Hackthiszine5.Pdf
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

"Ephemeral Data" and the Duty to Preserve Discoverable Electronically Stored Information Kenneth J
University of Baltimore Law Review Volume 37 Article 4 Issue 3 Spring 2008 2008 "Ephemeral Data" and the Duty to Preserve Discoverable Electronically Stored Information Kenneth J. Withers The Sedona Conference Follow this and additional works at: http://scholarworks.law.ubalt.edu/ublr Part of the Law Commons Recommended Citation Withers, Kenneth J. (2008) ""Ephemeral Data" and the Duty to Preserve Discoverable Electronically Stored Information," University of Baltimore Law Review: Vol. 37: Iss. 3, Article 4. Available at: http://scholarworks.law.ubalt.edu/ublr/vol37/iss3/4 This Article is brought to you for free and open access by ScholarWorks@University of Baltimore School of Law. It has been accepted for inclusion in University of Baltimore Law Review by an authorized administrator of ScholarWorks@University of Baltimore School of Law. For more information, please contact [email protected]. "EPHEMERAL DATA" AND THE DUTY TO PRESERVE DISCOVERABLE ELECTRONICALLY STORED INFORMATION Kenneth J. Witherst I. ELECTRONIC ALL Y STORED INFORMATION AND THE DUTY OF PRESERVATION UNDER THE RULES OF CIVIL PROCEDURE The duty to take reasonable steps to preserve evidence discoverable in pending or anticivated civil litigation is well established in U.S. civil jurisprudence. Courts differ about when the duty of preservation is triggered, the particular scope of that duty, and what steps of preservation are considered reasonable on a case-by-case basis,2 but the general rule is clear: parties have a duty to preserve t Kenneth J. Withers is Director of Judicial Education and Content for The Sedona Conference®, a non-profit law and policy think-tank based in Arizona. -

Exinda Applications List
Application List Exinda ExOS Version 6.4 © 2014 Exinda Networks, Inc. 2 Copyright © 2014 Exinda Networks, Inc. All rights reserved. No parts of this work may be reproduced in any form or by any means - graphic, electronic, or mechanical, including photocopying, recording, taping, or information storage and retrieval systems - without the written permission of the publisher. Products that are referred to in this document may be either trademarks and/or registered trademarks of the respective owners. The publisher and the author make no claim to these trademarks. While every precaution has been taken in the preparation of this document, the publisher and the author assume no responsibility for errors or omissions, or for damages resulting from the use of information contained in this document or from the use of programs and source code that may accompany it. In no event shall the publisher and the author be liable for any loss of profit or any other commercial damage caused or alleged to have been caused directly or indirectly by this document. Document Built on Tuesday, October 14, 2014 at 5:10 PM Documentation conventions n bold - Interface element such as buttons or menus. For example: Select the Enable checkbox. n italics - Reference to other documents. For example: Refer to the Exinda Application List. n > - Separates navigation elements. For example: Select File > Save. n monospace text - Command line text. n <variable> - Command line arguments. n [x] - An optional CLI keyword or argument. n {x} - A required CLI element. n | - Separates choices within an optional or required element. © 2014 Exinda Networks, Inc. -
P2P and Bittorrent
inf5040 - Presentation by group 1 nghial, baardehe, chricar 30.10.08 Goals of today After this lecture you should have a general understanding of what P2P and bittorrent is be able to recognize the main differences of bitTorrent and other P2P networks A way of organizing resource sharing in computer networks What is P2P? Server/client model Peer-to-peer model Characteristics of P2P networks Peers act as equals Peers function as both client and server No central server managing the network No central router Examples of ”pure” P2P networks Gnutella, Freenet (filesharing) In short Decentralization and multirole BUT! Most networks and applications described as P2P actually contain or rely on some non-peer elements History 1970 – SMTP, NNTP (Usenet) One process both server and client IBM, 1984 ”Advanced Peer to Peer Networking” Software for filesharing in a LAN 1990 – IRC (DCC), MBONE One client can both send and receive 1997 – Napster Created a lot of controversy Convicted because of the centralized file indexing Advantages of P2P networks Better performance and reliability compared to server/client scheme Popular resources will be available at several locations Principle of locality -> less delay and faster transmission Overlay routing Application layer routing (middleware) Two ways of searching for files Flooding DHT (Distributed Hash Table) Area of application Mostly used in ad hoc networks Often categorized by what it’s used for Filesharing Media streaming Telephony (skype) Discussion forums Used to distribute -

The Application Layer: Overview
The Application Layer: Overview ▪ P2P applications ▪ Principles of network ▪ video streaming and applications content distribution ▪ Web and HTTP networks ▪ E-mail, SMTP, IMAP ▪ socket programming with ▪ The Domain Name System UDP and TCP DNS 1 Peer-to-peer (P2P) Architecture ▪no always-on server ▪arbitrary end systems directly mobile network communicate national or global ISP ▪peers request service from other peers, provide service in return to other peers • self scalability – new peers bring new local or service capacity, and new service regional ISP demands home network content ▪peers are intermittently provider network datacenter connected and change IP network addresses • complex management enterprise ▪examples: P2P file sharing network (BitTorrent), streaming (KanKan), VoIP (Skype) 2 File distribution: client-server vs P2P Q: how much time to distribute file (size F) from one server to N peers? • peer upload/download capacity is limited resource us: server upload capacity di: peer i file, size F u1 d us 1 u2 d download capacity server 2 di uN network (with abundant bandwidth) ui dN ui: peer i upload capacity 3 File distribution time: client-server ▪server transmission: must sequentially send (upload) N file copies: F us • time to send one copy: F/us di • time to send N copies: NF/us network u ▪ client: each client must i download file copy • dmin = min client download rate • min client download time: F/dmin time to distribute F to N clients using Dc-s > max{NF/us,,F/dmin} client-server approach increases linearly in N 4 File distribution time: P2P ▪server transmission: must upload at least one copy: • time to send one copy: F/u F s us d ▪ client: each client must i network download file copy ui • min client download time: F/dmin ▪ clients: as aggregate must download NF bits • max upload rate (limiting max download rate) is us + Σui time to distribute F to N clients using DP2P > max{F/us,,F/dmin,,NF/(us + Σui)} P2P approach increases linearly in N … … but so does this, as each peer brings service capacity 5 Client-server vs. -
Hacker, Hoaxer, Whistleblower, Spy: the Story of Anonymous
hacker, hoaxer, whistleblower, spy hacker, hoaxer, whistleblower, spy the many faces of anonymous Gabriella Coleman London • New York First published by Verso 2014 © Gabriella Coleman 2014 The partial or total reproduction of this publication, in electronic form or otherwise, is consented to for noncommercial purposes, provided that the original copyright notice and this notice are included and the publisher and the source are clearly acknowledged. Any reproduction or use of all or a portion of this publication in exchange for financial consideration of any kind is prohibited without permission in writing from the publisher. The moral rights of the author have been asserted 1 3 5 7 9 10 8 6 4 2 Verso UK: 6 Meard Street, London W1F 0EG US: 20 Jay Street, Suite 1010, Brooklyn, NY 11201 www.versobooks.com Verso is the imprint of New Left Books ISBN-13: 978-1-78168-583-9 eISBN-13: 978-1-78168-584-6 (US) eISBN-13: 978-1-78168-689-8 (UK) British Library Cataloguing in Publication Data A catalogue record for this book is available from the British library Library of Congress Cataloging-in-Publication Data A catalog record for this book is available from the library of congress Typeset in Sabon by MJ & N Gavan, Truro, Cornwall Printed in the US by Maple Press Printed and bound in the UK by CPI Group Ltd, Croydon, CR0 4YY I dedicate this book to the legions behind Anonymous— those who have donned the mask in the past, those who still dare to take a stand today, and those who will surely rise again in the future. -

Web 2.0 Enabled Classroom
7/16/2010 Agenda Market Evolution and Trends Where to Begin Web Questions?2.0 Enabled Introduction to Unified Performance Management Case Studies Classroom © 2002 – 2010, Exinda Networks Inc. Proprietary & Confidential © 2002 – 2010, Exinda Networks Inc. Proprietary & Confidential Performance You Can See Performance You Can See 1 7/16/2010 Exinda at a Glance Founded in 2002 Melbourne based Leading provider of WAN optimization solutions Privately held with venture capital financing Market Evolution Over 3,000 customers Questions? Several thousand appliances deployed in 40+ countries & Trends Worldwide distribution © 2002 – 2010, Exinda Networks Inc. Proprietary & Confidential © 2002 – 2010, Exinda Networks Inc. Proprietary & Confidential Performance You Can See Performance You Can See 2 7/16/2010 Market Evolution & Trends Market Evolution & Trends Top five bandwidth heavy websites were: 1. YouTube – 10% of all bandwidth used 2. Facebook – 4.5% 3. Windows Update – 3.3% “On average, 37% of network capacity has 4. Yimg (Yahoo!'s image server) – 2.7% been occupied by traffic that is not business- 5. Google – 2.5% critical.” - Aberdeen Group, “Application Performance Management: When 250 IT managers were asked about their biggest Getting IT on the C-Level Agenda”, March 2009 security concerns, the top answer was "employees using applications on social networks" while at work. Source: Network Box, 20th April, 2010 © 2002 – 2010, Exinda Networks Inc. Proprietary & Confidential © 2002 – 2010, Exinda Networks Inc. Proprietary & Confidential Performance You Can See Performance You Can See 3 7/16/2010 Market Evolution & Trends Market Evolution & Trends The Council of Australian University Directors Australia Is Social Networking Capital Of The World of Information Technology (CAUDIT) have TELEGRAPH.CO.UK - Mar 3 - According to Nielsen, indicated that traffic is typically doubling Australia's web users are at the forefront of the social networking craze, posting, poking and every nine months (250 per cent a year). -
Bittorrent (Protocol) 1 Bittorrent (Protocol)
BitTorrent (protocol) 1 BitTorrent (protocol) BitTorrent is a peer-to-peer file sharing protocol used for distributing large amounts of data over the Internet. BitTorrent is one of the most common protocols for transferring large files and it has been estimated that peer-to-peer networks collectively have accounted for roughly 43% to 70% of all Internet traffic (depending on geographical location) as of February 2009.[1] Programmer Bram Cohen designed the protocol in April 2001 and released a first implementation on July 2, 2001.[2] It is now maintained by Cohen's company BitTorrent, Inc. There are numerous BitTorrent clients available for a variety of computing platforms. As of January 2012 BitTorrent has 150 million active users according to BitTorrent Inc.. Based on this the total number of monthly BitTorrent users can be estimated at more than a quarter billion.[3] At any given instant of time BitTorrent has, on average, more active users than YouTube and Facebook combined. (This refers to the number of active users at any instant and not to the total number of unique users.)[4][5] Description The BitTorrent protocol can be used to reduce the server and network impact of distributing large files. Rather than downloading a file from a single source server, the BitTorrent protocol allows users to join a "swarm" of hosts to download and upload from each other simultaneously. The protocol is an alternative to the older single source, multiple mirror sources technique for distributing data, and can work over networks with lower bandwidth so many small computers, like mobile phones, are able to efficiently distribute files to many recipients. -
Intellectual Property Update
INTELLECTUAL PROPERTY UPDATE FALA WINTER MEETING 2008 By Gregory A. Piccionelli Piccionelli & Sarno Introduction I. Copyrights Destruction Of Evidence Is A Significant Factor In MPAA Victory In Torrentspy.Com Copyright Infringement Action Columbia Pictures Industries, et al v. Justin Bunneli, et al, U.S. District Court for the Central District of California, Case No. CV 06-1093 FMC (JCx) The Motion Picture Association of America (MPAA) has prevailed in a significant ruling against the operators of the website “TorrentSpy.com”, largely based upon the judge’s determination the defendants tampered with evidence. In a ruling that could have implications for the privacy of website users, Judge Florence- Marie Cooper of the U.S. District Court for the Central District of California, ruled that that TorrentSpy.com infringed plaintiff’s copyrights in a default judgment against the operators of the bit torrent site. The judge agreed with the plaintiff that the defendants had destroyed important evidence after another judge had ordered them to preserve server logs, user IP (Internet Protocol) addresses and other information. Defendants have described the TorrentSpy technology as a means to find files distributed on BitTorrent peer-to-peer networks. According to the Judge Cooper, the defendants' conduct was “obstreperous”. In her opinion, she wrote that the defendants “engaged in widespread and systematic efforts to destroy evidence and have provided false testimony under oath in a effort to hide evidence of such destruction.” The judge also noted that “[d]efendants were on notice that this information would be of importance in this case.” TorrentSpy had located its servers in the Netherlands and argued that Dutch law protected them from having to turn over server logs and other information. -
Crawling Bittorrent Dhts for Fun and Profit
Crawling BitTorrent DHTs for Fun and Profit Scott Wolchok and J. Alex Halderman The University of Michigan {swolchok, jhalderm}@eecs.umich.edu Abstract major torrent discovery sites and the major trackers [1,29] is feasible. Though a boon to copyright enforcement, this This paper presents two kinds of attacks based on crawl- capability reduces the privacy of BitTorrent downloaders ing the DHTs used for distributed BitTorrent tracking. by making it much harder to “hide in the crowd.” First, we show how pirates can use crawling to rebuild The BitTorrent community has responded to these BitTorrent search engines just a few hours after they are trends by deploying decentralizing tracking systems based shut down (crawling for fun). Second, we show how on distributed hash tables (DHTs). So far, their impact content owners can use related techniques to monitor pi- on privacy and copyright enforcement has been unclear. rates’ behavior in preparation for legal attacks and negate Distributed tracking is harder to disrupt through legal any perceived anonymity of the decentralized BitTorrent threats, but users still rely on centralized torrent discov- architecture (crawling for profit). ery sites that remain relatively easy targets. Some might We validate these attacks and measure their perfor- expect that decentralizing the tracking architecture would mance with a crawler we developed for the Vuze DHT. enhance privacy by making monitoring more difficult, but We find that we can establish a search engine with over the question has received little research attention to date. one million torrents in under two hours using a single In this work, we demonstrate how deployed distributed desktop PC. -

United States Court of Appeals for the Ninth Circuit
Case: 10-55946 12/17/2010 Page: 1 of 92 ID: 7585231 DktEntry: 18 Docket No. 10-55946 In the United States Court of Appeals For the Ninth Circuit COLUMBIA PICTURES INDUSTRIES, INC., DISNEY ENTERPRISES, INC., PARAMOUNT PICTURES CORPORATION, TRISTAR PICTURES, INC., TWENTIETH CENTURY FOX FILM CORPORATION, UNIVERSAL CITY STUDIOS LLLP, UNIVERSAL CITY STUDIOS PRODUCTIONS, LLLP and WARNER BROS. ENTERTAINMENT, INC., Plaintiffs-Appellees, v. GARY FUNG and ISOHUNT WEB TECHNOLOGIES, INC., Defendants-Appellants. _______________________________________ Appeal from a Decision of the United States District Court for the Central District of California, No. 06-CV-05578 · Honorable Stephen V. Wilson BRIEF OF APPELLANTS IRA P. ROTHKEN, ESQ. ROBERT L. KOVSKY, ESQ. JARED R. SMITH, ESQ. ROTHKEN LAW FIRM 3 Hamilton Landing, Suite 280 Novato, California 94949 (415) 924-4250 Telephone (415) 924-2905 Facsimile Attorneys for Appellants, Gary Fung and isoHunt Web Technologies, Inc. COUNSEL PRESS · (800) 3-APPEAL PRINTED ON RECYCLED PAPER Case: 10-55946 12/17/2010 Page: 2 of 92 ID: 7585231 DktEntry: 18 CORPORATE DISCLOSURE STATEMENT OF ISOHUNT TECHNOLOGIES, INC. Pursuant to Federal Rule of Appellate Procedure 26.1 and Circuit Rule 26-1, appellant isoHunt Technologies, Inc. states that it has no parent corporation and that there is no publicly held corporation that owns 10% or more of its stock. APPELLANTS’ REQUEST FOR ORAL ARGUMENT The case presents important issues concerning copyright law, Internet development, free speech and international law. Appellants request oral argument. Case: 10-55946 12/17/2010 Page: 3 of 92 ID: 7585231 DktEntry: 18 TABLE OF CONTENTS Page Corporate Disclosure Statement of isoHunt Web Technologies, Inc Appellants’ Request for Oral Argument Table of Authorities ………………………………………………………. -
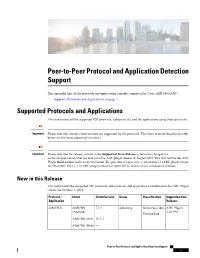
Peer-To-Peer Protocol and Application Detection Support
Peer-to-Peer Protocol and Application Detection Support This appendix lists all the protocols and applications currently supported by Cisco ASR 5500 ADC. • Supported Protocols and Applications, on page 1 Supported Protocols and Applications This section lists all the supported P2P protocols, sub-protocols, and the applications using these protocols. Important Please note that various client versions are supported for the protocols. The client versions listed in the table below are the latest supported version(s). Important Please note that the release version in the Supported from Release column has changed for protocols/applications that are new since the ADC plugin release in August 2015. This will now be the ADC Plugin Build number in the x.xxx.xxx format. The previous releases were versioned as 1.1 (ADC plugin release for December 2012 ), 1.2 (ADC plugin release for April 2013), and so on for consecutive releases. New in this Release This section lists the supported P2P protocols, sub-protocols and applications introduced in the ADC Plugin release for October 1, 2018. Protocol / Client Client Version Group Classification Supported from Application Release ABSCBN ABSCBN 7.1.2 Streaming Streaming-video ADC Plugin (Android) 2.28.990 Unclassified ABSCBN (iOS) 10.3.3 ABSCBN (Web) — Peer-to-Peer Protocol and Application Detection Support 1 Peer-to-Peer Protocol and Application Detection Support New in this Release Protocol / Client Client Version Group Classification Supported from Application Release Smashcast Smashcast 1.0.13 Streaming -

Bittorrent - Wikipedia, the Free Encyclopedia 11/12/13 Create Account Log In
BitTorrent - Wikipedia, the free encyclopedia 11/12/13 Create account Log in Article Talk Read Edit View history BitTorrent From Wikipedia, the free encyclopedia Main page Contents This article is about the file sharing protocol. For other uses, see BitTorrent (disambiguation). Featured content This article may be too technical for most readers to Current events understand. Please help improve this article to make it Random article understandable to non-experts, without removing the technical Donate to Wikipedia details. The talk page may contain suggestions. (May 2011) Wikimedia Shop BitTorrent is a protocol supporting the practice of Part of a series on Interaction peer-to-peer file sharing that is used to distribute large File sharing Help amounts of data over the Internet. BitTorrent is one of About Wikipedia the most common protocols for transferring large files, Community portal and peer-to-peer networks have been estimated to Recent changes collectively account for approximately 43% to 70% of Technologies Contact page all Internet traffic (depending on geographical location) Peer to peer · BitTorrent · Tools as of February 2009.[1] In November 2004, BitTorrent File hosting services was responsible for 35% of all Internet traffic.[2] As of Development and societal aspects Print/export February 2013, BitTorrent was responsible for 3.35% Timeline · Legal aspects Non-public file sharing Languages of all worldwide bandwidth, more than half of the 6% Anonymous P2P Friend-to-friend Darknet of total bandwidth dedicated to file sharing.[3] · · · Private P2P العربية Azərbaycanca Programmer Bram Cohen, a former University at File sharing networks and services [4] Беларуская Buffalo graduate student in Computer Science, Gnutella / Gnutella2 (G2) · FastTrack · Български designed the protocol in April 2001 and released the eDonkey · Direct Connect · Mininova · isoHunt The Pirate Bay Bitcoin Bosanski first available version on July 2, 2001,[5] and the final · · [6] By country or region Català version in 2008.