Java Programming Language Family Godiva Scala Processing Aspectj Groovy Javafx Script Einstein J Sharp Judoscript Jasmin Beanshell
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Open Source Used in DNAC-Wide Area Bonjour Magneto
Open Source Used In DNAC-Wide Area Bonjour Magneto Cisco Systems, Inc. www.cisco.com Cisco has more than 200 offices worldwide. Addresses, phone numbers, and fax numbers are listed on the Cisco website at www.cisco.com/go/offices. Text Part Number: 78EE117C99-1090203837 Open Source Used In DNAC-Wide Area Bonjour Magneto 1 This document contains licenses and notices for open source software used in this product. With respect to the free/open source software listed in this document, if you have any questions or wish to receive a copy of any source code to which you may be entitled under the applicable free/open source license(s) (such as the GNU Lesser/General Public License), please contact us at [email protected]. In your requests please include the following reference number 78EE117C99-1090203837 Contents 1.1 javax-activation 1.2.0 1.1.1 Available under license 1.2 metrics-servlets 3.1.0 1.3 mongodb-driver 3.0.4 1.4 jaxb-core 2.3.0 1.4.1 Available under license 1.5 antlr 2.7.6 1.5.1 Available under license 1.6 spring-boot-autoconfigure 1.5.12.RELEASE 1.7 spring-instrument 4.3.19.RELEASE 1.7.1 Available under license 1.8 nimbus-jose-jwt 4.3.1 1.9 javax-inject 1 1.9.1 Available under license 1.10 json-smart 1.3.1 1.11 opentracing-util 0.31.0 1.12 xpp3-min 1.1.3.4.O 1.12.1 Notifications 1.12.2 Available under license 1.13 ojdbc 6 1.14 jax-ws-api 2.3.0 1.15 aspect-j 1.9.2 1.15.1 Available under license 1.16 jetty-util 9.3.27.v20190418 1.17 unirest-java 1.4.5 1.18 jetty-continuation 9.3.27.v20190418 Open Source Used In -
Chapter 12 Calc Macros Automating Repetitive Tasks Copyright
Calc Guide Chapter 12 Calc Macros Automating repetitive tasks Copyright This document is Copyright © 2019 by the LibreOffice Documentation Team. Contributors are listed below. You may distribute it and/or modify it under the terms of either the GNU General Public License (http://www.gnu.org/licenses/gpl.html), version 3 or later, or the Creative Commons Attribution License (http://creativecommons.org/licenses/by/4.0/), version 4.0 or later. All trademarks within this guide belong to their legitimate owners. Contributors This book is adapted and updated from the LibreOffice 4.1 Calc Guide. To this edition Steve Fanning Jean Hollis Weber To previous editions Andrew Pitonyak Barbara Duprey Jean Hollis Weber Simon Brydon Feedback Please direct any comments or suggestions about this document to the Documentation Team’s mailing list: [email protected]. Note Everything you send to a mailing list, including your email address and any other personal information that is written in the message, is publicly archived and cannot be deleted. Publication date and software version Published December 2019. Based on LibreOffice 6.2. Using LibreOffice on macOS Some keystrokes and menu items are different on macOS from those used in Windows and Linux. The table below gives some common substitutions for the instructions in this chapter. For a more detailed list, see the application Help. Windows or Linux macOS equivalent Effect Tools > Options menu LibreOffice > Preferences Access setup options Right-click Control + click or right-click -
Administration and Configuration Guide
Red Hat JBoss Data Virtualization 6.4 Administration and Configuration Guide This guide is for administrators. Last Updated: 2018-09-26 Red Hat JBoss Data Virtualization 6.4 Administration and Configuration Guide This guide is for administrators. Red Hat Customer Content Services Legal Notice Copyright © 2018 Red Hat, Inc. This document is licensed by Red Hat under the Creative Commons Attribution-ShareAlike 3.0 Unported License. If you distribute this document, or a modified version of it, you must provide attribution to Red Hat, Inc. and provide a link to the original. If the document is modified, all Red Hat trademarks must be removed. Red Hat, as the licensor of this document, waives the right to enforce, and agrees not to assert, Section 4d of CC-BY-SA to the fullest extent permitted by applicable law. Red Hat, Red Hat Enterprise Linux, the Shadowman logo, JBoss, OpenShift, Fedora, the Infinity logo, and RHCE are trademarks of Red Hat, Inc., registered in the United States and other countries. Linux ® is the registered trademark of Linus Torvalds in the United States and other countries. Java ® is a registered trademark of Oracle and/or its affiliates. XFS ® is a trademark of Silicon Graphics International Corp. or its subsidiaries in the United States and/or other countries. MySQL ® is a registered trademark of MySQL AB in the United States, the European Union and other countries. Node.js ® is an official trademark of Joyent. Red Hat Software Collections is not formally related to or endorsed by the official Joyent Node.js open source or commercial project. -

This Article Appeared in a Journal Published by Elsevier. the Attached Copy Is Furnished to the Author for Internal Non-Commerci
This article appeared in a journal published by Elsevier. The attached copy is furnished to the author for internal non-commercial research and education use, including for instruction at the authors institution and sharing with colleagues. Other uses, including reproduction and distribution, or selling or licensing copies, or posting to personal, institutional or third party websites are prohibited. In most cases authors are permitted to post their version of the article (e.g. in Word or Tex form) to their personal website or institutional repository. Authors requiring further information regarding Elsevier’s archiving and manuscript policies are encouraged to visit: http://www.elsevier.com/copyright Author's personal copy Computer Languages, Systems & Structures 37 (2011) 132–150 Contents lists available at ScienceDirect Computer Languages, Systems & Structures journal homepage: www.elsevier.com/locate/cl Reconciling method overloading and dynamically typed scripting languages Alexandre Bergel à Pleiad Group, Computer Science Department (DCC), University of Chile, Santiago, Chile article info abstract Article history: The Java virtual machine (JVM) has been adopted as the executing platform by a large Received 13 July 2010 number of dynamically typed programming languages. For example, Scheme, Ruby, Received in revised form Javascript, Lisp, and Basic have been successfully implemented on the JVM and each is 28 February 2011 supported by a large community. Interoperability with Java is one important require- Accepted 15 March 2011 ment shared by all these languages. We claim that the lack of type annotation in interpreted dynamic languages makes Keywords: this interoperability either flawed or incomplete in the presence of method overloading. Multi-language system We studied 17 popular dynamically typed languages for JVM and .Net, none of them Interoperability were able to properly handle the complexity of method overloading. -

Design and Implementation of a Behaviorally Typed Programming System for Web Services
Universidade Nova de Lisboa Faculdade de Cienciasˆ e Tecnologia Departamento de Informatica´ Dissertac¸ao˜ de Mestrado Mestrado em Engenharia Informatica´ Design and Implementation of a Behaviorally Typed Programming System for Web Services Filipe David Oliveira Militao˜ (26948) Lisboa (2008) Universidade Nova de Lisboa Faculdade de Cienciasˆ e Tecnologia Departamento de Informatica´ Dissertac¸ao˜ de Mestrado Design and Implementation of a Behaviorally Typed Programming System for Web Services Filipe David Oliveira Militao˜ (26948) Orientador: Prof. Doutor Lu´ıs Caires J ´uri Presidente: • Doutor Jos´eAlberto Cardoso e Cunha, Professor Catedratico,´ Departamento de Informatica´ da Faculdade de Cienciasˆ e Tecnologia, Universidade Nova de Lisboa. Vogais: • Doutor Francisco Martins, Professor Auxiliar, Departamento de Informatica´ da Faculdade de Ciencias,ˆ Universidade de Lisboa. • Doutor Lu´ısManuel Marques da Costa Caires, Professor Associado, Departa- mento de Informatica´ da Faculdade de Cienciasˆ e Tecnologia, Universidade Nova de Lisboa. Disserta¸c˜aoapresentada na Faculdade de Ciˆenciase Tecnologia da Uni- versidade Nova de Lisboa para a obten¸c˜aodo Grau de Mestre em En- genharia Inform´atica. Lisboa (2008) Acknowledgements This work was partially supported by a CITI/PLM/1001/2007 research grant. v Summary The growing use of the Internet as a global infrastructure for communication between dis- tributed applications is leading to the development of a considerable amount of technologies to ease the deployment, description and data exchange among services and thus improve their in- teroperability. There is also a growing interest in the use of the “software as a service” business model where a software vendor develops and hosts applications to be used by its clients over the Internet. -
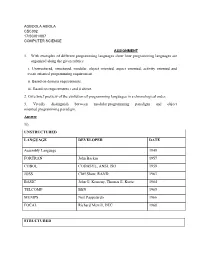
1. with Examples of Different Programming Languages Show How Programming Languages Are Organized Along the Given Rubrics: I
AGBOOLA ABIOLA CSC302 17/SCI01/007 COMPUTER SCIENCE ASSIGNMENT 1. With examples of different programming languages show how programming languages are organized along the given rubrics: i. Unstructured, structured, modular, object oriented, aspect oriented, activity oriented and event oriented programming requirement. ii. Based on domain requirements. iii. Based on requirements i and ii above. 2. Give brief preview of the evolution of programming languages in a chronological order. 3. Vividly distinguish between modular programming paradigm and object oriented programming paradigm. Answer 1i). UNSTRUCTURED LANGUAGE DEVELOPER DATE Assembly Language 1949 FORTRAN John Backus 1957 COBOL CODASYL, ANSI, ISO 1959 JOSS Cliff Shaw, RAND 1963 BASIC John G. Kemeny, Thomas E. Kurtz 1964 TELCOMP BBN 1965 MUMPS Neil Pappalardo 1966 FOCAL Richard Merrill, DEC 1968 STRUCTURED LANGUAGE DEVELOPER DATE ALGOL 58 Friedrich L. Bauer, and co. 1958 ALGOL 60 Backus, Bauer and co. 1960 ABC CWI 1980 Ada United States Department of Defence 1980 Accent R NIS 1980 Action! Optimized Systems Software 1983 Alef Phil Winterbottom 1992 DASL Sun Micro-systems Laboratories 1999-2003 MODULAR LANGUAGE DEVELOPER DATE ALGOL W Niklaus Wirth, Tony Hoare 1966 APL Larry Breed, Dick Lathwell and co. 1966 ALGOL 68 A. Van Wijngaarden and co. 1968 AMOS BASIC FranÇois Lionet anConstantin Stiropoulos 1990 Alice ML Saarland University 2000 Agda Ulf Norell;Catarina coquand(1.0) 2007 Arc Paul Graham, Robert Morris and co. 2008 Bosque Mark Marron 2019 OBJECT-ORIENTED LANGUAGE DEVELOPER DATE C* Thinking Machine 1987 Actor Charles Duff 1988 Aldor Thomas J. Watson Research Center 1990 Amiga E Wouter van Oortmerssen 1993 Action Script Macromedia 1998 BeanShell JCP 1999 AngelScript Andreas Jönsson 2003 Boo Rodrigo B. -

Red5 Documentation Daniel Rossi Red5 Documentation Daniel Rossi Copyright © 2007 Daniel Rossi
Red5 Documentation Daniel Rossi Red5 Documentation Daniel Rossi Copyright © 2007 Daniel Rossi Abstract Table of Contents .................................................................................................................................. 1 .................................................................................................................................. 2 Frequently Asked Questions ................................................................................... 2 Project Management ...................................................................................... 6 Server Side Development ............................................................................... 6 Codecs/Media integration ............................................................................... 7 Client Side/API Testing ................................................................................. 7 Branding/Logo/Website .................................................................................. 7 Documentation ............................................................................................. 7 .................................................................................................................................. 9 How to build with eclipse ...................................................................................... 9 ................................................................................................................................ 10 ............................................................................................................................... -

Pwning Your Java Messaging with Deserialization Vulnerabilities Matthias Kaiser About Me
Pwning Your Java Messaging With Deserialization Vulnerabilities Matthias Kaiser About me . Head of Vulnerability Research at Code White in Ulm, Germany . Software Dev/Architect in the past, enjoying technical security for 7 years now . Specialized on Java Security . Found bugs in products of Oracle, IBM, VMware, SAP, Redhat, Symantec, Apache, Adobe, etc. Recently looking more into the Windows world and client-side stuff @matthias_kaiser 08/03/2016 2 1 Motivation Introduction to Java‘s 2 Native Serialization 3 The Java Message Service 4 Attacking JMS 5 Introducing JMET 6 JMET in Action 7 Conclusion 08/03/2016 3 Motivation . During my research time I looked at all kinds of products running on Java . Several Java core technologies rely heavily on serialization (RMI, JMX) . Furthermore the Java Message Service (JMS) requires the use of Java’s Serialization . Previous security research on Java Message Service (JMS): . “A Pentesters Guide to Hacking ActiveMQ Based JMS Applications” + JMSDigger Tool by Gursev Singh Kalra of McAfee Foundstone Professional Services (2014) . “Your Q is my Q” by G. Geshev of MWR InfoSecurity (2014) . I haven’t found any research on attacking Java Messaging Service using (de)-serialization . That’s the reason why I’m here 08/03/2016 4 Disclaimer . This talk continues my research on Java Deserialization Vulnerabilities . Therefore I won‘t cover all the technical details about finding and exploiting deserialization vulnerabilities which I have shown in my other talks . If you want to dig deeper, you should look at: . “Deserialize My Shorts: Or How I Learned To Start Worrying and Hate Java Object Deserialization” by Chis Frohoff (OWASP-SD 2016) . -
Magicdraw Macro Engine User Guide
MACRO ENGINE USER GUIDE version 17.0 No Magic, Inc. 2011 All material contained herein is considered proprietary information owned by No Magic, Inc. and is not to be shared, copied, or reproduced by any means. All information copyright 2009-2011 by No Magic, Inc. CONTENTS MACRO ENGINE 2 1. Introduction 2 2. Working with Macro Engine 2 2.1 Selecting a Default Macro Language 2 2.2 Creating a Macro 4 2.3 Adding a Macro, Entering and Editing Macro Information 5 2.3.1 Opening Macro Information Dialog 5 2.3.2 Adding a Macro and Its Information 7 2.3.3 Editing Macro Information 11 2.3.4 Macro Information Dialog Mnemonic Keys 12 2.4 Deleting and Executing Macros 12 2.4.1 Deleting a Macro 12 2.4.2 Executing a Macro 13 2.4.3 Organize Macros Dialog Mnemonic Keys 15 2.5 Macro Keyboard Shortcuts 17 2.5.1 Assigning a Keyboard Shortcut to a Macro 19 2.5.2 Removing a Keyboard Shortcut from a Macro 19 2.6 Opaque Objects 20 2.6.1 Getting an Opaque Object 20 2.6.2 Getting Element Property Values 21 2.6.3 Setting Element Property Values 22 2.6.4 Getting the Child of an Element 25 2.6.5 Getting the Owner of an Element 26 2.6.6 Creating a New Element 26 2.6.7 Creating a Relationship Between Elements 26 2.6.8 Removing an Element 26 2.6.9 Adding a Stereotype to an Element 27 2.6.10 Removing a Stereotype from an Element 27 2.6.11 Printing Element Details 27 2.7 Recording Macros 28 3. -

Christian Schneider Alvaro Muñoz
Chris;an Schneider Whitehat Hacker & Developer Serial Killer: Silently Pwning Freelancer @cschneider4711 Your Java Endpoints Alvaro Muñoz Principal Security Researcher HPE Security For@fy @pwntester Why this talk? Java deserializa@on aEacks have been known for years Rela@vely new GadGet in Apache Commons-Collec/ons made the topic also available to mainstream (dev) audience in 2015 Some inaccurate advice to protect your applica@ons is makinG the rounds In this talk we’ll demonstrate the weakness of this advice by … … showing you new RCE gadgets … showing you bypasses We’ll Give advice how to spot this vulnerability and its GadGets durinG … … code reviews (i.e. showinG you what to look for) … pentests (i.e. how to Generically test for such issues) 2 Standing on the Shoulder of Giants… Spring AOP (by Wouter Coekaerts, public exploit: @pwntester in 2011) AMF DoS (by Wouter Coekaerts in 2011) Commons-fileupload (by Arun Babu NeelicaEu in 2013) Groovy (by cpnrodzc7 / @frohoff in 2015) Commons-Collec;ons (by @frohoff and @gebl in 2015) Spring Beans (by @frohoff and @gebl in 2015) Serial DoS (by Wouter Coekaerts in 2015) SpringTx (by @zerothinkinG in 2016) JDK7 (by @frohoff in 2016) Probably more we are forge7ng and more to come in few minutes … 3 What is Java Serializa;on again? TakinG a snapshot of an object graph as a byte stream that can be used to reconstruct the object Graph to its oriGinal state Only object data is serialized, not the code The code sits on the ClassPath of the (de)serializinG end Developers can customize this serializa@on/deserializa@on process Individual object/state serializa@on via .writeObject() / .writeReplace() / .writeExternal() methods Individual object/state re-construc@on on deserializinG end via .readObject() / .readResolve() / .readExternal() methods (and more) 4 AWack SurFace Usages of Java serializa@on in protocols/formats/products: RMI (Remote Method Invoca@on) Android JMX (Java Management Extension) AMF (Ac@on Message Format) JMS (Java MessaginG System) JSF ViewState SprinG Service Invokers WebLogic T3 HTTP, JMS, RMI, etc. -

Implementing Parallel Algorithms Swarm – Multithreaded Framework
Implementing Parallel Algorithms Julius Hrivnac, LAL Swarm – Multithreaded Framework continuation of Minerva project BasicBasic principles: principles: ➢➢multithreadingmultithreading should should not not obscure obscure the the implementation implementation of of algorithms algorithms TwoTwo levels levels of of parallelism: parallelism: ➢➢aa user user should should see see the the program program logic, logic, not not parallelisation parallelisation artifacts artifacts ➢➢parallelparallel Consumers/Producers Consumers/Producers ➢➢threadthread scheduling scheduling and and balancing balancing should should be be automatic automatic ➢➢Fork&JoinFork&Join algorithms algorithms on on parallel parallel containers containers Uses:Uses: ➢➢JavaJava 7 7 ➢ObjectBrowser Architecture:Architecture: ➢ObjectBrowser ➢➢Colt ➢➢basedbased on on the the classical classical Producer-Consumer Producer-Consumer InfoBus InfoBus pattern pattern Colt ➢➢JUNG ➢➢allall BusMember BusMemberss declare declare their their input/output input/output BusItem BusItem types, types, including including possible possible multiplicity multiplicity JUNG ➢➢BeanShell (one(one BusItem BusItem processed processed by by several several Consumers) Consumers) BeanShell ➢➢FreeHEP ➢➢pluggablepluggable Balancer Balancer orchestrates orchestrates Producer/Consumer Producer/Consumer threads threads to to optimize optimize performance performance FreeHEP ➢➢GenericGeneric Collections Collections ➢➢ConcurrentConcurrent ➢➢Log4JLog4J ➢➢GroovyGroovy ➢➢ScalaScala ➢Clojure Design:Design: ➢Clojure -
Apache Ant User Manual Guide – Version 1.6.0 12/29/2003 9:39 AM
Apache Ant User Manual Guide – Version 1.6.0 12/29/2003 9:39 AM Apache Ant User Manual Guide Version 1.6.0 Compiled by: Abdul Habra (www.tek271.com) From: http://ant.apache.org/ 12/2003 Copyright © 2000-2003 Apache Software Foundation. All rights Reserved. 1 of 130 Apache Ant User Manual Guide – Version 1.6.0 12/29/2003 9:39 AM 2 of 130 Apache Ant User Manual Guide – Version 1.6.0 12/29/2003 9:39 AM Contents At A Glance 1 Apache Ant User Manual Authors ............................................................................................................9 2 Feedback and Troubleshooting .............................................................................................................10 3 Introduction.........................................................................................................................................11 4 Installing Ant .......................................................................................................................................12 5 Running Ant ........................................................................................................................................18 6 Using Ant ............................................................................................................................................23 7 Concepts .............................................................................................................................................30 8 Listeners & Loggers..............................................................................................................................86