Introduction to INTERVAL ANALYSIS
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Cantor Groups
Integre Technical Publishing Co., Inc. College Mathematics Journal 42:1 November 11, 2010 10:58 a.m. classroom.tex page 60 Cantor Groups Ben Mathes ([email protected]), Colby College, Waterville ME 04901; Chris Dow ([email protected]), University of Chicago, Chicago IL 60637; and Leo Livshits ([email protected]), Colby College, Waterville ME 04901 The Cantor set C is simultaneously small and large. Its cardinality is the same as the cardinality of all real numbers, and every element of C is a limit of other elements of C (it is perfect), but C is nowhere dense and it is a nullset. Being nowhere dense is a kind of topological smallness, meaning that there is no interval in which the set is dense, or equivalently, that its complement is a dense open subset of [0, 1]. Being a nullset is a measure theoretic concept of smallness, meaning that, for every >0, it is possible to cover the set with a sequence of intervals In whose lengths add to a sum less than . It is possible to tweak the construction of C that results in a set H that remains per- fect (and consequently has the cardinality of the continuum), is still nowhere dense, but the measure can be made to attain any number α in the interval [0, 1). The con- struction is a special case of Hewitt and Stromberg’s Cantor-like set [1,p.70],which goes like this: let E0 denote [0, 1],letE1 denote what is left after deleting an open interval from the center of E0.IfEn−1 has been constructed, obtain En by deleting open intervals of the same length from the center of each of the disjoint closed inter- vals that comprise En−1. -

1. Definition. Let I Be the Unit Interval. If I, G Are Maps on I Then 1 and G Are Conjugate Iff There Is a Homeomorphism H of I Such That 1 = H -I Gh
TRANSACTIONS OF THE AMERICAN MATHEMATICAL SOCIETY Volume 319. Number I. May 1990 A COMPLETE CLASSIFICATION OF THE PIECEWISE MONOTONE FUNCTIONS ON THE INTERVAL STEWART BALDWIN ABSTRACT. We define two functions f and g on the unit interval [0, I] to be strongly conjugate iff there is an order-preserving homeomorphism h of [0, I] such that g = h-1 fh (a minor variation of the more common term "conjugate", in which h need not be order-preserving). We provide a complete set of invariants for each continuous (strictly) piecewise monotone function such that two such functions have the same invariants if and only if they are strongly conjugate, thus providing a complete classification of all such strong conjugacy classes. In addition, we provide a criterion which decides whether or not a potential invariant is actually realized by some 'piecewise monotone continuous function. INTRODUCTION 1. Definition. Let I be the unit interval. If I, g are maps on I then 1 and g are conjugate iff there is a homeomorphism h of I such that 1 = h -I gh. A more convenient term for our purposes will be: I, g are strongly conjugate (written 1 ~ g) iff there is an order preserving homeomorphism h as above. Given a map 1 on I, define the map j by I*(x) = 1 - 1(1 - x) (essentially a 1800 rotation of the graph). The main result of this paper will be to give a complete set of invariants for the strong conjugacy classes of the piecewise monotone continuous functions on the unit interval I = [0, I]. -

Interval Notation and Linear Inequalities
CHAPTER 1 Introductory Information and Review Section 1.7: Interval Notation and Linear Inequalities Linear Inequalities Linear Inequalities Rules for Solving Inequalities: 86 University of Houston Department of Mathematics SECTION 1.7 Interval Notation and Linear Inequalities Interval Notation: Example: Solution: MATH 1300 Fundamentals of Mathematics 87 CHAPTER 1 Introductory Information and Review Example: Solution: Example: 88 University of Houston Department of Mathematics SECTION 1.7 Interval Notation and Linear Inequalities Solution: Additional Example 1: Solution: MATH 1300 Fundamentals of Mathematics 89 CHAPTER 1 Introductory Information and Review Additional Example 2: Solution: 90 University of Houston Department of Mathematics SECTION 1.7 Interval Notation and Linear Inequalities Additional Example 3: Solution: Additional Example 4: Solution: MATH 1300 Fundamentals of Mathematics 91 CHAPTER 1 Introductory Information and Review Additional Example 5: Solution: Additional Example 6: Solution: 92 University of Houston Department of Mathematics SECTION 1.7 Interval Notation and Linear Inequalities Additional Example 7: Solution: MATH 1300 Fundamentals of Mathematics 93 Exercise Set 1.7: Interval Notation and Linear Inequalities For each of the following inequalities: Write each of the following inequalities in interval (a) Write the inequality algebraically. notation. (b) Graph the inequality on the real number line. (c) Write the inequality in interval notation. 23. 1. x is greater than 5. 2. x is less than 4. 24. 3. x is less than or equal to 3. 4. x is greater than or equal to 7. 25. 5. x is not equal to 2. 6. x is not equal to 5 . 26. 7. x is less than 1. 8. -

Interval Computations: Introduction, Uses, and Resources
Interval Computations: Introduction, Uses, and Resources R. B. Kearfott Department of Mathematics University of Southwestern Louisiana U.S.L. Box 4-1010, Lafayette, LA 70504-1010 USA email: [email protected] Abstract Interval analysis is a broad field in which rigorous mathematics is as- sociated with with scientific computing. A number of researchers world- wide have produced a voluminous literature on the subject. This article introduces interval arithmetic and its interaction with established math- ematical theory. The article provides pointers to traditional literature collections, as well as electronic resources. Some successful scientific and engineering applications are listed. 1 What is Interval Arithmetic, and Why is it Considered? Interval arithmetic is an arithmetic defined on sets of intervals, rather than sets of real numbers. A form of interval arithmetic perhaps first appeared in 1924 and 1931 in [8, 104], then later in [98]. Modern development of interval arithmetic began with R. E. Moore’s dissertation [64]. Since then, thousands of research articles and numerous books have appeared on the subject. Periodic conferences, as well as special meetings, are held on the subject. There is an increasing amount of software support for interval computations, and more resources concerning interval computations are becoming available through the Internet. In this paper, boldface will denote intervals, lower case will denote scalar quantities, and upper case will denote vectors and matrices. Brackets “[ ]” will delimit intervals while parentheses “( )” will delimit vectors and matrices.· Un- derscores will denote lower bounds of· intervals and overscores will denote upper bounds of intervals. Corresponding lower case letters will denote components of vectors. -

General Topology
General Topology Tom Leinster 2014{15 Contents A Topological spaces2 A1 Review of metric spaces.......................2 A2 The definition of topological space.................8 A3 Metrics versus topologies....................... 13 A4 Continuous maps........................... 17 A5 When are two spaces homeomorphic?................ 22 A6 Topological properties........................ 26 A7 Bases................................. 28 A8 Closure and interior......................... 31 A9 Subspaces (new spaces from old, 1)................. 35 A10 Products (new spaces from old, 2)................. 39 A11 Quotients (new spaces from old, 3)................. 43 A12 Review of ChapterA......................... 48 B Compactness 51 B1 The definition of compactness.................... 51 B2 Closed bounded intervals are compact............... 55 B3 Compactness and subspaces..................... 56 B4 Compactness and products..................... 58 B5 The compact subsets of Rn ..................... 59 B6 Compactness and quotients (and images)............. 61 B7 Compact metric spaces........................ 64 C Connectedness 68 C1 The definition of connectedness................... 68 C2 Connected subsets of the real line.................. 72 C3 Path-connectedness.......................... 76 C4 Connected-components and path-components........... 80 1 Chapter A Topological spaces A1 Review of metric spaces For the lecture of Thursday, 18 September 2014 Almost everything in this section should have been covered in Honours Analysis, with the possible exception of some of the examples. For that reason, this lecture is longer than usual. Definition A1.1 Let X be a set. A metric on X is a function d: X × X ! [0; 1) with the following three properties: • d(x; y) = 0 () x = y, for x; y 2 X; • d(x; y) + d(y; z) ≥ d(x; z) for all x; y; z 2 X (triangle inequality); • d(x; y) = d(y; x) for all x; y 2 X (symmetry). -
Multidisciplinary Design Project Engineering Dictionary Version 0.0.2
Multidisciplinary Design Project Engineering Dictionary Version 0.0.2 February 15, 2006 . DRAFT Cambridge-MIT Institute Multidisciplinary Design Project This Dictionary/Glossary of Engineering terms has been compiled to compliment the work developed as part of the Multi-disciplinary Design Project (MDP), which is a programme to develop teaching material and kits to aid the running of mechtronics projects in Universities and Schools. The project is being carried out with support from the Cambridge-MIT Institute undergraduate teaching programe. For more information about the project please visit the MDP website at http://www-mdp.eng.cam.ac.uk or contact Dr. Peter Long Prof. Alex Slocum Cambridge University Engineering Department Massachusetts Institute of Technology Trumpington Street, 77 Massachusetts Ave. Cambridge. Cambridge MA 02139-4307 CB2 1PZ. USA e-mail: [email protected] e-mail: [email protected] tel: +44 (0) 1223 332779 tel: +1 617 253 0012 For information about the CMI initiative please see Cambridge-MIT Institute website :- http://www.cambridge-mit.org CMI CMI, University of Cambridge Massachusetts Institute of Technology 10 Miller’s Yard, 77 Massachusetts Ave. Mill Lane, Cambridge MA 02139-4307 Cambridge. CB2 1RQ. USA tel: +44 (0) 1223 327207 tel. +1 617 253 7732 fax: +44 (0) 1223 765891 fax. +1 617 258 8539 . DRAFT 2 CMI-MDP Programme 1 Introduction This dictionary/glossary has not been developed as a definative work but as a useful reference book for engi- neering students to search when looking for the meaning of a word/phrase. It has been compiled from a number of existing glossaries together with a number of local additions. -
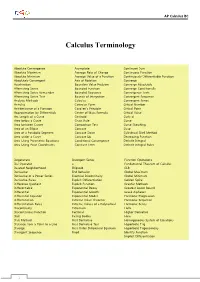
Calculus Terminology
AP Calculus BC Calculus Terminology Absolute Convergence Asymptote Continued Sum Absolute Maximum Average Rate of Change Continuous Function Absolute Minimum Average Value of a Function Continuously Differentiable Function Absolutely Convergent Axis of Rotation Converge Acceleration Boundary Value Problem Converge Absolutely Alternating Series Bounded Function Converge Conditionally Alternating Series Remainder Bounded Sequence Convergence Tests Alternating Series Test Bounds of Integration Convergent Sequence Analytic Methods Calculus Convergent Series Annulus Cartesian Form Critical Number Antiderivative of a Function Cavalieri’s Principle Critical Point Approximation by Differentials Center of Mass Formula Critical Value Arc Length of a Curve Centroid Curly d Area below a Curve Chain Rule Curve Area between Curves Comparison Test Curve Sketching Area of an Ellipse Concave Cusp Area of a Parabolic Segment Concave Down Cylindrical Shell Method Area under a Curve Concave Up Decreasing Function Area Using Parametric Equations Conditional Convergence Definite Integral Area Using Polar Coordinates Constant Term Definite Integral Rules Degenerate Divergent Series Function Operations Del Operator e Fundamental Theorem of Calculus Deleted Neighborhood Ellipsoid GLB Derivative End Behavior Global Maximum Derivative of a Power Series Essential Discontinuity Global Minimum Derivative Rules Explicit Differentiation Golden Spiral Difference Quotient Explicit Function Graphic Methods Differentiable Exponential Decay Greatest Lower Bound Differential -

Semisimplicial Unital Groups
International Journal of Theoretical Physics, Vol. 43, Nos. 7/8, August 2004 (C 2004) Semisimplicial Unital Groups David J. Foulis1 and Richard J. Greechie2 If there is an order-preserving group isomorphism from a directed abelian group G with a finitely generated positive cone G+ onto a simplicial group, then G is called a semisimplicial group. By factoring out the torsion subgroup of a unital group having a finite unit interval, one obtains a semisimplicial unital group. We exhibit a represen- tation for the base-normed space associated with a semisimplicial unital group G as the Banach dual space of a finite dimensional order-unit space that contains G as an additive subgroup. In terms of this representation, we formulate necessary and sufficient conditions for G to be archimedean. KEY WORDS: partially ordered abelian group; directed group; unital group; sim- plicial group; semisimplicial unital group; effect algebra; state; base-normed space, order-unit space. 1. INTRODUCTION If H is a Hilbert space, then the set G of all bounded self-adjoint operators on H is organized in the usual way into a partially ordered real linear space (in fact, an order-unit Banach space), and the operators belonging to the interval E :={A ∈ G | 0 ≤ A ≤ 1} are called the effect operators on H. The set E, organized into a partial algebra under the restriction ⊕ of addition on G to E, is called the algebra of effect operators on H. In the contemporary theory of quantum measurement (Busch et al., 1991), an observable is represented by a positive-operator-valued (POV) measure defined on a σ-field of sets and taking on values in the effect algebra E. -

Chapter 1: Interval Analysis, Fuzzy Set Theory and Possibility Theory In
Draft 1.0 November 4, 2010 CHAPTER 1 of the book Lodwick, Weldon A. (2011). Flexible and Un- certainty Optimization (to be published) Interval Analysis, Fuzzy Set Theory and Possibility Theory in Optimization Weldon A. Lodwick University of Colorado Denver Department of Mathematical and Statistical Sciences, Campus Box 170 P.O. Box 173364 Denver, CO 80217-3364, U.S.A. Email: [email protected] Abstract: This study explores the interconnections between interval analysis, fuzzy interval analysis, and interval, fuzzy, and possibility optimization. The key ideas considered are: (1) Fuzzy and possibility optimization are impor- tant methods in applied optimization problems, (2) Fuzzy sets and possibility distributions are distinct which in the context of optimization lead to ‡exible optimization on one hand and optimization under uncertainty on the other, (3) There are two ways to view possibility analysis leading to two distinct types of possibility optimization under uncertainty, single and dual distribu- tion optimization, and (4) The semantic (meaning) of constraint set in the presence of fuzziness and possibility needs to be known a-priori in order to determine what the constraint set is and how to compute its elements. The thesis of this exposition is that optimization problems that intend to model real problems are very (most) often satis…cing and epistemic and that the math- ematical language of fuzzy sets and possibility theory are well-suited theories for stating and solving a wide classes of optimization problems. Keywords: Fuzzy optimization, possibility optimization, interval analysis, constraint fuzzy interval arithmetic 1 Introduction This exposition explores interval analysis, fuzzy interval analysis, fuzzy set theory, and possibility theory as they relate to optimization which is both a synthesis of the author’s previous work bringing together, transforming, 1 and updating many ideas found in [49],[50], [51], [52], [58], [63], [64], [118], [116], and [117] as well as some new material dealing with the computation of constraint sets. -

WHY a DEDEKIND CUT DOES NOT PRODUCE IRRATIONAL NUMBERS And, Open Intervals Are Not Sets
WHY A DEDEKIND CUT DOES NOT PRODUCE IRRATIONAL NUMBERS And, Open Intervals are not Sets Pravin K. Johri The theory of mathematics claims that the set of real numbers is uncountable while the set of rational numbers is countable. Almost all real numbers are supposed to be irrational but there are few examples of irrational numbers relative to the rational numbers. The reality does not match the theory. Real numbers satisfy the field axioms but the simple arithmetic in these axioms can only result in rational numbers. The Dedekind cut is one of the ways mathematics rationalizes the existence of irrational numbers. Excerpts from the Wikipedia page “Dedekind cut” A Dedekind cut is а method of construction of the real numbers. It is a partition of the rational numbers into two non-empty sets A and B, such that all elements of A are less than all elements of B, and A contains no greatest element. If B has a smallest element among the rationals, the cut corresponds to that rational. Otherwise, that cut defines a unique irrational number which, loosely speaking, fills the "gap" between A and B. The countable partitions of the rational numbers cannot result in uncountable irrational numbers. Moreover, a known irrational number, or any real number for that matter, defines a Dedekind cut but it is not possible to go in the other direction and create a Dedekind cut which then produces an unknown irrational number. 1 Irrational Numbers There is an endless sequence of finite natural numbers 1, 2, 3 … based on the Peano axiom that if n is a natural number then so is n+1. -

Topological Properties
CHAPTER 4 Topological properties 1. Connectedness • Definitions and examples • Basic properties • Connected components • Connected versus path connected, again 2. Compactness • Definition and first examples • Topological properties of compact spaces • Compactness of products, and compactness in Rn • Compactness and continuous functions • Embeddings of compact manifolds • Sequential compactness • More about the metric case 3. Local compactness and the one-point compactification • Local compactness • The one-point compactification 4. More exercises 63 64 4. TOPOLOGICAL PROPERTIES 1. Connectedness 1.1. Definitions and examples. Definition 4.1. We say that a topological space (X, T ) is connected if X cannot be written as the union of two disjoint non-empty opens U, V ⊂ X. We say that a topological space (X, T ) is path connected if for any x, y ∈ X, there exists a path γ connecting x and y, i.e. a continuous map γ : [0, 1] → X such that γ(0) = x, γ(1) = y. Given (X, T ), we say that a subset A ⊂ X is connected (or path connected) if A, together with the induced topology, is connected (path connected). As we shall soon see, path connectedness implies connectedness. This is good news since, unlike connectedness, path connectedness can be checked more directly (see the examples below). Example 4.2. (1) X = {0, 1} with the discrete topology is not connected. Indeed, U = {0}, V = {1} are disjoint non-empty opens (in X) whose union is X. (2) Similarly, X = [0, 1) ∪ [2, 3] is not connected (take U = [0, 1), V = [2, 3]). More generally, if X ⊂ R is connected, then X must be an interval. -

Calculus Formulas and Theorems
Formulas and Theorems for Reference I. Tbigonometric Formulas l. sin2d+c,cis2d:1 sec2d l*cot20:<:sc:20 +.I sin(-d) : -sitt0 t,rs(-//) = t r1sl/ : -tallH 7. sin(A* B) :sitrAcosB*silBcosA 8. : siri A cos B - siu B <:os,;l 9. cos(A+ B) - cos,4cos B - siuA siriB 10. cos(A- B) : cosA cosB + silrA sirrB 11. 2 sirrd t:osd 12. <'os20- coS2(i - siu20 : 2<'os2o - I - 1 - 2sin20 I 13. tan d : <.rft0 (:ost/ I 14. <:ol0 : sirrd tattH 1 15. (:OS I/ 1 16. cscd - ri" 6i /F tl r(. cos[I ^ -el : sitt d \l 18. -01 : COSA 215 216 Formulas and Theorems II. Differentiation Formulas !(r") - trr:"-1 Q,:I' ]tra-fg'+gf' gJ'-,f g' - * (i) ,l' ,I - (tt(.r))9'(.,') ,i;.[tyt.rt) l'' d, \ (sttt rrJ .* ('oqI' .7, tJ, \ . ./ stll lr dr. l('os J { 1a,,,t,:r) - .,' o.t "11'2 1(<,ot.r') - (,.(,2.r' Q:T rl , (sc'c:.r'J: sPl'.r tall 11 ,7, d, - (<:s<t.r,; - (ls(].]'(rot;.r fr("'),t -.'' ,1 - fr(u") o,'ltrc ,l ,, 1 ' tlll ri - (l.t' .f d,^ --: I -iAl'CSllLl'l t!.r' J1 - rz 1(Arcsi' r) : oT Il12 Formulas and Theorems 2I7 III. Integration Formulas 1. ,f "or:artC 2. [\0,-trrlrl *(' .t "r 3. [,' ,t.,: r^x| (' ,I 4. In' a,,: lL , ,' .l 111Q 5. In., a.r: .rhr.r' .r r (' ,l f 6. sirr.r d.r' - ( os.r'-t C ./ 7. /.,,.r' dr : sitr.i'| (' .t 8. tl:r:hr sec,rl+ C or ln Jccrsrl+ C ,f'r^rr f 9.