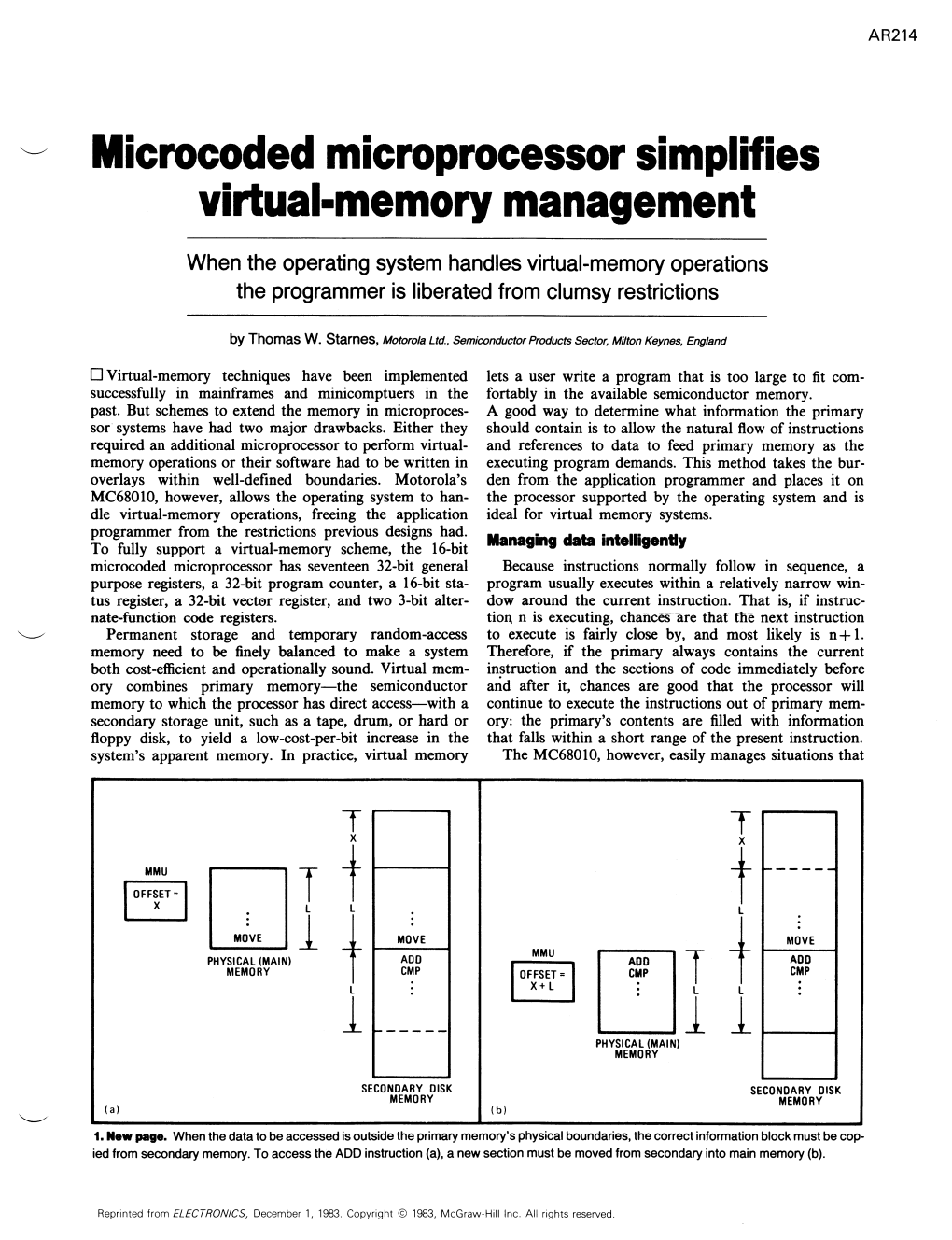
AR214 Microcoded Microprocessor Simplifies Virtual-Memory
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

University of California at Berkeley College of Engineering Department of Electrical Engineering and Computer Science
University of California at Berkeley College of Engineering Department of Electrical Engineering and Computer Science EECS 61C, Fall 2003 Lab 2: Strings and pointers; the GDB debugger PRELIMINARY VERSION Goals To learn to use the gdb debugger to debug string and pointer programs in C. Reading Sections 5.1-5.5, in K&R GDB Reference Card (linked to class page under “resources.”) Optional: Complete GDB documentation (http://www.gnu.org/manual/gdb-5.1.1/gdb.html) Note: GDB currently only works on the following machines: • torus.cs.berkeley.edu • rhombus.cs.berkeley.edu • pentagon.cs.berkeley.edu Please ssh into one of these machines before starting the lab. Basic tasks in GDB There are two ways to start the debugger: 1. In EMACS, type M-x gdb, then type gdb <filename> 2. Run gdb <filename> from the command line The following are fundamental operations in gdb. Please make sure you know the gdb commands for the following operations before you proceed. 1. How do you run a program in gdb? 2. How do you pass arguments to a program when using gdb? 3. How do you set a breakpoint in a program? 4. How do you set a breakpoint which which only occurs when a set of conditions is true (eg when certain variables are a certain value)? 5. How do you execute the next line of C code in the program after a break? 1 6. If the next line is a function call, you'll execute the call in one step. How do you execute the C code, line by line, inside the function call? 7. -

M32R Debugger and Trace
M32R Debugger and Trace TRACE32 Online Help TRACE32 Directory TRACE32 Index TRACE32 Documents ...................................................................................................................... ICD In-Circuit Debugger ................................................................................................................ Processor Architecture Manuals .............................................................................................. M32R ......................................................................................................................................... M32R Debugger and Trace .................................................................................................. 1 Introduction ....................................................................................................................... 4 Brief Overview of Documents for New Users 4 Warning .............................................................................................................................. 5 Quick Start ......................................................................................................................... 6 Troubleshooting ................................................................................................................ 9 SYStem.Up Errors 9 Memory Access Errors 9 FAQ ..................................................................................................................................... 9 CPU specific SYStem Settings and Restrictions .......................................................... -
Mac OS 8 Update
K Service Source Mac OS 8 Update Known problems, Internet Access, and Installation Mac OS 8 Update Document Contents - 1 Document Contents • Introduction • About Mac OS 8 • About Internet Access What To Do First Additional Software Auto-Dial and Auto-Disconnect Settings TCP/IP Connection Options and Internet Access Length of Configuration Names Modem Scripts & Password Length Proxies and Other Internet Config Settings Web Browser Issues Troubleshooting • About Mac OS Runtime for Java Version 1.0.2 • About Mac OS Personal Web Sharing • Installing Mac OS 8 • Upgrading Workgroup Server 9650 & 7350 Software Mac OS 8 Update Introduction - 2 Introduction Mac OS 8 is the most significant update to the Macintosh operating system since 1984. The updated system gives users PowerPC-native multitasking, an efficient desktop with new pop-up windows and spring-loaded folders, and a fully integrated suite of Internet services. This document provides information about Mac OS 8 that supplements the information in the Mac OS installation manual. For a detailed description of Mac OS 8, useful tips for using the system, troubleshooting, late-breaking news, and links for online technical support, visit the Mac OS Info Center at http://ip.apple.com/infocenter. Or browse the Mac OS 8 topic in the Apple Technical Library at http:// tilsp1.info.apple.com. Mac OS 8 Update About Mac OS 8 - 3 About Mac OS 8 Read this section for information about known problems with the Mac OS 8 update and possible solutions. Known Problems and Compatibility Issues Apple Language Kits and Mac OS 8 Apple's Language Kits require an updater for full functionality with this version of the Mac OS. -

PRE LIM INARY KDII-D Processor Manual (PDP-Ll/04)
PRE LIM I N A R Y KDII-D Processor Manual (PDP-ll/04) The information in this document is subject to change without notice and should not be construed as a commitment by Digital Equipment Corporation. Digital Equipment Corporation assumes no responsibility for any errors that may appear in this manual. Copyright C 1975 by Digital Equipment Corporation Written by PDP-II Engineering PREFACE OVE~ALt DESCRIPTION 3 8 0 INsT~UCTION SET 3~1 Introduction 1~2 Addressing ModIs 3.3 Instruction Timing l@4 In~truet1on Dtlcriptlonl le!5 Dlffer~ncei a,tween KOlle and KOllS ]0 6 Programming Diftereneel B~twlen pepita ).7 SUI L~tency Tim@1 CPu OPERlTING 5PECIFICATID~S 5 e 0 DETAILED HARDWARE DESC~ltTION 5.1 IntrOduction 5 m2 Data path Circuitry 5.2g1 General D~serlpt1on 5.2,,2 ALU 5,2 .. 3 Scratch Pad Mtmory 5.2,.3.1 Scratch P~d Circuitry 5.2.3.2 SCrateh P~d Addr~11 MUltlplex.r 5.2.3.3 SCrateh Pad Regilter 5 0 2 .. 4 B J:H'!qilil ter 5.2 .. 4.1 B ReQister CircuItry 5.2 .. 4.2 8 L~G MUltl~lex@r 5,2.5 AMUX 5.2.6 Pfoeellof statuI Word (PSW) 5.3 Con<Htion COd@i 5.3.1 G~neral De~erl~tlon 5.3.2 Carry and overflow Decode 5.3.3 Ayte Multiplexing 5.4 UNIBUS Addf@$5 and Data Interfaces S.4 g 1 U~IBUS Dr1v~rl and ~lee1Vtrl 5.4@2 Bus Addr~s~ Generation 5 8 4111 Internal Addrf$$ D@coder 5 0 4,.4 Bus Data Line Interface S.5 Instruet10n DeCoding 5.5,,1 General De~er1pt1nn 5;5.2 Instruction Re91lt~r 5.5,,3 Instruetlon Decoder 5.5.3 0 1 Doubl~ O~erand InltrYetions 5.5.3.2 Single Operand Inltruetlons 5,5.3.3 Branch In$truetionl 5 8 5.3 6 4 Op~rate rn~truet1ons 5.6 Auil11ary ALU Control 5.6.1 G~ntral Delcrlptlon 5.6.2 COntrol Circuitry 5.6.2.1 Double Op@rand Instructions 5.6.2.2 Singl@ nDef~nd Instruet10ns PaQe 3 5.7 Data Transfer Control 5,7,1 General Descr1ption 5,7,2 Control CIrcuItry 5,7,2,1 Procelsor Cloek Inhibit 5,7,2.2 UNIBUS Synchronization 5,7.2,3 BUs Control 5.7,2.4 MSyN/SSYN Timeout 5,7.2.5 Bus Error. -
Processes, System Calls and More
Processes • A process is an instance of a program running • Modern OSes run multiple processes simultaneously • Very early OSes only ran one process at a time • Examples (can all run simultaneously): - emacs – text editor - firefox – web browser • Non-examples (implemented as one process): - Multiple firefox windows or emacs frames (still one process) • Why processes? - Simplicity of programming - Speed: Higher throughput, lower latency 1 / 43 A process’s view of the world • Each process has own view of machine - Its own address space - Its own open files - Its own virtual CPU (through preemptive multitasking) • *(char *)0xc000 dierent in P1 & P2 • Simplifies programming model - gcc does not care that firefox is running • Sometimes want interaction between processes - Simplest is through files: emacs edits file, gcc compiles it - More complicated: Shell/command, Window manager/app. 2 / 43 Outline 1 Application/Kernel Interface 2 User view of processes 3 Kernel view of processes 3 / 43 System Calls • Systems calls are the interface between processes and the kernel • A process invokes a system call to request operating system services • fork(), waitpid(), open(), close() • Note: Signals are another common mechanism to allow the kernel to notify the application of an important event (e.g., Ctrl-C) - Signals are like interrupts/exceptions for application code 4 / 43 System Call Soware Stack Application 1 5 Syscall Library unprivileged code 4 2 privileged 3 code Kernel 5 / 43 Kernel Privilege • Hardware provides two or more privilege levels (or protection rings) • Kernel code runs at a higher privilege level than applications • Typically called Kernel Mode vs. User Mode • Code running in kernel mode gains access to certain CPU features - Accessing restricted features (e.g. -

NI Vxipc-486 500 Series Lynxos Manual
Full-service, independent repair center -~ ARTISAN® with experienced engineers and technicians on staff. TECHNOLOGY GROUP ~I We buy your excess, underutilized, and idle equipment along with credit for buybacks and trade-ins. Custom engineering Your definitive source so your equipment works exactly as you specify. for quality pre-owned • Critical and expedited services • Leasing / Rentals/ Demos equipment. • In stock/ Ready-to-ship • !TAR-certified secure asset solutions Expert team I Trust guarantee I 100% satisfaction Artisan Technology Group (217) 352-9330 | [email protected] | artisantg.com All trademarks, brand names, and brands appearing herein are the property o f their respective owners. Find the National Instruments VXIpc-486 Model 566 at our website: Click HERE Getting Started with Your NI-VXI™ Software for the VXIpc™-486 Model 500 Series and LynxOS bus September 1995 Edition Part Number 321006A-01 © Copyright 1995 National Instruments Corporation. All Rights Reserved. National Instruments Corporate Headquarters 6504 Bridge Point Parkway Austin, TX 78730-5039 (512) 794-0100 Technical support fax: (800) 328-2203 (512) 794-5678 Branch Offices: Australia 03 9 879 9422, Austria 0662 45 79 90 0, Belgium 02 757 00 20, Canada (Ontario) 519 622 9310, Canada (Québec) 514 694 8521, Denmark 45 76 26 00, Finland 90 527 2321, France 1 48 14 24 24, Germany 089 741 31 30, Hong Kong 2645 3186, Italy 02 48301892, Japan 03 5472 2970, Korea 02 596 7456, Mexico 95 800 010 0793, Netherlands 0348 433466, Norway 32 84 84 00, Singapore 2265886, Spain 91 640 0085, Sweden 08 730 49 70, Switzerland 056 200 51 51, Taiwan 02 377 1200, U.K. -

Memory Management
Memory Management • Peter Rounce - room G06 [email protected] Memory Protection Restrict addresses that an application can access:- • Limits application to its own code and data • Prevents access to other programs and OS • Prevents access to I/O addresses This address restriction is done by Memory Management hardware:- Memory Memory & CPU Address Bus Address Bus Management I/O Interfaces This Memory Management hardware does address translation as well. Memory Protection + Address Translation: Creation of illusion that program has all the memory to itself Logical Memory e.g. for Program X Physical Memory of system Stack Actual memory Unused by mapped by Program X used by Program Program X address translation O/S Data Program Y Code Program, users & CPU’s Physical memory is shared view of memory with other programs/processes used by Program X and with Operating System Solution: have logical addresses used by program and CPU ; have physical addresses to access memory Use Address translation to turn logical address into physical address. Address Translation: basis of Memory Protection and Memory Management MMU Logical address Physical address translation CPU Logical Address Bus MMU Physical Address Bus Memory Bus Error Data bus Logical address Address programmed into code and used by CPU CPU outputs Logical address on to CPU address Bus CPU only knows about Logical addresses Logical address where CPU considers data/instruction to be stored Physical address address where data/instruction is really stored Note:Physical addresses are never stored in the program, only appear on address bus not data bus. MMU = Memory Management Unit Pentium MMU is on same chip as CPU Base-Limit Registers - Memory Protection + Address Translation Several processes J,B,X…. -

RTI Connext DDS Core Libraries Release Notes Version 5.2.0 © 2015 Real-Time Innovations, Inc
RTI Connext DDS Core Libraries Release Notes Version 5.2.0 © 2015 Real-Time Innovations, Inc. All rights reserved. Printed in U.S.A. First printing. June 2015. Trademarks Real-Time Innovations, RTI, NDDS, RTI Data Distribution Service, DataBus, Connext, Micro DDS, the RTI logo, 1RTI and the phrase, “Your Systems. Working as one,” are registered trade- marks, trademarks or service marks of Real-Time Innovations, Inc. All other trademarks belong to their respective owners. Copy and Use Restrictions No part of this publication may be reproduced, stored in a retrieval system, or transmitted in any form (including electronic, mechanical, photocopy, and facsimile) without the prior written per- mission of Real-Time Innovations, Inc. The software described in this document is furnished under and subject to the RTI software license agreement. The software may be used or copied only under the terms of the license agreement. Technical Support Real-Time Innovations, Inc. 232 E. Java Drive Sunnyvale, CA 94089 Phone: (408) 990-7444 Email: [email protected] Website: https://support.rti.com/ Chapter 1 Introduction 14 Chapter 2 System Requirements 2.1 Supported Operating Systems 1 2.2 Requirements when Using Microsoft Visual Studio 3 2.3 Disk and Memory Usage 4 2.4 Networking Support 4 Chapter 2 Transitioning from 5.1 to 5.2 6 Chapter 3 Compatibility 3.1 Wire Protocol Compatibility 7 3.1.1 General Information on RTPS (All Releases) 7 3.1.2 Release-Specific Information for Connext DDS 5.x 7 3.1.2.1 Large Data with Endpoint Discovery 7 3.1.3 Release-Specific -

Why Oracle Database Runs Best on Oracle Linux
Why Oracle Database Runs Best on Oracle Linux White Paper May 6, 2020 | Version 2.2 Copyright © 2020, Oracle and/or its affiliates 1 WHITE PAPER | Why Oracle Database Runs Best on Oracle Linux | Version 2.2 Copyright © 2020, Oracle and/or its affiliates PURPOSE STATEMENT This document describes why the Oracle Linux operating environment is the best operating environment for running the Oracle Database. DISCLAIMER This document in any form, software or printed matter, contains proprietary information that is the exclusive property of Oracle. Your access to and use of this confidential material is subject to the terms and conditions of your Oracle software license and service agreement, which has been executed and with which you agree to comply. This document and information contained herein may not be disclosed, copied, reproduced or distributed to anyone outside Oracle without prior written consent of Oracle. This document is not part of your license agreement nor can it be incorporated into any contractual agreement with Oracle or its subsidiaries or affiliates. This document is for informational purposes only and is intended solely to assist you in planning for the implementation and upgrade of the product features described. It is not a commitment to deliver any material, code, or functionality, and should not be relied upon in making purchasing decisions. The development, release, and timing of any features or functionality described in this document remains at the sole discretion of Oracle. Due to the nature of the product architecture, it may not be possible to safely include all features described in this document without risking significant destabilization of the code. -
C Reference Slides
Reference slides! You ARE responsible for the material on these slides (they’re just taken from the reading anyway). These were the slides that generated the fewest questions in years past (i.e., those you could just read and fully understand.)! CS61C L04 Introduction to C (pt 2) (1)! Garcia, Fall 2011 © UCB! C Strings! • A string in C is just an array of characters.! ! !char string[] = "abc";! • How do you tell how long a string is?! • Last character is followed by a 0 byte (null terminator) !!! int strlen(char s[]) { int n = 0; while (s[n] != 0) n++; return n; } CS61C L04 Introduction to C (pt 2) (2)! Garcia, Fall 2011 © UCB! C String Standard Functions! • int strlen(char *string); • compute the length of string • int strcmp(char *str1, char *str2); • return 0 if str1 and str2 are identical (how is this different from str1 == str2?)! • char *strcpy(char *dst, char *src); • copy the contents of string src to the memory at dst. The caller must ensure that dst has enough memory to hold the data to be copied.! CS61C L04 Introduction to C (pt 2) (3)! Garcia, Fall 2011 © UCB! Administrivia! • Read K&R 6 by the next lecture! • There is a language called D!! • www.digitalmars.com/d/! • Homework expectations! • Readers don’t have time to fix your programs which have to run on lab machines.! • Code that doesn’t compile or fails all of the autograder tests ⇒ 0! CS61C L04 Introduction to C (pt 2) (4)! Garcia, Fall 2011 © UCB! Pointers & Allocation (1/2)! • After declaring a pointer:! int *ptr; !ptr doesn’t actually point to anything yet (it actually points somewhere - but don’t know where!). -
Problem Solving and Troubleshooting in AIX 5L
Front cover Problem Solving and Troubleshooting in AIX 5L Introduction of new problem solving tools and changes in AIX 5L Step by step troubleshooting in real environments Complete guide to the problem determination process HyunGoo Kim JaeYong An John Harrison Tony Abruzzesse KyeongWon Jeong ibm.com/redbooks International Technical Support Organization Problem Solving and Troubleshooting in AIX 5L January 2002 SG24-5496-01 Take Note! Before using this information and the product it supports, be sure to read the general information in “Special notices” on page 439. Second Edition (January 2002) This edition applies to IBM ^ pSeries and RS/6000 Systems for use with the AIX 5L Operating System Version 5.1 and is based on information available in August, 2001. Comments may be addressed to: IBM Corporation, International Technical Support Organization Dept. JN9B Building 003 Internal Zip 2834 11400 Burnet Road Austin, Texas 78758-3493 When you send information to IBM, you grant IBM a non-exclusive right to use or distribute the information in any way it believes appropriate without incurring any obligation to you. © Copyright International Business Machines Corporation 1999-2002. All rights reserved. Note to U.S Government Users – Documentation related to restricted rights – Use, duplication or disclosure is subject to restrictions set forth in GSA ADP Schedule Contract with IBM Corp. Contents Figures . xiii Tables . xv Preface . xvii The team that wrote this redbook. xvii Special notice . xix IBM trademarks . xix Comments welcome. xix Chapter 1. Problem determination introduction. 1 1.1 Problem determination process . 3 1.1.1 Defining the problem . 3 1.1.2 Gathering information from the user . -
Operating Systems : Interrupts, Exceptions, and System Calls
Interrupts, Exceptions, and System Calls Chester Rebeiro IIT Madras OS & Events • OS is event driven – i.e. executes only when there is an interrupt, trap, or system call OS 30 l e v e l e g e 13 l i v User process 1 User process 2 i r P event time 2 Why event driven design? • OS cannot trust user processes – User processes may be buggy or malicious – User process crash should not affect OS • OS needs to guarantee fairness to all user processes – One process cannot ‘hog’ CPU time – Timer interrupts 3 Event Types Events Interrupts Exceptions Hardware Interrupts Software Interrupts 4 Events • Interrupts : raised by hardware or programs to get OS attention – Types • Hardware interrupts : raised by external hardware devices • Software Interrupts : raised by user programs • Exceptions : due to illegal operations 5 Event view of CPU while(fetch next instruction) Current task suspended Execute Instruction Where? If event Execute event yes in handler no 6 Exception & Interrupt Vectors Event occured What to execute next? • Each interrupt/exception provided a number • Number used to index into an Interrupt descriptor table (IDT) • IDT provides the entry point into a interrupt/exception handler • 0 to 255 vectors possible – 0 to 31 used internally – Remaining can be defined by the OS 7 Exception and Interrupt Vectors 8 xv6 Interrupt Vectors • 0 to 31 reserved by Intel • 32 to 63 used for hardware interrupts T_IRQ0 = 32 (added to all hardware IRQs to scale them) • 64 used for system call interrupt ref : traps.h ([31], 3152) 9 Events Events Interrupts Exceptions Hardware Interrupts Software Interrupts 10 Why Hardware Interrupts? • Several devices connected to the CPU – eg.