Elliptic Curve Cryptography in Practice
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Cipher Support on a Citrix MPX/SDX (N3) Appliance
Cipher support on a Citrix MPX/SDX (N3) appliance The following table lists the support for different ciphers on SSL entities, such as virtual server, frontend, backend, and internal services. On an SDX appliance, if an SSL chip is assigned to a VPX instance, the cipher support of an MPX appliance applies. Otherwise, the normal cipher support of a VPX instance applies. From release 10.5 build 56.22, NetScaler MPX appliances support full hardware optimization for all ciphers. In earlier releases, part of ECDHE/DHE cipher optimization was done in software. Use the 'show hardware' command to identify whether your appliance has N3 chips. > sh hardware Platform: NSMPX-22000 16*CPU+24*IX+12*E1K+2*E1K+4*CVM N3 2200100 Manufactured on: 8/19/2013 CPU: 2900MHZ Host Id: 1006665862 Serial no: ENUK6298FT Encoded serial no: ENUK6298FT Done How to read the table Unless a build number is specified, a cipher suite is supported for all builds in a release. Example • 10.5, 11.0, 11.1, 12.0, 12.1, 13.0: All builds of 10.5, 11.0, 11.1, 12.0, 12.1, 13.0, releases. • 11.1, 12.0, 12.1, 13.0: All builds of 11.1, 12.0, 12.1, 13.0 releases. • 10.5-53.x and later, 11.0, 11.1, 12.0, 12.1, 13.0: Build 53.x and later in release 10.5. All builds of 11.0, 11.1, 12.0, 12.1, 13.0 releases. • NA: not applicable. Ciphersuite Name Hex Wireshark Ciphersuite Name Builds Builds Code Supported Supported (frontend) (backend) TLS1-AES-256-CBC-SHA 0x0035 TLS_RSA_WITH_AES_256_CB 10.5, 11.0, 10.5, 11.0, C_SHA 11.1, 12.0, 11.1, 12.0, 12.1, 13.0 12.1, 13.0 TLS1-AES-128-CBC-SHA 0x002f -

Examples from Complex Geometry
Examples from Complex Geometry Sam Auyeung November 22, 2019 1 Complex Analysis Example 1.1. Two Heuristic \Proofs" of the Fundamental Theorem of Algebra: Let p(z) be a polynomial of degree n > 0; we can even assume it is a monomial. We also know that the number of zeros is at most n. We show that there are exactly n. 1. Proof 1: Recall that polynomials are entire functions and that Liouville's Theorem says that a bounded entire function is in fact constant. Suppose that p has no roots. Then 1=p is an entire function and it is bounded. Thus, it is constant which means p is a constant polynomial and has degree 0. This contradicts the fact that p has positive degree. Thus, p must have a root α1. We can then factor out (z − α1) from p(z) = (z − α1)q(z) where q(z) is an (n − 1)-degree polynomial. We may repeat the above process until we have a full factorization of p. 2. Proof 2: On the real line, an algorithm for finding a root of a continuous function is to look for when the function changes signs. How do we generalize this to C? Instead of having two directions, we have a whole S1 worth of directions. If we use colors to depict direction and brightness to depict magnitude, we can plot a graph of a continuous function f : C ! C. Near a zero, we'll see all colors represented. If we travel in a loop around any point, we can keep track of whether it passes through all the colors; around a zero, we'll pass through all the colors, possibly many times. -

Cryptography in Modern World
Cryptography in Modern World Julius O. Olwenyi, Aby Tino Thomas, Ayad Barsoum* St. Mary’s University, San Antonio, TX (USA) Emails: [email protected], [email protected], [email protected] Abstract — Cryptography and Encryption have been where a letter in plaintext is simply shifted 3 places down used for secure communication. In the modern world, the alphabet [4,5]. cryptography is a very important tool for protecting information in computer systems. With the invention ABCDEFGHIJKLMNOPQRSTUVWXYZ of the World Wide Web or Internet, computer systems are highly interconnected and accessible from DEFGHIJKLMNOPQRSTUVWXYZABC any part of the world. As more systems get interconnected, more threat actors try to gain access The ciphertext of the plaintext “CRYPTOGRAPHY” will to critical information stored on the network. It is the be “FUBSWRJUASLB” in a Caesar cipher. responsibility of data owners or organizations to keep More recent derivative of Caesar cipher is Rot13 this data securely and encryption is the main tool used which shifts 13 places down the alphabet instead of 3. to secure information. In this paper, we will focus on Rot13 was not all about data protection but it was used on different techniques and its modern application of online forums where members could share inappropriate cryptography. language or nasty jokes without necessarily being Keywords: Cryptography, Encryption, Decryption, Data offensive as it will take those interested in those “jokes’ security, Hybrid Encryption to shift characters 13 spaces to read the message and if not interested you do not need to go through the hassle of converting the cipher. I. INTRODUCTION In the 16th century, the French cryptographer Back in the days, cryptography was not all about Blaise de Vigenere [4,5], developed the first hiding messages or secret communication, but in ancient polyalphabetic substitution basically based on Caesar Egypt, where it began; it was carved into the walls of cipher, but more difficult to crack the cipher text. -

A Review on Elliptic Curve Cryptography for Embedded Systems
International Journal of Computer Science & Information Technology (IJCSIT), Vol 3, No 3, June 2011 A REVIEW ON ELLIPTIC CURVE CRYPTOGRAPHY FOR EMBEDDED SYSTEMS Rahat Afreen 1 and S.C. Mehrotra 2 1Tom Patrick Institute of Computer & I.T, Dr. Rafiq Zakaria Campus, Rauza Bagh, Aurangabad. (Maharashtra) INDIA [email protected] 2Department of C.S. & I.T., Dr. B.A.M. University, Aurangabad. (Maharashtra) INDIA [email protected] ABSTRACT Importance of Elliptic Curves in Cryptography was independently proposed by Neal Koblitz and Victor Miller in 1985.Since then, Elliptic curve cryptography or ECC has evolved as a vast field for public key cryptography (PKC) systems. In PKC system, we use separate keys to encode and decode the data. Since one of the keys is distributed publicly in PKC systems, the strength of security depends on large key size. The mathematical problems of prime factorization and discrete logarithm are previously used in PKC systems. ECC has proved to provide same level of security with relatively small key sizes. The research in the field of ECC is mostly focused on its implementation on application specific systems. Such systems have restricted resources like storage, processing speed and domain specific CPU architecture. KEYWORDS Elliptic curve cryptography Public Key Cryptography, embedded systems, Elliptic Curve Digital Signature Algorithm ( ECDSA), Elliptic Curve Diffie Hellman Key Exchange (ECDH) 1. INTRODUCTION The changing global scenario shows an elegant merging of computing and communication in such a way that computers with wired communication are being rapidly replaced to smaller handheld embedded computers using wireless communication in almost every field. This has increased data privacy and security requirements. -

Choosing Key Sizes for Cryptography
information security technical report 15 (2010) 21e27 available at www.sciencedirect.com www.compseconline.com/publications/prodinf.htm Choosing key sizes for cryptography Alexander W. Dent Information Security Group, University Of London, Royal Holloway, UK abstract After making the decision to use public-key cryptography, an organisation still has to make many important decisions before a practical system can be implemented. One of the more difficult challenges is to decide the length of the keys which are to be used within the system: longer keys provide more security but mean that the cryptographic operation will take more time to complete. The most common solution is to take advice from information security standards. This article will investigate the methodology that is used produce these standards and their meaning for an organisation who wishes to implement public-key cryptography. ª 2010 Elsevier Ltd. All rights reserved. 1. Introduction being compromised by an attacker). It also typically means a slower scheme. Most symmetric cryptographic schemes do The power of public-key cryptography is undeniable. It is not allow the use of keys of different lengths. If a designer astounding in its simplicity and its ability to provide solutions wishes to offer a symmetric scheme which provides different to many seemingly insurmountable organisational problems. security levels depending on the key size, then the designer However, the use of public-key cryptography in practice is has to construct distinct variants of a central design which rarely as simple as the concept first appears. First one has to make use of different pre-specified key lengths. -
Cryptographic Control Standard, Version
Nuclear Regulatory Commission Office of the Chief Information Officer Computer Security Standard Office Instruction: OCIO-CS-STD-2009 Office Instruction Title: Cryptographic Control Standard Revision Number: 2.0 Issuance: Date of last signature below Effective Date: October 1, 2017 Primary Contacts: Kathy Lyons-Burke, Senior Level Advisor for Information Security Responsible Organization: OCIO Summary of Changes: OCIO-CS-STD-2009, “Cryptographic Control Standard,” provides the minimum security requirements that must be applied to the Nuclear Regulatory Commission (NRC) systems which utilize cryptographic algorithms, protocols, and cryptographic modules to provide secure communication services. This update is based on the latest versions of the National Institute of Standards and Technology (NIST) Guidance and Federal Information Processing Standards (FIPS) publications, Committee on National Security System (CNSS) issuances, and National Security Agency (NSA) requirements. Training: Upon request ADAMS Accession No.: ML17024A095 Approvals Primary Office Owner Office of the Chief Information Officer Signature Date Enterprise Security Kathy Lyons-Burke 09/26/17 Architecture Working Group Chair CIO David Nelson /RA/ 09/26/17 CISO Jonathan Feibus 09/26/17 OCIO-CS-STD-2009 Page i TABLE OF CONTENTS 1 PURPOSE ............................................................................................................................. 1 2 INTRODUCTION .................................................................................................................. -

Contents 5 Elliptic Curves in Cryptography
Cryptography (part 5): Elliptic Curves in Cryptography (by Evan Dummit, 2016, v. 1.00) Contents 5 Elliptic Curves in Cryptography 1 5.1 Elliptic Curves and the Addition Law . 1 5.1.1 Cubic Curves, Weierstrass Form, Singular and Nonsingular Curves . 1 5.1.2 The Addition Law . 3 5.1.3 Elliptic Curves Modulo p, Orders of Points . 7 5.2 Factorization with Elliptic Curves . 10 5.3 Elliptic Curve Cryptography . 14 5.3.1 Encoding Plaintexts on Elliptic Curves, Quadratic Residues . 14 5.3.2 Public-Key Encryption with Elliptic Curves . 17 5.3.3 Key Exchange and Digital Signatures with Elliptic Curves . 20 5 Elliptic Curves in Cryptography In this chapter, we will introduce elliptic curves and describe how they are used in cryptography. Elliptic curves have a long and interesting history and arise in a wide range of contexts in mathematics. The study of elliptic curves involves elements from most of the major disciplines of mathematics: algebra, geometry, analysis, number theory, topology, and even logic. Elliptic curves appear in the proofs of many deep results in mathematics: for example, they are a central ingredient in the proof of Fermat's Last Theorem, which states that there are no positive integer solutions to the equation xn + yn = zn for any integer n ≥ 3. Our goals are fairly modest in comparison, so we will begin by outlining the basic algebraic and geometric properties of elliptic curves and motivate the addition law. We will then study the behavior of elliptic curves modulo p: ultimately, there is a fairly strong analogy between the structure of the points on an elliptic curve modulo p and the integers modulo n. -

An Efficient Approach to Point-Counting on Elliptic Curves
mathematics Article An Efficient Approach to Point-Counting on Elliptic Curves from a Prominent Family over the Prime Field Fp Yuri Borissov * and Miroslav Markov Department of Mathematical Foundations of Informatics, Institute of Mathematics and Informatics, Bulgarian Academy of Sciences, 1113 Sofia, Bulgaria; [email protected] * Correspondence: [email protected] Abstract: Here, we elaborate an approach for determining the number of points on elliptic curves 2 3 from the family Ep = fEa : y = x + a (mod p), a 6= 0g, where p is a prime number >3. The essence of this approach consists in combining the well-known Hasse bound with an explicit formula for the quantities of interest-reduced modulo p. It allows to advance an efficient technique to compute the 2 six cardinalities associated with the family Ep, for p ≡ 1 (mod 3), whose complexity is O˜ (log p), thus improving the best-known algorithmic solution with almost an order of magnitude. Keywords: elliptic curve over Fp; Hasse bound; high-order residue modulo prime 1. Introduction The elliptic curves over finite fields play an important role in modern cryptography. We refer to [1] for an introduction concerning their cryptographic significance (see, as well, Citation: Borissov, Y.; Markov, M. An the pioneering works of V. Miller and N. Koblitz from 1980’s [2,3]). Briefly speaking, the Efficient Approach to Point-Counting advantage of the so-called elliptic curve cryptography (ECC) over the non-ECC is that it on Elliptic Curves from a Prominent requires smaller keys to provide the same level of security. Family over the Prime Field Fp. -
Cipher Support on a Citrix ADC VPX Appliance
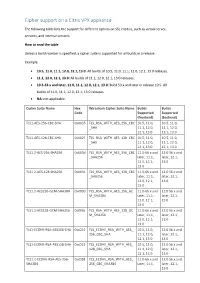
Cipher support on a Citrix VPX appliance The following table lists the support for different ciphers on SSL entities, such as virtual server, services, and internal services. How to read the table Unless a build number is specified, a cipher suite is supported for all builds in a release. Example • 10.5, 11.0, 11.1, 12.0, 12.1, 13.0: All builds of 10.5, 11.0, 11.1, 12.0, 12.1, 13.0 releases. • 11.1, 12.0, 12.1, 13.0: All builds of 11.1, 12.0, 12.1, 13.0 releases. • 10.5-53.x and later, 11.0, 11.1, 12.0, 12.1, 13.0: Build 53.x and later in release 10.5. All builds of 11.0, 11.1, 12.0, 12.1, 13.0 releases. • NA: not applicable. Cipher Suite Name Hex Wireshark Cipher Suite Name Builds Builds Code Supported Supported (frontend) (backend) TLS1-AES-256-CBC-SHA 0x0035 TLS_RSA_WITH_AES_256_CBC 10.5, 11.0, 10.5, 11.0, _SHA 11.1, 12.0, 11.1, 12.0, 12.1, 13.0 12.1, 13.0 TLS1-AES-128-CBC-SHA 0x002f TLS_RSA_WITH_AES_128_CBC 10.5, 11.0, 10.5, 11.0, _SHA 11.1, 12.0, 11.1, 12.0, 12.1, 13.0 12.1, 13.0 TLS1.2-AES-256-SHA256 0x003d TLS_RSA_WITH_AES_256_CBC 11.0-66.x and 12.0 56.x and _SHA256 later, 11.1, later, 12.1, 12.0, 12.1, 13.0 13.0 TLS1.2-AES-128-SHA256 0x003c TLS_RSA_WITH_AES_128_CBC 11.0-66.x and 12.0 56.x and _SHA256 later, 11.1, later, 12.1, 12.0, 12.1, 13.0 13.0 TLS1.2-AES256-GCM-SHA384 0x009d TLS_RSA_WITH_AES_256_GC 11.0-66.x and 12.0 56.x and M_SHA384 later, 11.1, later, 12.1, 12.0, 12.1, 13.0 13.0 TLS1.2-AES128-GCM-SHA256 0x009c TLS_RSA_WITH_AES_128_GC 11.0-66.x and 12.0 56.x and M_SHA256 later, 11.1, later, 12.1, 12.0, 12.1, 13.0 13.0 TLS1-ECDHE-RSA-AES256-SHA -

SHA-3 and the Hash Function Keccak
Christof Paar Jan Pelzl SHA-3 and The Hash Function Keccak An extension chapter for “Understanding Cryptography — A Textbook for Students and Practitioners” www.crypto-textbook.com Springer 2 Table of Contents 1 The Hash Function Keccak and the Upcoming SHA-3 Standard . 1 1.1 Brief History of the SHA Family of Hash Functions. .2 1.2 High-level Description of Keccak . .3 1.3 Input Padding and Generating of Output . .6 1.4 The Function Keccak- f (or the Keccak- f Permutation) . .7 1.4.1 Theta (q)Step.......................................9 1.4.2 Steps Rho (r) and Pi (p).............................. 10 1.4.3 Chi (c)Step ........................................ 10 1.4.4 Iota (i)Step......................................... 11 1.5 Implementation in Software and Hardware . 11 1.6 Discussion and Further Reading . 12 1.7 Lessons Learned . 14 Problems . 15 References ......................................................... 17 v Chapter 1 The Hash Function Keccak and the Upcoming SHA-3 Standard This document1 is a stand-alone description of the Keccak hash function which is the basis of the upcoming SHA-3 standard. The description is consistent with the approach used in our book Understanding Cryptography — A Textbook for Students and Practioners [11]. If you own the book, this document can be considered “Chap- ter 11b”. However, the book is most certainly not necessary for using the SHA-3 description in this document. You may want to check the companion web site of Understanding Cryptography for more information on Keccak: www.crypto-textbook.com. In this chapter you will learn: A brief history of the SHA-3 selection process A high-level description of SHA-3 The internal structure of SHA-3 A discussion of the software and hardware implementation of SHA-3 A problem set and recommended further readings 1 We would like to thank the Keccak designers as well as Pawel Swierczynski and Christian Zenger for their extremely helpful input to this document. -

Eurocrypt 2013 Athens, Greece, May 28Th, 2013
Keccak Guido Bertoni1 Joan Daemen1 Michaël Peeters2 Gilles Van Assche1 1STMicroelectronics 2NXP Semiconductors Eurocrypt 2013 Athens, Greece, May 28th, 2013 1 / 57 Symmetric crypto: what textbooks and intro’s say Symmetric cryptographic primitives: Block ciphers Stream ciphers Hash functions And their modes-of-use Picture by GlasgowAmateur 2 / 57 Outline 1 The sponge construction 2 Inside Keccak 3 Outside Keccak (using sponge and duplex) 4 Keccak towards the SHA-3 standard 5 Further inside Keccak 3 / 57 The sponge construction Outline 1 The sponge construction 2 Inside Keccak 3 Outside Keccak (using sponge and duplex) 4 Keccak towards the SHA-3 standard 5 Further inside Keccak 4 / 57 The sponge construction Our beginning: RadioGatún Initiative to design hash/stream function (late 2005) rumours about NIST call for hash functions forming of Keccak Team starting point: fixing Panama [Daemen, Clapp, FSE 1998] RadioGatún [Keccak team, NIST 2nd hash workshop 2006] more conservative than Panama arbitrary output length primitive expressing security claim for arbitrary output length primitive Sponge functions [Keccak team, Ecrypt hash, 2007] … closest thing to a random oracle with a finite state … Sponge construction calling random permutation 5 / 57 The sponge construction The sponge construction More general than a hash function: arbitrary-length output Calls a b-bit permutation f, with b = r + c r bits of rate c bits of capacity (security parameter) 6 / 57 The sponge construction Generic security of the sponge construction Theorem (Indifferentiability of the sponge construction) The sponge construction calling a random permutation, S0[F], is 2 (tD, tS, N, e)-indifferentiable from a random oracle, for any tD, tS = O(N ), c e e ≈ N N < 2 and for any with > fP(N) 2c+1 . -

25 Modular Forms and L-Series
18.783 Elliptic Curves Spring 2015 Lecture #25 05/12/2015 25 Modular forms and L-series As we will show in the next lecture, Fermat's Last Theorem is a direct consequence of the following theorem [11, 12]. Theorem 25.1 (Taylor-Wiles). Every semistable elliptic curve E=Q is modular. In fact, as a result of subsequent work [3], we now have the stronger result, proving what was previously known as the modularity conjecture (or Taniyama-Shimura-Weil conjecture). Theorem 25.2 (Breuil-Conrad-Diamond-Taylor). Every elliptic curve E=Q is modular. Our goal in this lecture is to explain what it means for an elliptic curve over Q to be modular (we will also define the term semistable). This requires us to delve briefly into the theory of modular forms. Our goal in doing so is simply to understand the definitions and the terminology; we will omit all but the most straight-forward proofs. 25.1 Modular forms Definition 25.3. A holomorphic function f : H ! C is a weak modular form of weight k for a congruence subgroup Γ if f(γτ) = (cτ + d)kf(τ) a b for all γ = c d 2 Γ. The j-function j(τ) is a weak modular form of weight 0 for SL2(Z), and j(Nτ) is a weak modular form of weight 0 for Γ0(N). For an example of a weak modular form of positive weight, recall the Eisenstein series X0 1 X0 1 G (τ) := G ([1; τ]) := = ; k k !k (m + nτ)k !2[1,τ] m;n2Z 1 which, for k ≥ 3, is a weak modular form of weight k for SL2(Z).