Modelling, Verification, and Comparative Performance Analysis
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

A Comprehensive Study of Routing Protocols Performance with Topological Changes in the Networks Mohsin Masood Mohamed Abuhelala Prof
A comprehensive study of Routing Protocols Performance with Topological Changes in the Networks Mohsin Masood Mohamed Abuhelala Prof. Ivan Glesk Electronics & Electrical Electronics & Electrical Electronics & Electrical Engineering Department Engineering Department Engineering Department University of Strathclyde University of Strathclyde University of Strathclyde Glasgow, Scotland, UK Glasgow, Scotland, UK Glasgow, Scotland, UK mohsin.masood mohamed.abuhelala ivan.glesk @strath.ac.uk @strath.ac.uk @strath.ac.uk ABSTRACT different topologies and compare routing protocols, but no In the modern communication networks, where increasing work has been considered about the changing user demands and advance applications become a functionality of these routing protocols with the topology challenging task for handling user traffic. Routing with real-time network limitations. such as topological protocols have got a significant role not only to route user change, network congestions, and so on. Hence without data across the network but also to reduce congestion with considering the topology with different network scenarios less complexity. Dynamic routing protocols such as one cannot fully understand and make right comparison OSPF, RIP and EIGRP were introduced to handle among any routing protocols. different networks with various traffic environments. Each This paper will give a comprehensive literature review of of these protocols has its own routing process which each routing protocol. Such as how each protocol (OSPF, makes it different and versatile from the other. The paper RIP or EIGRP) does convergence activity with any change will focus on presenting the routing process of each in the network. Two experiments are conducted that are protocol and will compare its performance with the other. -
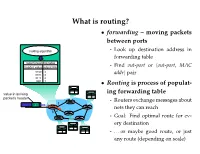
What Is Routing?
What is routing? • forwarding – moving packets between ports - Look up destination address in forwarding table - Find out-port or hout-port, MAC addri pair • Routing is process of populat- ing forwarding table - Routers exchange messages about nets they can reach - Goal: Find optimal route for ev- ery destination - . or maybe good route, or just any route (depending on scale) Routing algorithm properties • Static vs. dynamic - Static: routes change slowly over time - Dynamic: automatically adjust to quickly changing network conditions • Global vs. decentralized - Global: All routers have complete topology - Decentralized: Only know neighbors & what they tell you • Intra-domain vs. Inter-domain routing - Intra-: All routers under same administrative control - Intra-: Scale to ∼100 networks (e.g., campus like Stanford) - Inter-: Decentralized, scale to Internet Optimality A 6 1 3 2 F 1 E B 4 1 9 C D • View network as a graph • Assign cost to each edge - Can be based on latency, b/w, utilization, queue length, . • Problem: Find lowest cost path between two nodes - Must be computed in distributed way Distance Vector • Local routing algorithm • Each node maintains a set of triples - (Destination, Cost, NextHop) • Exchange updates w. directly connected neighbors - periodically (on the order of several seconds to minutes) - whenever table changes (called triggered update) • Each update is a list of pairs: - (Destination, Cost) • Update local table if receive a “better” route - smaller cost - from newly connected/available neighbor • Refresh existing -

The Routing Table V1.12 – Aaron Balchunas 1
The Routing Table v1.12 – Aaron Balchunas 1 - The Routing Table - Routing Table Basics Routing is the process of sending a packet of information from one network to another network. Thus, routes are usually based on the destination network, and not the destination host (host routes can exist, but are used only in rare circumstances). To route, routers build Routing Tables that contain the following: • The destination network and subnet mask • The “next hop” router to get to the destination network • Routing metrics and Administrative Distance The routing table is concerned with two types of protocols: • A routed protocol is a layer 3 protocol that applies logical addresses to devices and routes data between networks. Examples would be IP and IPX. • A routing protocol dynamically builds the network, topology, and next hop information in routing tables. Examples would be RIP, IGRP, OSPF, etc. To determine the best route to a destination, a router considers three elements (in this order): • Prefix-Length • Metric (within a routing protocol) • Administrative Distance (between separate routing protocols) Prefix-length is the number of bits used to identify the network, and is used to determine the most specific route. A longer prefix-length indicates a more specific route. For example, assume we are trying to reach a host address of 10.1.5.2/24. If we had routes to the following networks in the routing table: 10.1.5.0/24 10.0.0.0/8 The router will do a bit-by-bit comparison to find the most specific route (i.e., longest matching prefix). -

P2P Resource Sharing in Wired/Wireless Mixed Networks 1
INT J COMPUT COMMUN, ISSN 1841-9836 Vol.7 (2012), No. 4 (November), pp. 696-708 P2P Resource Sharing in Wired/Wireless Mixed Networks J. Liao Jianwei Liao College of Computer and Information Science Southwest University of China 400715, Beibei, Chongqing, China E-mail: [email protected] Abstract: This paper presents a new routing protocol called Manager-based Routing Protocol (MBRP) for sharing resources in wired/wireless mixed networks. MBRP specifies a manager node for a designated sub-network (called as a group), in which all nodes have the similar connection properties; then all manager nodes are employed to construct the backbone overlay network with ring topology. The manager nodes act as the proxies between the internal nodes in the group and the external world, that is not only for centralized management of all nodes to a certain extent, but also for avoiding the messages flooding in the whole network. The experimental results show that compared with Gnutella2, which uses super-peers to perform similar management work, the proposed MBRP has less lookup overhead including lookup latency and lookup hop count in the most of cases. Besides, the experiments also indicate that MBRP has well configurability and good scaling properties. In a word, MBRP has less transmission cost of the shared file data, and the latency for locating the sharing resources can be reduced to a great extent in the wired/wireless mixed networks. Keywords: wired/wireless mixed network, resource sharing, manager-based routing protocol, backbone overlay network, peer-to-peer. 1 Introduction Peer-to-Peer technology (P2P) is a widely used network technology, the typical P2P network relies on the computing power and bandwidth of all participant nodes, rather than a few gathered and dedicated servers for central coordination [1, 2]. -

Routing As a Service
Routing as a Service Karthik Lakshminarayanan Ion Stoica Scott Shenker Jennifer Rexford University of California, Berkeley Princeton University Abstract configuration, making it difficult to offer meaningful service- level agreements (SLAs) to customers or to identify the AS In Internet routing, there is a fundamental tussle between the responsible for end-to-end performance problems. end users who want control over the end-to-end paths and the An ISP's customers, such as end users, enterprise net- Autonomous Systems (ASes) who want control over the flow works, and smaller ISPs, have even less control over the se- of traffic through their infrastructure. To resolve this tussle lection of end-to-end paths. By connecting to more than one and offer flexible routing control across multiple routing do- ISPs, an enterprise can select from multiple paths [2]; how- mains, we argue that customized route computation should ever, the customer controls only the first hop for outbound be offered as a service by third-party providers. Outsourcing traffic and has (at best) crude influence on incoming traffic. specialized route computation allows different path-selection Yet, some customers need more control over the end-to-end mechanisms to coexist, and evolve over time. path, or at least its properties, to satisfy performance and pol- icy goals. For example, a customer might not want his Web 1 Introduction traffic forwarded through an AS that filters packets based on Interdomain routing has long been based on three pillars: their contents. Alternatively, a customer might need to discard traffic from certain sources to block denial-of-service attacks • Local control: ASes have complete control over routing or protect access to a server storing sensitive data. -

Lab 5.5.2: Examining a Route
Lab 5.5.2: Examining a Route Topology Diagram Addressing Table Device Interface IP Address Subnet Mask Default Gateway S0/0/0 10.10.10.6 255.255.255.252 N/A R1-ISP Fa0/0 192.168.254.253 255.255.255.0 N/A S0/0/0 10.10.10.5 255.255.255.252 10.10.10.6 R2-Central Fa0/0 172.16.255.254 255.255.0.0 N/A N/A 192.168.254.254 255.255.255.0 192.168.254.253 Eagle Server N/A 172.31.24.254 255.255.255.0 N/A host Pod# A N/A 172.16. Pod#.1 255.255.0.0 172.16.255.254 host Pod# B N/A 172.16. Pod#. 2 255.255.0.0 172.16.255.254 S1-Central N/A 172.16.254.1 255.255.0.0 172.16.255.254 All contents are Copyright © 1992–2007 Cisco Systems, Inc. All rights reserved. This document is Cisco Public Information. Page 1 of 7 CCNA Exploration Network Fundamentals: OSI Network Layer Lab 5.5.1: Examining a Route Learning Objectives Upon completion of this lab, you will be able to: • Use the route command to modify a Windows computer routing table. • Use a Windows Telnet client command telnet to connect to a Cisco router. • Examine router routes using basic Cisco IOS commands. Background For packets to travel across a network, a device must know the route to the destination network. This lab will compare how routes are used in Windows computers and the Cisco router. -

Routing Basics
CHAPTER 5 Chapter Goals • Learn the basics of routing protocols. • Learn the differences between link-state and distance vector routing protocols. • Learn about the metrics used by routing protocols to determine path selection. • Learn the basics of how data travels from end stations through intermediate stations and on to the destination end station. • Understand the difference between routed protocols and routing protocols. Routing Basics This chapter introduces the underlying concepts widely used in routing protocols. Topics summarized here include routing protocol components and algorithms. In addition, the role of routing protocols is briefly contrasted with the role of routed or network protocols. Subsequent chapters in Part VII, “Routing Protocols,” address specific routing protocols in more detail, while the network protocols that use routing protocols are discussed in Part VI, “Network Protocols.” What Is Routing? Routing is the act of moving information across an internetwork from a source to a destination. Along the way, at least one intermediate node typically is encountered. Routing is often contrasted with bridging, which might seem to accomplish precisely the same thing to the casual observer. The primary difference between the two is that bridging occurs at Layer 2 (the link layer) of the OSI reference model, whereas routing occurs at Layer 3 (the network layer). This distinction provides routing and bridging with different information to use in the process of moving information from source to destination, so the two functions accomplish their tasks in different ways. The topic of routing has been covered in computer science literature for more than two decades, but routing achieved commercial popularity as late as the mid-1980s. -

Routing Tables
Routing Tables A routing table is a grouping of information stored on a networked computer or network router that includes a list of routes to various network destinations. The data is normally stored in a database table and in more advanced configurations includes performance metrics associated with the routes stored in the table. Additional information stored in the table will include the network topology closest to the router. Although a routing table is routinely updated by network routing protocols, static entries can be made through manual action on the part of a network administrator. How Does a Routing Table Work? Routing tables work similar to how the post office delivers mail. When a network node on the Internet or a local network needs to send information to another node, it first requires a general idea of where to send the information. If the destination node or address is not connected directly to the network node, then the information has to be sent via other network nodes. In order to save resources, most local area network nodes will not maintain a complex routing table. Instead, they will send IP packets of information to a local network gateway. The gateway maintains the primary routing table for the network and will send the data packet to the desired location. In order to maintain a record of how to route information, the gateway will use a routing table that keeps track of the appropriate destination for outgoing data packets. All routing tables maintain routing table lists for the reachable destinations from the router’s location. -

Advanced Routing – Cisco (4 Cr.) Course Description
NVCC COLLEGE-WIDE COURSE CONTENT SUMMARY ITN 250 - Advanced Routing – Cisco (4 cr.) Course Description ITN 250 - Includes instruction focusing on the characteristics of various Routing protocols used in the TCP/IP networking environment, static routing, OSPF, IGRP, EIGRP, IS-IS, BGP, advanced IP addressing, and security. Course content also examines various strategies for optimizing network routing performance. Lecture 4 hours per week. Recommended Pre-requisites Student should: be a Cisco Certified Network Associate (CCNA), or, have successfully completed ITN157 WAN Technologies – Cisco, or have successfully completed TEL251 Internetworking 4, or, have successfully completed CCNA Semester 4 training at a Cisco Network Academy, or, have instructor’s permission. Course Objectives Upon completion of this course, the student will be able to: Selecting and configuring scalable IP addresses Configure the RIP version 2 routing protocol Configure the EIGRP routing protocol Configure Open Shortest Path First protocol in a multi-area environment Configure the IS-IS routing protocol Develop route filtering and policy routing Configure route redistribution Describe the Border Gateway Protocol (BGP) Configure and troubleshoot the BGP routing protocol Course Content Overview of Scalable Internetworks Advanced IP Addressing Management Routing Overview Routing Information Protocol Version 2 EIGRP OSPF IS-IS Route Optimization BGP Student Learning Outcomes Selecting and configuring scalable IP addresses Understand the issues of IP address -
Introduction to Wifi Networking
Introduction to WiFi Networking Marco Zennaro Ermanno Pietrosemoli Goals The goal of this lecture is to introduce: ‣ 802.11 family of radio protocols ‣ 802.11 radio channels ‣ Wireless network topologies ‣ WiFi modes of operation ‣ Strategies for routing network traffic 2 ISM / UNII bands Most commercial wireless devices (mobile phones, television, radio, etc.) use licensed radio frequencies. Large organizations pay licensing fees for the right to use those radio frequencies. WiFi uses unlicensed spectrum. License fees are not usually required to operate WiFi equipment. The Industrial, Scientific and Medical (ISM) bands allow for unlicensed use of 2.4-2.5 GHz, 5.8 GHz, and many other (non-WiFi) frequencies. 3 802.11 family 4 802.11 family 5 Wireless networking protocols The 802.11 family of radio protocols are commonly referred to as WiFi. • 802.11a supports up to 54 Mbps using the 5 GHz unlicensed bands. • 802.11b supports up to 11 Mbps using the 2.4 GHz unlicensed band. • 802.11g supports up to 54 Mbps using the 2.4 GHz unlicensed band. • 802.11n supports up to 600 Mbps using the 2.4 GHz and 5 GHz unlicensed bands. • 802.16 (WiMAX) is not 802.11 WiFi! It is a completely different technology that uses a variety of licensed and unlicensed frequencies. 6 Compatibility of standards AP 802.11a 802.11b 802.11g 802.11n 802.16 Yes C 802.11a Yes @5GHz L Yes Yes 802.11b Yes I (slower) @2.4GHz Yes Yes E 802.11g Yes (slower) @2.4GHz N Yes Yes Yes 802.11n Yes T @5GHz @2.4GHz @2.4GHz 802.16 Yes 7 IEEE 802.11 AC Improved performance by means of: • Two or up to 8 Spatial streams (MIMO) • Higher order modulation types (up to 256 QAM) • Wider Channels bandwidth (up to 160 MHz) 8 IEEE 802.11 AC: MIMO 9 IEEE 802.11 AC, 256 constellation 1 0 Data rates Note that the “data rates” quoted in the WiFi specifications refer to the raw radio symbol rate, not the actual TCP/IP throughput rate. -

Introduction to the Border Gateway Protocol – Case Study Using GNS3
Introduction to The Border Gateway Protocol – Case Study using GNS3 Sreenivasan Narasimhan1, Haniph Latchman2 Department of Electrical and Computer Engineering University of Florida, Gainesville, USA [email protected], [email protected] Abstract – As the internet evolves to become a vital resource for many organizations, configuring The Border Gateway protocol (BGP) as an exterior gateway protocol in order to connect to the Internet Service Providers (ISP) is crucial. The BGP system exchanges network reachability information with other BGP peers from which Autonomous System-level policy decisions can be made. Hence, BGP can also be described as Inter-Domain Routing (Inter-Autonomous System) Protocol. It guarantees loop-free exchange of information between BGP peers. Enterprises need to connect to two or more ISPs in order to provide redundancy as well as to improve efficiency. This is called Multihoming and is an important feature provided by BGP. In this way, organizations do not have to be constrained by the routing policy decisions of a particular ISP. BGP, unlike many of the other routing protocols is not used to learn about routes but to provide greater flow control between competitive Autonomous Systems. In this paper, we present a study on BGP, use a network simulator to configure BGP and implement its route-manipulation techniques. Index Terms – Border Gateway Protocol (BGP), Internet Service Provider (ISP), Autonomous System, Multihoming, GNS3. 1. INTRODUCTION Figure 1. Internet using BGP [2]. Routing protocols are broadly classified into two types – Link State In the figure, AS 65500 learns about the route 172.18.0.0/16 through routing (LSR) protocol and Distance Vector (DV) routing protocol. -

The Routing Table Lookup Process
The Routing Table Part 2 – The Routing Table Lookup Process By Rick Graziani Cisco Networking Academy [email protected] Updated: Oct. 10, 2002 This document is the second of two parts dealing with the routing table. Part I discussed the structure of the routing table, and how routes are created. Part II will discuss how the routing table lookup process finds the “best” route within the routing table. What happens when a router receives an IP packet, examines the IP destination address and looks that address up in the routing table? How does the router decide which route in the routing table is the best match? What affect does the subnet mask have on the routing table? How does the router decide whether or not to use a supernet or default route if there is not a better match? We will answer these questions and more in this document. The network we will be using is a simple three router network. RouterA and Router B share the common major network 172.16.0.0/24. RouterB and RouterC are connected by the 192.168.1.0/24 network. You will notice that RouterC also has a 172.16.4.0/24 subnet which is disconnected, or discontiguous, from the rest of the 172.16.0.0 network. 172.16.1.0/24 172.16.3.0/24 172.16.4.0/24 .1 fa0 .1 fa0 .1 fa0 .1 172.16.2.0/24 .2 .1 192.168.1.0/24 .2 s0 s0 s1 s0 Router A Router B Router C Most of this information is best explained by using examples.