Production Operations Manual Template
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
C-4 Confined Space Rescue
CENTRAL ZONE OPERATIONS MANUAL Number: Title: Page 1 of 6 C-4 CONFINED SPACE PROCEDURES PURPOSE The purpose of this policy is to establish the minimum standards and requirements needed for Central Zone Fire Departments to comply with all applicable regulations including Title 8, General industry safety orders (GISO), Article 108, Confined Spaces – 5156, 5157, and 5158 and OSHA 29 CFR 1910.146. The intent is to provide minimum procedures and guidelines for responding personnel at confined space incidents in order to protect employees from life-threatening or other serious hazards posed by entry and work in confined spaces. Nothing in this policy shall prevent a department from exceeding these guidelines. DEFINITIONS: A confined space shall be defined as: Large enough and so configured that an employee can enter and perform assigned work; and Has limited or restricted means of entry or exit i.e., tanks, vessels, silos, storage bins, hoppers, vaults, and pits are types of spaces that may have limited means of entry; and Is not designed for continuous employee occupancy. A Permit-Required Confined Space is defined as a confined space that has one or more of the following: Contains or has a known potential to contain, a hazardous atmosphere; or Contains material with the potential for engulfment; or Has an internal configuration such that an entrant could be trapped or asphyxiated by inwardly converging walls, or a floor which slopes and tapers to a smaller cross section; or Contains any other recognized serious safety or health hazard. POLICY/PROCEDURES It is the responsibility of all personnel to follow the guidelines in this policy at all times. -

Safe Operations Manual, March 15, 2015
AFRICA OIL CORPORATION SAFE OPERATIONS MANUAL HEALTH SAFETY AND ENVIRONMENT Issued 2014 This manual contains confidential and proprietary information of Africa Oil Corporation. Any use of this manual without authorization from Africa Oil Corporation and/or its affiliates is prohibited. Proprietary - Safe Operations Manual HSE AFRICA OIL CORPORATION HSE SAFE OPERATIONS MANUAL Document Revision Data Rev No Revision Data Revised by (name) Date Comment 1.1 Document Issue and Distribution Document Title Issue Date Distribution Sign Signature Safe Operations Manual 2014 15 Mar 14 AOK Ops Team HSE Mgr Safe Operations Manual 2014 15 Mar 14 AOE Ops Team HSE Mgr 1.2 How to revise this document Suggestions for revision to this document can be sent to the AOC HSE Manager directly. Revisions shall be recorded in the table at section 1. Document revision Data. Full revision data is required and must be recorded along with the revision location (section and paragraph number) and date. This document shall be reviewed annually to ensure it remains current. 1.3 Distribution of this document This document provides the standards by which Africa oil Corporation shall conduct safe operations. This document is issued primarily to support field operations, is complimented by HSE Procedures and other standards are incorporated for office use. The Operations Team Management is responsible for further distribution to applicable contractors. Applicable contractors are those with direct contracts with Africa Oil Corporation in support of company activities. Page 2 of 133 Proprietary –AOC Safe Operations Manual AFRICA OIL CORPORATION HSE SAFE OPERATIONS MANUAL Intentionally left blank Page 3 of 133 Proprietary –AOC Safe Operations Manual AFRICA OIL CORPORATION HSE SAFE OPERATIONS MANUAL Manual Contents 1. -
POLICIES and PROCEDURES HANDBOOK UNCW Center For
POLICIES AND PROCEDURES HANDBOOK UNCW Center for Marine Science Updated Fall 2016 1 The Center for Marine Science at UNCW supports faculty, students and staff from various departments and centers who carry out research, education, and outreach activities related to coastal and marine science. These include both residents at the Center for Marine Science Myrtle Grove facility as well as faculty and students based at the College Road campus and at Wrightsville Beach. This handbook is designed to acquaint faculty, staff and students with CMS and provide information about the center and relevant policies. Please comply with all provisions of the handbook as they have been developed by faculty and staff to ensure that they are in accordance with university and state policies and guidelines, reduce multi-user conflicts over Center resources and services, provide for faculty governance, and aid in the operation of key facilities. No set of policies and procedures can anticipate every circumstance or question, and there will be situations where the need arises for us to revise, add, or cancel policies. Normally, the Handbook will be reviewed and updated on an annual basis. However, through consultation with CMS advisory committees, these policies and procedures may sometimes need to be altered more frequently to meet changing needs and be in compliance with university or state regulations. This handbook is in no way intended to replace or modify policies and procedures set in place by UNCW or the North Carolina University system. In any case of a difference in policy between this handbook and the University authorities, the University policy supersedes any CMS policy. -
Personal Protective Equipment (PPE) Program
Personal Protective Equipment (PPE) Program The University Of Iowa Environmental Health & Safety 122 Grand Avenue Court Iowa City, IA 52242-1000 Phone: 319-335-8501 Date Revised/Reviewed: 6/1/2018 Table of Contents 1. Summary ................................................................................................................................ 2 2. Scope ...................................................................................................................................... 2 3. Policy and Regulation........................................................................................................... 2 4. Roles and Responsibilities .................................................................................................. 2 5. Procedures ............................................................................................................................. 3 6. Resources and Assistance .................................................................................................. 5 APPENDIX A - Forms .................................................................................................................. 6 APPENDIX B - PPE Information and Training Guides ........................................................... 7 Eye and Face Protection ................................................................................................................. 8 Protective Clothing ........................................................................................................................ -
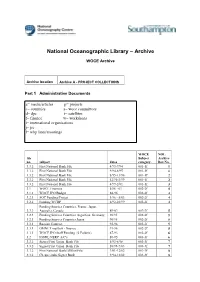
WOCE (World Ocean Circulation Experiment)
National Oceanographic Library – Archive WOCE Archive Archive location Archive A - PROJECT COLLECTIONS Part 1 Administrative Documents a= media/articles p= projects c= countries s= woce committees d= dpc t= satellites f= finance w= workshops i= international organisations j= jsc l= whp lines/moorings WOCE NOL file Subject Archive no. subject dates category. Box No. 3.3.2 First National Bank File 4/93-7/94 001-1f 1 3.3.2 First National Bank File 9/94-8/95 001-1f 1 3.3.2 First National Bank File 8/95-11/96 001-1f 2 3.3.2 First National Bank File 12/96-3/99 001-1f 2 3.3.2 First National Bank File 4/99-2/01 001-1f 3 3.1 WOCE Finances 5/86 - 01 002-2f 4 3.1.1 WOCE IPO Budget 88-96 002-2f 4 3.2.1 SOC Funding/Project 1/96 - 5/03 002-2f 4 3.2.2 Funding WCRP 6/92-10/99 002-2f 4 Funding Sources Countries, France, Japan, 3.2.3 Australia, Canada 89-02 002-2f 5 3.2.3 Funding Sources Countries Argentina, Germany, 90/95 002-2f 5 3.2.3 Funding Sources Countries Japan 90/95 002-2f 5 3.3.1 Russian Contract 92-96 002-2f 5 3.3.1 OMNET mailbox - finance 91-96 002-2f 5 3.3.1 WOCE IPO Staff Funding (2 Folders) 87-93 002-2f 6 3.2 IOSDL/NERC A/C's 89-95 003-3f 6 3.3.2 Signet/First Union Bank File 5/93-8/98 003-3f 7 3.3.2 Signet/First Union Bank File 10/98-7/03 003-3f 7 3.3.2 First National Bank/Allfirst File 3/01-12/02 003-3f 8 3.3.2 Cheque stubs Signet Bank 9/94-12/02 003-3f 8 4.6 Data Products Committee DPC 1/95-12/95 004-1d 9 4.6 Data Products Committee DPC 1/96-7/97 004-1d 9 4.6 Data Products Committee DPC 5/00-5/01 004-1d 10 4.6 Data Products Committee DPC -
Field Operations Manual for Marine Water-Column Benthic, and Trawl
FIELD OPERATIONS MANUAL FOR MARINE WATER-COLUMN, BENTHIC, AND TRAWL MONITORING IN SOUTHERN CALIFORNIA Southern California Bight Field Methods Committee March 2002 TABLE OF CONTENTS SECTION Acknowledgements ........................................................................................................................................................ 2 INTRODUCTION ................................................................................................................................................ 3 GENERAL CONSIDERATIONS........................................................................................................................ 5 Safety ........................................................................................................................................................ 5 Navigation................................................................................................................................................ 5 Cruise and Site Data................................................................................................................................ 6 Chain of Custody .................................................................................................................................... 7 WATER-COLUMN PROFILING....................................................................................................................... 9 Purpose.................................................................................................................................................... -

Job Hazard Analysis & Safe Work Procedures Workshop
Job Hazard Analysis & Safe Work Procedures Workshop Please Sign In! Workplace Safety and Health Act Further duties of employers 4(2)(b) “provide to all his workers such information, instruction, training, supervision and facilities to ensure, so far as reasonably practicable, the safety and health and welfare of his workers;” Workplace Safety and Health Act Content of Program 7.4(5) “A workplace safety and health must include… a plan for training workers and supervisors in safe work practices and procedures; Hierarchy of Controls: Most Desirable to Least Desirable • Most Attractive Option • Elimination: Remove the hazard completely. • Substitution: Replace the hazard with a non or less hazardous option. • Engineering Controls: Create Barriers to isolate worker from the hazard. Hierarchy of Controls: Con’t • Administrative Controls: Control remaining risk through Work Cycles, SWPs, Routine Maintenance or Policy. • Last Resort Personal Protective Equipment: After that, then we will think about using PPE. Difference between JHA & SWP • A Job Hazard Analysis (JHA) is an assessment tool. • Designed to Collect information. • Slow down and take a critical look at all steps and the whole environment. • Multiple Perspectives Difference… • A Safe Work Procedure is a step by step written instruction on how the employer wants the task performed. Similar to how you would follow a Recipe. • Used for training (with trainer and self- learning after), corrective action, enforcement, … Difference between Occupation and Job/Task • a job or a task in this context does not include a job such as a carpenter, • a carpenter is an occupation, a job or task for a carpenter could include cutting a board to the correct size. -

NAVY Safety & Occupational Health Manual OPNAV M-5100.23 of 5 Jun
OPNAV M-5100.23 5 Jun 2020 NAVY SAFETY AND OCCUPATIONAL HEALTH MANUAL THIS PAGE INTENTIONALLY LEFT BLANK THIS PAGE INTENTIONALLY LEFT BLANK OPNAV M-5100.23 5 Jun 2020 TABLE OF CONTENTS SECTION A. SAFETY MANAGEMENT SYSTEM Chapter 1. INTRODUCTION A0101. Purpose……………………………………………………………………..... A1-2 A0102. Scope and Applicability……………………………………………………… A1-2 A0103. Definition of Terms………………………………………………………….. A1-4 A0104. Background…………………………………………………………………... A1-4 A0105. Discussion……………………………………………………………………. A1-5 A0106. Introduction to the Navy SMS Framework………………………………….. A1-6 A0107. Responsibilities………………………………………………………………. A1-7 Chapter 2. POLICY AND ORGANIZATIONAL COMMITMENT A0201. Introduction………………………………………………………………….. A2-1 A0202. Methodology………………………………………………………………… A2-1 A0203. Organizational Commitment and Accountability…………………………… A2-3 A0204. Appointment of SMS Personnel……………………………………………… A2-4 Chapter 3. RISK MANAGEMENT A0301. Introduction………………………………………………………………….. A3-1 A0302. Methodology………………………………………………………………… A3-1 A0303. Error Tolerance……………………………………………………………… A3-1 A0304. Principles…………………………………………………………………..... A3-2 A0305. Requirements………………………………………………………………… A3-3 Chapter 4. ASSURANCE A0401. Introduction………………………………………………………………….. A4-1 A0402. Methodology………………………………………………………………… A4-1 A0403. Requirements……………………………………………………..................... A4-1 A0404. Continuous Improvement………………………………………………….… A4-2 A0405. Management Review……………………………………………………….... A4-2 Chapter 5. PROMOTION A0501. Introduction………………………………………………………………….. A5-1 -
LOCKOUT and TAGOUT Identifier
412.09 (06/03/2009 – Rev. 11) Identifier: PRD-5051 LOCKOUT AND TAGOUT Revision*: 15 Page: 1 of 29 Program Requirements For Additional Info: Companywide Effective Date: Document http://EDMS 07/21/14 Manual: 9 - Operations Change Number: 342239 *The current revision can be verified on EDMS. 1. PURPOSE This document establishes CH2M WG Idaho, LLC (CWI or “Company”) requirements for the control of hazardous energy at the Idaho Cleanup Project (ICP). 2. APPLICABILITY This document applies to activities where there is a potential for personnel injury during equipment servicing, maintenance, or modification activities due to the unexpected energization or start-up of machines or equipment or release of stored energy. MCP-101, “ICP Integrated Work Control Process,” and MCP-3562, “Hazard Identification, Analysis and Control of Operational Activities,” identify when lockout (see def.) and tagout (see def.) (LO/TO) is applicable to maintenance, operations, and research and development activities. All employees are required to comply with the restrictions and limitations imposed upon them during the use of LO/TO. The LO/TO process is considered the default and primary means for controlling hazardous energy while performing servicing and maintenance. Servicing and/or maintenance during normal production operations are covered by this program requirements document (PRD) only if: A. An employee is required to remove or bypass a guard or other safety device [29CFR1910.147(a)(2)(ii)(A)] OR B. An employee is required to place any part of his or her body into an area on a machine or piece of equipment where work is actually performed upon the material being processed (point of operation) or where an associated danger zone exists during a machine operating cycle. -
Dp Operations Manual
TECHOP TECHNICAL AND OPERATIONAL GUIDANCE (TECHOP) TECHOP (O-01 - Rev1 - Jan21) DP OPERATIONS MANUAL JANUARY 2021 TECHOP (O-01 - Rev1 - Jan21) DP OPERATIONS MANUAL 1 TECHOP DISCLAIMER The information presented in this publication of the Dynamic Positioning Committee of the Marine Technology Society (‘DP Committee’) is made available for general information purposes without charge. The DP Committee does not warrant the accuracy, completeness, or usefulness of this information. Any reliance you place on this publication is strictly at your own risk. We disclaim all liability and responsibility arising from any reliance placed on this publication by you or anyone who may be informed of its contents. 2 TECHOP (O-01 - Rev1 - Jan21) DP OPERATIONS MANUAL TECHOP CONTENTS SECTION PAGE 1 INTRODUCTION 4 1.1 PREAMBLE 4 1.2 TECHOP NAMING CONVENTION 4 1.3 MTS DP GUIDANCE REVISION METHODOLOGY 4 2 SCOPE AND IMPACT OF THIS TECHOP 5 2.1 SCOPE 5 2.2 IMPACT ON PUBLISHED GUIDANCE 5 3 CASE FOR ACTION 6 3.1 NEED FOR IMPROVEMENTS IN QUALITY AND CONTENT OF DP OPERATIONS MANUAL IDENTIFIED 6 4 PHILOSOPHY 7 4.1 OVERVIEW 7 5 COMPANY PHILOSOPHY AND POLICY 8 5.1 OVERVIEW 8 5.2 EQUIPMENT 8 5.3 PROCESSES 9 5.4 PEOPLE 9 5.5 VESSEL SPECIFIC REQUIREMENTS 10 5.6 INDUSTRIAL MISSION SPECIFIC INFORMATION 11 6 EXAMPLE CONTENTS OF A DP OPERATIONS MANUAL 12 7 GAP ANALYSIS 16 7.1 USE OF THE GAP ANALYSIS SPREADSHEET 16 7.2 GAP ANALYSIS RESULTS 16 7.3 GAP ANALYSIS CHECKLIST 17 TECHOP (O-01 - Rev1 - Jan21) DP OPERATIONS MANUAL 3 TECHOP 1 INTRODUCTION 1.1 PREAMBLE 1.1.1 The guidance documents on DP (Design and Operations and People) were published by the MTS DP Technical Committee in 2011, 2010 and 2012, respectively. -
Power System Operations Manual, Chapter 1
Power System Switching Procedure Chapter 1 Effective 2021 POWER SYSTEM OPERATIONS MANUAL WESTERN AREA POWER ADMINISTRATION Page left Blank Intentionally 1 of 83 Version History Table 1 provides the development history of this document. Table 1 Version Information Version Section Action Editor Number 1.4 Replaced CSO Operations Specialist with Supervisory 2013 Power System Dispatcher (AD 6) 2013 6.2.1 Updated link to CCVT information 2013 11 Special Work permits have been removed from the PSOM and are now covered in the PSMM, Chapter 12 2013 App. E Removed “Special Work Permit” template 2014 1.4 Added Senior Power Operations Specialist to review and revision process 2014 3.2 Changed “working days” to “business days” and updated note regarding following regional outage coordination procedures. 2014 6.2.1 Updated hyperlink to new CCVT Hazard policy 2014 6.4.2 Added note regarding tag transfers from previous clearance and added CCVT to list of pertinent equipment for status detail 2014 App A Added ICCP and Switchman Checker to definitions 2015 Preface Modified annual review statement 2015 1.9 Modified section on calling into System Operator and section on security patrols. Added Auto log in information 2015 6.2 Added Clearances shall establish a continuous zone of protection. 2015 8.2 Modified There are no “Safety” tags associated with general switching. 2015 13.2 Overview adjustment for Non-WAPA entity of neighboring utility. 2015 App D Made adjustments to revision form. 2015 App E Example read and review process 2015 App H Modified into one sheet. 2015 General Font & page adjustments throughout document. -

Us Coast Guard Emergency Management Manual, Volume I
U.S. COAST GUARD EMERGENCY MANAGEMENT MANUAL VOLUME I: EMERGENCY MANAGEMENT PLANNING POLICY This page intentionally left blank. Commandant US Coast Guard Stop 7516 United States Coast Guard 2703 Martin Luther King JR Ave SE Washington DC 20593-7516 Staff Symbol: CG-DCO Phone: (202) 372-2141 Fax: (202) 372-8384 Email: [email protected] COMDTCHANGENOTE 3010 7 DEC 2020 COMMANDANT CHANGE NOTICE 3010 Subj: CH-1 TO U.S. COAST GUARD EMERGENCY MANAGEMENT MANUAL, VOLUME I: EMERGENCY MANAGEMENT PLANNING POLICY, COMDTINST M3010.11E 1. PURPOSE. This Commandant Change Notice publishes a change to U.S. Coast Guard Emergency Management Manual, Volume I: Emergency Management Planning Policy, COMDTINST M3010.11E. 2. ACTION. All Coast Guard unit commanders, commanding officers, officers-in-charge, deputy/assistant commandants, and chiefs of headquarters staff elements must comply with the provisions of this Manual. Internet release is authorized. 3. DIRECTIVES AFFECTED. With the addition of this Commandant Change Notice, U.S. Coast Guard Emergency Management Manual, Volume I: Emergency Management Planning Policy, COMDTINST M3010.11E, is updated. 4. DISCLAIMER. This guidance is not a substitute for applicable legal requirements, nor is it itself a rule. It is intended to provide operational guidance for Coast Guard personnel and is not intended to nor does it impose legally-binding requirements on any party outside the Coast Guard. DISTRIBUTION – SDL No. 170 a b c d e f g h i j k l m n o p q r s t u v w x y z A B X X X X C X X X X D X E X F G H X NON-STANDARD DISTRIBUTION: See page 4 COMDTCHANGENOTE 3010 5.