A Template-Based Approach to Automatic Program Repair of Sonarqube Static Warnings
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Applicable for the Academic Year 2020-21 Batch: 2017
Applicable for the academicyear2018-19 Batch:2015 SCHEME & SYLLABUS OF VII & VIIISEMESTERS B.E. COMPUTER SCIENCE AND ENGINEERING 2020-21 Vision and Mission of theInstitution: Vision: Dept. of CSE, SIT, Tumakuru Applicable for the academic year 2020-21 Batch: 2017 Vision and Mission of the Institution: Vision: “To develop young minds in a learning environment of high academic ambience by synergizing spiritual values and technological competence”. Mission: “To continuously strive for the total development of students by educating them in state-of-the-art technologies and helping them imbibe professional ethics and societal commitment, so that they emerge as competent professionals to meet the global challenges”. Vision and Mission of the Department: Vision: “To work towards the vision of the institution by building a strong teaching and research environment that is capable of responding to the challenges of the 21st century”. Mission: “To prepare under graduate, graduate and research students for productive careers in industry and academia, through comprehensive educational programs, research in collaboration with industry & government, dissemination by scholarly publications and professional society & co- curricular activities”. Program Educational Objectives (PEOs) Engineering graduates (CSE) will be able to: 1. Pursue successful careers in State/National/Multi-National companies as software developers by following sound professional and ethical practices in various cadres in key areas like networking, web design, cloud computing, big data processing, IoT, e-commerce, information security and so on. 2. Work effectively in multi-disciplinary and multi-cultural teams and demonstrate good soft skills. 3. Pursue higher education for a successful career in industry/academics/ research. 4. Pursue life-long learning, by anticipating trends in computer science and engineering, to excel in industry/academia or own a startup for a successful career as entrepreneur. -

Command Line Interface
Command Line Interface Squore 21.0.2 Last updated 2021-08-19 Table of Contents Preface. 1 Foreword. 1 Licence. 1 Warranty . 1 Responsabilities . 2 Contacting Vector Informatik GmbH Product Support. 2 Getting the Latest Version of this Manual . 2 1. Introduction . 3 2. Installing Squore Agent . 4 Prerequisites . 4 Download . 4 Upgrade . 4 Uninstall . 5 3. Using Squore Agent . 6 Command Line Structure . 6 Command Line Reference . 6 Squore Agent Options. 6 Project Build Parameters . 7 Exit Codes. 13 4. Managing Credentials . 14 Saving Credentials . 14 Encrypting Credentials . 15 Migrating Old Credentials Format . 16 5. Advanced Configuration . 17 Defining Server Dependencies . 17 Adding config.xml File . 17 Using Java System Properties. 18 Setting up HTTPS . 18 Appendix A: Repository Connectors . 19 ClearCase . 19 CVS . 19 Folder Path . 20 Folder (use GNATHub). 21 Git. 21 Perforce . 23 PTC Integrity . 25 SVN . 26 Synergy. 28 TFS . 30 Zip Upload . 32 Using Multiple Nodes . 32 Appendix B: Data Providers . 34 AntiC . 34 Automotive Coverage Import . 34 Automotive Tag Import. 35 Axivion. 35 BullseyeCoverage Code Coverage Analyzer. 36 CANoe. 36 Cantata . 38 CheckStyle. .. -
Tracking Known Security Vulnerabilities in Third-Party Components
Tracking known security vulnerabilities in third-party components Master’s Thesis Mircea Cadariu Tracking known security vulnerabilities in third-party components THESIS submitted in partial fulfillment of the requirements for the degree of MASTER OF SCIENCE in COMPUTER SCIENCE by Mircea Cadariu born in Brasov, Romania Software Engineering Research Group Software Improvement Group Department of Software Technology Rembrandt Tower, 15th floor Faculty EEMCS, Delft University of Technology Amstelplein 1 - 1096HA Delft, the Netherlands Amsterdam, the Netherlands www.ewi.tudelft.nl www.sig.eu c 2014 Mircea Cadariu. All rights reserved. Tracking known security vulnerabilities in third-party components Author: Mircea Cadariu Student id: 4252373 Email: [email protected] Abstract Known security vulnerabilities are introduced in software systems as a result of de- pending on third-party components. These documented software weaknesses are hiding in plain sight and represent the lowest hanging fruit for attackers. Despite the risk they introduce for software systems, it has been shown that developers consistently download vulnerable components from public repositories. We show that these downloads indeed find their way in many industrial and open-source software systems. In order to improve the status quo, we introduce the Vulnerability Alert Service, a tool-based process to track known vulnerabilities in software projects throughout the development process. Its usefulness has been empirically validated in the context of the external software product quality monitoring service offered by the Software Improvement Group, a software consultancy company based in Amsterdam, the Netherlands. Thesis Committee: Chair: Prof. Dr. A. van Deursen, Faculty EEMCS, TU Delft University supervisor: Prof. Dr. A. -
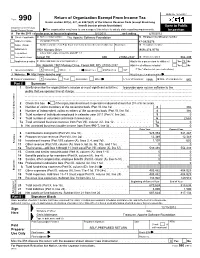
Return of Organization Exempt from Income
OMB No. 1545-0047 Return of Organization Exempt From Income Tax Form 990 Under section 501(c), 527, or 4947(a)(1) of the Internal Revenue Code (except black lung benefit trust or private foundation) Open to Public Department of the Treasury Internal Revenue Service The organization may have to use a copy of this return to satisfy state reporting requirements. Inspection A For the 2011 calendar year, or tax year beginning 5/1/2011 , and ending 4/30/2012 B Check if applicable: C Name of organization The Apache Software Foundation D Employer identification number Address change Doing Business As 47-0825376 Name change Number and street (or P.O. box if mail is not delivered to street address) Room/suite E Telephone number Initial return 1901 Munsey Drive (909) 374-9776 Terminated City or town, state or country, and ZIP + 4 Amended return Forest Hill MD 21050-2747 G Gross receipts $ 554,439 Application pending F Name and address of principal officer: H(a) Is this a group return for affiliates? Yes X No Jim Jagielski 1901 Munsey Drive, Forest Hill, MD 21050-2747 H(b) Are all affiliates included? Yes No I Tax-exempt status: X 501(c)(3) 501(c) ( ) (insert no.) 4947(a)(1) or 527 If "No," attach a list. (see instructions) J Website: http://www.apache.org/ H(c) Group exemption number K Form of organization: X Corporation Trust Association Other L Year of formation: 1999 M State of legal domicile: MD Part I Summary 1 Briefly describe the organization's mission or most significant activities: to provide open source software to the public that we sponsor free of charge 2 Check this box if the organization discontinued its operations or disposed of more than 25% of its net assets. -

Tech Staffing Case Study
TECH STAFFING CASE STUDY A comprehensive analysis of Andiamo’s technology recruiting success with Startups. Stang Success Story Andiamo is the top-rated stang partner for over 30 elite tech startups across the country. Andiamo helps these startup clients build out their technology divisions by finding the best and brightest technologists from top universities and elite companies. Through our data-driven recruiting model, we find success by tackling hiring challenges and placing engineers and developers at the most sought after startup companies. START UP HIRING NEEDS Positions: Full Stack Developer, Software Engineer, Big Data Engineer, SRE, Technical Project Manager, Mobile Developer Technologies: Java, Scala, Ruby, Python, Javascript (Angular.JS, React.JS, Node.JS), MongoDB, AWS, Docker, Chef, Puppet, Spark, OUR DELIVERY To meet our clients’ stang needs, Andiamo helps specific teams attract and hire the POSITIONS FILLED best engineering talent in the country. We leverage massive amounts of data to conduct 49 research analyzing national hiring and salary trends which help fill niche positions. Some of the startup clients we recruit on behalf of include: 25 6 9 5 4 Full Stack TPM Software Mobile UX/UI Database Developer Engineer Dev. FLATIRON DEVELOPERS PLACED The data below represents the profiles of developers that Andiamo has placed with Startups. AVERAGE YEARS FIELD OF STUDY SCHOOLS ATTENDED OF EXPERIENCE: 11 5% • Columbia University 5% Software Information Engineering • RPI Science 3% EDUCATION 5% Economics • University of Texas at Austin Mathematics • Cornell University 8% • University of Chicago at Illinois 34% Electrical Engineering 54% 65% 9% Computer Science TECH SKILLSET 5% Computer Engineering 5% Java 2% Other Front End (Angular/React) Assoc. -

Coverity Static Analysis
Coverity Static Analysis Quickly find and fix Overview critical security and Coverity® gives you the speed, ease of use, accuracy, industry standards compliance, and quality issues as you scalability that you need to develop high-quality, secure applications. Coverity identifies code critical software quality defects and security vulnerabilities in code as it’s written, early in the development process when it’s least costly and easiest to fix. Precise actionable remediation advice and context-specific eLearning help your developers understand how to fix their prioritized issues quickly, without having to become security experts. Coverity Benefits seamlessly integrates automated security testing into your CI/CD pipelines and supports your existing development tools and workflows. Choose where and how to do your • Get improved visibility into development: on-premises or in the cloud with the Polaris Software Integrity Platform™ security risk. Cross-product (SaaS), a highly scalable, cloud-based application security platform. Coverity supports 22 reporting provides a holistic, more languages and over 70 frameworks and templates. complete view of a project’s risk using best-in-class AppSec tools. Coverity includes Rapid Scan, a fast, lightweight static analysis engine optimized • Deployment flexibility. You for cloud-native applications and Infrastructure-as-Code (IaC). Rapid Scan runs decide which set of projects to do automatically, without additional configuration, with every Coverity scan and can also AppSec testing for: on-premises be run as part of full CI builds with conventional scan completion times. Rapid Scan can or in the cloud. also be deployed as a standalone scan engine in Code Sight™ or via the command line • Shift security testing left. -

Robert Munteanu, Adobe
Cloud-Native Legacy Applications Robert Munteanu, Adobe Slides revision: 20190922-478c9cc 1 Welcome 2 About me 3 Outline Welcome Cloud-native vs legacy Managing cloud-native applications Cloud-native transformation 4 Cloud-native vs legacy 5 Cloud-native applications 6 Defining cloud-native Using cloud-native services Application-centric design Automation Cloud Native Architectures - Kamal Arora, Erik Farr, Tom Laszewski, Piyum Zonooz 7 Cloud-native services Logging: StackDriver, Centralised Logging, Logging and Auditing Routing: ELB, Azure Load Balancer, Cloud Load Balancing Block storage: Azure Blob Store, S3, Cloud Storage Databases: RDS, Cloud SQL, Azure SQL Database 8 Application-centric design 9 Automation 1. Building 2. Testing 3. Integration 4. Deployment 5. Monitoring 6. Capacity adjustment 10 LLLeeegggaaacccyyy fffooorrr eeevvveeerrryyyooonnneee 11 LLLeeegggaaacccyyy fffooorrr ppprrrooogggrrraaammmmmmeeerrrsss 12 Legacy applications legacy /ˈlɛɡəsi/ 1. an amount of money or property le to someone in a will. 2. soware or hardware that has been superseded but is difficult to replace because of its wide use https://www.lexico.com/en/definition/legacy 13 Managing cloud-native applications 14 Containers, container, containers FROM openjdk:8-jre-alpine MAINTAINER [email protected] RUN mkdir -p /opt/sling COPY target/sling-cloud-ready-*.jar /opt/sling/sling.jar WORKDIR /opt/sling EXPOSE 8080 VOLUME /opt/sling/sling ENV JAVA_OPTS -Xmx512m ENV SLING_OPTS '' CMD exec java $JAVA_OPTS -jar sling.jar $SLING_OPTS 15 Kubernetes 16 Kubernetes -
Apachecon EU 08 Fast Feather Track Presentation on Sling
Apache Sling Felix Meschberger Day Management AG [email protected] General Request Processing request ResourceResolver Resource (resource type) ServletResolver Servlet Script response Virtual Resource Tree · Based on JCR Repository · Integrates with mapped Resources ± Resources from OSGi Bundles ± Servlets and Servlet Filters registered as OSGi Services · Unified access to Data from various sources · Primary Target is the JCR Repository URI Decomposition /content/page.print.a4.html Resource Path Selectors Extension Servlet and Script Resolution · Scripts and Servlets are Equal ± Servlets registered as OSGi Services are mapped into the virtual Resource Tree ± Scripts stored in the Repository · Default Servlets (or Scripts) ± Registerable ± Fallback / Last Ressort ScriptResolver · Path to Script built from ... · Configured Path ( /apps, /libs ) · Resource Type converted to path ( nt/file ) · Selector String ( print/a4) · Request Method & MIME Type ± GET --> Request URL Extension ( html ) ± else --> Method Name ( POST, PUT, ... ) ScriptResolver Example · URI: /content/page.print.a4.html · Resource: /content/page · Resource Type: sample:page · Script for GET: ± /sling/scripts/sample/page/print/a4/html.* · Script for POST: ± /sling/scripts/sample/page/print/a4/POST.* Facts · Sling API ± No Reference to JCR API · Modular and Runtime Configurable ± OSGi Framework · Two Deployment ± Standalone Java Application ± Web Application Standalone Java Application · One single executable JAR file · Small Launcher · Starts OSGi Framework (Apache Felix) · Uses Jetty in an OSGi Bundle Web Application · Extends Standalone Application ± Replaces Command Line Support with a Servlet · Uses a Bridge to connect Sling to the Servlet Container Questions One Last Word Visit http://dev.day.com/ . -

DATASHEET Federal
DATASHEET Federal The next generation of application performance management Distributed web applications often contain frustrating blind spots KEY BENEFITS FOR FEDERAL IT TEAMS and mysterious, recurring problems. Only AppDynamics delivers – Visualize your entire application, from the simplicity, visibility, and deep diagnostics that Ops and Dev the browser to the database teams require. – Monitor hybrid environments with The new world of government applications has created a whole new set of Java, .NET and PHP challenges for agencies tasked with ensuring application health and performance. – Troubleshoot bottlenecks 90% faster Modern application architectures, new technologies, and a rapid rate of change with code-level diagnostics have created a perfect storm of complexity in today’s applications. As a result, performance problems surface that are often difficult to identify, diagnose, and fix. – Automate common fixes with Application Run Book Automation With AppDynamics, federal IT teams can efficiently consolidate resources by optimizing the performance of applications. It’s more important than ever to have a simple yet fast way to monitor, diagnose, and resolve application problems before they affect revenue. Introducing AppDynamics for federal agencies “Our Mean-Time-to- Repair With AppDynamics, agency IT organizations can: used to be days or hours. – Proactively monitor end user experience from any location and cities With AppDynamics, it’s now a matter of minutes.” – Auto-discover and map application and transactions without manual -

A Comparison of SPARK with MISRA C and Frama-C
A Comparison of SPARK with MISRA C and Frama-C Johannes Kanig, AdaCore October 2018 Abstract Both SPARK and MISRA C are programming languages intended for high-assurance applications, i.e., systems where reliability is critical and safety and/or security requirements must be met. This document summarizes the two languages, compares them with respect to how they help satisfy high-assurance requirements, and compares the SPARK technology to several static analysis tools available for MISRA C with a focus on Frama-C. 1 Introduction 1.1 SPARK Overview Ada [1] is a general-purpose programming language that has been specifically designed for safe and secure programming. Information on how Ada satisfies the requirements for high-assurance software, including the avoidance of vulnerabilities that are found in other languages, may be found in [2, 3, 4]. SPARK [5, 6] is an Ada subset that is amenable to formal analysis and thus can bring increased confidence to software requiring the highest levels of assurance. SPARK excludes features that are difficult to analyze (such as pointers and exception handling). Its restrictions guarantee the absence of unspecified behavior such as reading the value of an uninitialized variable, or depending on the evaluation order of expressions with side effects. But SPARK does include major Ada features such as generic templates and object-oriented programming, as well as a simple but expressive set of concurrency (tasking) features known as the Ravenscar profile. SPARK has been used in a variety of high-assurance applications, including hypervisor kernels, air traffic management, and aircraft avionics. In fact, SPARK is more than just a subset of Ada. -

Trace-Based Debloat for Java Bytecode a ∗ a a a César Soto-Valero , , Thomas Durieux , Nicolas Harrand and Benoit Baudry
Trace-based Debloat for Java Bytecode a < a a a César Soto-Valero , , Thomas Durieux , Nicolas Harrand and Benoit Baudry aKTH Royal Institute of Technology, SE-100 44 Stockholm, Sweden ARTICLEINFO ABSTRACT Keywords: Software bloat is code that is packaged in an application but is actually not used and not necessary software bloat to run the application. The presence of bloat is an issue for software security, for performance, and dynamic analysis for maintenance. In this paper, we introduce a novel technique to debloat Java bytecode through program specialization dynamic analysis, which we call trace-based debloat. We have developed JDBL, a tool that automates build automation the collection of accurate execution traces and the debloating process. Given a Java project and a software maintenance workload, JDBL generates a debloated version of the project that is syntactically correct and preserves the original behavior, modulo the workload. We evaluate JDBL by debloating 395 open-source Java libraries for a total 10M+ lines of code. Our results indicate that JDBL succeeds in debloating 62:2 ~ of the classes, and 20:5 ~ of the dependencies in the studied libraries. Meanwhile, we present the first experiment that assesses the quality of debloated libraries with respect to 1;066 clients of these libraries. We show that 957/1;001 (95:6 ~) of the clients successfully compile, and 229/283 (80:9 ~) clients can successfully run their test suite, after the drastic code removal among their libraries. 1. Introduction We address this challenge through the combination of fea- tures provided by the diversity of implementations of code Software systems have a natural tendency to grow over coverage tools. -

Contents Qus: Technology Stack of CQ5 and Describe Each One?
Contents Qus: Technology Stack of CQ5 and describe each one? ..................................................................... 3 Inside CQ5 ........................................................................................................................................... 4 Server Startup Sequence..................................................................................................................... 5 Qus: What is cq5 Architecture ............................................................................................................ 5 Qus: How to use multi language translation in JSP in CQ / WEM ....................................................... 9 Qus: How to connect external DB from CQ5? .................................................................................. 12 Qus: What is Segmentation?............................................................................................................. 15 SEGMENTATION IN CQ .......................................................................................................... 17 DEFINING A NEW SEGMENT ................................................................................................ 19 USING AND AND OR CONTAINERS .................................................................................... 21 TESTING THE APPLICATION OF A SEGMENT ................................................................. 22 Qus: Campaign Management ..........................................................................................................