subexpression operator Get-Member Gets the properties and methods (arithmetic for signed, @( ) Array subexpression operator of objects logical for unsigned values) & The call operator, also known as Get-Module Gets the modules that have been the "invocation operator," lets imported or that can be imported Other Operators you run commands that are into the current session -Split Splits a string stored in variables and “abcdefghi” -split “de” represented by strings. Operators $a = "Get-Process" -join Joins multiple strings & $a Assignment Operators “abc”,”def”,”ghi” -join “;” $sb = { Get-Process | Select –First 2 } =, +=, -=, *=, /=, %=, ++, -- Assigns one or more values & $sb to a variable .. Range operator Logical Operators 1..10 | foreach {$_ * 5} Comparison Operators -and, -or, -xor, -not, ! Connect expressions and -eq, -ne Equal, not equal statements, allowing you to test -is, -isnot Type evaluator (Boolean). -gt, -ge Greater than, greater than for multiple conditions Tells whether an object is an or equal to Redirection Operators instance of a specified .NET -lt, -le Less than, less than or >, >> The redirection operators enable Framework type. equal to you to send particular types of 42 –is [int] -replace changes the specified output (success, error, warning, elements of a value verbose, and debug) to files and -as Type convertor. -

C Programming Tutorial
C Programming Tutorial C PROGRAMMING TUTORIAL Simply Easy Learning by tutorialspoint.com tutorialspoint.com i COPYRIGHT & DISCLAIMER NOTICE All the content and graphics on this tutorial are the property of tutorialspoint.com. Any content from tutorialspoint.com or this tutorial may not be redistributed or reproduced in any way, shape, or form without the written permission of tutorialspoint.com. Failure to do so is a violation of copyright laws. This tutorial may contain inaccuracies or errors and tutorialspoint provides no guarantee regarding the accuracy of the site or its contents including this tutorial. If you discover that the tutorialspoint.com site or this tutorial content contains some errors, please contact us at [email protected] ii Table of Contents C Language Overview .............................................................. 1 Facts about C ............................................................................................... 1 Why to use C ? ............................................................................................. 2 C Programs .................................................................................................. 2 C Environment Setup ............................................................... 3 Text Editor ................................................................................................... 3 The C Compiler ............................................................................................ 3 Installation on Unix/Linux ............................................................................ -

Library 4Q 2010
Library Anchorage: Performance. Value. Results. Mission Deliver opportunities for education, information, and enrichment for Municipal residents. Core Services • Education: foundational and self-directed • Information: materials, research assistance and instruction • Technology: computing access and services Accomplishment Goals • Increase opportunities for our children’s success when they enter school by teaching the foundations of reading, social skills and, creative skills through early learning educational activities. • Improve civic engagement, cultural enrichment, and enhance the quality of life for all Anchorage residents through provision of life-long educational services including library materials, online resources and programs/events. • Improve economic advancement by providing equitable access to computing equipment and resources and improve public safety by providing safe and stimulating places for teens and clean, well-maintained buildings for all. Performance Measures Measure #1: Increase library use and performance in relation to national standards Note: 2010 data for Measure # 1 will not be available until the Public Library Data Service Statistical Report is published (June 2011). The PLDS Statistical Report, published annually, collects information from more than 800 public libraries across the United States and Canada on finances, library resources, annual use figures and technology. 2010 per capita statistics are based on a population estimate of 280,000. US Census information will be available first quarter of 2011. 2010 expenditures will not be available until March after the fiscal year is closed. A. Number of computers available for public use 2088 – 19% below basic standard 1A. Number of Computers Available to the Public 200 150 100 50 0 2005 2006 2007 2008 2009 2010 B. Number of computers available for public use 2088 – 19% below basic standard 1A. -

Toward a New Service Model Jim Alderman University of North Florida, [email protected]
University of North Florida UNF Digital Commons Library Commons Project Thomas G. Carpenter Library 1-2011 Toward a New Service Model Jim Alderman University of North Florida, [email protected] Follow this and additional works at: http://digitalcommons.unf.edu/library_commons Part of the Library and Information Science Commons Suggested Citation Alderman, Jim, "Toward a New Service Model" (2011). Library Commons Project. 1. http://digitalcommons.unf.edu/library_commons/1 This Article is brought to you for free and open access by the Thomas G. Carpenter Library at UNF Digital Commons. It has been accepted for inclusion in Library Commons Project by an authorized administrator of UNF Digital Commons. For more information, please contact Digital Projects. © 1-2011 All Rights Reserved Toward a New Service Model (January 2011) Report by Jim Alderman, University Librarian, Reference and Instruction The Thomas G. Carpenter Library works with a model of Reference service that is fairly traditional in most senses. The Reference Desk is staffed with a combination of professional librarians and para-professionals a set number of hours per week. When the current library facility was planned, the emphasis was on making more and more computers available to library patrons and to place staff near the computers in order to facilitate service provision. That resulted in a large lab of 129 workstations with a student assistant desk nearby and a smaller lab of 40 workstations with the reference/documents service desk nearby. Subsequent shifts in OPS funding necessitated closing the student desk which in turn resulted in increased traffic at the reference/documents desk. -
Linkers and Loaders Do?
Linkers & Loaders by John R. Levine Table of Contents 1 Table of Contents Chapter 0: Front Matter ........................................................ 1 Dedication .............................................................................................. 1 Introduction ............................................................................................ 1 Who is this book for? ......................................................................... 2 Chapter summaries ............................................................................. 3 The project ......................................................................................... 4 Acknowledgements ............................................................................ 5 Contact us ........................................................................................... 6 Chapter 1: Linking and Loading ........................................... 7 What do linkers and loaders do? ............................................................ 7 Address binding: a historical perspective .............................................. 7 Linking vs. loading .............................................................................. 10 Tw o-pass linking .............................................................................. 12 Object code libraries ........................................................................ 15 Relocation and code modification .................................................... 17 Compiler Drivers ................................................................................. -

MASS C++ Developer's Guide
MASS C++ Developer’s Guide Updated December 11, 2015 1 SETUP 1.1 LOCATION AND PROJECT SETUP MASS C++ can be found on the Dslab computer and the Linux Lab computers. Currently, the RedHat Linux machine Hercules is being used for development. The master copy of MASS C++ can be found in the folder ~/MASS/c++, as shown in figure 1. Figure 1 Location of MASS C++ The codebase is broKen up into several folders. The worK_ folders are currently unused and present only for historical reasons. Development occurs with git branches based on the source directory. The redhat and ubuntu folders contain MaKefiles specific to those systems. The source folder contains the release version of the MASS C++ library. Within the appls directory there are sevral sample MASS applications that can be used to test the MASS C++ library, those applications are: SugarScape, Wave2D, Heat2D, and Conway’s Game of Life. 1.2 GETTING A COPY OF THE CODE FOR DEVELOPMENT To get a local copy of MASS C++, git clone the repository on your machine from: https://bitbucKet.org/mass_library_developers/mass_cpp_core (the repository is private for now) or on the Linux lab machines copy the contents of: /net/metis/home/dslab/MASS/c++/ 2 MAKING CHANGES 2.1 MAKING THE CHANGE If you are unfamiliar with Git, checKout the Git training files for more indepth discussion on how to use in in development. The training files can be found in the ~/Training/GitTraining folder. MASS C++ is using the Git Flow model for updates. To add a feature, branch off of the develop branch. -

Tms320c55x Chip Support Library API Reference Guide (Rev. J)
TMS320C55x Chip Support Library API Reference Guide SPRU433J September 2004 Printed on Recycled Paper IMPORTANT NOTICE Texas Instruments Incorporated and its subsidiaries (TI) reserve the right to make corrections, modifications, enhancements, improvements, and other changes to its products and services at any time and to discontinue any product or service without notice. Customers should obtain the latest relevant information before placing orders and should verify that such information is current and complete. All products are sold subject to TI’s terms and conditions of sale supplied at the time of order acknowledgment. TI warrants performance of its hardware products to the specifications applicable at the time of sale in accordance with TI’s standard warranty. Testing and other quality control techniques are used to the extent TI deems necessary to support this warranty. Except where mandated by government requirements, testing of all parameters of each product is not necessarily performed. TI assumes no liability for applications assistance or customer product design. Customers are responsible for their products and applications using TI components. To minimize the risks associated with customer products and applications, customers should provide adequate design and operating safeguards. TI does not warrant or represent that any license, either express or implied, is granted under any TI patent right, copyright, mask work right, or other TI intellectual property right relating to any combination, machine, or process in which TI products or services are used. Information published by TI regarding third-party products or services does not constitute a license from TI to use such products or services or a warranty or endorsement thereof.